When Cloud Firewall and Bastionhost are deployed together, Cloud Firewall may block the bastion host's traffic by default, making service ports unreachable, preventing asset and user imports, and breaking web page-based O&M and video playback. This topic explains how to configure access control policies on the Internet firewall so Cloud Firewall protects your bastion host's traffic without disrupting its operations.

Prerequisites
Before you begin, ensure that you have:
Cloud Firewall purchased. For more information, see Purchase Cloud Firewall.
A bastion host purchased and enabled. For more information, see Purchase a bastion host and Enable a bastion host.
Policies to create
You need to create four access control policies in total: an allow and a deny-all policy for inbound traffic, and an allow and a deny-all policy for outbound traffic.
Create all four policies and complete all steps. Skipping any policy may leave the bastion host inaccessible or allow unintended traffic.
| Direction | Action | Source | Destination | Ports | Purpose |
|---|---|---|---|---|---|
| Inbound | Allow | Your authorized public CIDR blocks | Bastion host IP address | 60022, 63389, 9443, 443, 20045 | Allow authorized users to reach the bastion host's service ports |
| Inbound | Deny | 0.0.0.0/0 | Bastion host IP address | Any | Block all other inbound Internet traffic |
| Outbound | Allow | Bastion host egress IP addresses | Alibaba credible domains | 443, 80 | Allow the bastion host to reach Alibaba Cloud services it depends on |
| Outbound | Deny | 0.0.0.0/0 | Any | Any | Block all other outbound traffic from the bastion host |
Procedure
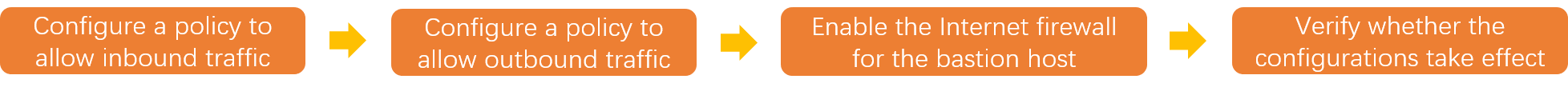
Step 1: Configure a policy to allow inbound traffic
The inbound allow policy controls which external IP addresses can reach the bastion host's open ports (Internet to bastion host). Without this policy, Cloud Firewall blocks all inbound traffic to the bastion host.
Log on to the Cloud Firewall console.
In the left-side navigation pane, choose Prevention Configuration > Access Control > Internet Border.
On the Inbound tab, click Create Policy.
In the Create Inbound Policy panel, click the Create Policy tab, configure the following parameters, and then click OK.
Parameter Value Source Type IP Source The public CIDR blocks authorized to access the bastion host Destination Type IP Destination The IP address of the bastion host's O&M address. To find this IP address, go to the Internet Border page and filter by Asset Type. You do not need to log on to the Bastionhost console. Protocol Type TCP Port Type Port or Address Book. To allow multiple ports, create an address book that contains the ports first, then select it here. Port Specify the ports based on the services your bastion host needs to expose. The following ports cover common use cases: 60022(SSH-based O&M),63389(Remote Desktop Protocol (RDP)-based O&M),9443(video playback),443(host O&M and O&M portal),20045(Bastionhost Assistant)Application ANY Action Allow Description Enter a description to identify the policy Priority Highest Enabling Status Turn on Create a deny-all inbound policy to block all other Internet traffic. Use the same panel to create a second inbound policy. Set Source to
0.0.0.0/0and Priority to Lowest. Keep all other settings consistent with the allow policy.
Step 2: Configure a policy to allow outbound traffic
After configuring the inbound policy, create an outbound allow policy. The bastion host needs to reach Alibaba Cloud services over the Internet for operations such as syncing assets and users and streaming O&M session videos (bastion host to cloud services). Without this policy, Cloud Firewall blocks the bastion host's outbound connections to the services it depends on.
On the Outbound tab, click Create Policy.
In the Create Outbound Policy panel, click the Create Policy tab, configure the following parameters, and then click OK.
Parameter Value Source Type IP Source The egress IP addresses of the bastion host Destination Type Address Book. In the Select Address Book panel, select Cloud Service Address Book and search for Alibaba credible domains. This address book contains the Alibaba Cloud service endpoints the bastion host needs to function. Protocol Type TCP Port Type Port or Address Book. To allow multiple ports, create an address book that contains the ports first, then select it here. Port 443and80Application HTTP and HTTPS Action Allow Description Enter a description to identify the policy Priority Highest Enabling Status Turn on Create a deny-all outbound policy to block all other outbound traffic from the bastion host. Use the same panel to create a second outbound policy. Set Source to
0.0.0.0/0and Priority to Lowest.
Step 3: Enable the Internet firewall for the bastion host
After creating all four policies, enable the Internet firewall for the bastion host to put the policies into effect.
In the left-side navigation pane, click Firewall Settings.
On the Internet Firewall tab, find the IP address of the bastion host and click Enable Protection in the Actions column.
If the bastion host was recently purchased, its information is synced to Cloud Firewall after approximately 15 to 30 minutes. If the bastion host does not appear in the list, wait and refresh the page.
After you complete the preceding configurations, the bastion host is protected by Cloud Firewall, and the workload of the bastion host is not affected by Cloud Firewall. You can log on to the bastion host to import assets and users for O&M and audit.
Step 4: Verify the configurations
Confirm the configurations are working correctly by checking that all of the following work as expected:
Access the service ports of the bastion host
Import assets and users
Perform web page-based O&M
Play videos
To review the traffic logs, go to the Traffic Logs tab on the Log Audit page of the Cloud Firewall console. For more information, see Log audit.