Enterprise IT environments require centralized management of user identities, devices, and resource access. You can deploy Active Directory (AD) Domain Services in the cloud to build an IT management domain. This enables unified identity verification, authorization, and policy control over cloud resources.
How it works

Domain Controller (DC): An instance that runs Active Directory Domain Services and DNS services. It serves as the core of domain authentication and resolution. This instance must have a static private IP address to ensure service continuity.
Client: An instance that joins the domain. Its DNS server is configured to point to the domain controller so that it can be managed by domain policies and use unified identity verification.
Network: The domain controller and client are located in the same VPC and vSwitch and communicate over the private network.
Procedure
Preparations
Create two Elastic Compute Service (ECS) instances in the same VPC. One instance serves as the domain controller (DC) for the AD domain, and the other serves as a client that will join the domain. This topic uses Windows Server 2016 as an example with the following configurations:
VPC CIDR block:
172.31.0.0/16Domain Controller (DC) IP:
172.31.106.88(static private IP)Client IP:
172.31.106.87(static private IP)Root domain name:
example.com
Alibaba Cloud does not recommend deploying a new domain controller from a custom image of an existing domain controller. If you must use this method, ensure that the new instance has the same hostname as the source instance, or change the hostname after you create the new instance.
Step 1: Deploy the domain controller
Log on to the domain controller ECS instance.
Go to the ECS Instances page. In the top-left corner, select the resource group and region where the target resource is located.
On the details page of the target instance, click Connect and select Workbench. Set the connection method to Terminal, enter your username and password, and log on to the graphical terminal.
Install the AD Domain Services and DNS Server roles.
Right-click the
 icon, click Run, enter
icon, click Run, enter servermanager.exeand press Enter to open Server Manager. Then, click Add Roles And Features.On the Installation Type and Server Selection pages, keep the default configurations and click Next.
On the Server Roles page, select the Active Directory Domain Services and DNS Server roles and confirm to add them.
AD Domain Services rely on DNS for domain name resolution and service location. The installation process automatically configures the local DNS server and creates the necessary DNS zones and records for the domain. If the DNS service is deployed on another server, you must manually configure DNS zone delegation, add AD-related DNS records, and ensure network connectivity.
Click Next until you reach the Install page. Click Install. After the installation is complete, click Close.
Promote the server to a domain controller.
After you install the roles, you must promote the server to a domain controller.
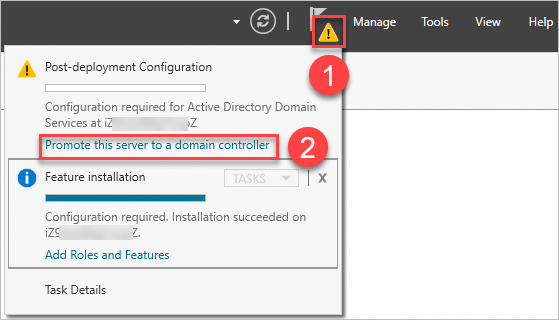
In the upper-right corner of Server Manager, click the yellow exclamation mark icon, and then select Promote this server to a domain controller.
On the Deployment Configuration page, select Add New Forest and set the Root Domain, such as
example.com.On the Domain Controller Options page, set the Directory Services Restore Mode (DSRM) password. This password is used for disaster recovery. Store this password in a secure location.
On the DNS Options page, click Next.
You can ignore the warning that a delegation for this DNS server cannot be created. This warning appears because the installation wizard attempts to contact the parent DNS zone to create a delegation. However, because you are creating the root domain of a new forest, no parent zone exists. This warning is expected and does not affect the functionality of the domain controller.
On the Other Options page, the system automatically generates a NetBIOS domain name (such as
EXAMPLE). Click Next.Keep the default configurations for the following steps. When the Prerequisite Check passes, click Install. The server will automatically restart after the installation is complete.
Verify the domain controller status.
