You can store logs in Simple Log Service (SLS) only for regions and virtual private clouds (VPCs) where traffic analysis is enabled. Enabling log storage automatically enables traffic analysis. If you disable traffic analysis, no log data is collected. For more information, see Enable or disable network traffic analysis.
Use cases
For compliance and security reasons, organizations are often required to store and analyze network logs. The private zone resolution log details how domain names are used within your private network. This helps you audit user activity and promptly identify potential security risks.
Private zone resolution logs
A private zone resolution log records DNS query and response activity from endpoints within all VPCs associated with a specific Alibaba Cloud account. Each log entry includes details such as the region, VPC ID, source IP address, destination IP address (DNS server address), queried domain name, record type, and response. The queried domains include both authoritative private domains configured in Private Zone and external public domains. To simplify log collection, management, and analysis in multi-account and multi-region scenarios, Alibaba Cloud DNS and SLS provide a one-click logging feature in the Log Audit application.
A private zone resolution log records domain name queries and responses from internal endpoints. The queried domain names fall into the following four categories:
1. Authoritative zone
Private Zone provides the service in the Alibaba Cloud VPC environment. This service lets you map custom private domain names to IP addresses in one or more VPCs. You can use these custom private domain names to manage Alibaba Cloud resources within your VPC, such as ECS hostnames, SLB instances, and OSS buckets. These private domain names are not accessible from outside the VPC. You can also connect your VPC to a traditional data center with a leased line or VPN. This enables resource sharing between your data center and VPC through private domain names.
2. Cloud product instance domain names
The cloud infrastructure DNS resolves all instance domain names from Alibaba Cloud products.
3. Forwarded external domain names
The forwarding feature forwards domain name resolution requests from a VPC to your data center's DNS system.
4. Recursively resolved public domain names
A public authoritative DNS server is a DNS server configured for a specific public domain name, such as "example.com", at a domain name registry or domain name registrar. These servers manage and resolve authoritative data for root domains, top-level domains, and other domain levels. A public authoritative DNS server resolves only the domain names that it manages and rejects requests for other domain names.
Private zone resolution log fields
1. Request log
Parameter | Description | Example |
dns_msg_flags | The DNS message flags.
| RD |
dns_msg_id | The unique ID for the DNS query. | 30914 |
dst_addr | The destination IP address. | 100.100.2.136 |
dst_port | The destination port. | 53 |
ecs_hostname | The ECS hostname. | iZbp1b1mx9fhe34k***** |
ecs_id | The ECS instance ID. | i-bp1b1mx9fhe34kh**** |
module_type | The module that generated the log. For a request log, this is always
| GLOBAL |
query_name | The queried domain name. | www.example.com. |
query_type | The record type of the query, such as A, AAAA, CNAME, TXT, or MX. | A |
region_id | The region ID. | cn-shanghai |
src_addr | The source IP address. | 192.168.0.1 |
src_port | The source port. | 42071 |
transport | The transport protocol. | UDP |
user_id | The Alibaba Cloud account ID. | 139749398683**** |
vpc_id | The VPC ID. | vpc-bp1eyy43516itw78**** |
edns | Extension Mechanisms for DNS (EDNS). This field can appear in query or response logs. | "flags: DO udp: 1408 CLIENT-SUBNET: 1.1.XX.XX/32/24" |
2. Global response log
Parameter | Description | Example |
answer_rrset | The answer resource record set. | JSON array: ["www.example.com. 600 A 192.168.1.1", "www.example.com 600 A 192.168.1.2", ] |
authority_rrset | The authority resource record set. | JSON array: ["example.com. 600 SOA ns1.example.com. hostmaster.example.com. 2023010101 3600 1200 3600 360" ] |
additional_rrset | The additional resource record set. | JSON array: ["ns1.example.com. 600 A 100.100.2.136"] |
dns_msg_flags |
| QR |
dns_msg_id | The unique ID for the DNS query. | 30914 |
dst_addr | The destination IP address. | 192.168.0.1 |
dst_port | The destination port. | 42071 |
ecs_hostname | The ECS hostname. | iZbp1b1mx9fhe34k***** |
ecs_id | The ECS instance ID. | i-bp1b1mx9fhe34kh**** |
module_type | The module that generated the log.
