By default, Service Mesh (ASM) creates one Classic Load Balancer (CLB) instance for each ingress gateway. To handle additional traffic patterns -- such as separating public and internal traffic or scaling beyond a single CLB's capacity -- you can associate multiple CLB instances with the same ingress gateway. Each additional CLB is backed by a new Kubernetes Service that shares the gateway's pod selector.
Scenarios
Multiple CLB instances on a single ingress gateway address the following needs:
Separate external and internal traffic -- Expose one internet-facing CLB for public access and one VPC-internal CLB for backend services.
Isolate traffic by tenant or environment -- Route traffic from different clients or environments through dedicated load balancer endpoints.
Scale beyond a single CLB's connection limit -- Distribute traffic across multiple CLB instances to handle higher throughput.
How it works
Each CLB instance is backed by a Kubernetes Service of type LoadBalancer. All Services share the same pod selector (including app: istio-ingressgateway, istio: ingressgateway, and other gateway labels), so traffic from any CLB reaches the same set of ingress gateway pods.
When ASM deploys an ingress gateway, it automatically creates a Service named istio-ingressgateway in the istio-system namespace. To add a second CLB, you create another Service with the same selector and a different name.
Deleting a Service also deletes the CLB instance associated with it. Do not remove a Service unless you intend to decommission the corresponding CLB.
Prerequisites
Before you begin, make sure that you have:
A cluster added to the ASM instance. For more information, see Add a cluster to an ASM instance
An ingress gateway deployed in the Container Service for Kubernetes (ACK) cluster added to the ASM instance. For more information, see Create an ingress gateway
The Bookinfo application and Istio resources deployed so that the ingress gateway can route traffic. For more information, see Deploy an application in an ACK cluster and Use Istio resources to route traffic to different versions of a service
Step 1: Create a Service for the additional CLB instance
Log on to the ACK console. In the left-side navigation pane, click Clusters.
On the Clusters page, find the target cluster and click its name or click Details in the Actions column.
In the left-side navigation pane, choose Network > Services.
Set Namespace to istio-system, then click Create Resources in YAML.
Select Custom from the Sample Template drop-down list and paste the following YAML:
ImportantThe
nodePortvalues must not conflict with any existing port assignments in the cluster.apiVersion: v1 kind: Service metadata: annotations: service.beta.kubernetes.io/alibaba-cloud-loadbalancer-spec: slb.s1.small service.beta.kubernetes.io/alicloud-loadbalancer-address-type: internet labels: app: istio-ingressgateway asm-system: 'true' istio: ingressgateway name: istio-ingressgateway-2 namespace: istio-system spec: externalTrafficPolicy: Cluster ports: - name: http-0 nodePort: 30544 port: 80 protocol: TCP targetPort: 80 - name: https-2 nodePort: 30682 port: 443 protocol: TCP targetPort: 443 selector: app: istio-ingressgateway asm-system: 'true' istio: ingressgateway provider: asm sessionAffinity: None type: LoadBalancerClick Create. After the Service is created, a CLB instance is automatically provisioned.
Key parameters
| Parameter | Description | Valid values |
|---|---|---|
name | Name of the new Service. Must be unique within the namespace. | Example: istio-ingressgateway-2 |
service.beta.kubernetes.io/alibaba-cloud-loadbalancer-spec | CLB instance specification. | slb.s1.small, slb.s2.small, slb.s2.medium, slb.s3.small, slb.s3.medium, slb.s3.large |
service.beta.kubernetes.io/alicloud-loadbalancer-address-type | Network type of the CLB instance. | internet (internet-facing) or intranet (internal-facing) |
nodePort | Port opened on every cluster node that forwards traffic to the Service. | Any unused port in the node port range |
To create an internal-facing CLB instead of an internet-facing one, set alicloud-loadbalancer-address-type to intranet:
annotations:
service.beta.kubernetes.io/alicloud-loadbalancer-address-type: intranetStep 2: Verify the configuration
After the Service is created, confirm that both CLB instances route traffic to the ingress gateway.
