E-MapReduce (EMR) allows you to configure a custom ECS application role in the Advanced Settings section of the Basic Settings step when you create a cluster in the EMR console. You can use this role to access other cloud resources, such as Object Storage Service (OSS) and Log Service, in your Alibaba Cloud account in password-free mode. This topic describes how to create and use a custom ECS application role.
Background information
- A cluster can access only the OSS data directories that you specify.
- A cluster can access the external resources that you specify.
Prerequisites
An OSS bucket is created in the OSS console. Make sure that the bucket resides in the region where you want to create an EMR cluster. For more information about how to create a bucket, see Create buckets.
Procedure
Step 1: Create a policy
Go to the Create Policy page.
Log on to the RAM console by using an Alibaba Cloud account.
In the left-side navigation pane, choose .
On the Policies page, click Create Policy.
On the Create Policy page, click the JSON tab.
Enter the policy document and click OK.
Enter the following policy document in the script editor:
{ "Version": "1", "Statement": [ { "Action": [ "oss:GetObject", "oss:ListObjects" ], "Resource": [ "acs:oss:*:*:emr-logs2", "acs:oss:*:*:emr-logs2/*" ], "Effect": "Allow" } ] }NoteElements in the policy:
Action: the actions on resources. In this example, the permissions to read and query OSS data are granted.
Resource: the resources on which the permissions are granted. In this example, the OSS bucket emr-logs2 and the objects in this OSS bucket are used as the resources.
For more information about the basic elements of a policy, see Policy elements.
Configure the Name parameter in the Basic information section to specify the policy name.
In this example, the name is test-emr.
Click OK.
Step 2: Create a RAM role
In the left-side navigation pane of the RAM console, choose .
On the Roles page, click Create Role.
Create a RAM role.
In the Select Role Type step, select Alibaba Cloud Service for Select Trusted Entity.
Click Next.
In the Configure Role step, configure the parameters.
Parameter
Description
RAM Role Name
In this example, the name is test-emr.
Select Trusted Service
Select Elastic Compute Service from the drop-down list.
Click OK.
Optional. Change the trusted service.
ImportantIf you want to create a cluster of EMR V5.X or later, a minor version later than EMR V4.5, or a minor version later than EMR V3.32, skip this step.
On the Roles page, click the name of the RAM role that you created.
Click the Trust Policy tab.
Click Edit Trust Policy.
Change
ecs.aliyuncs.comtoemr.aliyuncs.com.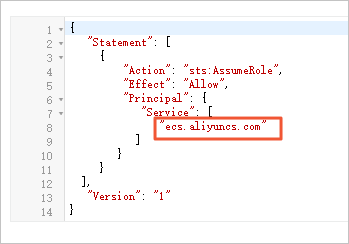
Click Save trust policy document.
Add the required permissions.
On the Roles page, find the RAM role that you created and click Grant Permission in the Actions column.
In the Grant Permission panel, select Custom Policy from the drop-down list in the Policy section and select the policy that you created in Step 1.
Click Grant permissions.
Click Close.
Step 3: Create a cluster and access external resources
Log on to the EMR console. In the left-side navigation pane, click EMR on ECS.
In the top navigation bar, select the region in which your cluster resides and select a resource group based on your business requirements.