After the restart, reconnect to the instance. Right-click the
 icon and click Run. Then, enter
icon and click Run. Then, enter control systemand press Enter. Verify the computer name and domain information. If the information is correct, the installation was successful.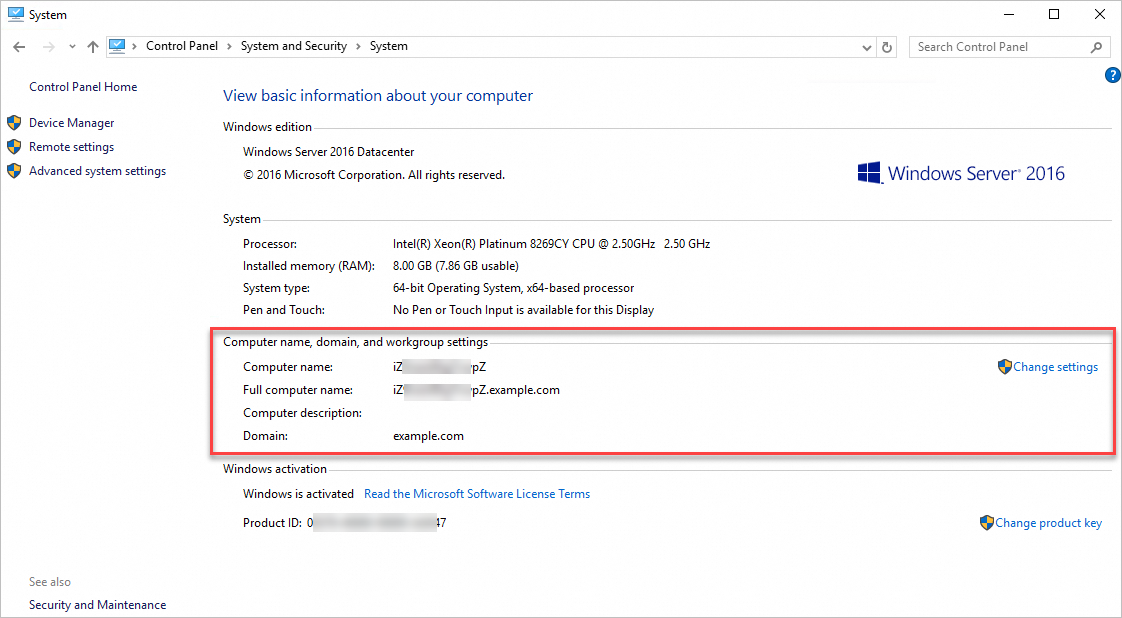
Step 2: Join the client to the AD domain
After you deploy the domain controller, join the client instance to the domain to enable centralized management.
Log on to the client ECS instance.
Go to the ECS Instances page. In the top-left corner, select the resource group and region where the target resource is located.
Go to the details page of the target instance. Click Connect and select Workbench. Select Terminal as the connection method, enter your username and password, and then log on to the instance.
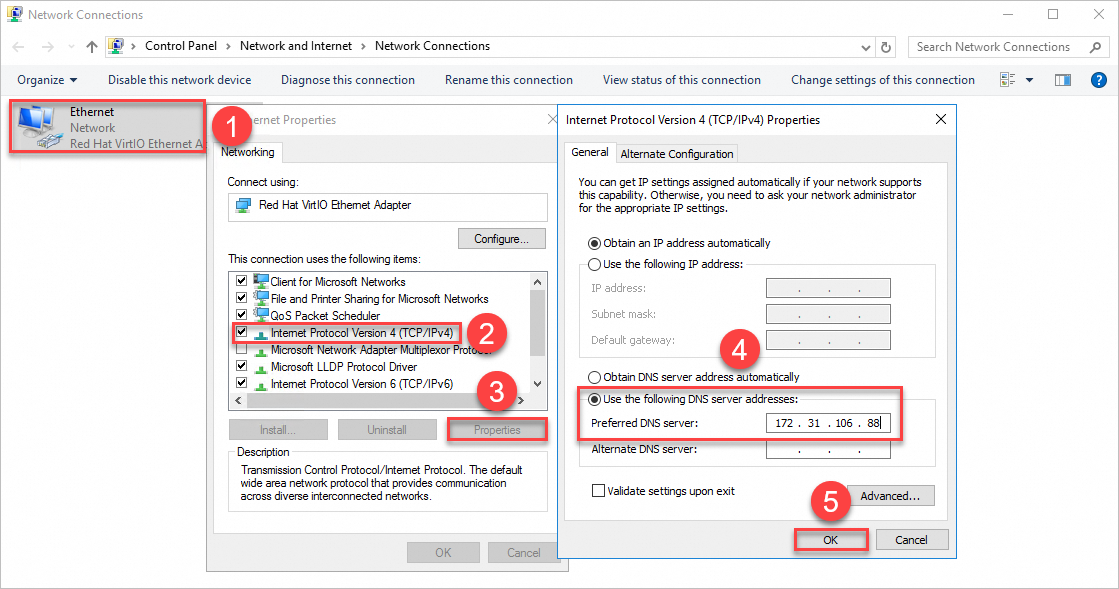
Configure the client DNS.
