Set up a Software Guard Extensions (SGX) confidential computing environment on an Intel SGX-enabled Elastic Compute Service (ECS) instance (vSGX instance) and verify that the SGX feature works correctly.
Prerequisites
Before you begin, ensure that you have:
A vSGX instance created and running (only the g7t, c7t, and r7t instance families support SGX — see Instance family overview)
SSH access to the instance
How SGX works
Intel SGX provides hardware-based confidential computing by isolating the runtime environment of SGX programs using instruction set extensions and an access control mechanism. Unlike firmware- or software-based security, SGX roots its trust solely in hardware, which prevents vulnerabilities in software-level trust anchors from compromising the system.
The g7t, c7t, and r7t security-enhanced instance families support SGX for virtual machines. These instances (referred to as vSGX instances) provide confidential memory backed by Intel SGX, letting you develop and run SGX programs in a protected enclave.
If you use hardware-bound keys — such as SGX sealing keys — to encrypt data inside an Intel SGX enclave, the encrypted data cannot be decrypted after the instance host changes. Implement data redundancy and backup at the application layer before using sealing keys in production.
Steps overview
Step 1: Check whether SGX is enabled
Use CPUID to confirm that SGX is enabled on the instance before proceeding.
Choose your OS path
The steps differ by operating system:
| OS image | Package manager | Notes |
|---|---|---|
| Alibaba Cloud Linux 2/3 (UEFI) | yum | Dedicated images include a built-in SGX driver |
| Ubuntu 22.04 (UEFI) | apt-get | Dedicated images include a built-in SGX driver |
| Other Linux (CentOS, etc.) | Manual | Install the SGX driver and Platform SoftWare (PSW) manually — see Intel SGX SW Installation Guide for Linux |
Follow the section that matches the image used to create your vSGX instance.
Alibaba Cloud Linux 2/3 (UEFI)
Install CPUID.
sudo yum install -y cpuidCheck whether SGX is enabled.
NoteDedicated images provided by Alibaba Cloud include a built-in SGX driver. If you are using a dedicated image, skip to step 3 to confirm the driver is present. If you are using a non-dedicated image, install the SGX driver separately before continuing.
cpuid -1 -l 0x7 |grep SGXOutput similar to the following indicates that SGX is enabled.
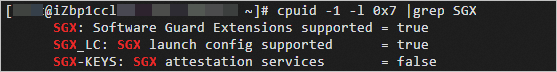
Confirm the SGX driver is installed.
ls -l /dev/{sgx_enclave,sgx_provision}Output similar to the following indicates that the SGX driver is installed.
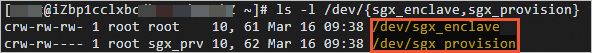
Ubuntu 22.04 (UEFI)
Install CPUID.
sudo apt-get update && sudo apt-get install -y --no-install-recommends cpuidCheck whether SGX is enabled.
cpuid -1 -l 0x7 |grep SGXOutput similar to the following indicates that SGX is enabled.
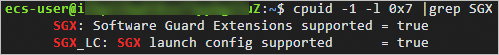
Install the SGX driver.
Create the
install_sgx_dcap.shscript.cat <<'EOF' > install_sgx_dcap.sh #!/bin/bash version_id=$(cat /etc/os-release|grep "VERSION_ID"|cut -d"=" -f2|tr -d "\"") version_codename=$(cat /etc/os-release|grep "VERSION_CODENAME"|cut -d"=" -f2) apt-get update && DEBIAN_FRONTEND=noninteractive apt-get install -y build-essential dkms curl wget if [ ! -e /dev/sgx/enclave -a ! -e /dev/sgx_enclave ]; then dcap_version=$(curl -s https://download.01.org/intel-sgx/latest/version.xml |grep dcap| sed -r 's/.*>(.*)<.*/\1/') dcap_files=$(curl -s https://download.01.org/intel-sgx/latest/dcap-latest/linux/SHA256SUM_dcap_${dcap_version}.cfg) echo "${dcap_files}" | grep "ubuntu${version_id}-server" |grep "sgx_linux_x64_driver" | awk '{print $2}' | xargs -I{} curl -O -J https://download.01.org/intel-sgx/latest/dcap-latest/linux/{} bash sgx_linux_x64_driver*.bin else echo "driver already installed" fi EOFRun the script to install the SGX driver. ``
bash sudo bash ./install_sgx_dcap.sh``
NoteDedicated images provided by Alibaba Cloud include a built-in SGX driver. Skip this step if you are using a dedicated image.