Get the external IP addresses of both Services: Expected output:
kubectl -n istio-system get svc istio-ingressgateway istio-ingressgateway-2 \ -o custom-columns="NAME:.metadata.name,EXTERNAL-IP:.status.loadBalancer.ingress[0].ip,PORT:.spec.ports[0].port"NAME EXTERNAL-IP PORT istio-ingressgateway 198.51.xxx.xx 80 istio-ingressgateway-2 203.0.xxx.xx 80Store the IP addresses in environment variables:
export INGRESS_IP_1=$(kubectl -n istio-system get svc istio-ingressgateway -o jsonpath='{.status.loadBalancer.ingress[0].ip}') export INGRESS_IP_2=$(kubectl -n istio-system get svc istio-ingressgateway-2 -o jsonpath='{.status.loadBalancer.ingress[0].ip}')Send a request through each CLB instance: Both commands should return
200. You can also openhttp://<INGRESS_IP_1>/productpageandhttp://<INGRESS_IP_2>/productpagein a browser to confirm that the Bookinfo application page loads through both endpoints.curl -s -o /dev/null -w "%{http_code}" http://$INGRESS_IP_1/productpage curl -s -o /dev/null -w "%{http_code}" http://$INGRESS_IP_2/productpage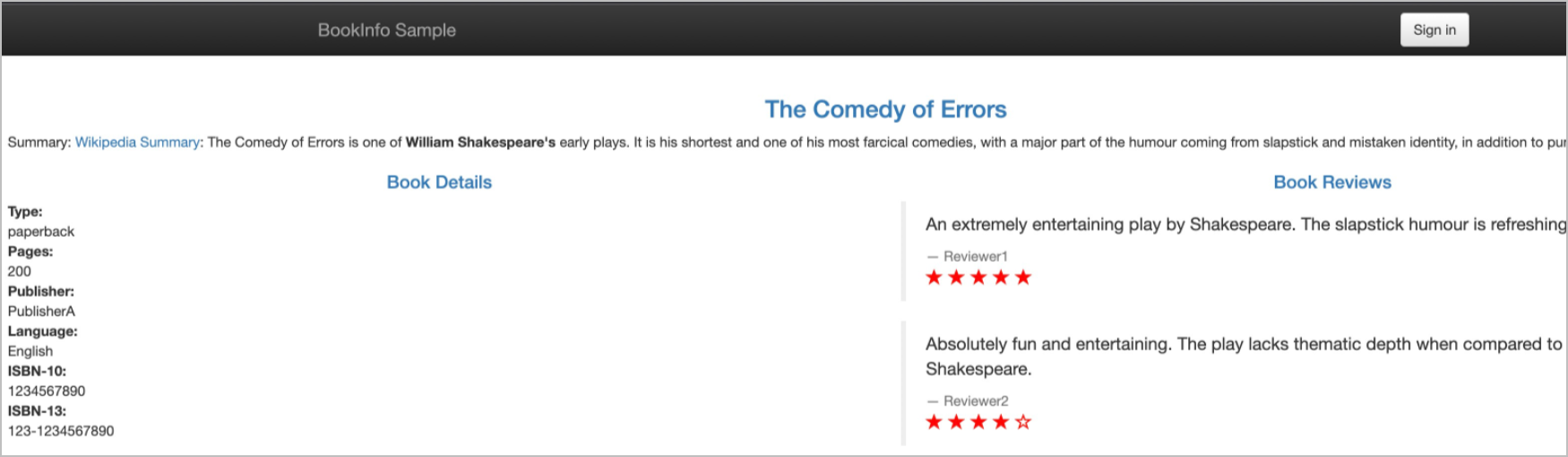
Result
The ingress gateway is now accessible through two CLB instances. Traffic arriving at either CLB endpoint routes to the same set of ingress gateway pods.