In traditional DataWorks node development, accessing external services such as Object Storage Service (OSS) requires configuring plaintext AccessKeys. Hard-coding permanent keys creates a leak risk — a single exposed key can compromise your entire data asset. Managing individual keys per task also leads to overly broad permissions that violate the least-privilege principle. RAM role authorization solves both problems: DataWorks uses Security Token Service (STS) to obtain short-lived temporary credentials dynamically, so no permanent key is stored and each task gets only the permissions it needs.
Solution overview
The setup requires three steps: Create a RAM role → Create an access policy → Grant permissions to a RAM user.
Each step produces one artifact, and all three together form a complete authorization chain:
Step | Artifact | Purpose |
Step 1 | Trust policy on the RAM role | Allows |
Step 2 | Permissions policy on the RAM role | Defines what the role can do (for example, read OSS) |
Step 3 | PassRole policy attached to the RAM user | Allows the user to pass that specific role to DataWorks |
Prerequisites
Before you begin, ensure that you have:
An Alibaba Cloud account or a RAM administrator account with the
AliyunRAMFullAccesspermission
Step 1: Create and configure a RAM role
This role is the identity credential that DataWorks assumes when accessing other cloud resources.
Log in to the Roles page of the RAM console and click Create Role. Keep the default settings, click OK, and enter a descriptive role name such as
DataWorksRAMROLEforDataStudio.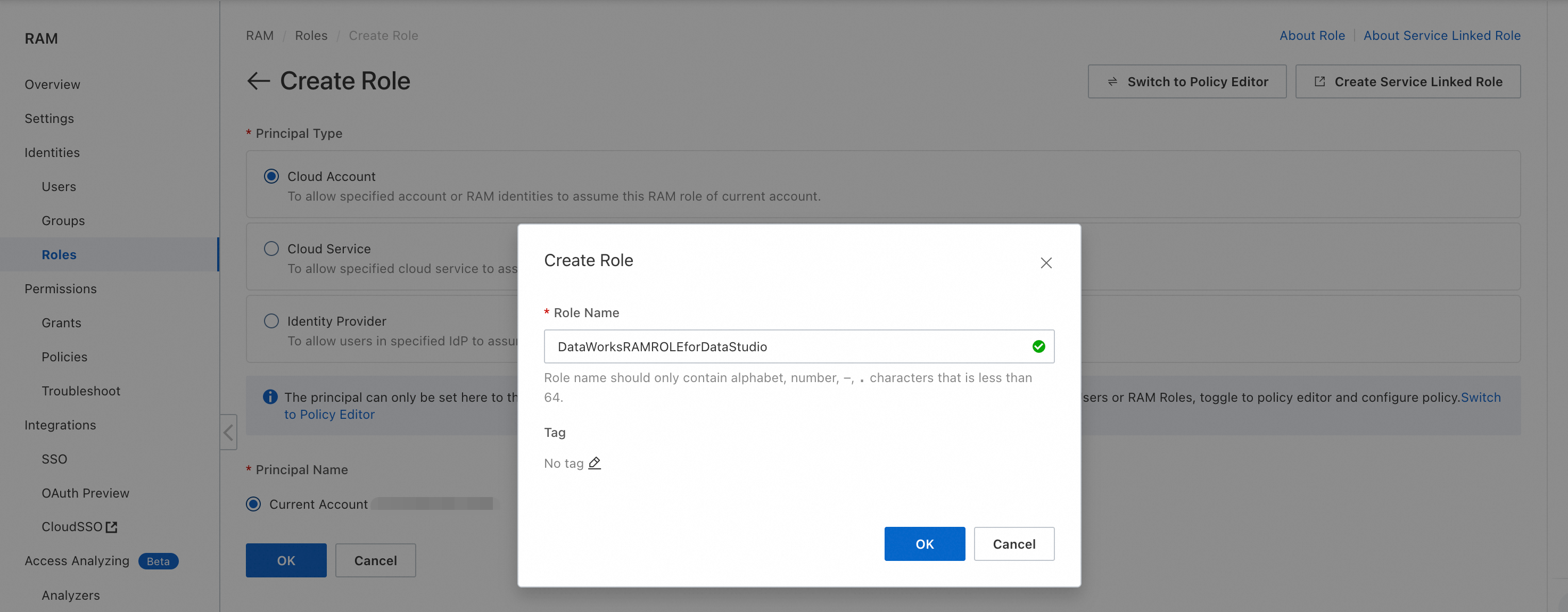
After the role is created, open its details page. On the Trust Policy tab, replace the policy with the following document to allow only
dataworks.aliyuncs.comto assume this role: > For background on editing trust policies, see Modify the trust policy of a RAM role.{ "Version": "1", "Statement": [ { "Action": "sts:AssumeRole", "Effect": "Allow", "Principal": { "Service": [ "dataworks.aliyuncs.com" ] } } ] }Restricting
Principaltodataworks.aliyuncs.comensures that no other service or user can assume this role, even if the role later has broad permissions. Do not use a wildcard (*) here.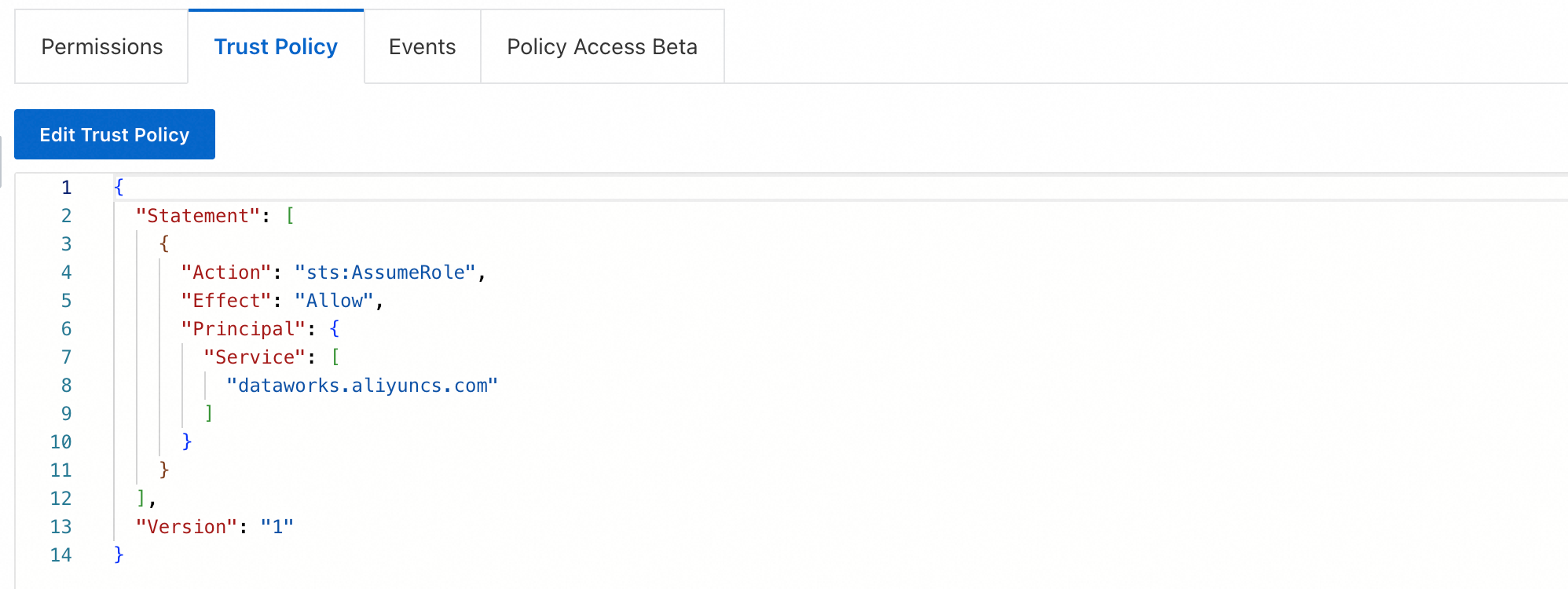
On the role details page, click the Permissions tab, then click Grant Permissions. Attach the permissions the role needs to access target cloud resources. For OSS access, grant
AliyunOSSReadOnlyAccess(read-only) orAliyunOSSFullAccess(full access). > For details, see Manage RAM role permissions.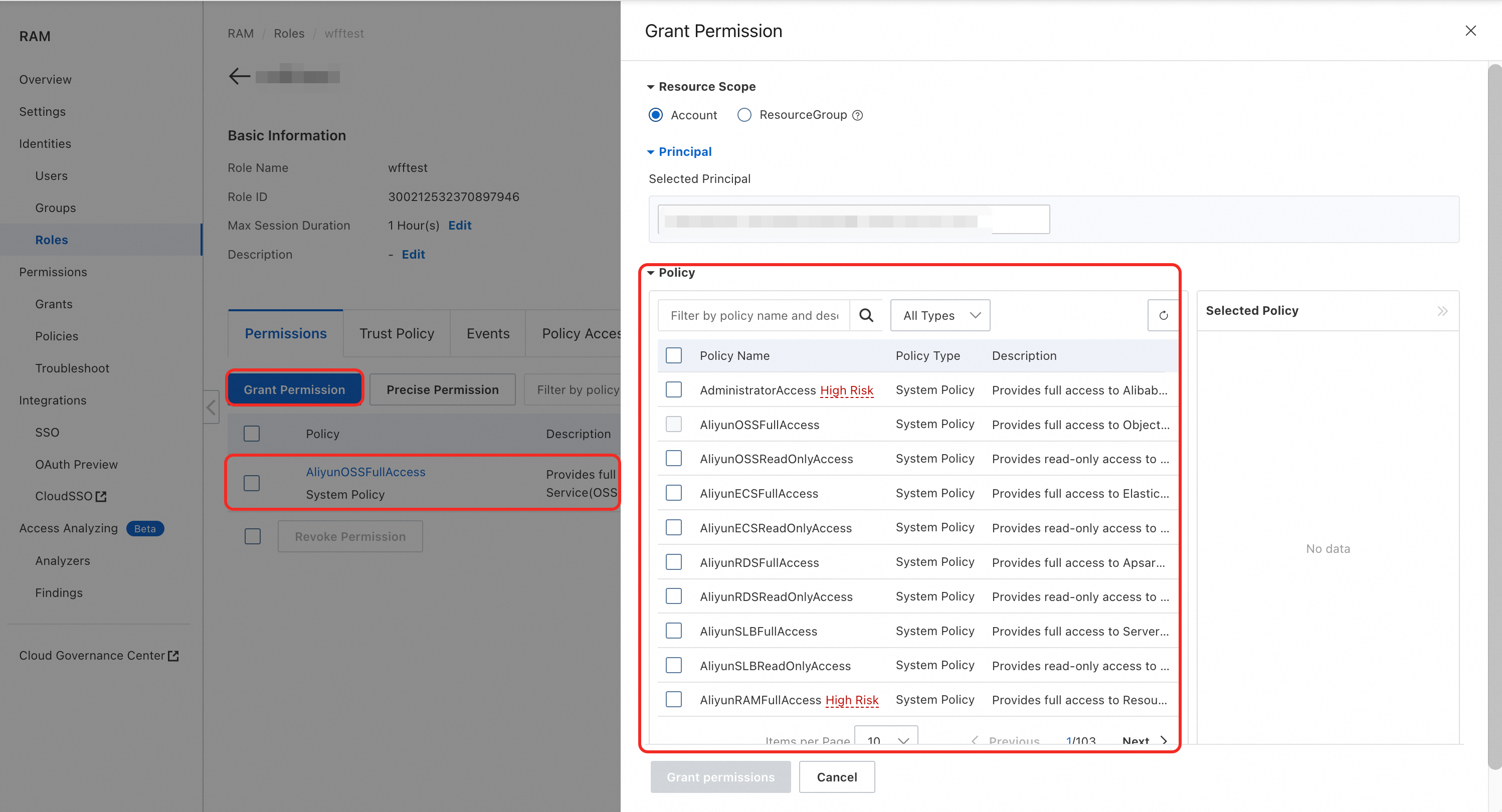
Step 2: Create an access policy
This policy lets a RAM user pass the role created in Step 1 to DataWorks. Without it, the user cannot select or assign the role in the DataWorks console.
Log in to the Policies page of the RAM console and click Create Policy. On the JSON tab, enter the following policy document:
ImportantKeep the
Resourceinram:PassRolescoped to a specific role ARN, not*. GrantingPassRoleon*would let the user pass any role in the account, including ones with permissions that exceed what the user is allowed to have directly.Placeholder
Value
<account-id>Your Alibaba Cloud account UID
<role-name>The RAM role name from Step 1 (for example,
DataWorksRAMROLEforDataStudio)Action
Purpose
ram:ListRolesLets the user view available roles in the console dropdown
ram:PassRoleLets the user pass the specified role to DataWorks — scoped to one exact role ARN
{ "Version": "1", "Statement": [ { "Effect": "Allow", "Action": [ "ram:ListRoles" ], "Resource": "*" }, { "Effect": "Allow", "Action": "ram:PassRole", "Resource": "acs:ram::<account-id>:role/<role-name>" } ] }Replace the placeholders before saving: The two statements serve different purposes: > For details on creating custom policies, see Create a custom policy.
