If the system policies do not meet your requirements, you can create custom policies for fine-grained permission management.
Prerequisites
Before you create a custom policy, you must be familiar with the basic structure and syntax of the access policy language. For more information, see Access policy structure and syntax.
Introduction to CADT custom policies
Cloud Architect Design Tools (CADT) provides three common custom policy templates that you can configure based on your requirements:
|
Custom policy |
Description |
Sample configuration file |
|
Read-only permission |
Permission to manage CADT in read-only mode |
|
|
Import permission |
Permission to discover and import resources in CADT |
|
|
Management permission |
Permission to manage CADT |
The sample files include permissions for only some products. You can configure the permissions as needed.
Examples
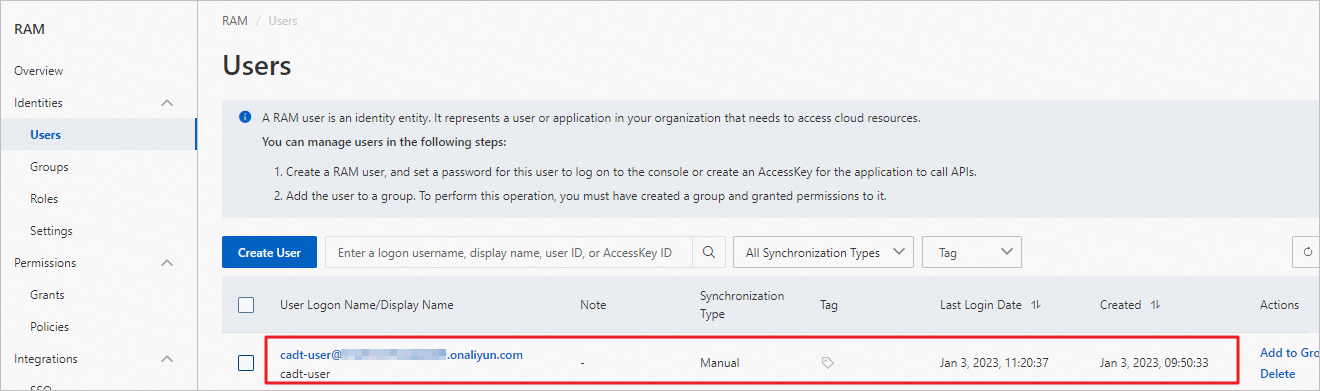
Create a RAM user
-
Log on to the Resource Access Management (RAM) console.
-
Create a test user named `cadt-user`. For more information, see Create a RAM user.
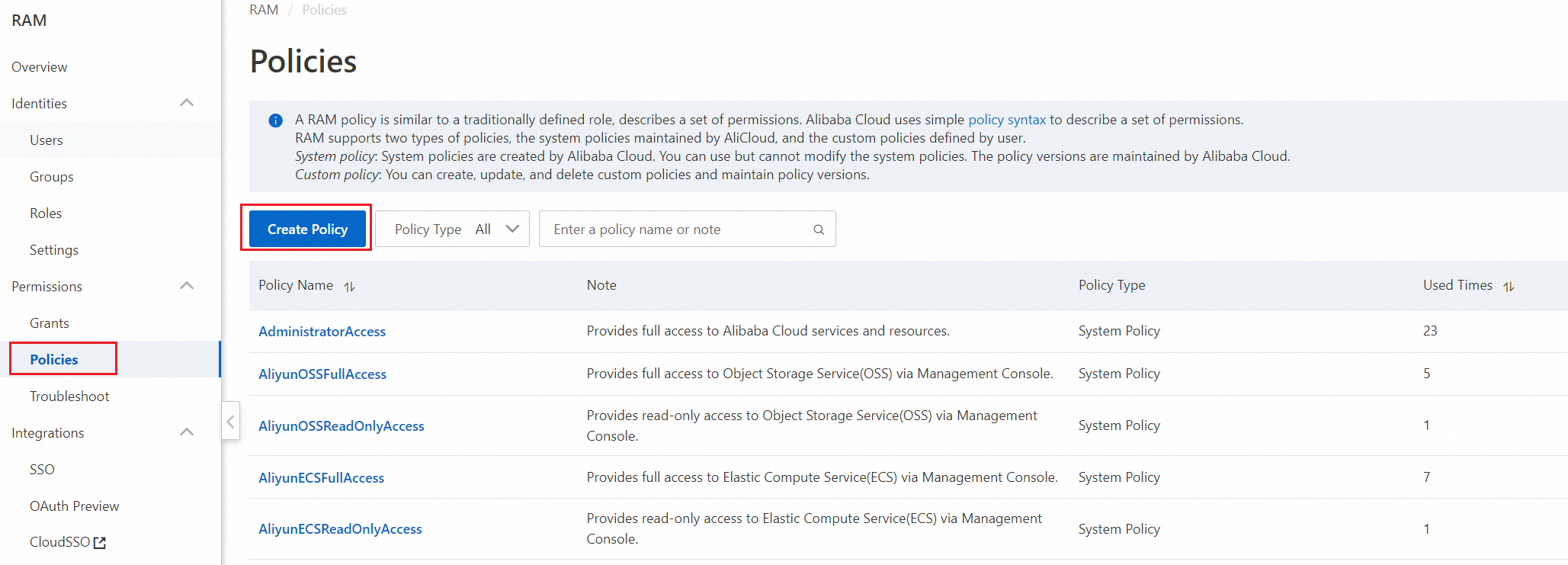
Create a CADT custom policy
-
Create a custom policy that grants read-only permission.
-
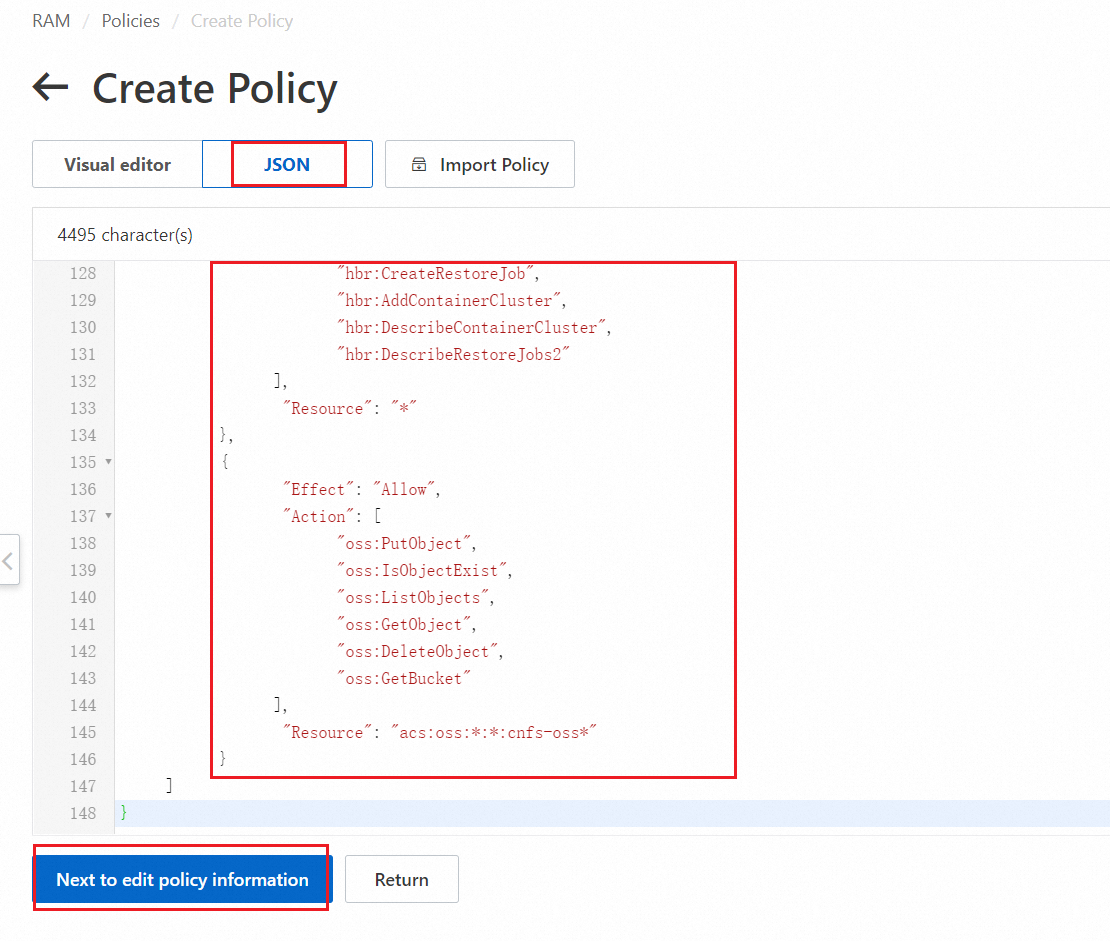
On the Create Policy page, select Script Editor. Copy the content of the read-only permission script into the editor, and then click Continue to edit basic information.
