Sharing an Alibaba Cloud account across a team risks exposing AccessKey pairs. Instead, grant Resource Access Management (RAM) users and RAM roles only the Service Mesh (ASM) permissions they need -- such as creating instances, updating configurations, or managing RBAC authorization.
When to use this guide
Choose the scope of permissions based on what the RAM identity needs to do:
| Scenario | Required permissions |
|---|---|
| Manage ASM instances only | Follow this topic to attach system or custom policies for ASM. |
| Manage both ASM instances and ACK clusters (for example, adding or removing clusters from a mesh) | Grant ASM permissions from this topic and ACK permissions by following Use RAM to authorize access to clusters and cloud resources. |
Prerequisites
Before you begin, make sure that you have:
A basic understanding of RAM policy structure and syntax
System policies
ASM provides two built-in system policies:
| Policy | Permissions |
|---|---|
| AliyunASMReadOnlyAccess | Read-only access to ASM instances. The RAM identity can view instance information but cannot modify configurations. |
| AliyunASMFullAccess | Full access to ASM instances. The RAM identity has the same ASM permissions as the Alibaba Cloud account. |
Attach a system policy
The following steps use AliyunASMReadOnlyAccess as an example. To attach a different system policy, substitute the policy name in step 4.
For more information, see Grant permissions to a RAM user and Grant permissions to a RAM role.
Log on to the RAM console as a RAM administrator.
In the left-side navigation pane, choose .
On the Users page, find the required RAM user, and click Add Permissions in the Actions column.

You can also select multiple RAM users and click Add Permissions in the lower part of the page to grant permissions to the RAM users at a time.
In the Grant Permission panel, configure the following settings:
Configure the Resource Scope parameter.
Account: The authorization takes effect on the current Alibaba Cloud account.
Resource Group: The authorization takes effect on a specific resource group.
ImportantIf you select Resource Group for the Resource Scope parameter, make sure that the required cloud service supports resource groups. For more information, see Services that work with Resource Group. For more information about how to grant permissions on a resource group, see Use a resource group to restrict a RAM user to managing only specific ECS instances.
Configure the Principal parameter.
The principal is the RAM user to which you want to grant permissions. The current RAM user is automatically selected.
Select System Policy from the All Types drop-down list, enter AliyunASMReadOnlyAccess in the search box, and then select AliyunASMReadOnlyAccess.
NoteA maximum of five policies can be attached at a time. To attach more, repeat this procedure.
Click OK.
Click Close.
Custom policies
Use custom policies for fine-grained access control -- for example, granting all ASM permissions except RBAC authorization.
Step 1: Create a custom policy
Log on to the RAM console as a RAM user who has administrative rights.
In the left-side navigation pane, choose .
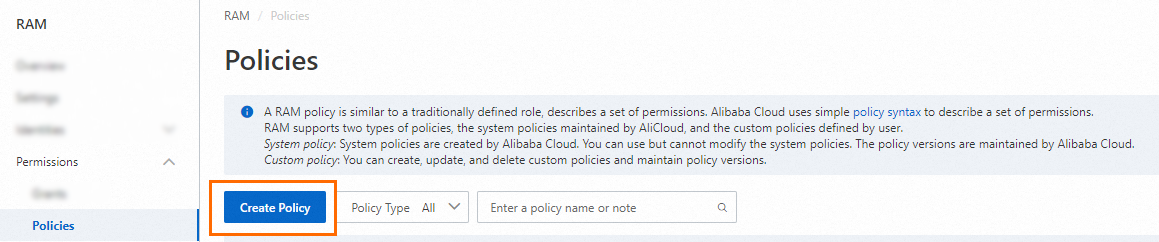
On the Policies page, click Create Policy.
On the Create Policy page, click the JSON tab.