Confirm the SGX driver is installed.
ls -l /dev/{sgx_enclave,sgx_provision}Output similar to the following indicates that the SGX driver is installed.
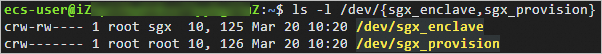
Step 2: Build the SGX confidential computing environment
Install the SGX runtime and SDK, then configure the remote attestation service. Alibaba Cloud TEE SDK is fully compatible with Intel SGX SDK, so applications written against the Intel SGX SDK run without modification.
When you create a vSGX instance in the ECS console, the Alibaba Cloud SGX runtime is installed automatically. Skip the runtime installation step and go directly to installing the SDK.
Choose your OS path
| OS image | SDK installed |
|---|---|
| Alibaba Cloud Linux 2/3 (UEFI) | Alibaba Cloud TEE SDK via yum |
| Ubuntu 22.04 (UEFI) | Intel SGX SDK and PSW via script |
Alibaba Cloud Linux 2/3 (UEFI)
Install the Alibaba Cloud SGX runtime (skip if already installed)
Import the YUM repository for Alibaba Cloud confidential computing. The repository URLs follow these formats: Replace
<region-id>with the region ID of your vSGX instance (for example,cn-hangzhou). Run the following script to import the repository automatically:Create the
install_sgx_repo.shscript.cat <<'EOF' > install_sgx_repo.sh ID=$(grep -w '^ID' /etc/os-release | awk -F= '{print $2}' | tr -d '"') VERSION_ID=$(grep -w '^VERSION_ID' /etc/os-release | awk -F= '{print $2}' | tr -d '"') # Query the region of the instance. token=$(curl -s -X PUT -H "X-aliyun-ecs-metadata-token-ttl-seconds: 5" "http://100.100.100.200/latest/api/token") region_id=$(curl -s -H "X-aliyun-ecs-metadata-token: $token" http://100.100.100.200/latest/meta-data/region-id) # Enable the Alibaba Cloud experimental repository if an Alibaba Cloud Linux 2 (UEFI) image is used. if [ "$ID" = "alinux" -a "$VERSION_ID" = "2.1903" ]; then sudo rpmkeys --import http://mirrors.cloud.aliyuncs.com/epel/RPM-GPG-KEY-EPEL-7 sudo yum install -y alinux-release-experimentals fi yum install -y yum-utils && \ yum-config-manager --add-repo \ https://enclave-${region_id}.oss-${region_id}-internal.aliyuncs.com/repo/alinux/enclave-expr.repo EOFRun the script to import the repository. ``
bash sudo bash ./install_sgx_repo.sh``
Network URL format Public https://enclave-<region-id>.oss-<region-id>.aliyuncs.com/repo/alinux/enclave-expr.repoVPC internal https://enclave-<region-id>.oss-<region-id>-internal.aliyuncs.com/repo/alinux/enclave-expr.repoInstall the Alibaba Cloud SGX runtime.
