Vulnerability Management automates the discovery, assessment, and remediation of security vulnerabilities on your servers. To help you manage security risks and reduce your system's attack surface, it covers operating systems (OS), Web Content Management Systems (Web-CMS), and various applications. Vulnerability Management provides automated scanning and fixes, replacing traditional manual patching and making it ideal for managing large-scale server clusters.
Use cases
Continuous and automated vulnerability management for critical business servers
Scenario: Critical business servers require daily vulnerability scans and timely fixes to keep services secure and stable.
Applicable editions: Advanced, Enterprise, or Ultimate.
Features: Supports one automatic periodic vulnerability scan per day and unlimited vulnerability fixes. It also supports manual vulnerability scans to address sudden security incidents.
Basic protection for non-core servers or development environments
Scenario: You need basic vulnerability detection and fixing for a small number of servers (fewer than 10) or for development and testing environments, while keeping costs low.
Applicable editions: Anti-virus, with an option to Purchase vulnerability fixes on demand.
Features: Supports one automatic periodic vulnerability scan every two days, meeting basic needs. When you need to fix vulnerabilities, you can use the pay-as-you-go model or purchase a fix package for flexible vulnerability management.
Rapidly respond to and investigate newly disclosed critical vulnerabilities
Scenario: When a major security vulnerability (such as Log4j2) is disclosed, you need to immediately determine if any of your server assets are affected.
Applicable editions: Enterprise or Ultimate.
Features: Use the manual vulnerability scan to immediately run a comprehensive scan on all or a subset of your servers. The scan results provide detailed vulnerability information and official remediation advice for manual fixes.
Core features
Vulnerability scan
Vulnerability Scan supports two methods: manual vulnerability scan and periodic automatic vulnerability scan.
Comparison | Manual vulnerability scan | Periodic automatic vulnerability scan |
Trigger method | Users initiate scans on demand from the console. | The system automatically runs scans at scheduled intervals based on a preset policy. |
Scan frequency | Not fixed; determined by the user. | Advanced, Enterprise, and Ultimate Edition: Daily by default. Basic Edition and other editions: Every two days by default. |
Use cases | • Emergency response: Quickly investigate newly disclosed high-risk vulnerabilities. • Post-change verification: Verify system security immediately after deploying new applications or updates. | • Routine inspection: For continuous, automated vulnerability monitoring to meet compliance requirements. • Centralized management: Regularly receive vulnerability reports for all assets without manual intervention. |
Vulnerability fixing
Security Center provides a One-click Fix capability that automatically deploys a patch to help you resolve security issues quickly.
Application Vulnerability and Urgent Vulnerability do not support One-click Fix from the console. You must log in to the server and fix them manually, following the suggestions in the vulnerability details.
Vulnerability fix calculation rules
Minimum unit: Successfully fixing one Security Notice on one server counts as one fix.
ImportantA single Security Notice may contain multiple related CVEs. Fixing the notice counts as only 1 fix, regardless of how many CVEs it includes.
Number of vulnerability fixes = Σ (Number of Security Notices with the "Fixed" status on each server)
ImportantA fix is counted only after the server restarts and its status changes to "Fixed". Failed fixes are not counted.
Example:
If you use Security Center to successfully fix 10 different Security Notices on each of 5 servers:
Total vulnerability fixes = 5 servers × 10 Security Notices = 50 fixes
Vulnerability fix priority
When vulnerabilities exist, the Alibaba Cloud vulnerability scoring system (based on CVSS and combined with real-world cloud attack scenarios) helps you prioritize fixes. This system considers a vulnerability's severity, exploit maturity, threat risk, and the scope of affected assets.
Vulnerability Remediation Urgency Score = Alibaba Cloud Vulnerability Score × Time Factor × Environment Factor × Asset Importance Factor.
Alibaba Cloud Vulnerability Score: Evaluates the inherent severity of the vulnerability.
Time Factor: Considers dynamic factors like the vulnerability's disclosure date and the prevalence of exploit methods (value from 0 to 1).
Environment Factor: Assesses the vulnerability's exploitability in the server environment, such as whether it is connected to the public internet (value is dynamically adjusted).
Asset Importance Factor: Adjusts the priority based on the asset's importance setting (Important: 1.5, General: 1, Test: 0.5).
Fix priority and suggestions:
Priority
Remediation Urgency Score
Description
Remediation Suggestion
High
13.5 or higher
Easily exploitable by an unauthenticated remote attacker, leading to system compromise (e.g., arbitrary code execution) without user interaction. Often used by worms and ransomware.
Fix as soon as possible
Medium
7.1 to 13.5
Potentially compromises the confidentiality, integrity, or availability of resources. Typically includes vulnerabilities with high official ratings but are not yet demonstrably exploitable.