Enter the policy document in the editor and click OK.
The following example grants all ASM permissions except RBAC authorization. A RAM identity with this policy can perform all operations on ASM instances but cannot grant RBAC permissions to other identities.
Each field in the policy serves a specific purpose:
Field Description EffectWhether to allow or deny the specified actions. ActionThe API operations to authorize. Wildcards ( *) match multiple operations.ResourceThe target resources. Use *for all resources, or specify an ARN to scope the policy to a single resource.ConditionOptional conditions that must be met for the policy to take effect. { "Statement": [ { "Effect": "Allow", "Action": [ "servicemesh:Add*", "servicemesh:CRBatchDeletion", "servicemesh:Create*", "servicemesh:Delete*", "servicemesh:Describe*", "servicemesh:Enable*", "servicemesh:Disable*", "servicemesh:Get*", "servicemesh:InvokeApiServer", "servicemesh:List*", "servicemesh:Modify*", "servicemesh:Re*", "servicemesh:Run*", "servicemesh:Set*", "servicemesh:Sync*", "servicemesh:Update*", "servicemesh:Upgrade*" ], "Resource": "*" }, { "Effect": "Allow", "Action": [ "log:ListLogStores", "log:ListDashboard", "log:GetDashboard", "log:ListSavedSearch", "log:ListProject" ], "Resource": "*" }, { "Effect": "Allow", "Action": "log:GetLogStoreLogs", "Resource": "acs:log:*:*:project/*/logstore/audit-*" }, { "Effect": "Allow", "Action": "log:GetLogStoreLogs", "Resource": "acs:log:*:*:project/*/logstore/istio-*" }, { "Action": "ram:CreateServiceLinkedRole", "Resource": "*", "Effect": "Allow", "Condition": { "StringEquals": { "ram:ServiceName": "servicemesh.aliyuncs.com" } } } ], "Version": "1" }For more information about policy syntax, see Policy structure and syntax.
In the Basic Information section, enter a name in the Name field (for example, ASMPolicy1) and click OK.
Step 2: Attach the custom policy
To attach the custom policy to a RAM role instead of a RAM user, see Grant permissions to a RAM role.
Log on to the RAM console as a RAM user who has administrative rights.
In the left-side navigation pane, choose .
On the Users page, find the required RAM user, and click Add Permissions in the Actions column.

You can also select multiple RAM users and click Add Permissions in the lower part of the page to grant permissions to the RAM users at a time.
In the Add Permissions panel, configure the following settings:
Configure the Resource Scope parameter.
Account: The authorization takes effect on the current Alibaba Cloud account.
Resource Group: The authorization takes effect on a specific resource group.
ImportantIf you select Resource Group for the Resource Scope parameter, make sure that the required cloud service supports resource groups. For more information, see Services that work with Resource Group. For more information about how to grant permissions on a resource group, see Use a resource group to restrict a RAM user to managing only specific ECS instances.
Configure the Principal parameter.
The principal is the RAM user to which you want to grant permissions. The current RAM user is automatically selected.
Select Custom Policy from the All Types drop-down list, enter
ASMPolicy1in the search box, and then select ASMPolicy1.
Click OK.
Click Close.
Custom policy examples
The following examples cover common permission scenarios. Replace placeholder values with your actual resource identifiers before applying these policies.
Grant permissions on a single ASM instance
Restrict a RAM identity to manage only one specific ASM instance.
Replace <ServicemeshId> with the ID of the target ASM instance.
{
"Statement": [
{
"Effect": "Allow",
"Action": "servicemesh:*",
"Resource": "acs:servicemesh:*:*:servicemesh/<ServicemeshId>"
},
{
"Effect": "Allow",
"Action": "servicemesh:DescribeServiceMeshes",
"Resource": "*"
},
{
"Effect": "Allow",
"Action": "log:GetLogStoreLogs",
"Resource": "acs:log:*:*:project/*/logstore/audit-<ServicemeshId>"
},
{
"Effect": "Allow",
"Action": "log:GetLogStoreLogs",
"Resource": "acs:log:*:*:project/*/logstore/istio-<ServicemeshId>"
}
],
"Version": "1"
}How this policy works:
The first statement grants all
servicemesh:*actions, but only on the specified instance ARN.The second statement grants
servicemesh:DescribeServiceMesheson all resources, which is required for listing meshes in the console.The last two statements grant log access scoped to the specified instance.
Grant read and write access to Istio resources
Allow a RAM identity to manage Istio resources through the ASM console without changing other ASM settings such as feature configurations.
This policy builds on AliyunASMReadOnlyAccess by adding the servicemesh:InvokeApiServer action, which enables Istio resource management.
{
"Statement": [
{
"Effect": "Allow",
"Action": [
"servicemesh:List*",
"servicemesh:Describe*",
"servicemesh:Get*",
"servicemesh:InvokeApiServer"
],
"Resource": "*"
},
{
"Effect": "Allow",
"Action": [
"log:ListLogStores",
"log:ListDashboard",
"log:GetDashboard",
"log:ListSavedSearch"
],
"Resource": "*"
},
{
"Effect": "Allow",
"Action": "log:GetLogStoreLogs",
"Resource": "acs:log:*:*:project/*/logstore/audit-*"
}
],
"Version": "1"
}Grant RBAC authorization permissions
Allow a RAM identity to manage RBAC permissions of other RAM users and RAM roles through the ASM console, without granting access to manage ASM instances.
{
"Statement": [
{
"Effect": "Allow",
"Action": [
"servicemesh:DescribeUserPermissions",
"servicemesh:GrantUserPermissions",
"servicemesh:DescribeServiceMeshes",
"servicemesh:DescribeUsersWithPermissions"
],
"Resource": "*"
},
{
"Effect": "Allow",
"Action": "ims:ListUserBasicInfos",
"Resource": "*"
}
],
"Version": "1"
}