| GLOBAL |
query_name | The queried domain name. | www.example.com. |
query_type | The record type of the query, such as A, AAAA, CNAME, TXT, or MX. | A |
rcode | The response code.
| 0 |
region_id | The region ID. | cn-shanghai |
resolve_path | The resolution path. This field is included only in global response logs. Values are separated by commas, representing the authoritative fast zone, authoritative normal zone, cache module, forwarding module, and recursion module respectively. 1: Indicates that the request passed through this module. 0: Indicates that this module was skipped. When multi-level CNAME resolution is involved, multiple positions may have a value of 1. | 1,0,0,0,0 |
rt | The response latency:
| 10ms |
src_addr | The source IP address. | 100.100.2.136 |
src_port | The source port. | 53 |
transport | The transport protocol. | UDP |
user_id | The Alibaba Cloud account ID. | 139749398683**** |
vpc_id | The VPC ID. | vpc-bp1eyy43516itw78**** |
edns | Extension Mechanisms for DNS (EDNS). This field can appear in query or response logs. | "flags: DO udp: 1408 CLIENT-SUBNET: 1.1.XX.XX/32/24" |
3. Module response log example
Parameter | Description | Example |
answer_rrset | The answer resource record set. | Json array: ["www.example.com. 600 A 192.168.1.1", "www.example.com 600 A 192.168.1.2", ] |
authority_rrset | The authority resource record set. | Json array: ["example.com. 600 SOA ns1.example.com. hostmaster.example.com. 2023010101 3600 1200 3600 360" ] |
additional_rrset | The additional resource record set. | Json array: ["ns1.example.com. 600 A 100.100.2.136"] |
dns_msg_id | The unique ID for the DNS query. | 30914 |
dst_addr | The destination IP address. | 100.100.2.136 |
dst_port | The destination port. | 53 |
ecs_hostname | The ECS hostname. | iZbp1b1mx9fhe34k***** |
ecs_id | The ECS instance ID. | i-bp1b1mx9fhe34kh**** |
module_type | The module that generated the log.
| AUTH_FAST |
query_name | The queried domain name. | www.example.com. |
query_type | The record type of the query, such as A, AAAA, CNAME, TXT, or MX. | A |
rcode | The response code.
| 0 |
region_id | The region ID. | cn-shanghai |
rt | The response latency:
| 1ms |
src_addr | The source IP address. | 192.168.0.1 |
src_port | The source port. | 42071 |
transport | The transport protocol. | UDP |
user_id | The Alibaba Cloud account ID. | 139749398683**** |
vpc_id | The VPC ID. | vpc-bp1eyy43516itw78**** |
edns | Extension Mechanisms for DNS (EDNS). This field can appear in query or response logs. | "flags: DO udp: 1408 CLIENT-SUBNET: 1.1.XX.XX/32/24" |
Private Zone log audit
1. What is an audit log
Log Audit Service is an application on the Alibaba Cloud Log Service SLS platform. It inherits all the features of Log Service SLS and provides powerful capabilities, such as multi-account management and cross-region collection of logs from various Alibaba Cloud products. The service also allows you to use Resource Directory to centrally and systematically manage and record log information for cloud product instances across multiple accounts.
2. Enabling Private Zone audit logs
The Private Zone Log Audit feature is available in the China (Shanghai), China (Beijing), China (Guangzhou), China (Shenzhen), China (Hangzhou), China (Qingdao), China (Zhangjiakou), Singapore, China (Hong Kong), and China (Shenzhen) Finance regions. If you need this feature in other regions, submit a ticket. The product team will evaluate your request and decide whether to add support.
Log on to the Log Audit application console.
On the Global Settings page, turn on the Log Audit switch for Private Zone and select the Central Project region, such as cn-hangzhou. For more information, see Enable log collection.

3. Other features
Cross-account collection
The powerful cross-account collection capability of Log Audit allows you to centrally collect Private Zone logs from member accounts into a central account in multi-account scenarios. Log Audit supports two types of multi-account management configurations:
Resource Directory management mode
Custom authentication management mode
For detailed configuration steps, see Collect multi-account cloud product logs.
