Bastionhost cannot audit secure copy (SCP) operations natively. To make SCP file transfers auditable, configure ProxyJump on your local machine so that SCP traffic is routed through the bastion host before reaching the target host.
How it works
ProxyJump, supported by OpenSSH 7.3 and later, forces SCP traffic to pass through an intermediary. When the SSH client connects to a target host via ProxyJump:
The SSH client establishes a secure connection to the bastion host.
The bastion host forwards the connection to the target host.
Because the SCP traffic passes through the bastion host, the bastion host can audit SCP-based operations.
This is what makes session audit possible: traffic passes through the bastion host, not around it.
Prerequisites
Before you begin, ensure that you have:
An on-premises client that can connect to the bastion host. For troubleshooting connection issues, see FAQ about connections between clients and bastion hosts.
Target hosts and host accounts added to and managed by the bastion host. See Add hosts and Manage a host account.
A bastion host user authorized to manage the target host. See Authorize a user to manage hosts or Authorize a user to manage host groups.
OpenSSH 7.3 or later installed on the client.
Configure ProxyJump
Log in to the on-premises Linux machine.
Run the following command to create the
configfile in the~/.sshdirectory and configure the parameters:vim ~/.ssh/configAdd the following configuration blocks. Replace the placeholder values with your actual bastion host and target host details.
# Bastion host Host bastion # Operations and maintenance (O&M) address of the bastion host. # Find this value in the Bastionhost console under connection settings. HostName <your-bastion-host-om-address> # Example: xxxx-public.bastionhost.aliyuncs.com Port 60022 # Default port User <your-bastion-username> # Target host Host target-host-A HostName <target-host-ip> # Example: 192.168.1.10 User <target-host-username> ProxyJump bastionThe
ProxyJump bastiondirective tells the SSH client to connect totarget-host-Athrough the bastion host defined in theHost bastionblock.Run SCP commands to transfer files. The SSH client automatically routes traffic through the bastion host.
Upload a file to the target host:
scp /file-name.txt target-host-A:/home/Download a file from the target host:
scp target-host-A:/file-name.txt /home/
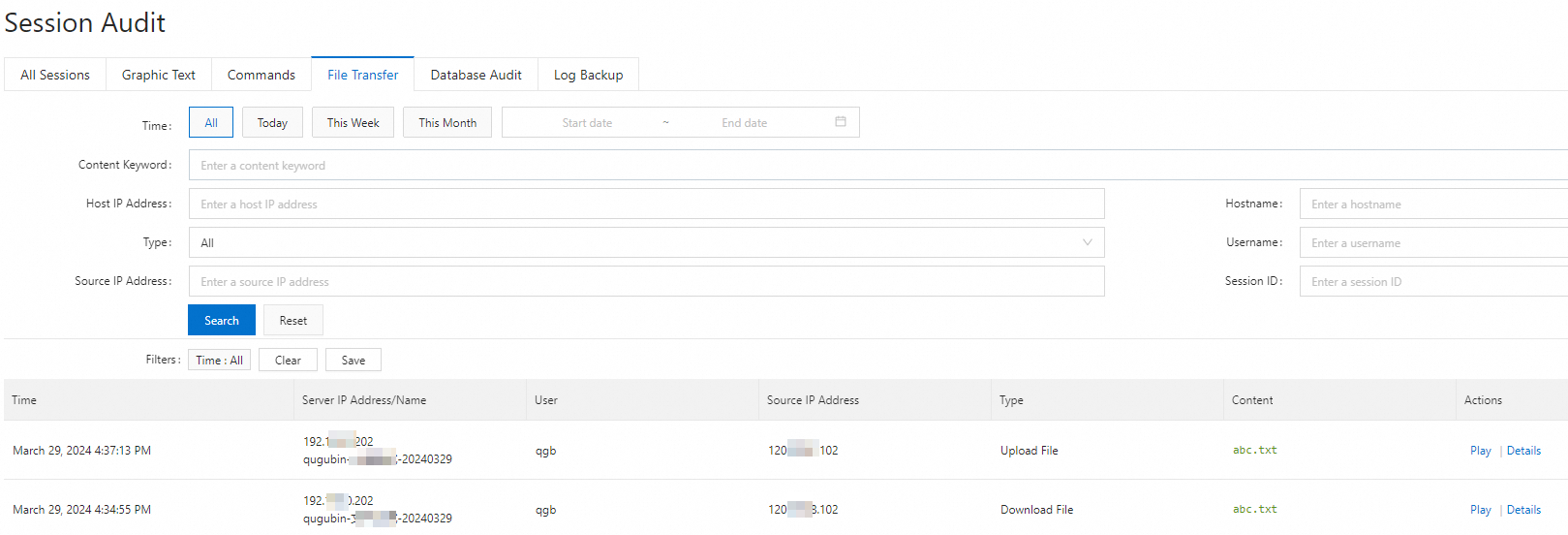
View session audit logs
After the file transfer completes, log in to the Bastionhost console to review the session audit logs. For details, see Search for sessions and view session details.