This topic describes how to configure permissions for your digital employees.
This topic applies only to RAM users. If you use an Alibaba Cloud account, you already have full management permissions for digital employees by default. No configuration is required. You can start using digital employees right away.
Permission types
Digital employee permissions fall into two categories. Understanding the difference between them is critical.
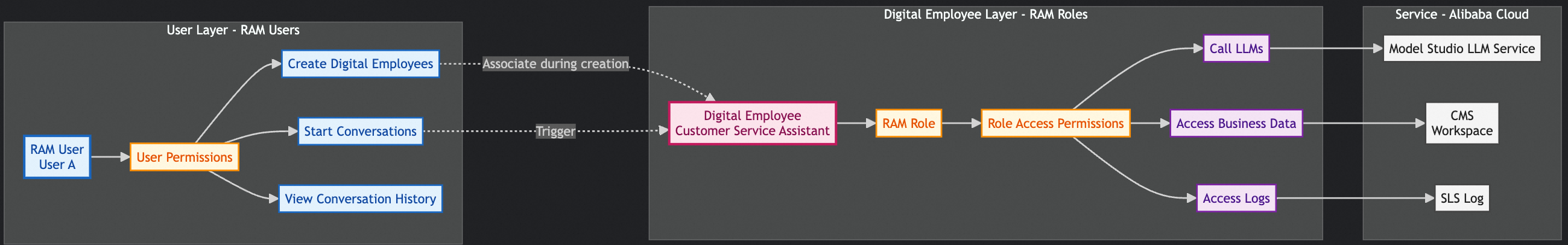
Permissions for digital employee operations
Definition: These permissions allow RAM users—people who actually use digital employees—to perform actions on them.
Scope:
Create, view, modify, or delete digital employees
Chat with digital employees
View chat history
Manage digital employee configurations
Scenarios:
Administrators create and manage digital employees
Regular users chat with digital employees
Developers debug and test digital employees
Authorization object: RAM user
Digital employee access permissions
Definition: These permissions control which resources and data a digital employee can access.
Scope:
Access workspace and entity storage data
Access Simple Log Service (SLS)
Access cloud resource data
Scenarios:
Digital employees need to access business data
Digital employees need to record logs
Authorization object: RAM role (assumed by the digital employee)
Configure permissions for digital employee operations
Log on to the RAM console using your Alibaba Cloud account or a RAM administrator.
Create a custom policy using the script editor (for example, name it digitalemployee-manager-policy). In the script editor tab, use one of the following policies based on your scenario:
Management permissions
Allows users to create, modify, delete, and view digital employees and chats.
{ "Version": "1", "Statement": [ { "Effect": "Allow", "Action": [ "cms:CreateChat", "cms:GetDigitalEmployee", "cms:ListDigitalEmployees", "cms:GetThread", "cms:GetThreadData", "cms:ListThreads", "cms:CreateDigitalEmployee", "cms:UpdateDigitalEmployee", "cms:DeleteDigitalEmployee", "cms:CreateThread", "cms:UpdateThread", "cms:DeleteThread" ], "Resource": [ "acs:cms:*:*:digitalemployee/*", "acs:cms:*:*:digitalemployee/*/thread/*" ] }, { "Effect": "Allow", "Action": "ram:PassRole", "Resource": "*", "Condition": { "StringEquals": { "acs:Service": "cloudmonitor.aliyuncs.com" } } } ] }Read-only permissions
Allows users to view digital employee information, start chats, and view chat history—but not modify or delete digital employees or chats.
{ "Version": "1", "Statement": [ { "Effect": "Allow", "Action": [ "cms:CreateChat", "cms:GetDigitalEmployee", "cms:ListDigitalEmployees", "cms:CreateThread", "cms:GetThread", "cms:GetThreadData", "cms:ListThreads" ], "Resource": [ "acs:cms:*:*:digitalemployee/*", "acs:cms:*:*:digitalemployee/*/thread/*" ] }, { "Effect": "Allow", "Action": "ram:PassRole", "Resource": "*", "Condition": { "StringEquals": { "acs:Service": "cloudmonitor.aliyuncs.com" } } } ] }View-only Digital Employee permissions
Use this policy when users only need to view Digital Employee information—not start chats.
{ "Version": "1", "Statement": [ { "Effect": "Allow", "Action": [ "cms:GetDigitalEmployee", "cms:ListDigitalEmployees" ], "Resource": "acs:cms:*:*:digitalEmployee/*" } ] }Chat-only permissions
Use this policy when users only need to chat—and do not need to manage Digital Employees.
{ "Version": "1", "Statement": [ { "Effect": "Allow", "Action": [ "cms:CreateChat", "cms:GetThread", "cms:GetThreadData", "cms:ListThreads", "cms:CreateThread" ], "Resource": [ "acs:cms:*:*:digitalemployee/*", "acs:cms:*:*:digitalemployee/*/thread/*" ] }, { "Effect": "Allow", "Action": "ram:PassRole", "Resource": "*", "Condition": { "StringEquals": { "acs:Service": "cloudmonitor.aliyuncs.com" } } } ] }Specify a digital employee
Use this policy when users need access to only one specific Digital Employee.
{ "Version": "1", "Statement": [ { "Effect": "Allow", "Action": [ "cms:CreateChat", "cms:GetDigitalEmployee", "cms:ListDigitalEmployees", "cms:GetThread", "cms:GetThreadData", "cms:ListThreads", "cms:CreateThread" ], "Resource": [ "acs:cms:*:*:digitalemployee/<specified-digital-employee-id>", "acs:cms:*:*:digitalemployee/<specified-digital-employee-id>/thread/*" ] }, { "Effect": "Allow", "Action": "ram:PassRole", "Resource": "*", "Condition": { "StringEquals": { "acs:Service": "cloudmonitor.aliyuncs.com" } } } ] }
Configure digital employee access permissions
Create a RAM role with Alibaba Cloud service as the trusted entity:
Trusted entity type: Cloud service
Trusted entity name: Cloud Monitor
NoteAfter creation, verify that the role’s trust policy includes at least
cloudmonitor.aliyuncs.comin the Service field.Create a custom policy (for example, digitalemployee-chat) that grants access to Cloud Monitor and SLS. Example policies:
Allow digital employees to access all required resources and services
{ "Version": "1", "Statement": [ { "Effect": "Allow", "Action": [ "log:Get*", "log:List*" ], "Resource": "acs:log:*:*:*" }, { "Effect": "Allow", "Action": [ "cms:Get*", "cms:List*" ], "Resource": [ "acs:cms:*:*:workspace/*", "acs:cms:*:*:cloudresource" ] } ] }Access only a specific workspace
Scenarios:
Digital employees from different lines-of-business must access only their own workspaces
You need strict control over digital employee data access
Data isolation in multi-tenant environments
{ "Version": "1", "Statement": [ { "Effect": "Allow", "Action": [ "log:Get*", "log:List*" ], "Resource": "acs:log:*:*:*" }, { "Effect": "Allow", "Action": [ "cms:Get*", "cms:List*" ], "Resource": [ "acs:cms:*:*:workspace/<specified-workspace-id>/*", "acs:cms:*:*:workspace/<specified-workspace-id>", "acs:cms:*:*:cloudresource" ] } ] }