NoteThe SGX Architectural Enclave Service Manager (AESM) manages enclave startup, key provisioning, and remote attestation. Its default installation path is
/opt/intel/sgx-aesm-service.sudo yum install -y libsgx-ae-le libsgx-ae-pce libsgx-ae-qe3 libsgx-ae-qve \ libsgx-aesm-ecdsa-plugin libsgx-aesm-launch-plugin libsgx-aesm-pce-plugin \ libsgx-aesm-quote-ex-plugin libsgx-dcap-default-qpl libsgx-dcap-ql \ libsgx-dcap-quote-verify libsgx-enclave-common libsgx-launch libsgx-pce-logic \ libsgx-qe3-logic libsgx-quote-ex libsgx-ra-network libsgx-ra-uefi \ libsgx-uae-service libsgx-urts sgx-ra-service sgx-aesm-service
Install Alibaba Cloud TEE SDK
sudo yum install -y sgxsdkThe default installation path is /opt/alibaba/teesdk/intel/sgxsdk/. For development reference, see Intel SGX Developer Reference.
Ubuntu 22.04 (UEFI)
Create the
install_sgx_sdk.shscript.cat <<'EOF' > install_sgx_sdk.sh #!/bin/bash version_id=$(cat /etc/os-release|grep "VERSION_ID"|cut -d"=" -f2|tr -d "\"") version_codename=$(cat /etc/os-release|grep "VERSION_CODENAME"|cut -d"=" -f2) apt-get update && DEBIAN_FRONTEND=noninteractive apt-get install -y build-essential dkms curl wget dcap_version=$(curl -s https://download.01.org/intel-sgx/latest/version.xml |grep dcap| sed -r 's/.*>(.*)<.*/\1/') linux_version=$(curl -s https://download.01.org/intel-sgx/latest/version.xml |grep linux| sed -r 's/.*>(.*)<.*/\1/') dcap_files=$(curl -s https://download.01.org/intel-sgx/latest/dcap-latest/linux/SHA256SUM_dcap_${dcap_version}.cfg) echo "${dcap_files}" | grep "ubuntu${version_id}-server" | awk '{print $2}' | xargs -I{} curl -O -J https://download.01.org/intel-sgx/latest/dcap-latest/linux/{} # install sgx_sdk bash sgx_linux_x64_sdk*.bin --prefix /opt/intel source /opt/intel/sgxsdk/environment # install psw echo "deb [arch=amd64] https://download.01.org/intel-sgx/sgx_repo/ubuntu ${version_codename} main" | tee /etc/apt/sources.list.d/intelsgx.list wget -qO - https://download.01.org/intel-sgx/sgx_repo/ubuntu/intel-sgx-deb.key | apt-key add - apt-get update && DEBIAN_FRONTEND=noninteractive apt-get install -y libsgx-launch libsgx-urts libsgx-epid libsgx-quote-ex libsgx-dcap-ql libsgx-dcap-ql-dev systemctl enable --now aesmd.service EOFRun the script to install Intel SGX SDK and Platform SoftWare (PSW).
sudo bash ./install_sgx_sdk.sh
Configure the SGX remote attestation service
The Alibaba Cloud SGX remote attestation service is fully compatible with the Intel SGX Elliptic Curve Digital Signature Algorithm (ECDSA)-based remote attestation service. vSGX instances use remote attestation to prove enclave integrity to remote parties.
The service provides:
SGX certificates
Revocation lists for revoked SGX certificates
Trusted computing base information (root of trust)
Intel Ice Lake supports only Data Center Attestation Primitives (DCAP)-based remote attestation. It does not support Enhanced Privacy ID (EPID)-based remote attestation. Adapt your applications accordingly before using the remote attestation feature.
The service is deployed per region. For optimal stability, access the service endpoint in the same region as your vSGX instance.
After you install Alibaba Cloud TEE SDK, the default configuration file /etc/sgx_default_qcnl.conf is generated automatically. Update this file to point to the Alibaba Cloud Provisioning Certificate Caching Service (PCCS) in your region using one of the following methods.
Supported regions
| Region | Region ID |
|---|---|
| China (Qingdao) | cn-qingdao |
| China (Beijing) | cn-beijing |
| China (Zhangjiakou) | cn-zhangjiakou |
| China (Ulanqab) | cn-wulanchabu |
| China (Hangzhou) | cn-hangzhou |
| China (Shanghai) | cn-shanghai |
| China (Shenzhen) | cn-shenzhen |
| China (Heyuan) | cn-heyuan |
| China (Guangzhou) | cn-guangzhou |
| China (Chengdu) | cn-chengdu |
| China (Hong Kong) | cn-hongkong |
| Singapore | ap-southeast-1 |
| Indonesia (Jakarta) | ap-southeast-5 |
Method 1: Auto-configure (recommended)
Run the following commands to detect the instance region automatically and update /etc/sgx_default_qcnl.conf.