Can be fixed later
Low
Below 7.1
Extremely low probability of successful exploitation or no real risk if exploited. Common in source code bugs or vulnerabilities with minor impacts on compliance or business performance.
Can be postponed
Special
-
Urgent Vulnerability and Web-CMS Vulnerability: High-risk vulnerabilities confirmed by Alibaba Cloud security engineers. We recommend you fix them as soon as possible. When the environment factor cannot be obtained due to network issues, the suggestion may display as "Can be postponed."
Fix as soon as possible
Detection rules and data management policy
Rule update schedule
To cover new Security Notices from OS vendors, Security Center regularly updates its vulnerability detection rules.
Vulnerability updates may be delayed during public holidays.
Linux Systems:
High-risk vulnerabilities: Detection rules are added within 48 hours of the OS vendor's announcement.
CVE vulnerabilities: Detection rules are added within 14 days of the OS vendor's announcement.
Windows Systems: CVE vulnerability detection rules are added within 48 hours of Microsoft's announcement.
Data retention policy
To ensure efficient system performance, Security Center automatically cleans up stale vulnerability data.
Active vulnerabilities:
If a vulnerability's status (e.g., Fixed, Fixing Failed, Ignored, Unfixed, Fixing, Verifying) does not change for one year, the system automatically deletes the vulnerability record.Invalid vulnerabilities:
The system automatically deletes a vulnerability record if its status remains Invalid for longer than the retention period defined in Retain Invalid Vulnerabilities For under Vulnerability Settings.
Billing
Security Center offers two billing models for its vulnerability scanning and fixing features: Subscription and Pay-as-you-go. For more details, see Billing overview.
To activate vulnerability scanning and fixing, you must associate your servers with an edition or protection level after purchase. For instructions, see Manage host and container security quotas.
Subscription: Purchase an edition or a Vulnerability Fixing value-added service.
Pay-as-you-go: Purchase Host and Container Security or the Vulnerability Fixing post-paid feature.
The supported feature scope varies by model, as shown in the table below:
Service Model | Service Edition / Protection Level | Manual Scan Scope | Periodic Automatic Scan Scope | Vulnerability Fixing Capability |
Subscription | Enterprise Edition, Ultimate Edition | All | All | Supports fixing Linux, Windows, and Web-CMS vulnerabilities. |
Advanced Edition | All vulnerabilities except Application Vulnerability. | All vulnerabilities except Application Vulnerability. | Supports fixing Linux and Windows vulnerabilities. | |
Basic Edition, Value-added Edition, Anti-virus Edition | Urgent Vulnerability only. | Linux Software Vulnerability, Windows System Vulnerability, Web-CMS Vulnerability. | Important To enable One-click Fix, you must purchase the separate Vulnerability Fix value-added service. For instructions, see Purchase Vulnerability Fixing (Subscription) and Activate Vulnerability Fixing (Pay-as-you-go). After purchase, supports fixing Linux and Windows vulnerabilities. | |
Pay-as-you-go | Host Protection, Host and Container Protection | All | All | |
Unprotected, Anti-Virus | Urgent Vulnerability only. | Linux Software Vulnerability, Windows System Vulnerability, Web-CMS Vulnerability. |
Get started
Purchase and activate Vulnerability Management: Purchase Security Center.
Associate your servers with an edition or protection level: Manage licenses.
Scan for vulnerabilities: Scan for vulnerabilities.
View and handle vulnerabilities: View and handle vulnerabilities.
Troubleshoot failures: Troubleshoot issues that cause vulnerability fixing failures.
