Data Security Center (DSC) continuously monitors your database configurations against established security baselines—checking authentication, access control, encryption, backup, and recovery settings. This feature helps you identify configuration risks before they become security incidents.
Security baseline check is built on two components: check policies (groups of related security requirements) and check items (individual configuration checks within a policy).
Prerequisites
Before you begin, ensure that you have:
DSC Free Edition activated or a paid DSC edition purchased. DSC Free Edition supports a subset of baseline check items; paid editions support all check items. For details, see DSC Free Edition and Purchase DSC
DSC authorized to access your data assets. For details, see Asset authorization
How it works
DSC checks your databases against two security baselines, both aligned with the Information Security Technology - Data Security Capability Maturity Model (GB/T 37988-2019):
China Personal Information Protection Law (PIPL): Provides full-lifecycle security monitoring for personal information and data assets. Applies to database instances and Object Storage Service (OSS) buckets that contain personal information or sensitive personal information identified by data identification tasks.
Best practices of Alibaba Cloud for data security: Provides full-lifecycle security monitoring for data assets. Applies to database instances and OSS buckets that DSC is authorized to access.
DSC checks configurations across seven policy areas:
| Check policy | What it checks |
|---|---|
| Log auditing and monitoring | Whether log auditing or log storage is enabled for your databases |
| Identity and permission management | Whether permission control is in place—for example, whether standard accounts are restricted to routine tasks following the principle of least privilege |
| Sensitive data protection | Whether databases allow public reads and writes, and whether access control is enforced on projects containing sensitive data. Note This policy only applies to instances and OSS buckets where data identification tasks have found personal information or sensitive personal information. If you do not perform data scanning and detection on the database instances and OSS buckets, or the scan result does not contain personal information or sensitive personal information, the check items of this policy pass automatically. |