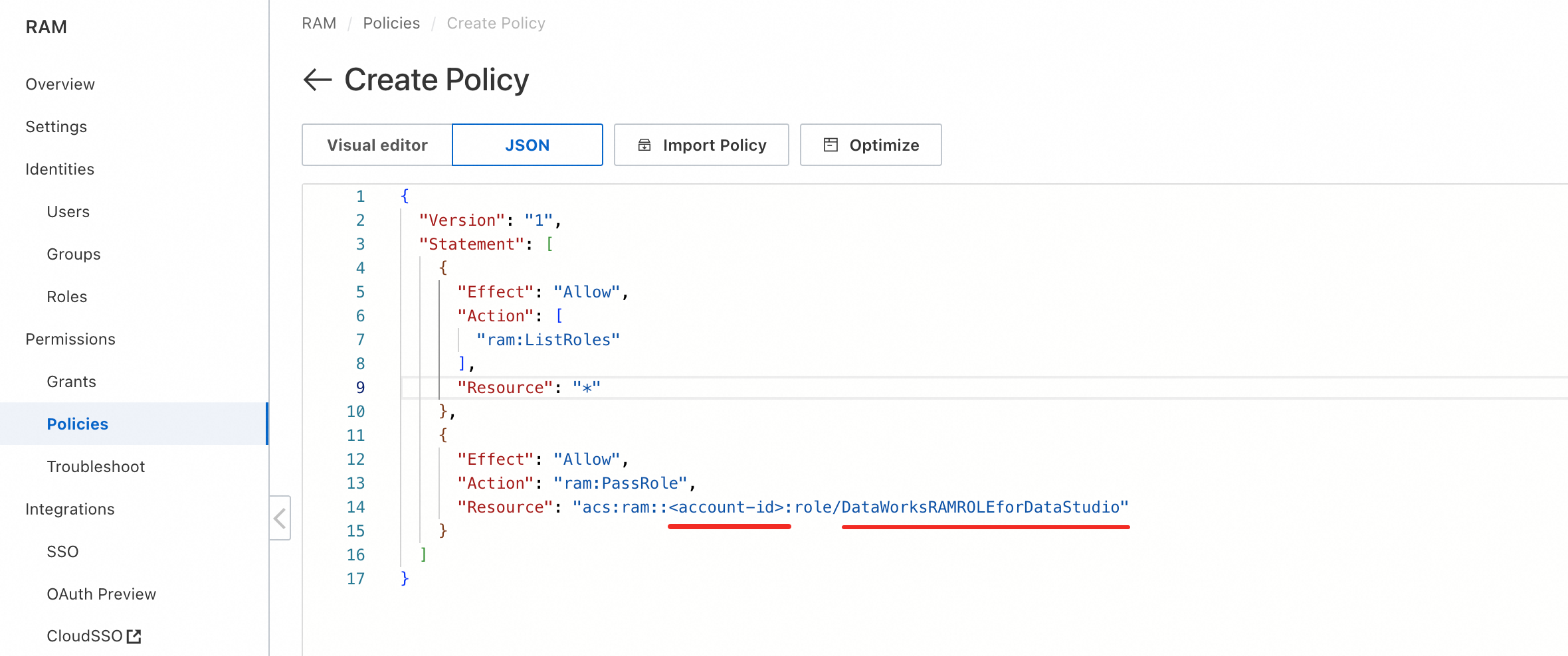
Click OK and name the policy
DataWorksRAMPolicyforDataStudio.
Step 3: Grant permissions to a RAM user
Log in to the Users page of the RAM console. Find the RAM user to authorize (for example,
new_ram_user@...). In the Actions column, click Add Permissions.Search for and select the
DataWorksRAMPolicyforDataStudiopolicy created in Step 2, then click OK.
To authorize multiple RAM users, repeat this step for each user.
What to do next
Log in with the authorized RAM user account and open the new Data Development page. Use the Associated Role feature to assign the role to individual nodes and run tasks. For details, see Configure an associated role for a node in scheduling.
For the list of node types that support associated roles, see the DataWorks console.
