Application Security is a security service that is developed based on the Runtime Application Self-Protection (RASP) technology. Application Security can provide runtime self-protection for applications. To use Application Security, you do not need to change the application code. You only need to install the Application Security agent on instances. Application Security can protect your applications against the attacks exploited by most unknown vulnerabilities.
Background information
Application Security is a feature that is developed based on the RASP technology of Alibaba Cloud. The RASP technology can detect attacks and provide runtime self-protection for applications. It is built into applications and monitors the interactions between applications and other systems in real time by hooking key functions. When suspicious behavior occurs in an application, RASP identifies and blocks attacks based on the current context.
Traditional border protection schemes such as firewalls and web application firewalls (WAFs) are similar to protective suits and masks, which reduce the risk of human infection by blocking or filtering virus transmission pathways. In contrast, RASP is like a vaccine, which eliminates viruses when they invade by producing antibodies inside the human body. 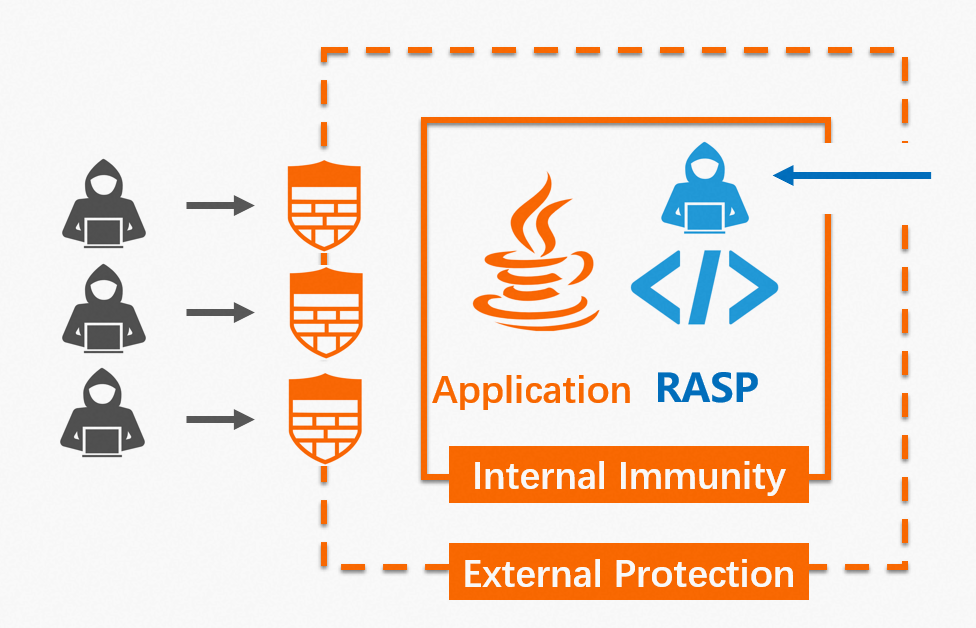
RASP and WAF do not replace each other. They have their own advantages in different business and security protection scenarios. To protect your applications, you can use both ARMS Application Security and Alibaba Cloud Web Application Firewall (WAF) based on your business environment and requirements. This enhances protection capabilities and minimizes the risks of application intrusion, data breach, and service unavailability.
Limits
Application Security supports only Java applications.
Features
Protection against security vulnerabilities
Application Security can protect applications against attacks such as SQL injection, malicious file read and write, malicious file upload, command injection, arbitrary file read, server-side request forgery (SSRF), thread injection, malicious DNS query, and memory horse injection. In addition, RASP-based Application Security does not depend on static rule libraries and can defend against unknown vulnerabilities such as zero-day vulnerabilities.
Identifying security risks of third-party components
For third-party application components with security vulnerabilities, Application Security automatically identifies the CVE vulnerabilities corresponding to the components, the detailed path of the components, the risk level and score of the vulnerabilities, and relevant instance information. This helps the R&D and security teams check the potential risks of third-party components, quickly locate the risk details, and fix the risks based on priorities.
Application security monitoring
You can run Application Security in Monitor mode to protect your applications. You can fix vulnerabilities in time when attacks are detected.
Before you use Application Security, the relevant applications must be monitored by ARMS Application Monitoring.
The Java agent version of Application Monitoring must be 2.7.1.3 or later. You can perform the following steps to view the agent version related to each application: Log on to the ARMS console. In the left-side navigation pane, choose .
FAQ
Does Application Security affect running applications?
The impact on running applications is almost negligible because Application Security has good control over performance, compatibility, and stability. In actual tests, the CPU overhead is less than 1%, the memory overhead is less than 30 MB, and the response time (RT) is less than 1 ms. In addition, Application Security provides features such as observation mode and soft fuse escape mechanism to minimize interference to applications.
How do I enable Application Security?
You can enable Application Security in the ARMS console. Then, you can restart the instance corresponding to your application. You do not need to change the application code. Application Security supports only Java applications. For more information, see Connect an application to Application Security.
How do I use Application Security to protect applications?
Theoretically speaking, the attacks detected by Application Security can actually produce security threats. Compared with the traditional detection technologies that are based on traffic characteristics, Application Security has lower false positive rate. Therefore, you must pay attention to the attacks detected by Application Security. After Application Security is enabled, the protection mode is set to "Monitor" by default. After the application runs stably for a period of time, you can set the protection mode to "Monitor and Block".
For more information, see FAQ on Application Security.
Contact us
If you have any questions about Application Security, see the documentation or join the DingTalk group chat (group chat ID: 34833427) to communicate with product managers and security experts.