# Get the region ID of the instance.
token=$(curl -s -X PUT -H "X-aliyun-ecs-metadata-token-ttl-seconds: 5" "http://100.100.100.200/latest/api/token")
region_id=$(curl -s -H "X-aliyun-ecs-metadata-token: $token" http://100.100.100.200/latest/meta-data/region-id)
# Set the PCCS URL for the region.
PCCS_URL=https://sgx-dcap-server-vpc.${region_id}.aliyuncs.com/sgx/certification/v4/
sudo bash -c 'cat > /etc/sgx_default_qcnl.conf' << EOF
# PCCS server address
PCCS_URL=${PCCS_URL}
# To accept insecure HTTPS cert, set this option to FALSE
USE_SECURE_CERT=TRUE
EOFFor more information about instance metadata, see Access instance metadata.
Method 2: Configure manually
Edit /etc/sgx_default_qcnl.conf and set the PCCS_URL based on your instance's network configuration. Replace <region-id> with your region ID.
| Network type | PCCS_URL |
|---|---|
| Public IP | https://sgx-dcap-server.<region-id>.aliyuncs.com/sgx/certification/v4/ |
| VPC internal only | https://sgx-dcap-server-vpc.<region-id>.aliyuncs.com/sgx/certification/v4/ |
Example for a VPC-only instance in cn-hangzhou:
# PCCS server address
PCCS_URL=https://sgx-dcap-server-vpc.cn-hangzhou.aliyuncs.com/sgx/certification/v4/
# To accept insecure HTTPS cert, set this option to FALSE
USE_SECURE_CERT=TRUEVerify the SGX feature
Run the sample code included with Alibaba Cloud TEE SDK to confirm that the SGX environment works end to end. Sample code is stored in /opt/alibaba/teesdk/intel/sgxsdk/SampleCode by default.
Example 1: Start an enclave
Start a sample enclave to confirm that the installed SGX SDK operates correctly.
Alibaba Cloud Linux 2/3 (UEFI)
Install a compiler.
ID=$(grep -w '^ID' /etc/os-release | awk -F= '{print $2}' | tr -d '"') VERSION_ID=$(grep -w '^VERSION_ID' /etc/os-release | awk -F= '{print $2}' | tr -d '"') if [ "$ID" = "alinux" ]; then case "$VERSION_ID" in "2.1903" ) sudo yum install -y devtoolset-9 ;; "3" ) sudo yum groupinstall -y "Development Tools" ;; esac fiConfigure the SGX SDK environment variables.
if [ "$ID" = "alinux" -a "$VERSION_ID" = "2.1903" ]; then source /opt/rh/devtoolset-9/enable fi source /opt/alibaba/teesdk/intel/sgxsdk/environmentCompile the SampleEnclave code.
Go to the SampleEnclave directory. ``
bash cd /opt/alibaba/teesdk/intel/sgxsdk/SampleCode/SampleEnclave``Build the sample. ``
bash sudo -E make``
Run the compiled executable.
sudo ./appThe following output indicates that SGX is running correctly.

Ubuntu 22.04 (UEFI)
Update the package list.
sudo apt updateInstall the
build-essentialcompiler.sudo apt install -y build-essentialCompile the SampleEnclave code.
Go to the SampleEnclave directory. ``
bash cd /opt/intel/sgxsdk/SampleCode/SampleEnclave/``Build the sample. ``
bash sudo make SGX_DEBUG=1``
Run the compiled executable.
sudo ./appThe following output indicates that SGX is running correctly.