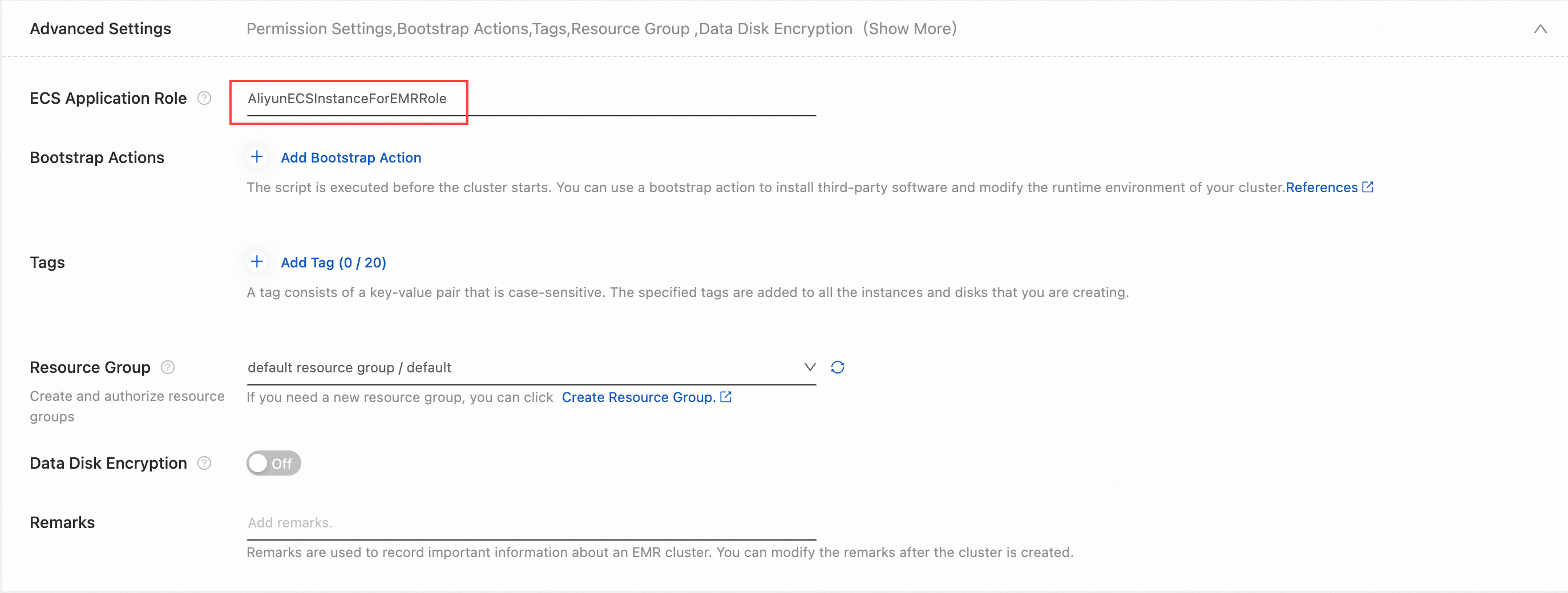
On the EMR on ECS page, click Create Cluster. In the Advanced Settings section of the Basic Configuration step, enter the name of the RAM role that you created in Step 2: Create a RAM role. For more information, see Create a cluster.
After the cluster is created, log on to the cluster by using SSH. For more information, see Log on to a cluster.
Run the following command to check whether you can access the OSS bucket that is specified in the policy:
hdfs dfs -ls oss://<yourBucketName>/NoteReplace <yourBucketName> in the command with the name of the OSS bucket.
If you do not have permissions to access the bucket, access to the OSS bucket is denied.
If you have permissions to access the bucket, access to the OSS bucket is allowed.
FAQ
- Q: What do I do if the NoPermission message appears when I create a cluster? A: Perform the following operations in sequence to resolve the issue:
- Check whether the RAM user that you used to create the cluster is authorized to create clusters and change ECS application roles. If the RAM user is granted the AliyunEMRDevelopAccess permission, you must change the permission to AliyunEMRFullAccess.
- Check whether the name of the ECS application role that you specified when you create the cluster is valid.
- Check whether the trust policy is changed to emr.aliyuncs.com.
Q: What do I do if I cannot access an OSS bucket from Hadoop Distributed File System (HDFS)?
A: Perform the following operations in sequence to resolve the issue:
Check whether the OSS bucket that you want to access resides in the same region as your cluster. If the OSS bucket and your cluster do not reside in the same region, you must add the endpoint of the OSS bucket to the access links.
Check whether the OSS bucket that you want to access is one of the resources specified in the created policy. If the OSS bucket is not one of the resources, modify the policy.
Check whether the related permissions on the OSS bucket are configured in the OSS console. If the permissions are configured, you must cancel the settings in the OSS console and specify Action in the policy to configure the permissions.