Attribute-Based Access Control (ABAC) lets chaincode and the Hyperledger Fabric runtime make access control decisions based on attributes embedded in a user's enrollment certificate (ECert). When you enroll a user identity, the Certificate Authority (CA) embeds one or more named attributes in the ECert. The chaincode reads those attributes at runtime to allow or deny an operation.
For example, to restrict a sensitive chaincode operation to app administrators only, embed an attribute named app1Admin with a value of true in the administrator's ECert. The chaincode checks for that attribute before executing the restricted operation.
For the full Hyperledger Fabric ABAC specification, see Attribute-Based Access Control.
How it works
Set one or more custom attributes in the Superior options when creating an organization user in the BaaS console.
The CA embeds those attributes in the user's ECert alongside three built-in attributes:
hf.EnrollmentID,hf.Type, andhf.Affiliation.The chaincode reads attributes from the ECert and makes an access control decision.
Set user attributes
Prerequisites
Before you begin, ensure that you have:
An organization in Alibaba Cloud Blockchain as a Service
Permission to create users in that organization
Add attributes when creating a user
Log on to the Alibaba Cloud BaaS console.
On the Overview page, locate My Organizations, find the target organization, and click its name.
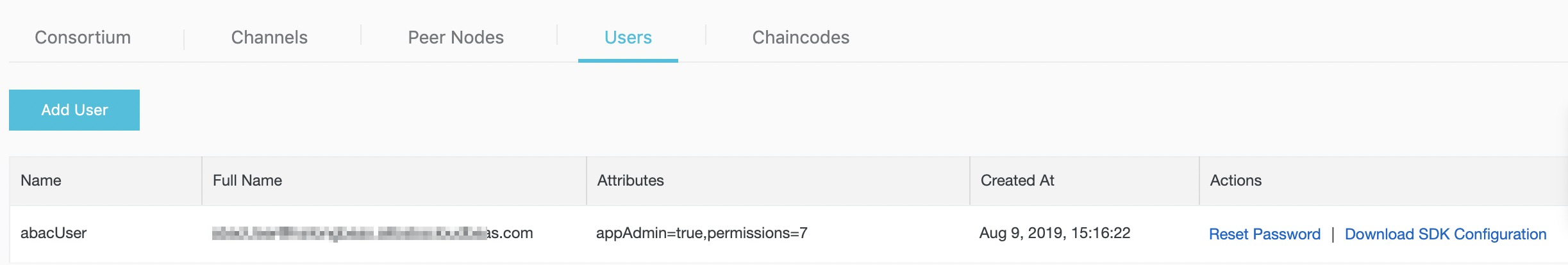
Click Users.
Click Add User, then click Superior and enter the user attributes.
After creating the user, you can check the user attributes.
Attribute format
Attributes are entered as a single comma-separated string using name=value pairs.
Format: name1=value1,name2=value2
Example input:
app1Admin=true,permissions=7The CA processes this input and embeds the attributes in the user's ECert:
{"attrs":{"app1Admin":"true","permissions":"7","hf.Affiliation":"","hf.EnrollmentID":"abacUser1","hf.Type":"client"}}Formatting rules:
| Rule | Detail |
|---|---|
| Attribute separator | Use , to separate multiple attributes |
| Name-value separator | Use = to separate an attribute name from its value |
| Allowed characters | Attribute names and values must consist of English letters or numbers only |
| Value type | All attribute values are stored as strings ("7", not 7) |
Note: The attributeshf.EnrollmentID,hf.Type, andhf.Affiliationare automatically registered for every identity. You do not need to set them manually.
Extract attributes in chaincode
Use the chaincode/shim/ext/cid package to read attributes from the caller's ECert. The package provides two functions for attribute-based access control:
| Function | What it does |
|---|---|
cid.GetAttributeValue(stub, name) | Returns the attribute value and a boolean indicating whether the attribute exists |
cid.AssertAttributeValue(stub, name, value) | Returns an error if the attribute is missing or does not match the expected value |
Use GetAttributeValue when you need the attribute's value for logic. Use AssertAttributeValue when you only need to confirm that the attribute equals a specific value.
Example: check that the caller has `permissions=7`
id, err := cid.New(stub)
fmt.Println("client ID object:")
fmt.Println(id)
if err != nil {
return shim.Error(err.Error())
}
// Get the attribute value
val, ok, err = cid.GetAttributeValue(stub, "permissions")
if err != nil {
return shim.Error(err.Error())
}
if !ok {
return shim.Error("The client identity does not possess the attribute:permissions")
}
// Assert the attribute equals the required value
err := cid.AssertAttributeValue(stub, "permissions", "7")
if err != nil {
return shim.Error("The client identity does not have the permissions")
}
fmt.Println("permissions:")
fmt.Println(val)What's next
Hyperledger Fabric CA User's Guide — detailed reference for attribute registration and enrollment options
chaincode/shim/ext/cidREADME — full API reference for the client identity package