After you add an ingress gateway to a Service Mesh (ASM) instance, deploy applications to the associated clusters. This tutorial walks through deploying the Bookinfo sample application to an ACK cluster, enabling ambient mode on the namespace, and verifying that mutual TLS (mTLS) encryption is active between all pods -- without sidecars or application restarts.
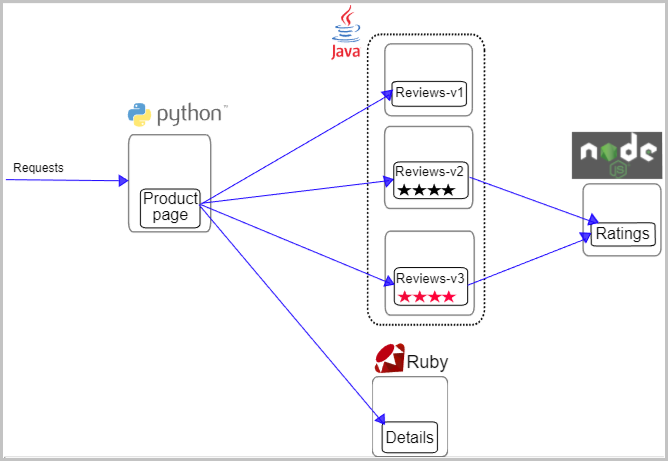
Bookinfo application architecture
Bookinfo is a book review application composed of four microservices.
| Microservice | Role |
|---|---|
| Productpage | Generates the page by calling Details and Reviews |
| Details | Provides book information |
| Reviews | Displays book reviews; may call Ratings |
| Ratings | Returns star ratings based on reviews |
The Reviews microservice runs three versions simultaneously:
v1 -- Returns reviews only. Does not call Ratings.
v2 -- Calls Ratings. Displays one to five black stars.
v3 -- Calls Ratings. Displays one to five red stars.
Prerequisites
Before you begin, make sure that you have:
Managed Service for Prometheus or a self-managed Prometheus instance integrated with the ACK cluster for metrics collection. For setup instructions, see Integrate Managed Service for Prometheus or Integrate self-managed Prometheus
Step 1: Deploy the Bookinfo application
Create a file named
bookinfo.yamlwith the following content.Deploy the application to the
defaultnamespace.kubectl apply -f bookinfo.yamlVerify that all pods are running. Expected output: Wait until all six pods show
Runningstatus before you continue.kubectl get podsNAME READY STATUS RESTARTS AGE details-v1-xxx 1/1 Running 0 30s productpage-v1-xxx 1/1 Running 0 30s ratings-v1-xxx 1/1 Running 0 30s reviews-v1-xxx 1/1 Running 0 30s reviews-v2-xxx 1/1 Running 0 30s reviews-v3-xxx 1/1 Running 0 30s
Step 2: Deploy and configure the ingress gateway
Create a file named
bookinfo-gateway.yamlwith the following content. The Gateway listens on port 80, and the VirtualService forwards matching requests (/productpage,/static,/login,/logout,/api/v1/products) to port 9080 of theproductpageservice.apiVersion: networking.istio.io/v1beta1 kind: Gateway metadata: name: bookinfo-gateway namespace: default spec: selector: istio: ingressgateway servers: - port: number: 80 name: http protocol: HTTP hosts: - '*' --- apiVersion: networking.istio.io/v1beta1 kind: VirtualService metadata: name: vs-demo namespace: default spec: hosts: - '*' http: - name: gw-to-productage match: - uri: exact: /productpage - uri: prefix: /static - uri: exact: /login - uri: exact: /logout - uri: prefix: /api/v1/products route: - destination: host: productpage port: number: 9080 gateways: - bookinfo-gatewayApply the gateway configuration.
kubectl apply -f bookinfo-gateway.yaml
Step 3: Access the application
Get the ingress gateway IP address.
echo $(kubectl -n istio-system get istiogateway ingressgateway -o jsonpath="{.status.GatewayAddress[0]}")Open
http://<gateway-ip>/productpagein a browser. Replace<gateway-ip>with the IP address from the previous step.
Refresh the page several times. The star ratings under Book Reviews cycle through three states, matching the three versions of the Reviews service: This confirms that all three versions of the Reviews service are running and load-balanced.
No stars (v1)
Black stars (v2)
Red stars (v3)
Step 4: Enable ambient mode
Ambient mode adds mTLS encryption between all pods in a namespace without injecting sidecar proxies. No application restarts are required.
Log on to the ASM console.
In the left-side navigation pane, choose Service Mesh > Mesh Management.
On the Mesh Management page, click the name of your ASM instance.
In the left-side navigation pane, choose ASM Instance > Global Namespace.
In the Data Plane Mode column of the Default namespace, click Switch To Ambient Mesh Mode.
To revert, switch the Data Plane Mode back to sidecar mode at any time from the Global Namespaces page.
Open
http://<gateway-ip>/productpagein a browser to verify that the application still works. The page loads exactly as before. The difference is that mTLS encryption is now active between all Bookinfo pods. Service-to-service communication is encrypted transparently, without code changes or restarts.
Step 5: View the mesh topology
Set up monitoring metrics collection and mesh topology to visualize traffic between services.
Enable monitoring metrics collection
Skip this section if you already use a self-managed Prometheus instance.
On the Mesh Management page, click the name of your ASM instance.
In the left-side navigation pane, choose Observability Management Center > Monitoring metrics.
Click Collect Metrics to Managed Service for Prometheus. In the Submit dialog box, select the cluster name and click OK.
Enable mesh topology
On the Mesh Management page, click the name of your ASM instance.
In the left-side navigation pane, choose Observability Management Center > Mesh Topology.
Click To Enable and configure the following parameters.
Add a dedicated port for mesh topology by editing the gateway configuration.
Parameter Description Service deployment mode Data plane deployment mode for your Kubernetes cluster. NoteThe managed deployment mode only supports access through a Serverless ASM gateway.
Observability cluster Your observability cluster ID (for example, c6118d720xxxxxxxxxxxxxx58410a9c7d0).Prometheus scrape address Leave blank for Managed Service for Prometheus. For self-managed Prometheus, enter the read address. When multiple clusters are added to ASM, create an aggregation instance and enter its read address. Identity authentication - logon method Token Entry ASM. For Select an ASM gateway, choose ingressgateway. For Select an ASM gateway port, choose443.Click Confirm Enabling.
Generate test traffic and view the topology
Send 100 requests to generate traffic data for the topology diagram.
export GATEWAY_ADDRESS=$(kubectl -n istio-system get istiogateway ingressgateway -o jsonpath="{.status.GatewayAddress[0]}") for i in $(seq 1 100); do echo "Request $i: $(curl -sSI -o /dev/null -w "%{http_code}" "http://${GATEWAY_ADDRESS}:80/productpage")" doneOn the Mesh Topology page, in the Logon Method section, click View the logon token and copy the token.
Click Access ASM mesh topology next to Topology address. On the Kiali page, paste the token into the Token field and click Log in. The topology graph shows traffic flow between all Bookinfo microservices, confirming that ambient mode, mTLS, and monitoring are working together.