When your applications run inside a service mesh, external traffic must pass through an ingress gateway to reach mesh workloads. Application Load Balancer (ALB) provides layer-7 load balancing -- including host- and path-based routing, health checks, and managed certificates -- at the network edge. By chaining ALB with an ASM ingress gateway, you combine ALB edge capabilities with mesh-level features such as mTLS, fine-grained traffic routing, and distributed tracing, without exposing the ingress gateway directly to the internet.
After you complete this guide, external requests reach your mesh workloads through the following path:
Client --> ALB --> Kubernetes Ingress --> Istio Gateway --> Application pod
| | | |
Layer-7 LB Routes traffic to Applies Istio Sidecar proxy
(public or the ingress gateway routing rules handles mTLS
private) service on port 80 (VirtualService) and telemetryPrerequisites
Before you begin, ensure that you have:
-
An ACK cluster added to an ASM instance, with the following requirements:
-
ASM instance: Enterprise Edition
-
ACK cluster:
-
The Terway network plug-in
-
Cloud Controller Manager (CCM) v1.9.3.313-g748f81e-aliyun or later. See Cloud Controller Manager
-
The ALB Ingress controller installed. See Manage components
-
-
-
Automatic sidecar proxy injection enabled for the
defaultnamespace. See the "Enable automatic sidecar proxy injection" section in Manage global namespaces -
An ingress gateway created with CLB Instance Type set to Private Access and Service Port set to 80. See Create an ingress gateway
Step 1: Deploy a sample application
Connect to the ACK cluster using its kubeconfig file, then deploy the Bookinfo application:
kubectl apply -f https://raw.githubusercontent.com/istio/istio/master/samples/bookinfo/platform/kube/bookinfo.yamlFor detailed instructions, see Deploy an application in an ASM instance.
Step 2: Create Istio routing resources
Two Istio resources control how traffic flows inside the mesh:
-
Gateway -- defines which ports and protocols the ingress gateway listens on. It does not include routing logic.
-
VirtualService -- defines how incoming requests are routed to backend services based on URI matching rules.
-
Create a Gateway
-
Log on to the ASM console. In the left-side navigation pane, choose Service Mesh > Mesh Management.
-
Click the name of your ASM instance. In the left-side navigation pane, choose ASM Gateways > Gateway.
-
Click Create and configure the gateway as shown in the following figure.
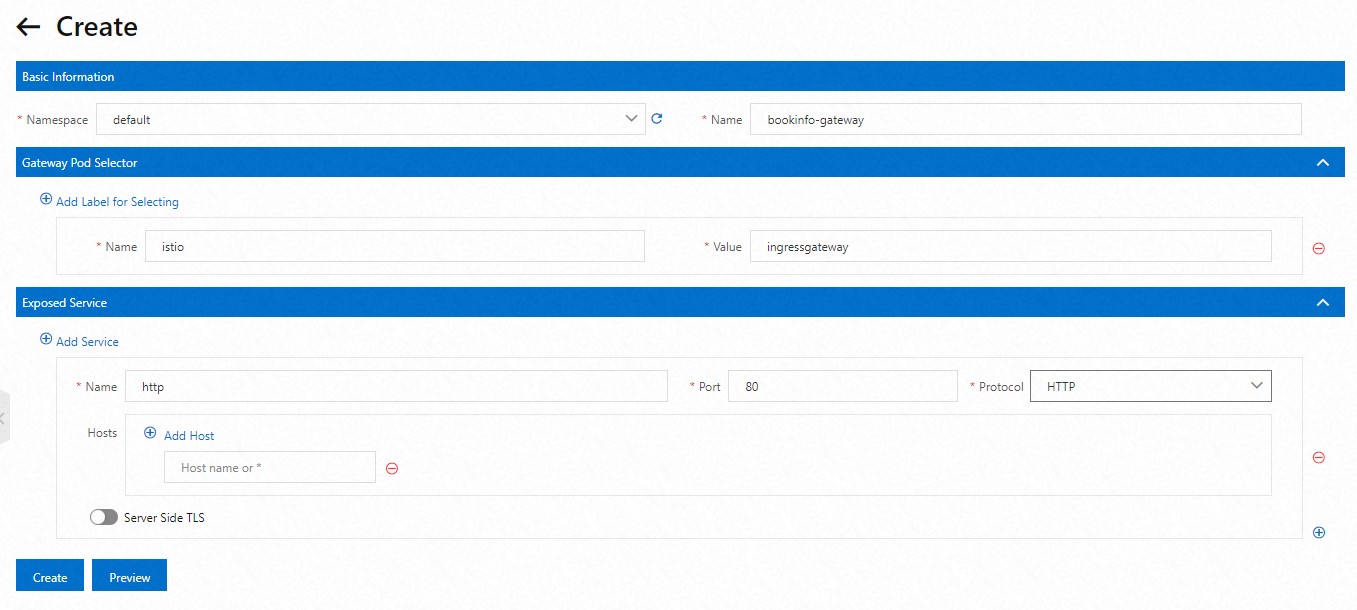
-
Click Preview to review the YAML. After you confirm the information, click Submit. Then click Create.