| Access control | Whether your databases are publicly accessible |
| Data backup and recovery | Whether data backup is enabled for your databases |
| Data storage security | Whether encryption is enabled for your databases |
| Data transmission encryption | Whether data transmission is encrypted for your databases |
The check items displayed on the Policies tab under Risk Governance > Configuration Risks are the authoritative list. Handle detected configuration risks promptly to protect your data assets from attacks.
Supported databases
Security baseline check covers the following Alibaba Cloud database services:
| Category | Database engine |
|---|---|
| Relational database | RDS MySQL |
| RDS SQL Server | |
| RDS PostgreSQL | |
| RDS MariaDB | |
| ApsaraDB for OceanBase in MySQL mode | |
| ApsaraDB for OceanBase in Oracle mode | |
| PolarDB-X 1.0 | |
| PolarDB for MySQL | |
| PolarDB for PostgreSQL | |
| PolarDB for Oracle | |
| Non-relational database | MongoDB |
| Redis | |
| Big data | TableStore |
| MaxCompute | |
| AnalyticDB for MySQL | |
| AnalyticDB for PostgreSQL | |
| Unstructured database | OSS |
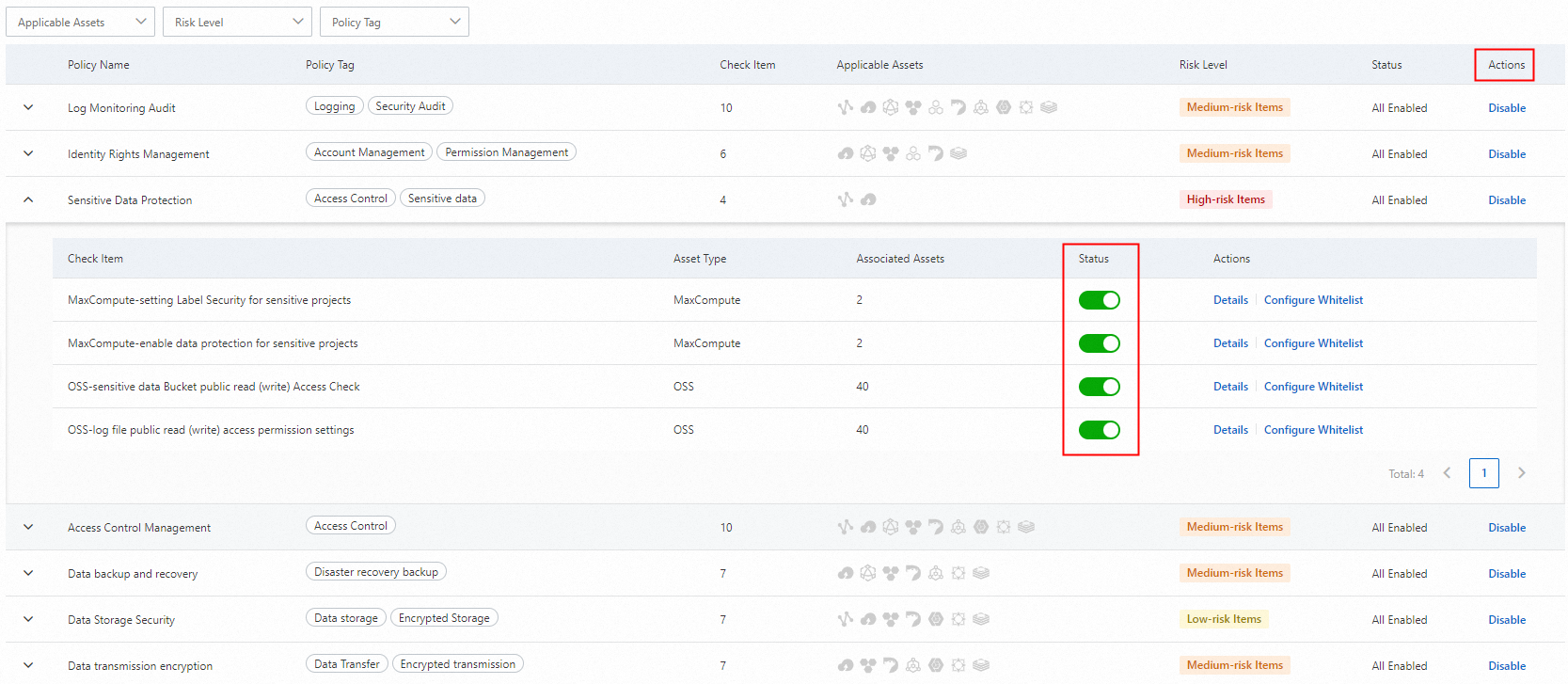
Enable or disable check items
All check items are enabled by default. Disable individual check items or entire check policies based on your business requirements.
Log on to the DSC console.
In the left-side navigation pane, choose Risk Governance > Configuration Risks.
Click the Policies tab, then select either the Alibaba Cloud Data Security Best Practices or PIPL-based Security Baseline Check tab.
In the check policy list, find the check item you want to change and toggle the switch in the Status column.
To enable or disable all check items within a policy at once, toggle the switch at the policy level.
Run checks
View the last check time
On the Policies tab, click either the Alibaba Cloud Data Security Best Practices or PIPL-based Security Baseline Check tab and look at the Last Checked Time value.
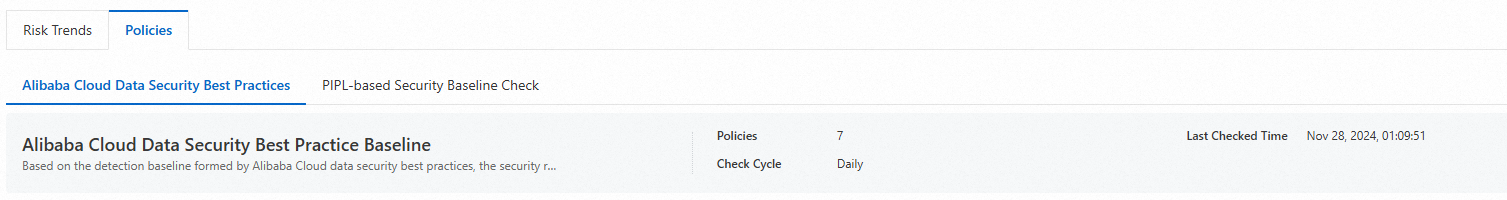
Automatic checks
DSC automatically performs a check on the databases connected to DSC at approximately 01:00:00 (UTC+8) every day.