NoteThe script includes read-only permissions for some cloud products. You can modify the script as needed.
-
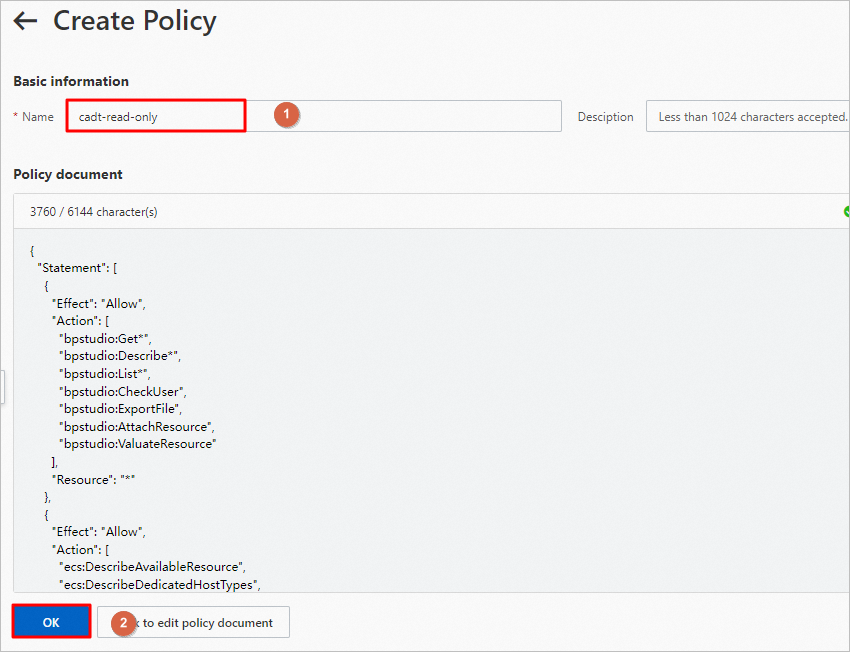
Set the policy name. In this example, set the name to `cadt-read-only`. Then, click OK.
-
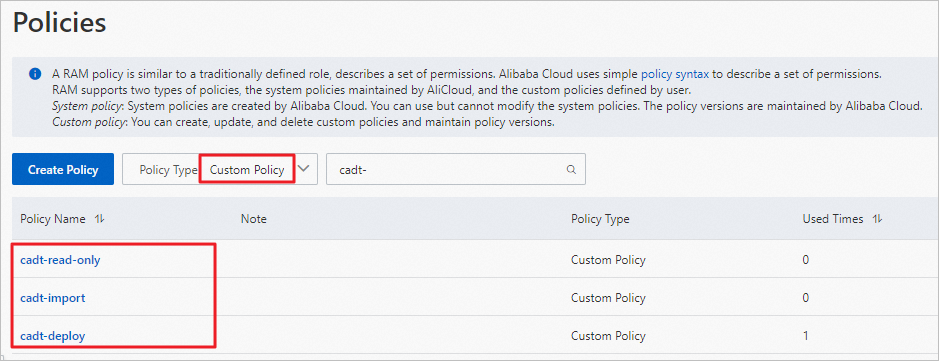
Similarly, create custom policies that grant import permission (named `cadt-import`) and management permission (named `cadt-deploy`).
Permission validation
Validate read-only permission
The read-only permission grants read-only access to CADT applications and Alibaba Cloud resources. For example, you can view applications and