-
-
Create a VirtualService
-
On the ASM instance details page, choose Traffic Management Center > VirtualService in the left-side navigation pane.
-
On the VirtualService page, click Create and configure a virtual service for the
bookinfo-gatewaygateway as shown in the following figure.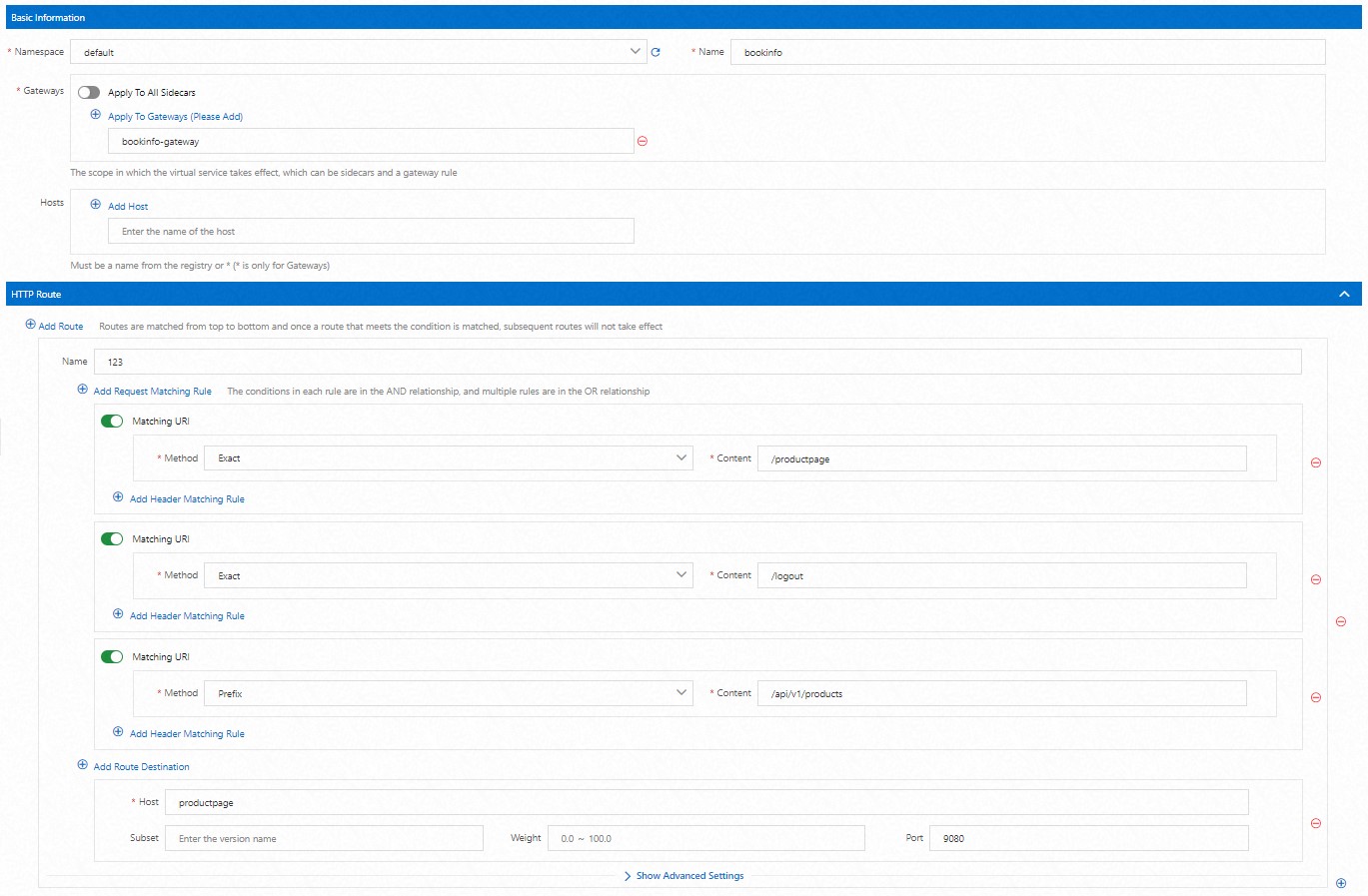
-