Example 2: Use the SGX remote attestation service
This example demonstrates DCAP-based remote attestation using the QuoteGenerationSample and QuoteVerificationSample files. The challenged party (the SGX program running in the vSGX instance) generates a quote using QuoteGenerationSample. The challenging party (the remote verifier) validates the quote using QuoteVerificationSample.
This example uses an Alibaba Cloud Linux 2 (UEFI) or Alibaba Cloud Linux 3 (UEFI) image.
Install a compiler.
Alibaba Cloud Linux 2 (UEFI):
Install devtoolset. ``
bash sudo yum install -y devtoolset-9``Configure the devtoolset environment variables. ``
bash source /opt/rh/devtoolset-9/enable``
Alibaba Cloud Linux 3 (UEFI): ``
bash sudo yum groupinstall -y "Development Tools"``
Configure the SGX SDK environment variables.
source /opt/alibaba/teesdk/intel/sgxsdk/environmentInstall the remote attestation dependency packages.
sudo yum install -y libsgx-dcap-ql-devel libsgx-dcap-quote-verify-devel libsgx-dcap-default-qpl-develCompile the QuoteGenerationSample code (challenged party).
Go to the QuoteGenerationSample directory. ``
bash cd /opt/alibaba/teesdk/intel/sgxsdk/SampleCode/QuoteGenerationSample``Build the sample. ``
bash sudo -E make``
Run the compiled executable to generate a quote.
sudo ./appThe following output indicates that quote generation succeeded.

Compile the QuoteVerificationSample code (challenging party).
Go to the QuoteVerificationSample directory. ``
bash cd /opt/alibaba/teesdk/intel/sgxsdk/SampleCode/QuoteVerificationSample``Build the sample. ``
bash sudo -E make``
Sign the QuoteVerificationSample enclave. To release an official enclave, sign it with a private key.
NoteIf the error
Failed to open file "Enclave/Enclave_private_sample.pem"appears, use the key from the QuoteGenerationSample directory instead:sudo sgx_sign sign -key ../QuoteGenerationSample/Enclave/Enclave_private_sample.pem -enclave enclave.so -out enclave.signed.so -config Enclave/Enclave.config.xmlsudo sgx_sign sign -key Enclave/Enclave_private_sample.pem -enclave enclave.so -out enclave.signed.so -config Enclave/Enclave.config.xmlRun the compiled executable to verify the quote.
sudo ./appThe following output indicates that quote verification succeeded.

Update the SGX SDK, PSW, and DCAP software
The Intel SGX software stack consists of SGX SDK, SGX PSW, and SGX Data Center Attestation Primitives (DCAP). Update these packages regularly to maintain optimal security.
The following example uses an Alibaba Cloud Linux 3 (UEFI) image.
Update all SGX-related packages.
sudo rpm -qa --qf "%{NAME}\n"|grep -E "sgxsdk|libsgx-|libtdx-|^sgx-|^tdx-"|sudo xargs bash -c '</dev/tty yum update "$@"' _Check the installed versions.
SGX SDK and SGX PSW: ``
bash sudo rpm -qa|grep -E "sgxsdk|sgx-aesm-service|libsgx-(ae-epid|ae-le|ae-pce|aesm|enclave|epid|headers|launch|quote-ex|uae-service|urts)"`` Example output:
SGX DCAP: ``
bash sudo rpm -qa|grep -E "sgx-(dcap-pccs|pck|ra-service)|libsgx-(ae-id-enclave|ae-qe3|ae-qve|ae-tdqe|dcap|pce-logic|qe3-logic|ra-|tdx-)|libtdx-|^tdx-"`` Example output:
Known issues
Memory leak on Alibaba Cloud Linux 2 kernel 4.19.91-23.al7
The SGX driver bundled with Alibaba Cloud Linux 2 kernel version 4.19.91-23.al7.x86_64 has a memory leak. This is fixed in the latest kernel version.
To fix without updating the kernel, install the hotfix patch:
sudo yum install -y alinux-release-experimentals && \
sudo yum install -y kernel-hotfix-5577959-23.al7.x86_64