architecture graphs in CADT. You can also view information such as Elastic Compute Service (ECS) IP addresses, hostnames, and ApsaraDB RDS database addresses. This permission is useful for daily development and testing.
-
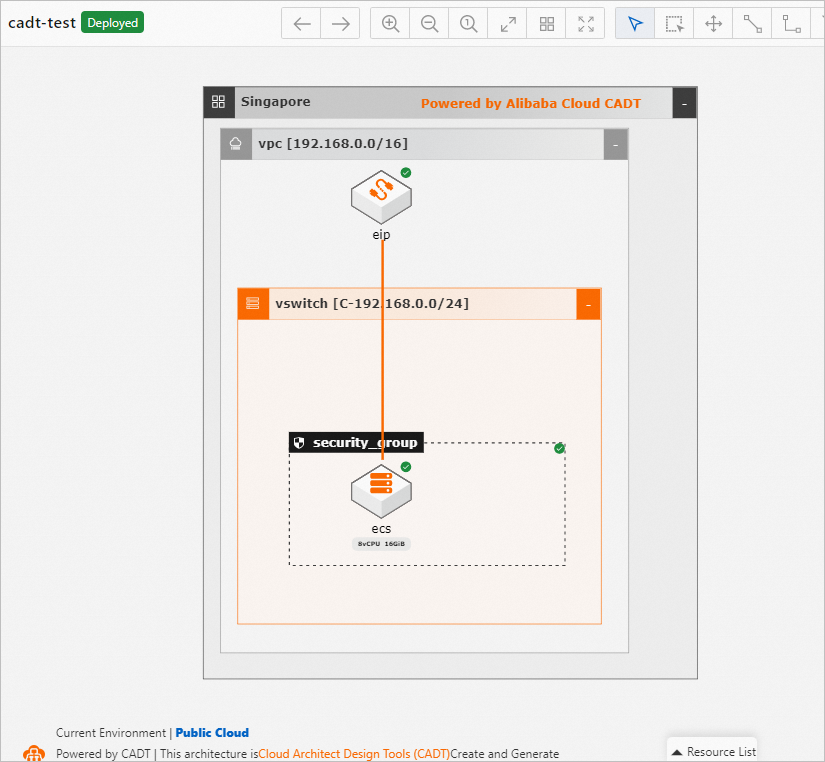
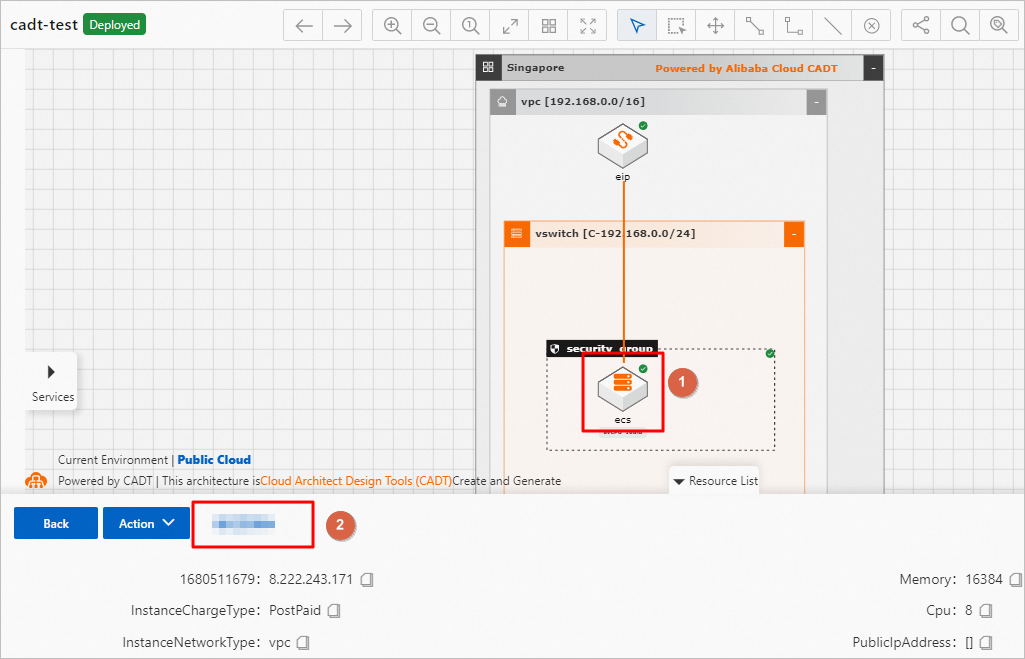
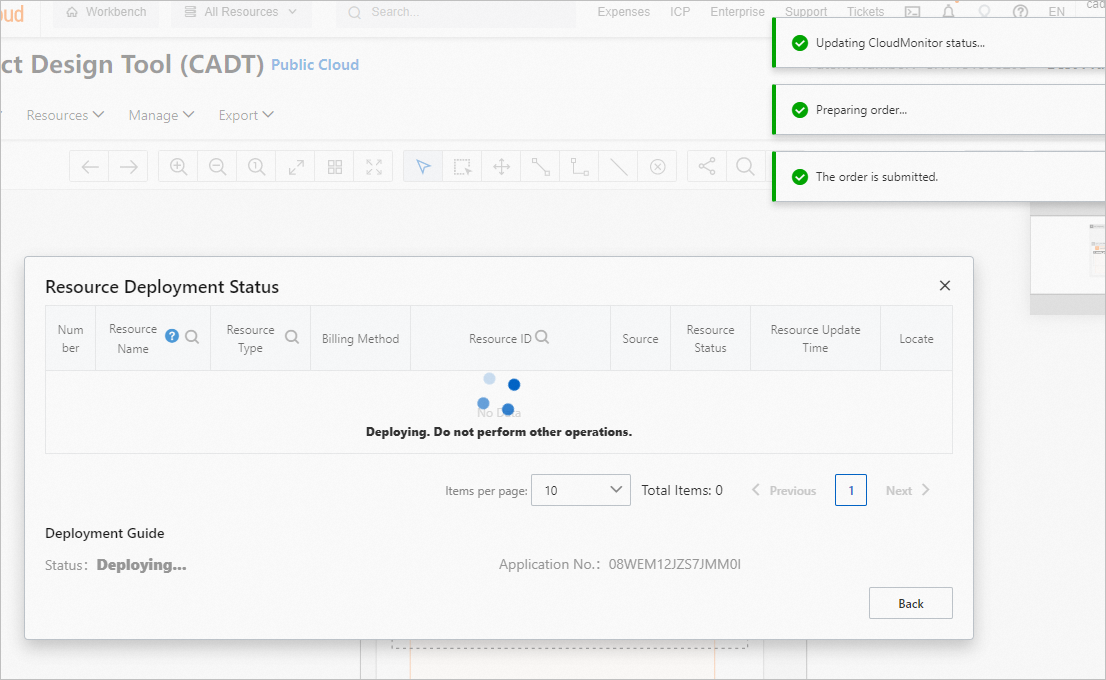
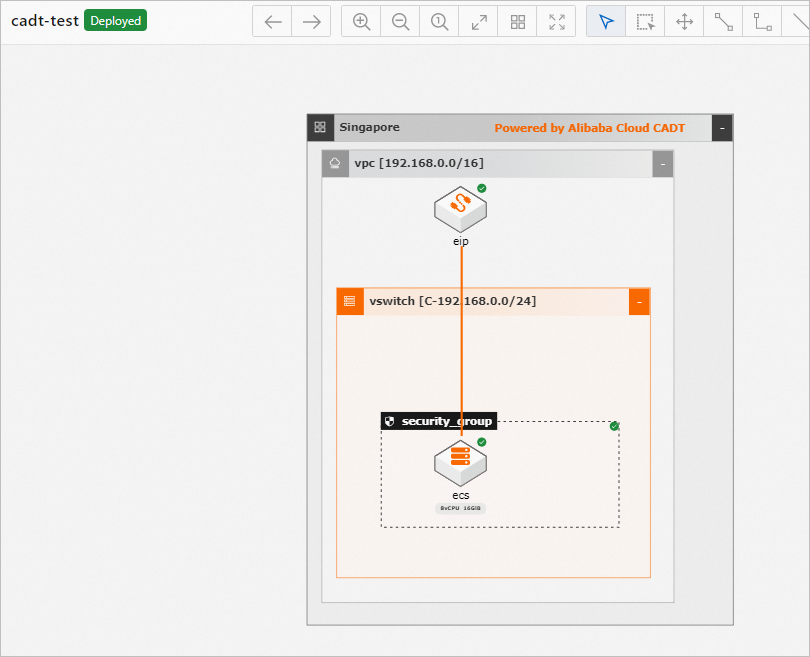
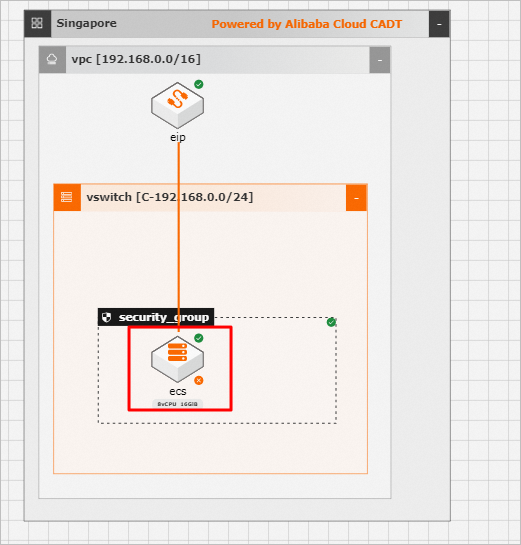
For testing purposes, use your Alibaba Cloud account to deploy a simple application in CADT that consists of an ECS instance and an elastic IP address (EIP). Name the application `cadt-test`.