Click Preview to review the YAML. After you confirm the information, click Submit. Then click Create.
-
Step 3: Create an AlbConfig object
An AlbConfig custom resource tells the ALB Ingress controller which ALB instance to use. Choose one of the following options based on your scenario.
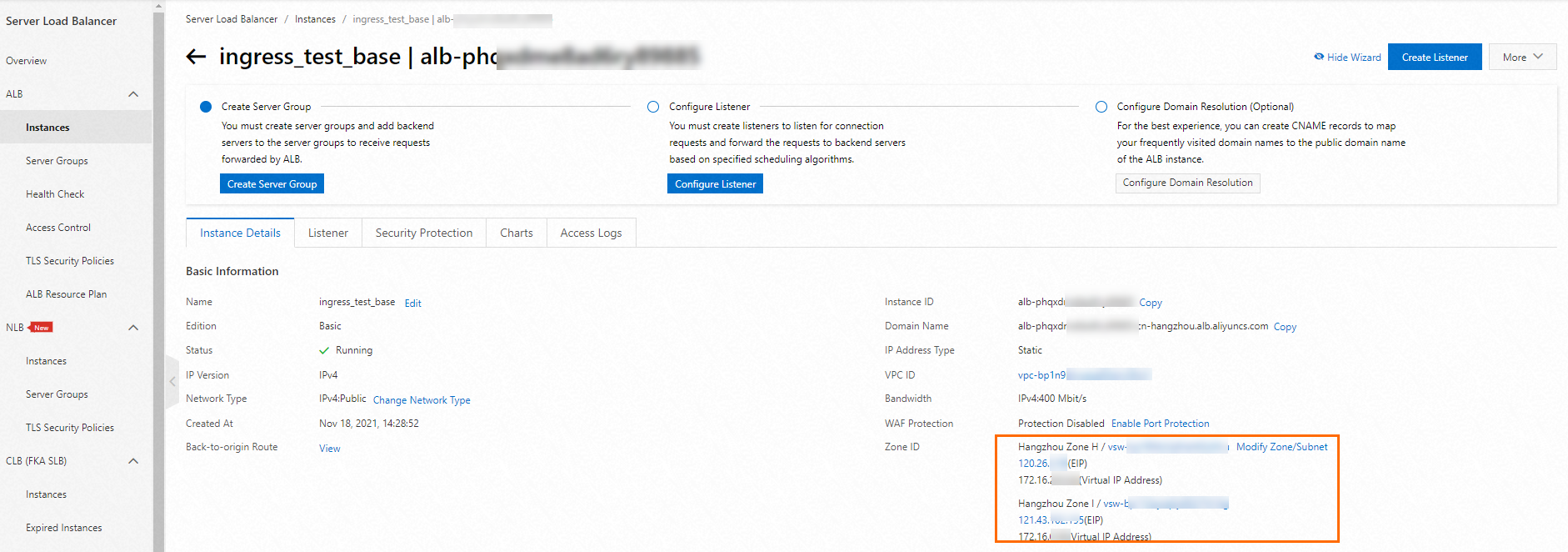
Option A: Use an existing ALB instance
-
Get the ALB instance ID from the ALB console.
