Security hosting eliminates database credentials from your team's workflow. Instead of sharing database accounts and passwords, DMS takes over credential management and enforces fine-grained permission control — so users access only what they're authorized to, and every access is auditable.
How it works
When security hosting is enabled for an instance, the instance enters the logon-free state. DMS stores and manages the database credentials on behalf of your team. Users authenticate through Alibaba Cloud accounts or single sign-on (SSO) and access databases based on their assigned DMS permissions — without ever seeing a database password.

Benefits
After security hosting is enabled:
Logon-free access: Users no longer need database accounts or passwords to connect. DMS manages authentication on their behalf.
Fine-grained permissions: Manage access at the instance, database, table, row, and column levels — not just instance-level logon.
Permission lifecycle management: Set an expiration time for permissions so they are automatically revoked when no longer needed.
Alibaba Cloud account or SSO access: Users authenticate using Alibaba Cloud accounts or SSO instead of per-database credentials.
Sustained connectivity: No more disconnections after 24 hours. Users retain query and change permissions on the instance without re-logon.
Before and after comparison
| Item | Before security hosting | After security hosting |
|---|---|---|
| Database account and password | Required for logon; credentials may be leaked | Not required |
| Session persistence | Logon status may become invalid; disconnects after 24 hours; requires re-logon | No logon required; query and change permissions persist |
| Multi-database access | Separate accounts required per database | Access via Alibaba Cloud account or SSO |
| Permission scope | Instance-level logon permissions only | Instance, database, table, row, and column levels |
| Permission lifecycle | Manual revocation required | Set expiration times for automatic revocation |
| User access | Instance logon permissions must be applied for separately | Regular users apply for query, export, and change permissions based on business needs |
Billing
Security hosting is free of charge.
Considerations
Security hosting is enabled by default for instances managed in Security Collaboration mode. For instances managed in Stable Change or Flexible Management mode, enable it manually.
When enabling security hosting, specify a database account with sufficient privileges so DMS can manage database operations on behalf of users.
Enabling security hosting does not affect existing database connections.
Enable security hosting
DMS administrators and database administrators (DBAs) can enable security hosting from the DMS console 5.0.
For instances not yet registered with DMS
Enable security hosting during registration. For Alibaba Cloud databases, see Register an Alibaba Cloud database instance. For third-party or self-managed databases, see Register a database hosted on a third-party cloud service or a self-managed database.
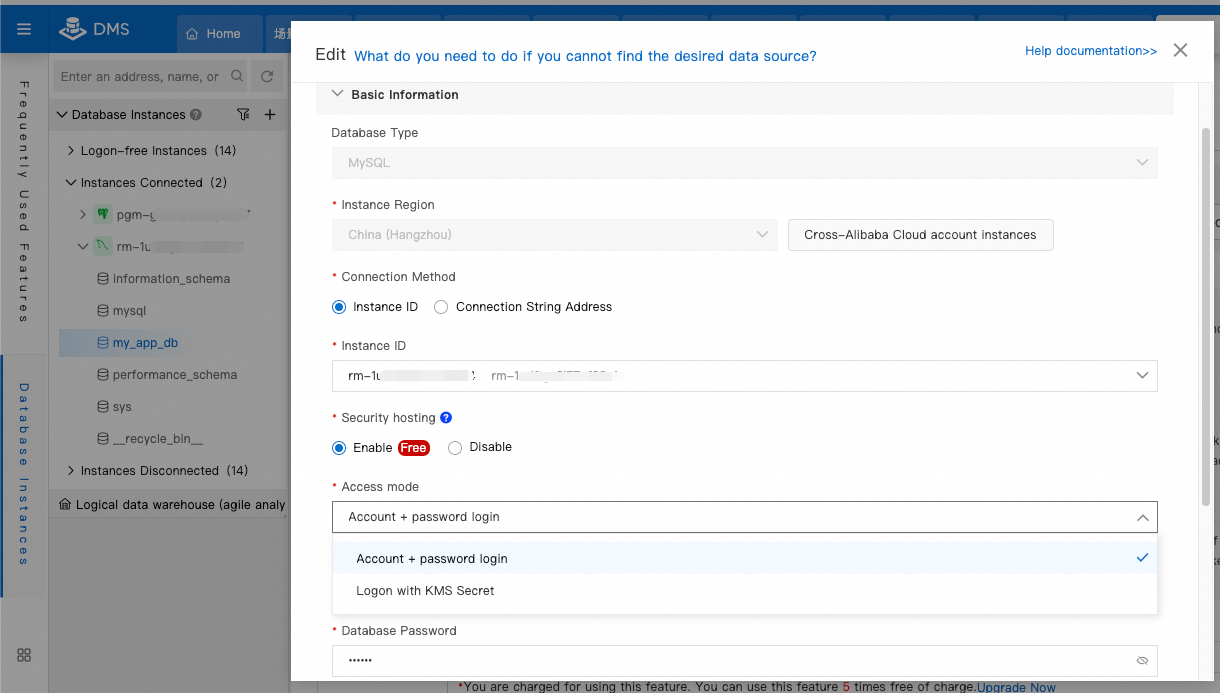
For instances already registered with DMS
In the Database Instances section on the left side of the homepage, right-click the target instance and select Edit.