-
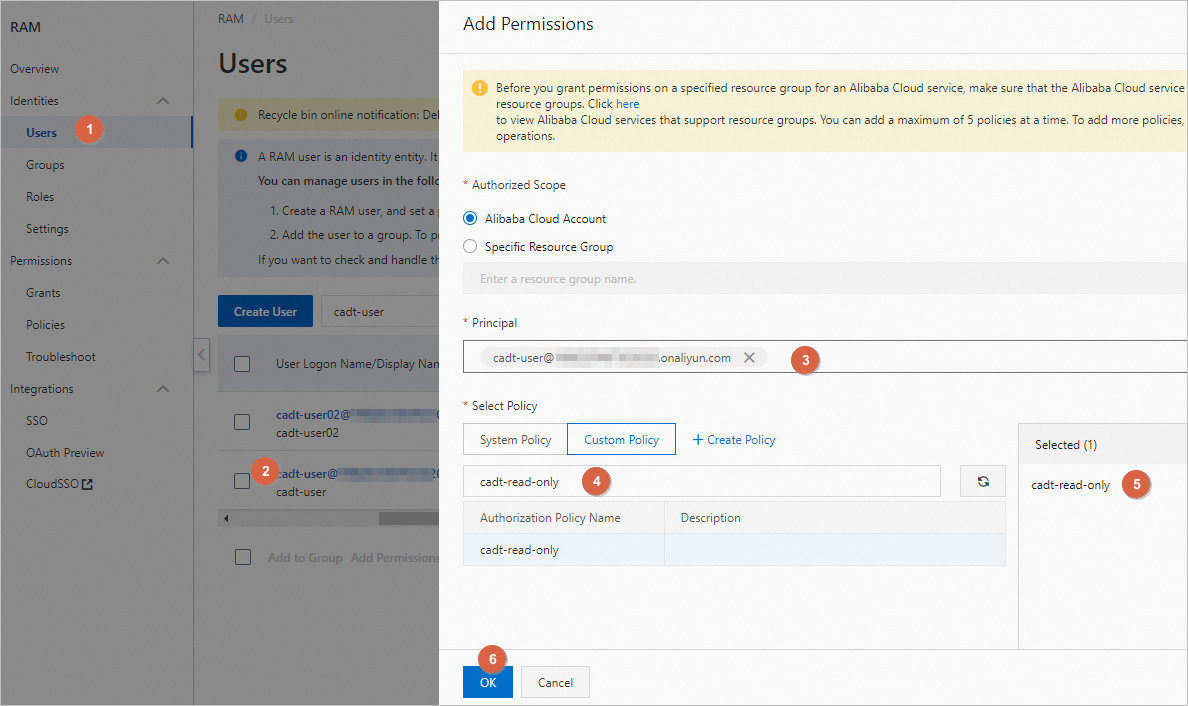
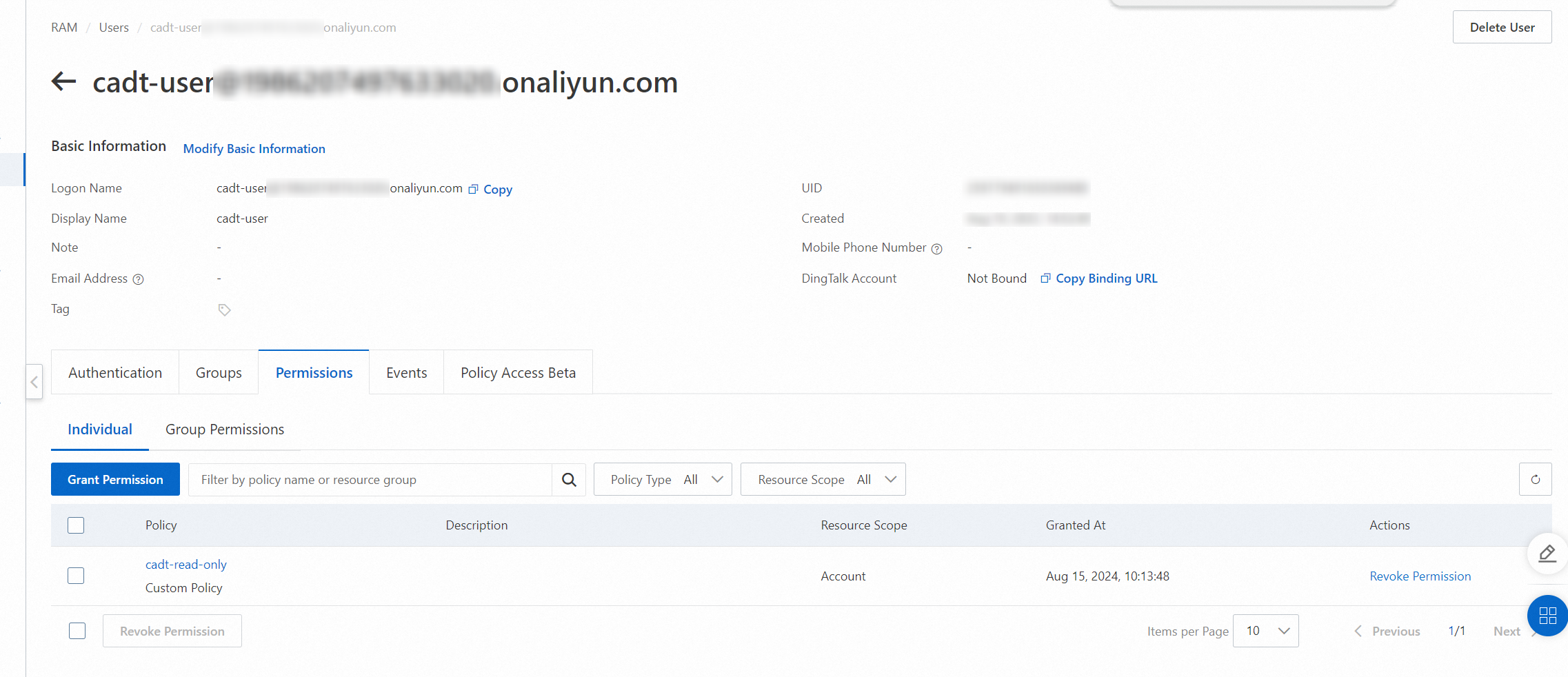
Click the cadt-read-only tag to add the read-only permission.
-
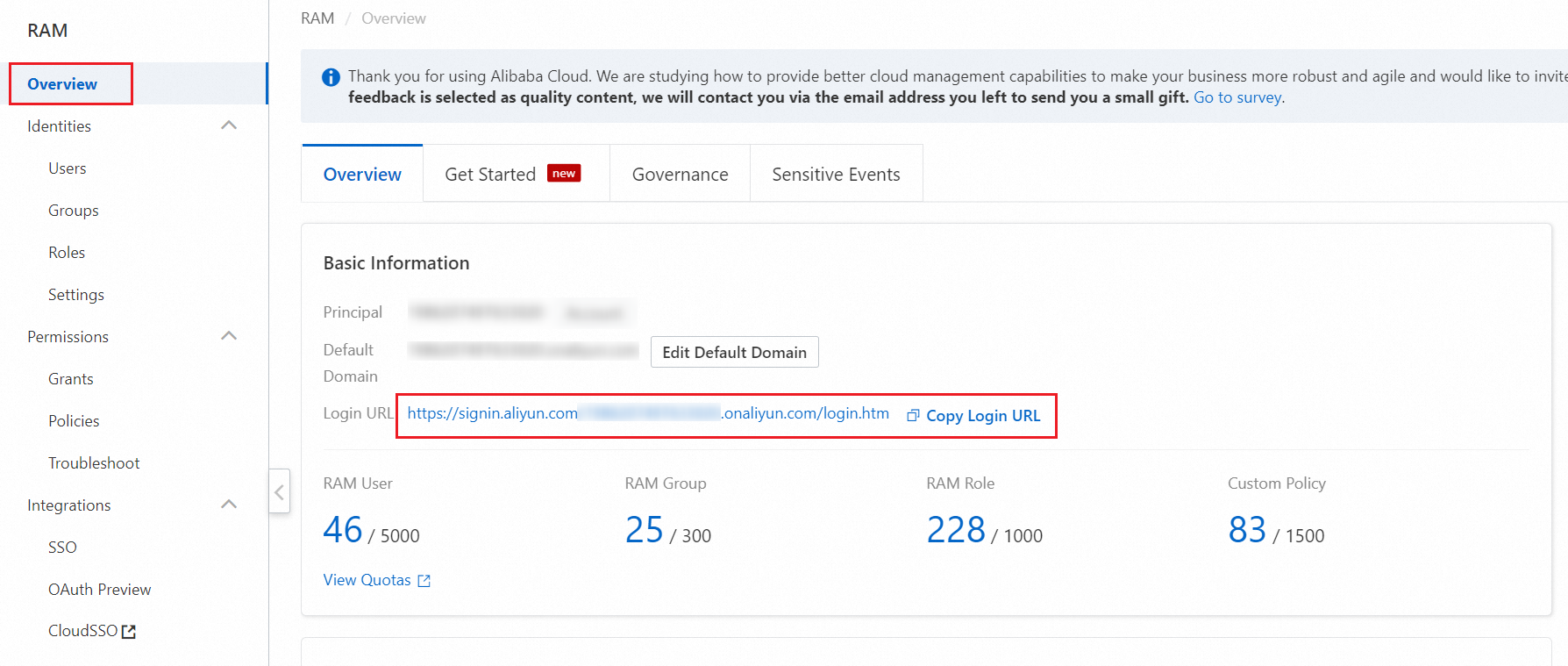
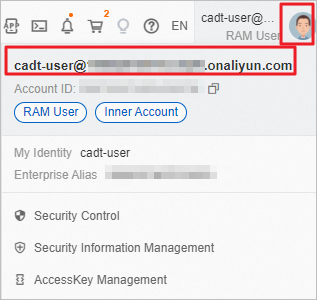
On the Overview page, note the logon URL and log on as `cadt-user`.