To allow the client to resolve the domain name and find the domain controller, you must set the client's DNS server address to the private IP address of the domain controller.
To open the Network Connections window, right-click the
 icon, click Run, enter
icon, click Run, enter ncpa.cpl, and press Enter.Right-click Ethernet and select Properties. Select Internet Protocol Version 4 (TCP/IPv4) and click Properties. Select Use the following DNS server addresses and change the DNS server address to the IP address of the domain controller from Step 1.
Join the client to the domain.
Right-click the
 icon, click Run, enter
icon, click Run, enter control system, and press Enter. In the Computer name, domain, and workgroup settings area, click Change settings on the right.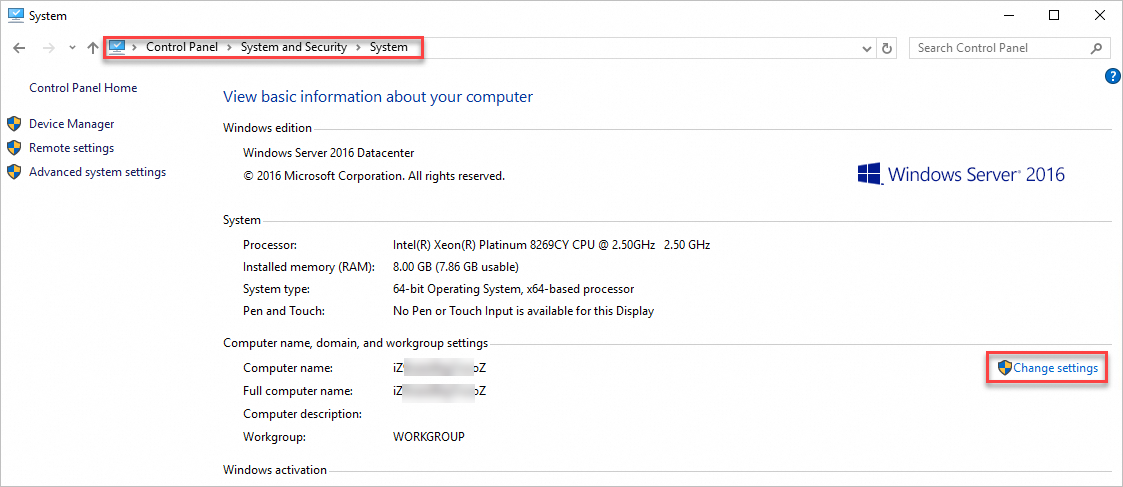
On the System Properties page, click Change.
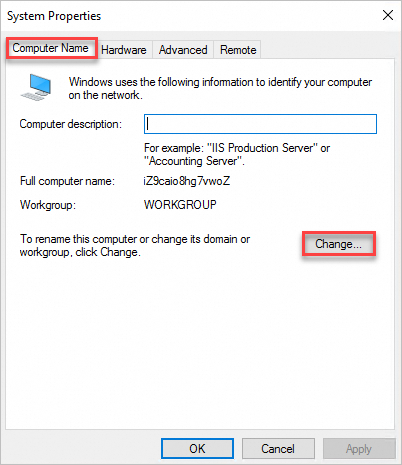
On the Computer Name/Domain Change page, enter the AD domain information.
Enter the root domain name of the AD domain that you set in Step 1: Deploy the domain controller, for example,
example.com.Restart the server for the changes to take effect.
