The security assessment feature provides you with database security-related detection items. You can enable corresponding security configurations based on actual needs.
Procedure
Log on to the ApsaraDB for OceanBase console.
In the left-side navigation pane, choose Autonomy Service > Diagnostics Center.
In the Instance Details section, click the name of the target instance.
The system automatically redirects to the diagnostics center.
In the left-side navigation pane, choose Security Management > Security Assessment.
View the statistics of Total Detection Items, Cluster Security Risk Items, and Tenant Security Risk Items.
Click the Cluster Detection Item and Tenant Detection Item tabs to view the status of each detection item. For items with the Risky state, you can view the evaluation recommendations and then click To Deal to go to the relevant page.
If a reassessment is needed, click Start Assessment in the upper-right corner of the page, and then click OK in the confirmation box that appears.
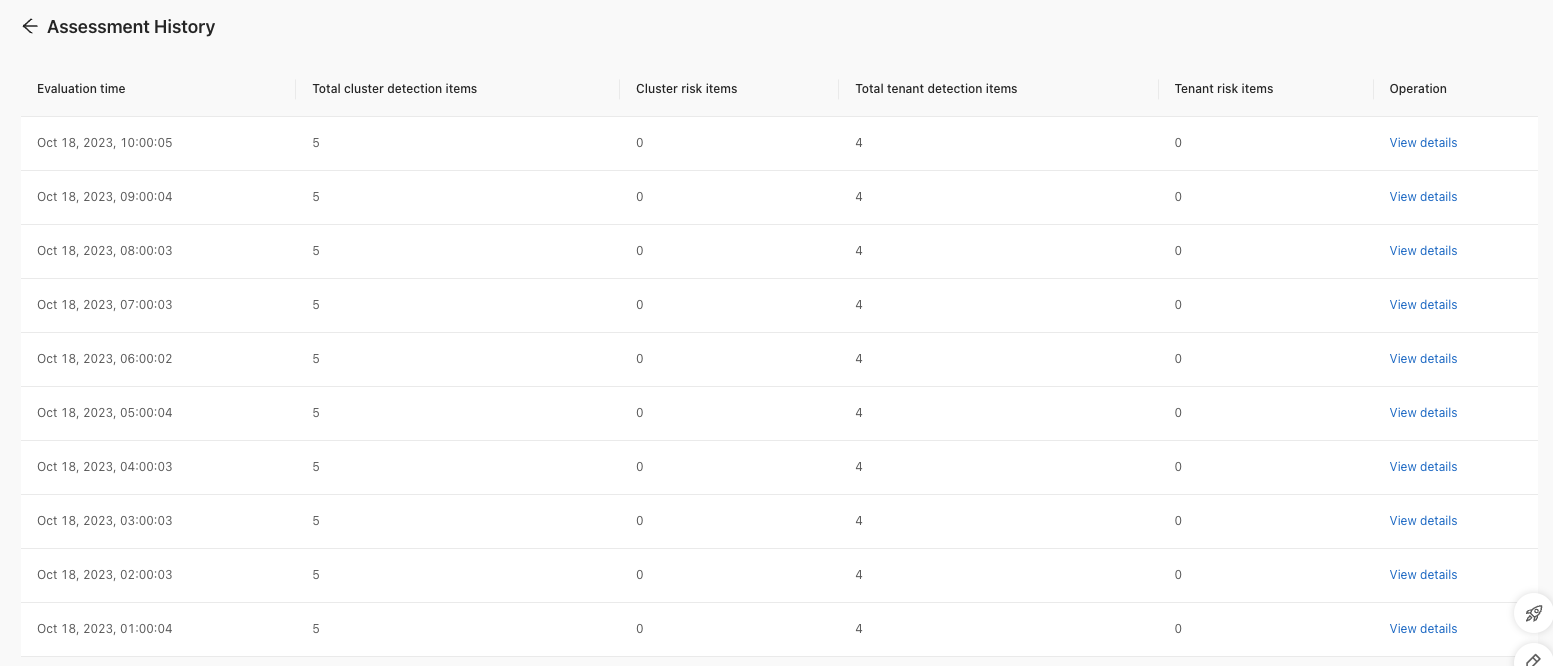
Click Assessment History to view the historical records of security assessments.