-
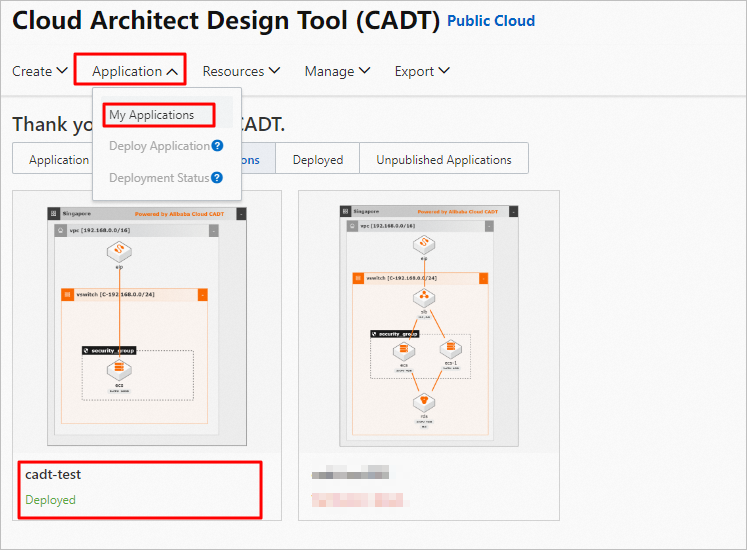
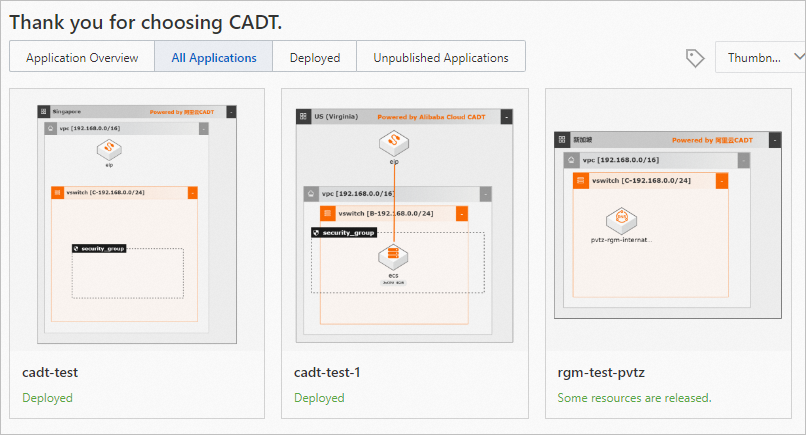
On the My Applications page of the CADT console, you can view the `cadt-test` application that was created by the Alibaba Cloud account, and all other applications.
-
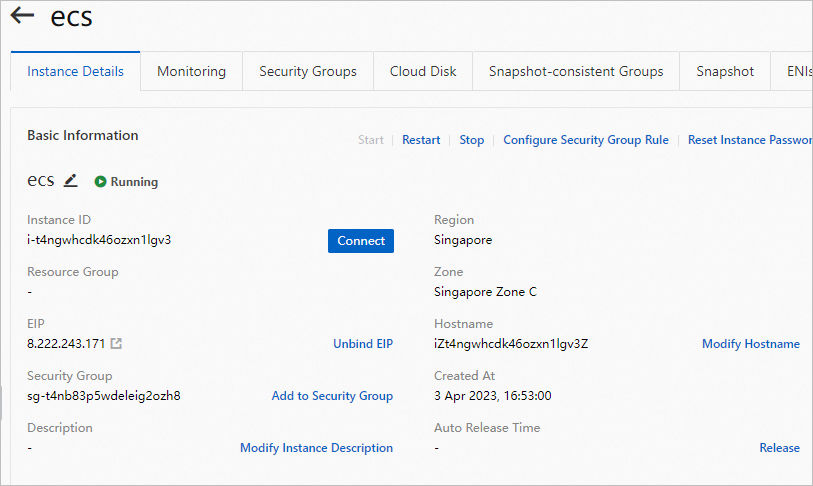
View the details of a resource, such as an ECS instance:
-
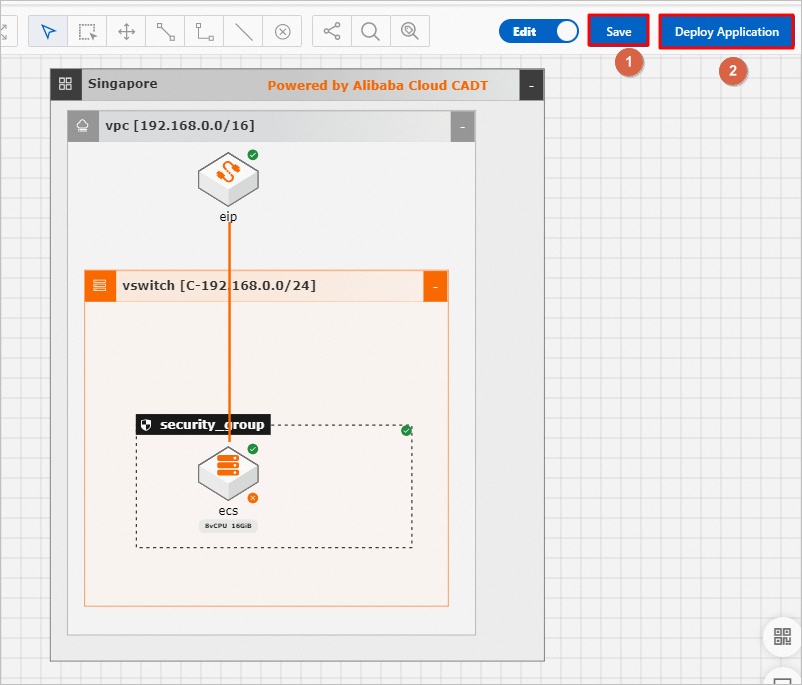
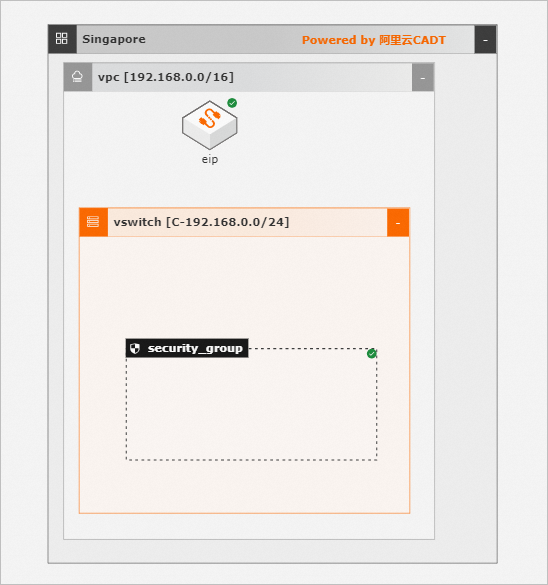
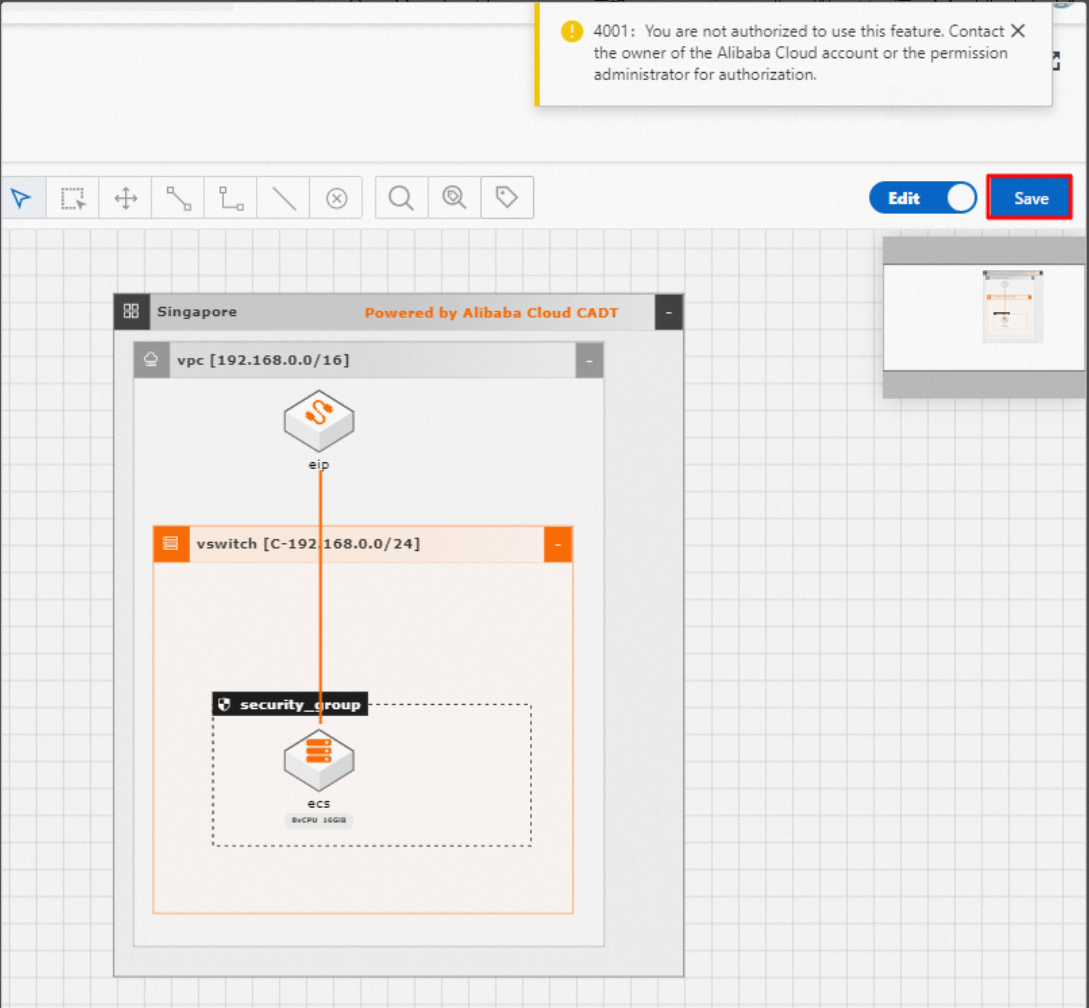
You can create new applications, design architectures, and configure parameters. However, you do not have permission to save or deploy applications.