-
Create a file named
alb-demo.yaml:apiVersion: alibabacloud.com/v1 kind: AlbConfig metadata: name: default spec: config: id: <your-alb-instance-id> # Replace with your ALB instance ID, e.g. alb-bp1a4g3k*** forceOverride: false -
Apply the manifest:
kubectl apply -f alb-demo.yaml
Option B: Create a new ALB instance
-
Create a file named
alb-demo.yaml. For the full parameter reference, see Access services by using an ALB Ingress.apiVersion: alibabacloud.com/v1 kind: AlbConfig metadata: name: default spec: config: name: alb-demo # Display name for the new ALB instance addressType: Internet # Internet (public) or Intranet (VPC-only) zoneMappings: - vSwitchId: <your-vswitch-id-1> # vSwitch in availability zone A - vSwitchId: <your-vswitch-id-2> # vSwitch in availability zone BParameter
Description
spec.config.nameDisplay name of the ALB instance to create
addressTypeInternet-- public IP, accessible from the internet (default).Intranet-- private IP, accessible only within the VPCzoneMappingsAt least two vSwitch IDs in different availability zones. See Supported regions and zones. To create a vSwitch, see Create and manage a vSwitch
Replace the placeholder values:
Placeholder Description Example <your-vswitch-id-1>vSwitch ID in availability zone A vsw-uf6ccg2a9g71hx8go\*\*\*\* <your-vswitch-id-2>vSwitch ID in availability zone B vsw-uf6nun9tql5t8nh15\*\*\*\* -
Apply the manifest:
kubectl apply -f alb-demo.yaml
Step 4: Create an IngressClass resource
The IngressClass links Kubernetes Ingress resources to the ALB controller and the AlbConfig created in the previous step.
-
Create a file named
alb.yaml:apiVersion: networking.k8s.io/v1 kind: IngressClass metadata: name: alb spec: controller: ingress.k8s.alibabacloud/alb # ALB Ingress controller identifier parameters: apiGroup: alibabacloud.com kind: AlbConfig name: default # Must match the AlbConfig name from Step 3 scope: Cluster -
Apply the manifest:
kubectl apply -f alb.yamlExpected output:
ingressclass.networking.k8s.io/alb created
Step 5: Create an Ingress resource
The Ingress resource routes ALB traffic to the ingress gateway service. Create it in the istio-system namespace where the ingress gateway runs.
-
Create a file named
asm-gateway-ingress.yaml:apiVersion: networking.k8s.io/v1 kind: Ingress metadata: name: asm-gateway-ingress namespace: istio-system # Same namespace as the ingress gateway spec: ingressClassName: alb # References the IngressClass from Step 4 rules: - http: paths: - backend: service: name: istio-ingressgateway # The ingress gateway Kubernetes service port: number: 80 # Must match the ingress gateway Service Port path: /* pathType: ImplementationSpecific -
Apply the manifest:
kubectl apply -f asm-gateway-ingress.yaml
Step 6: Verify the integration
-
Get the ALB endpoint assigned to the Ingress:
kubectl get ing -n istio-systemExpected output:
NAME CLASS HOSTS ADDRESS PORTS AGE asm-gateway-ingress alb * alb-xxxx.xxxx.alb.aliyuncs.com 80 18h -
Send a test request to the Bookinfo product page:
# Replace with the ADDRESS from the output above curl -s -o /dev/null -w "%{http_code}" http://alb-xxxx.xxxx.alb.aliyuncs.com/productpageA
200response confirms that traffic flows through ALB to the ingress gateway and reaches the application. -
(Optional) Open
http://<ALB-endpoint>/productpagein a browser to view the Bookinfo product page.Alternatively, find the ALB public IP address in the ALB console. If the ALB instance is bound to a domain name, use the domain name instead.