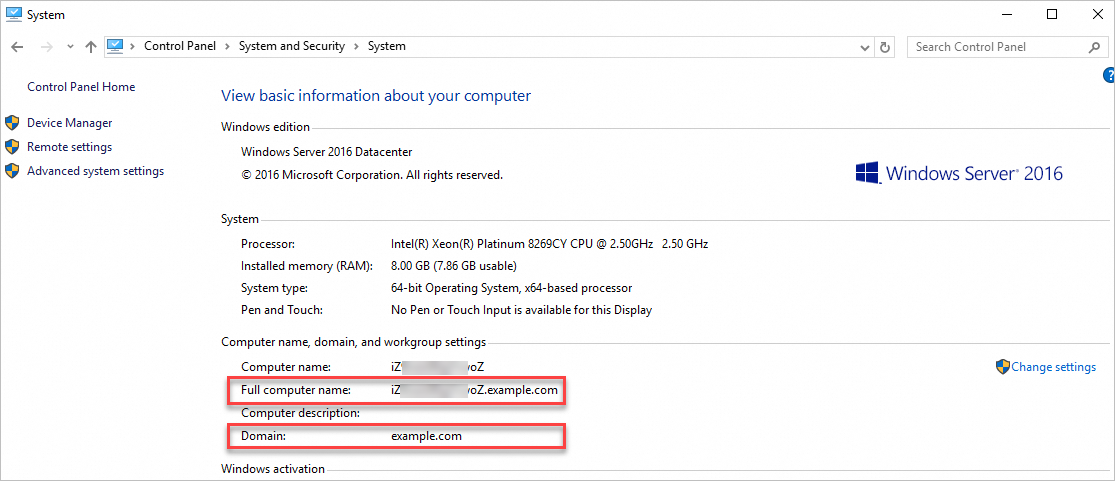
Verify the domain join status.
Right-click the
 icon, click Run, enter
icon, click Run, enter control system, and press Enter. If the full computer name and domain name include the AD root domain, the client has successfully joined the domain.After you set up an AD domain on an ECS instance and join a client to the domain, you can perform related operations based on your requirements, such as creating users and organizational units. For more information, see Active Directory Domain Services Overview.
After you set up the AD domain, ensure that the domain controller always uses a static IP address. If the IP address of the domain controller changes, clients that have the old IP address cached will fail to connect, which causes domain authentication to fail. You must manually update the DNS server configuration on all clients to point to the new IP address of the domain controller.
FAQ
How do I fix the "The security database on the server does not have a computer account for this workstation trust relationship" error?
Cause: The trust relationship between the domain member ECS instance and the Domain Controller (DC) is broken. Possible reasons include the following:
Snapshot recovery: The ECS instance was reverted to an old snapshot. This causes the locally stored machine password to mismatch the password stored in AD.
SID conflict: Multiple ECS instances were created from a custom image that did not run Sysprep, resulting in duplicate computer names or security identifier (SID) conflicts.
Long-term offline status: The instance was shut down or had no network connectivity for more than 30 days. This causes the machine account password to expire because it was not automatically updated.
Accidental deletion in AD: An administrator manually reset or deleted the computer account in AD.
Solution:
Solution 1: Quick repair with PowerShell (Recommended)
This solution repairs the secure channel online without requiring you to leave the domain.
Log on to the ECS instance with a local administrator account.
Execute the following command in PowerShell as an administrator to perform the repair.
Test-ComputerSecureChannel -Repair -Credential (Get-Credential)In the pop-up window, enter the username and password of a domain administrator.
Verify the result:
If it returns True, the repair was successful. Restart the ECS instance to restore the ability to log on with a domain account.
If it returns False or an error occurs, proceed to Solution 2.
Solution 2: Leave and rejoin the domain
Log on to the ECS instance with a local administrator account.
Leave the domain:
Right-click This PC, select , and then click Change.
Change the membership to Workgroup (for example, WORKGROUP).
Enter domain administrator credentials to confirm. After the operation succeeds, restart the computer.
Reset the computer account: On the domain controller, locate the computer account, right-click it, and select Reset Account.
Rejoin the domain:
Go to the Computer Name/Domain Changes window again.
For Member of, select Domain and enter the domain name.
Enter domain administrator credentials to confirm. After the operation succeeds, restart the computer.
After the restart, verify that the error is resolved.
What should I do if the error "The domain join cannot be completed because the SID of the domain you attempted to join was identical to the SID of this machine" appears when joining a client to an AD domain?
Cause: Multiple ECS instances were created from the same custom image and therefore have the same computer security identifier (SID) and computer name. When one of these instances communicates with the domain controller, conflicts arise when other instances with the same SID attempt to communicate. This leads to a broken trust relationship.
Solution:
Use the Windows System Preparation (Sysprep) tool to change the SID.
On the ECS instance, find the Sysprep tool
Sysprep.exe, which is usually in theC:\Windows\System32\Sysprepdirectory.Run
Sysprep.exeas an administrator, select the Generalize option, and click OK.After the system restarts, the SID is changed. You can then try to join the AD domain again.