Validate import permission
The import permission lets you discover resources on Alibaba Cloud, create architecture graphs, and create applications. In CADT, you can also create applications, configure resources, import existing resources, validate resources, estimate costs, and view reports. This permission does not grant permission to deploy resources.
-
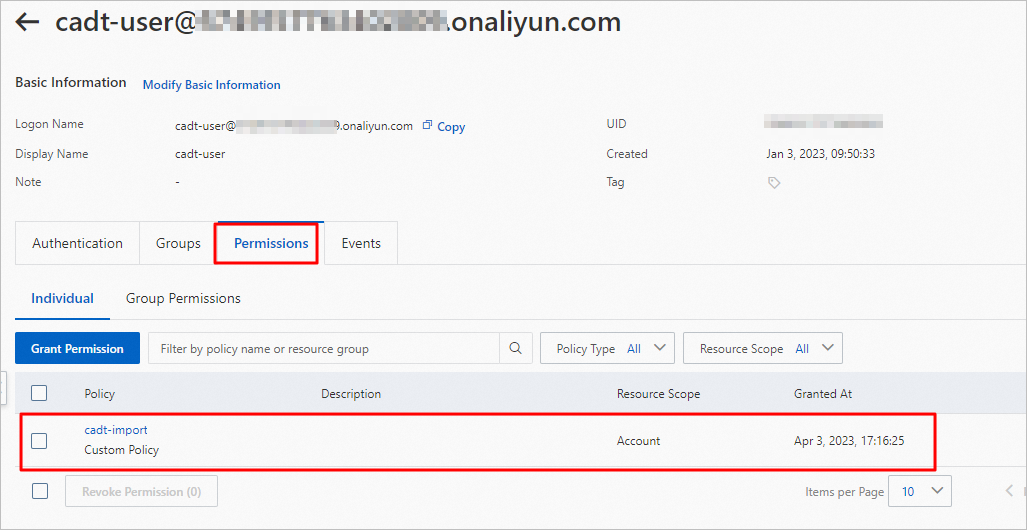
Use your Alibaba Cloud account to revoke the read-only permission from the RAM user `cadt-user` and grant the import permission (`cadt-import`).