Manual re-check
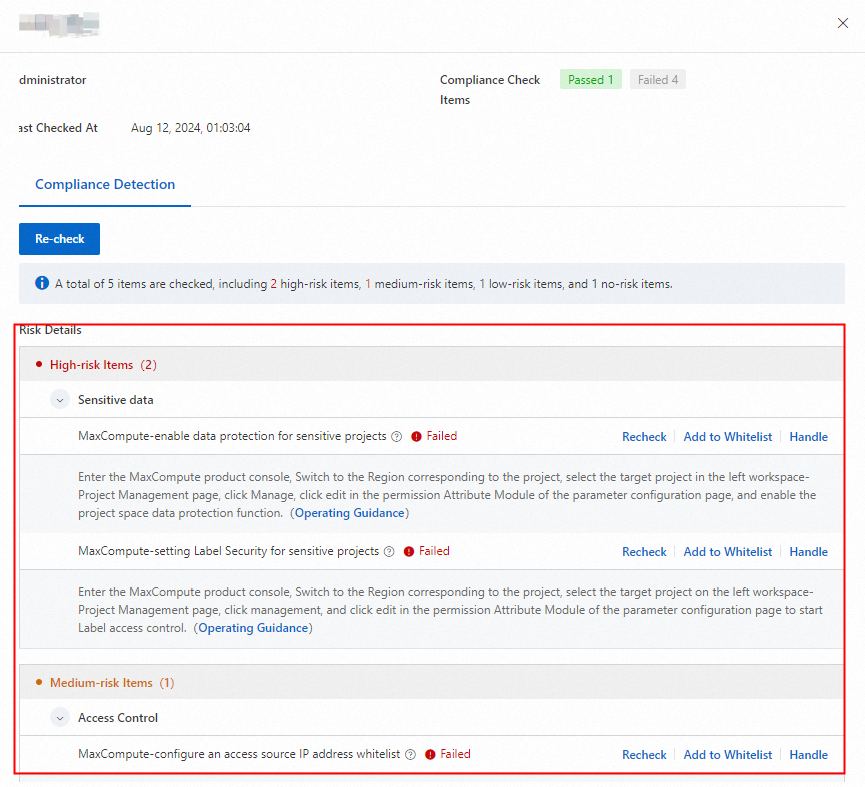
After connecting a new data asset or modifying database configurations, trigger an immediate re-check. A re-check takes about 10 minutes.
In the left-side navigation pane, choose Risk Governance > Configuration Risks.
On the Risk Trends tab, click Alerts, find the relevant policy, and click Details in the Actions column.
On the Risk Situation or Assets tab, click Re-check to run a re-check scoped to specific check items or data assets.

View asset risk trends
DSC combines security baseline check results with sensitive data detection to show you risk trends across your data assets.
In the left-side navigation pane, choose Risk Governance > Configuration Risks.
On the Risk Trends tab, select a baseline type from the drop-down list.
On the Asset Risks tab, review the following:
Data Asset Sensitivity Situation: A column chart showing the number of high-risk, medium-risk, and low-risk assets.
Security Situation of Sensitive Data: A column chart breaking down risk levels across sensitive personal information, personal information, and general information.
Risk governance progress: Shows the scan status per asset. The Progress column shows passed check items versus total applicable check items—for example,
2/3means 3 check items apply and 2 have passed. Completed means all applicable check items have passed. The Risk Level column shows the highest risk level among all failed check items for that asset.
Handle configuration risks
DSC provides handling suggestions for each detected risk, but you must take the remediation action manually. Choose one of three views based on your workflow.
Handle configuration risks promptly based on the suggestions to prevent data leaks and security incidents.
From the asset perspective
This view lists all scannable data assets and shows which ones have configuration risks.
In the left-side navigation pane, choose Risk Governance > Configuration Risks.
On the Risk Trends tab, click the Asset Risks tab.
Select an action:
Handle a risk: Click Handle in the Actions column for a data asset to see its failed check items and remediation suggestions. In the Risk Details section, click Handle to apply the fix.
Add an asset to the whitelist: If a security engineer determines that baseline checks are not required for a database, click Add to Whitelist in the Actions column. All check items for that asset are added to the whitelist, and Completed appears in the Progress column.
Add a specific check item to the whitelist: Click Handle in the Actions column. In the Risk Governance panel, select the check item and click Add to Whitelist next to it. Added to Whitelist appears for that check item.
From the check policy perspective
This view organizes risks by check policy, showing how many assets are affected by each policy.
In the left-side navigation pane, choose Risk Governance > Configuration Risks.
On the Risk Trends tab, click the Alerts tab to see all check policies.
Number of alarms: The number of assets that fail check items in the policy.
Associate Asset: The total count of asset-to-check-item associations. An asset is counted once per applicable check item.
Click Details in the Actions column for a check policy.
On the details page, use the two tabs:
Risk Situation: Lists all check items in the policy with details—number of risky assets, total applicable assets, and check item status. Click Check in the Actions column to run a re-check for a specific check item.
Assets: Lists assets covered by the policy. From here, rescan an asset, add it to or remove it from the whitelist, or click Handle to remediate risks.
From the check item perspective
This view lets you drill into individual check items across all policies.
In the left-side navigation pane, choose Risk Governance > Configuration Risks, then click the Policies tab.
Select a check policy and click the
 icon to expand its check items.
icon to expand its check items.Select a check item and click Details or Configure Whitelist in the Actions column to manage the assets it applies to. From the details panel, you can:
Click Add to Whitelist in the Actions column to whitelist an asset for that check item.
Click Handle to remediate risks for the selected asset.
After remediation, click Verification to confirm the risks are resolved.