FAQ
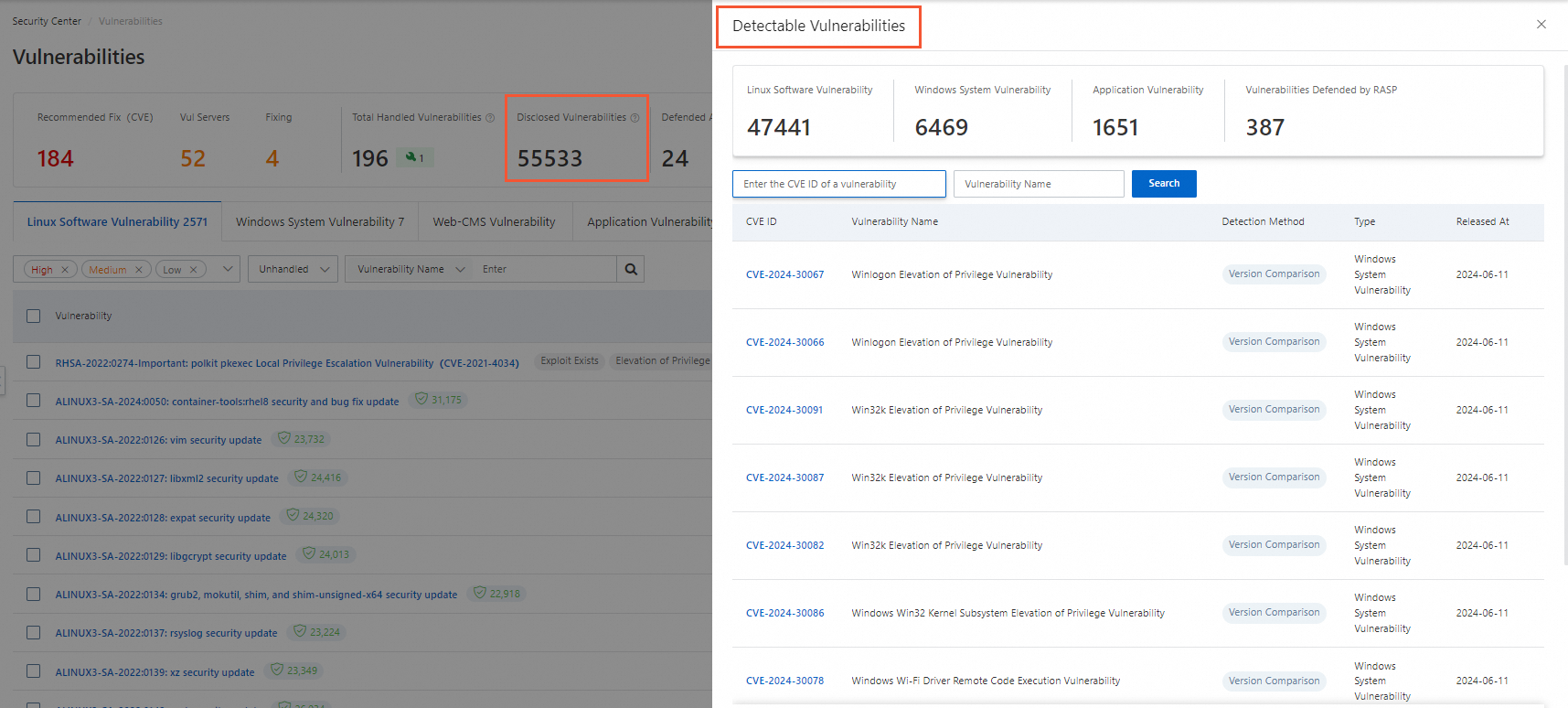
How do I view the vulnerabilities that can be detected?
On the Vulnerabilities page, click the number in the Disclosed Vulnerabilities section to view the list of supported vulnerabilities.
Appendix
Supported operating systems for vulnerability scanning and fixing
OS Type | Version |
Windows Server |
|
CentOS |
|
Red Hat |
|
Ubuntu |
|
Alibaba Cloud Linux |
|
Anolis OS |
|
Debian |
Note Only scanning is supported; fixing is not. |
SUSE | |
Kylin | Kylin Advanced Server OS V10 |
End-of-life OS vulnerability support
For operating systems that have reached End of Life (EOL), Security Center no longer supports scanning, detection, or fixing of Linux Software Vulnerabilities and Windows System Vulnerabilities disclosed after the EOL date.
Scanning and fixing for Web-CMS Vulnerability, Application Vulnerability, Emergency Vulnerability, and other Security Center features are not affected.
OS Version | Official End of Life (EOL) Date | Patch Support Cutoff Date |
Windows Server 2003 | July 14, 2015 | July 14, 2015 |
Windows Server 2008 | January 14, 2020 | January 14, 2020 |
Windows Server 2008 R2 | January 14, 2020 | January 14, 2020 |
Windows Server 2008 SP2 | January 14, 2020 | January 14, 2020 |
Windows Server 2012 | October 10, 2023 | October 10, 2023 |
Windows Server 2012 R2 | October 10, 2023 | October 10, 2023 |
Ubuntu 12.04 LTS | April 28, 2017 | April 28, 2017 |
Ubuntu 14.04 LTS | April 2019 | April 2019 |
Ubuntu 16.04 LTS | April 2021 | April 2021 |
Ubuntu 18.04 LTS | April 2023 | April 2023 |
CentOS 5 | March 31, 2017 | March 31, 2017 |
CentOS 6 | November 30, 2020 | November 30, 2020 |
CentOS 8 | December 31, 2021 | December 31, 2021 |
Red Hat 5 | March 31, 2017 | March 31, 2017 |
Red Hat 6 | November 30, 2020 | November 30, 2020 |