-
The permissions in CADT are as follows:
-
Permission to discover resources:
-
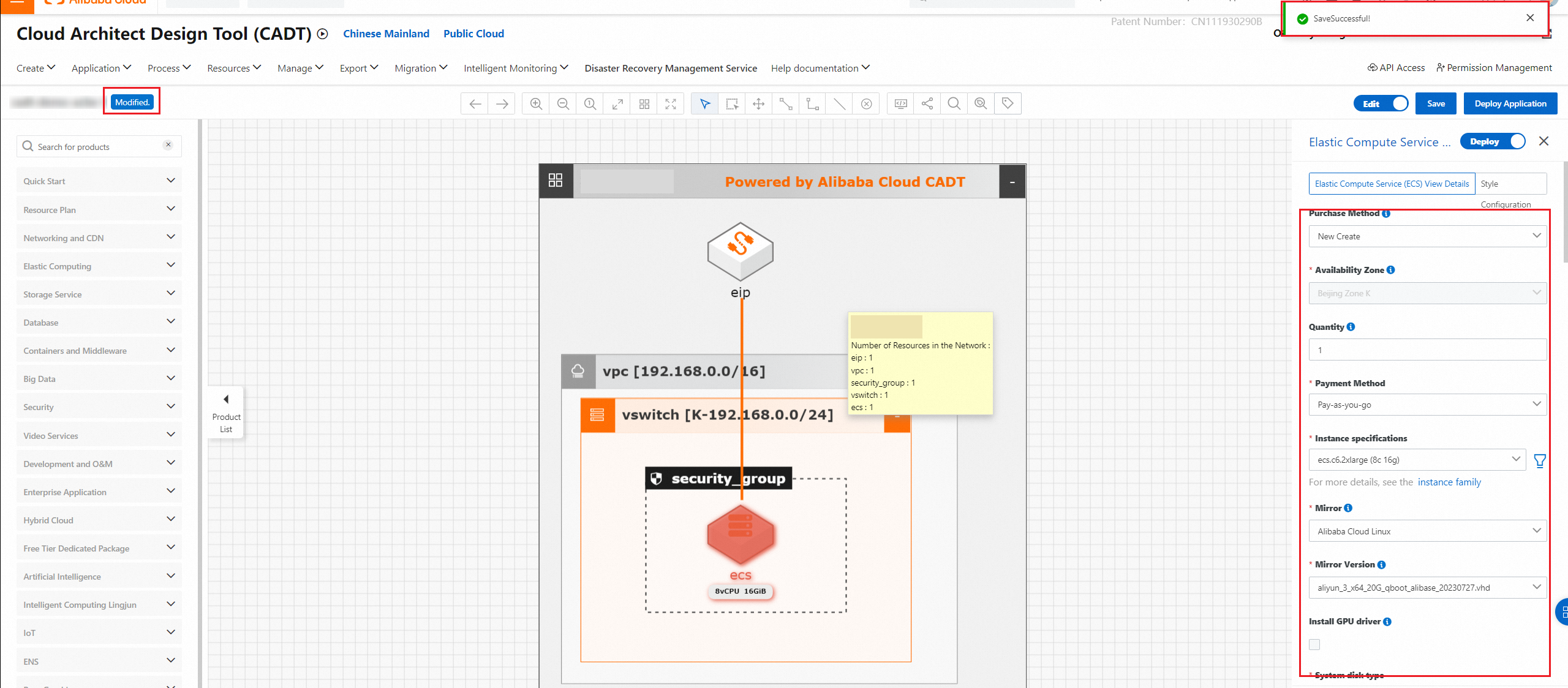
Permission to create applications, configure parameters, and save applications:
-
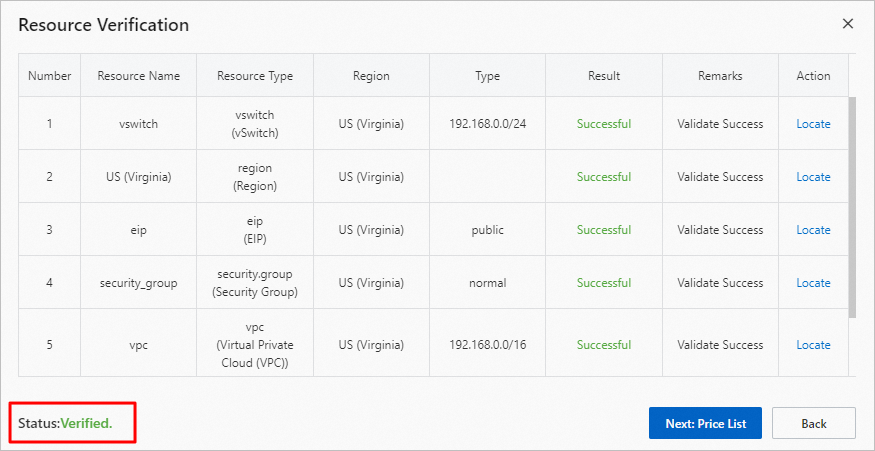
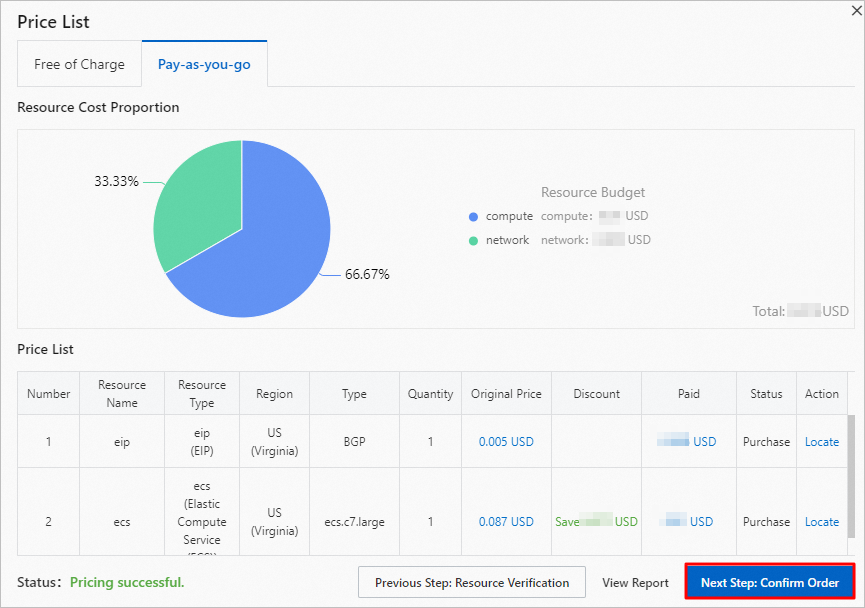
Permission to validate resources:
-
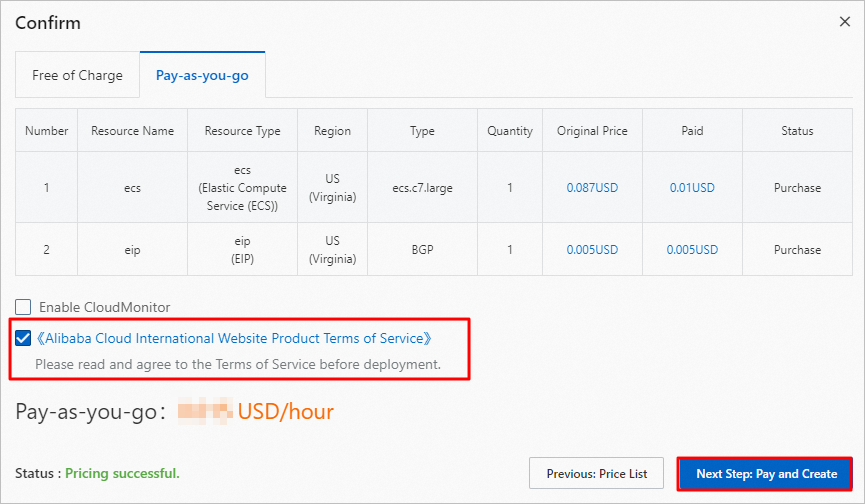
Permission to estimate costs and view reports:
-
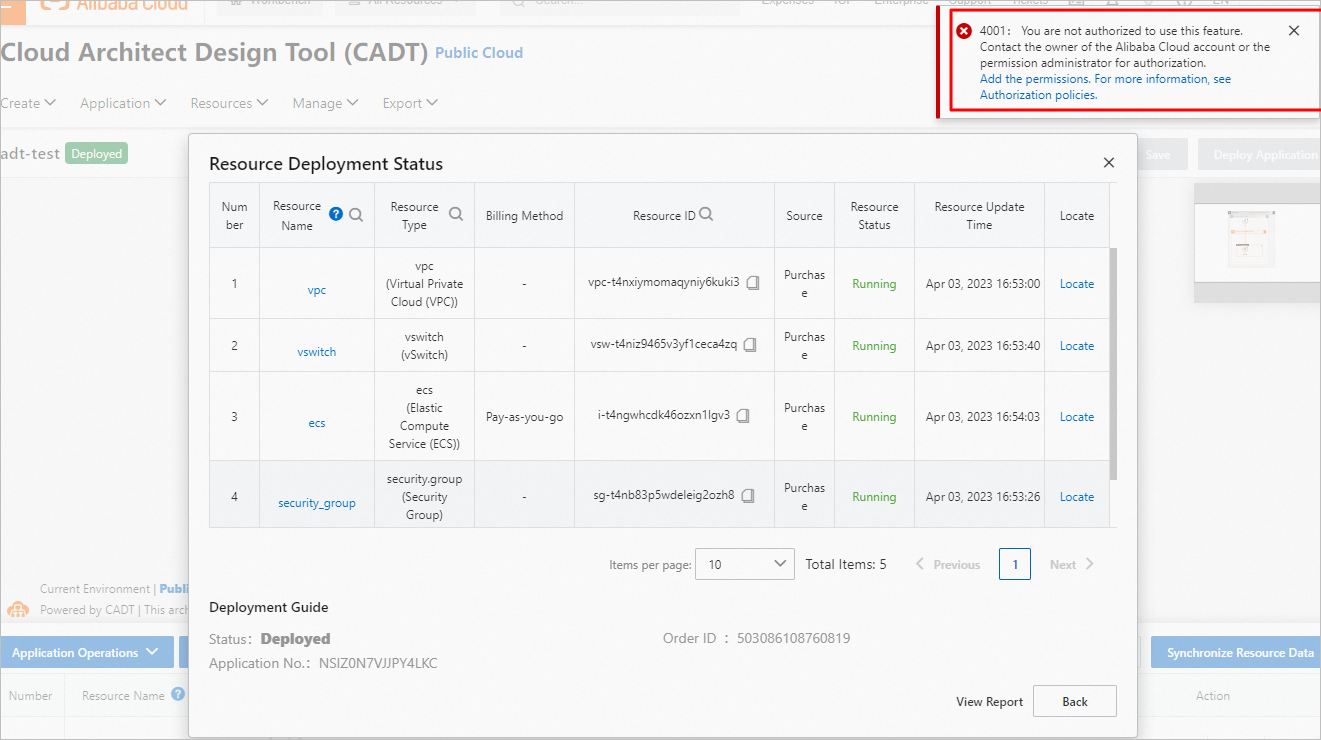
No permission to deploy resources:
-
Permission to import existing resources:
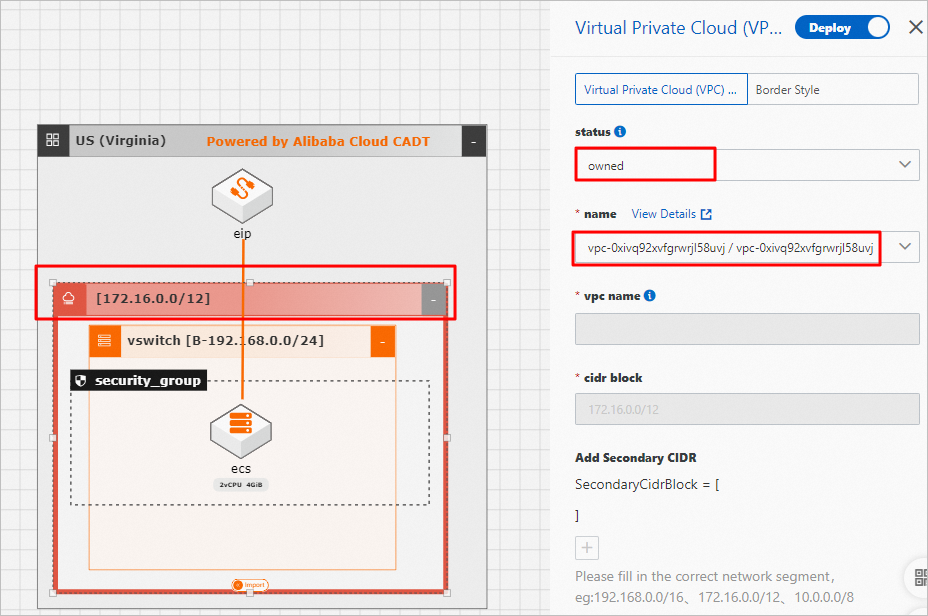
-
Validate management permission
The management permission includes all import permissions, plus the permission to deploy resources. To prevent accidental operations and reduce risks, the one-click release feature is disabled. For daily O&M tasks, you can delete resources individually from the architecture graph.