In the dialog box, enable Security hosting.
For more information, see Modify database instances.
Disable security hosting
To remove an instance from the logon-free state, disable security hosting:
In the Database Instances section on the left side of the homepage, find the database instance that you want to manage and select Edit.
Set the Access mode parameter to Disable Security Hosting (Not Recommended).
After security hosting is disabled, all permission configurations for the instance become invalid. Users must use a database account and password to log in.
More operations
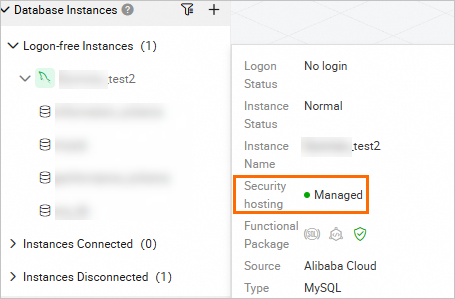
Check whether security hosting is enabled
In the Database Instances section on the left side of the homepage, hover over the target instance to see whether security hosting is enabled.
Grant permissions
DMS administrators, DBAs, and instance owners can grant permissions by right-clicking the target instance or database and selecting Manage Permissions. In the dialog box, assign permissions on the instance, database, or other resources to the user. See Manage permissions.
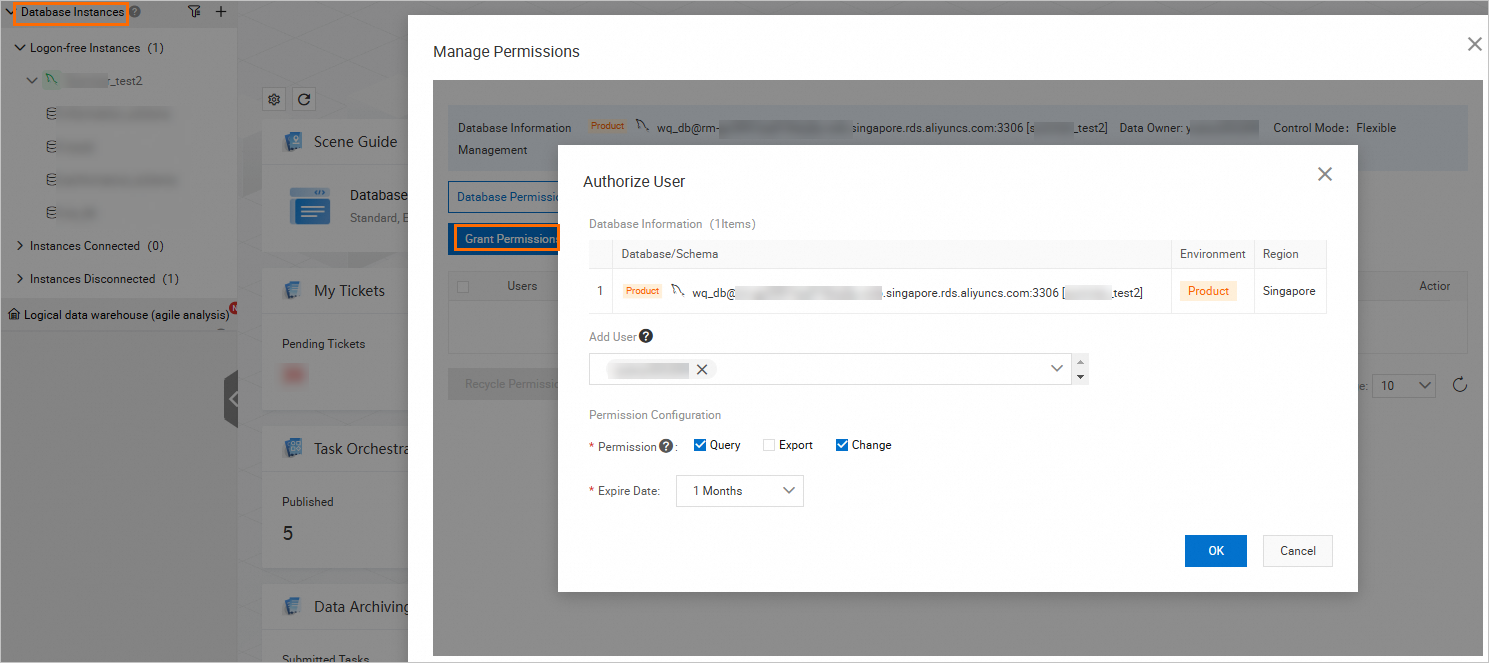
For large teams or many databases, group related resources — such as instances, databases, and tables with the same business purpose — into a permission template and assign the template to users. See Create a permission template. Regular users can also apply for permissions directly. See Submit a ticket to apply for permissions.
View permissions
View your own permissions: View owned permissions.
View other users' permissions as a DMS administrator: Manage permissions as a DMS administrator.
Audit operations
Track permission change operations as a DMS administrator or DBA. See Use the operation audit feature.
FAQ
How do I prevent users from accessing instances they are not authorized to view after security hosting is enabled?
Disable RAM permission verification. Go to O&M > Configuration Management and disable Whether to enable RAM permission verification. This prevents RAM users from performing operations on instances in DMS using existing RAM permissions.

Restrict access based on what you want to control. For more information, see Access control.
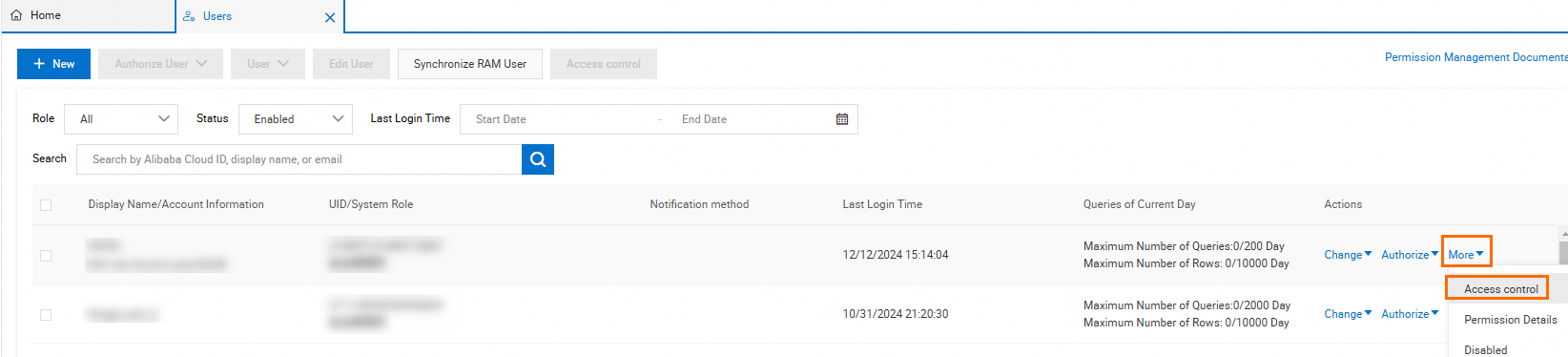
To control which users can see a specific instance: Go to Data Assets > Instances, find the target instance, and choose More > Access control in the Actions column. After access control is enabled, only authorized users can search for the instance.
NoteAccess control is available only for instances managed in Security Collaboration mode.

To control which instances a specific user can see: Go to O&M > Users, find the target user, and choose More > Access control in the Actions column. After access control is enabled, the user can only search for authorized instances or databases.
For more frequently asked questions, see FAQ about security hosting.