Terraform
Terraform is an open-source tool that provides a command-line interface (CLI) for deploying and version-controlling configuration files on Alibaba Cloud or any other supported cloud. For detailed steps on how to use Terraform to configure log collection for cloud products in Log Audit, see Use Terraform to configure the Log Audit service.
The following example shows how to use Terraform to configure Private Zone log collection:
resource "alicloud_log_audit" "dns_example" {
display_name = "tf-audit-test-dns"
aliuid = "1480************" // The management account.
variable_map = {
"dns_intranet_enabled" = "true", // Enable collection of Private Zone logs.
"dns_sync_enabled" = "true", // Enable synchronization of regional logs to the central project.
"dns_intranet_ttl" = "3", // Storage period for regional logs: 3 days.
"dns_sync_ttl" = "185" // Storage period for centralized logs: 185 days.
"dns_intranet_collection_policy" = "accept tag.env == \\\"test\\\"\\ndrop \\\"*\\\"" // Enable Private Zone logs only for VPC instances with the tag env=test.
}
multi_account = ["1039************"] // Multi-account configuration.
}You can manage the collection of Private Zone logs with fine-grained control. The minimum collection granularity is a VPC instance, which allows you to control log collection for each VPC.
You can manage collection policies in the Log Audit console. The following figure shows an example of a policy configured to collect Private Zone logs only from VPC instances that have the tag key env and the tag value prod. By configuring collection policies, you can implement fine-grained collection management and reduce unnecessary log collection.

Log analysis best practices
The following are some common scenarios for querying and analyzing Private Zone logs. You can also create custom query and analysis statements based on your actual requirements. In addition, you can add the SQL query results to a dashboard, save them as a quick query, or create an alert from them for subsequent analysis and processing.
DNS resolution result types
The distribution of DNS requests for different domain names in a specified VPC during a specific time period.
* and vpc_id: vpc-2ze9dducyc3t6p8aeksb3 |select count(*) as total_req, query_name group by query_name
DNS resolution response time issues
Statistical analysis of DNS resolution response time for a specified VPC, domain name, and query type within a specific time period.
* and vpc_id: vpc-2ze9dducyc3t6p8aeksb3 and query_name: "metrichub-cn-beijing.aliyun.com." and query_type: A | select stddev(__time__) as RT, dns_msg_id GROUP by dns_msg_id
Resolution exception analysis
A customer's Alibaba Cloud ECS server experiences resolution anomalies when querying a domain. The customer enables private zone resolution logs and stores the relevant logs in SLS to further analyze the cause of the anomalies. The SLS log records may contain the following three types of logs: request log, global response log, and module response log.
The analysis process is as follows:
Use the
src_portanddns_msg_idparameters to identify and filter all log entries for a single resolution request.Use the following fields to distinguish between the three log types:
rt: This field is empty for request logs.resolve_path: This field is empty for module response logs.This field is not empty for global response logs.
Example of an error result
Based on the rules above, the first entry is a request log, the second is a module response log, and the third is a global response log.
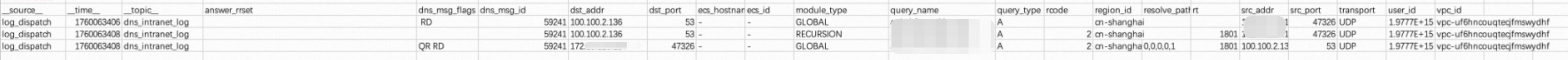
A client sends a DNS request for a recursive query.
The request is sent to the recursive module, but resolution fails.
The server at 100.100.2.136 returns a failure result to the client.
Example of a successful result
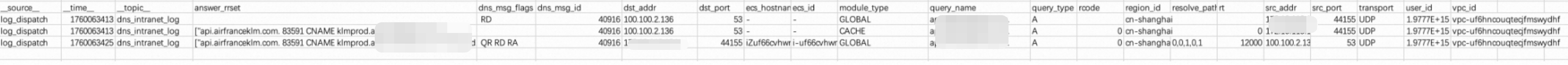
A client sends a DNS request for a recursive query.
The request is sent to the recursive module, and resolution succeeds.
The server at 100.100.2.136 returns the resolution result to the client.