-
Use your Alibaba Cloud account to revoke other permissions from the RAM user `cadt-user` and grant the management permission (`cadt-deploy`).
-
In addition to all import permissions, this permission also grants the permission to deploy resources.
-
You do not have permission to release all resources with one click.
-
You have the permission to delete resources individually from the architecture graph.
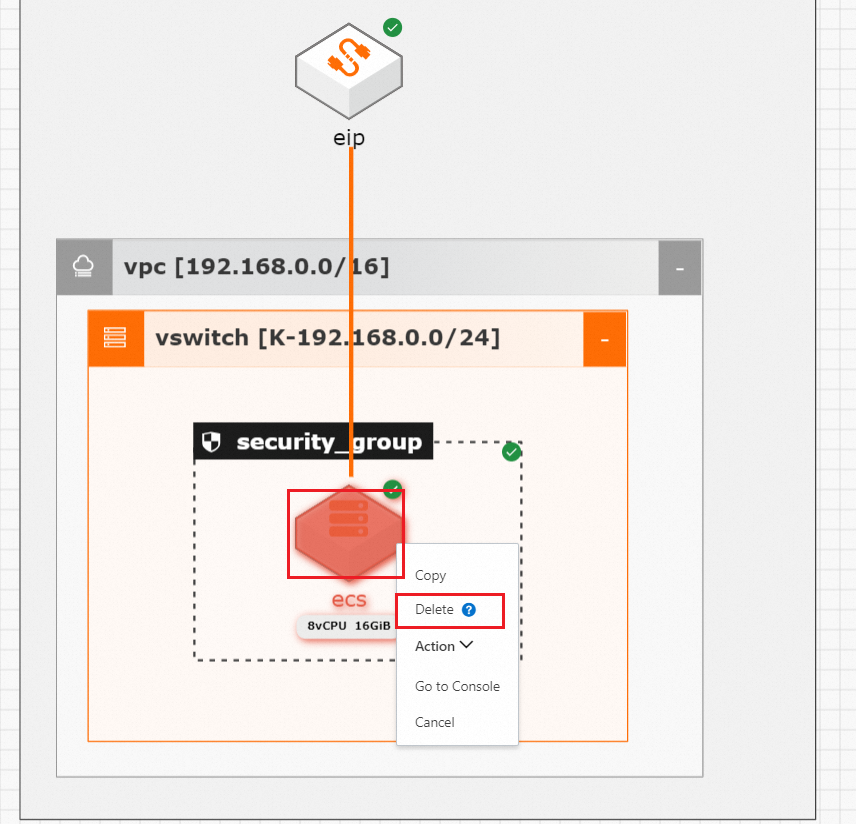
 After you flag a resource for deletion, save and deploy the application. Follow the prompts to release the resource:
After you flag a resource for deletion, save and deploy the application. Follow the prompts to release the resource: