The statistical report aggregates attack protection data for Anti-DDoS Pro and Anti-DDoS Premium over the past year, giving you a single view of traffic trends, attack distribution, and protection effectiveness.
Data availability
| Instance type | Data available from |
|---|---|
| Anti-DDoS Proxy (Chinese Mainland) | August 8, 2024 |
| Anti-DDoS Proxy (Outside Chinese Mainland) | September 17, 2025 |
Attack analysis is based on data sampling. Statistical results may not be fully precise.
Metric visibility by query scope
The metrics displayed depend on whether your query includes an instance, a domain name, or both.
| Metric | Instance only | Domain name only | Instance + domain name |
|---|---|---|---|
| Network-layer traffic statistics | Yes | — | Yes |
| Application-layer traffic statistics | — | Yes | Yes |
| Blackhole filtering events and duration | Yes | — | Yes |
| Peak QPS of single attack event | — | Yes | Yes |
| Request trend in QPS | — | Yes | Yes |
| Top 5 source regions of network-layer attacks | Yes | — | Yes |
| Top 5 source regions of application-layer attacks | — | Yes | Yes |
| Top 20 source IPs by peak attack throughput | Yes | — | Yes |
| Top 10 destination IPs by peak attack throughput | Yes | — | Yes |
| Top 10 destination domain names by peak attack throughput | — | Yes | Yes |
| Top 10 destination ports by attack | Yes | — | Yes |
| Defense against application-layer attacks by module | — | Yes | Yes |
The following query combinations are not supported:
No instance + No domain name
Some instances + Some domain names
View and download a statistical report
Go to the Statistical Reports page of the Traffic Security console.
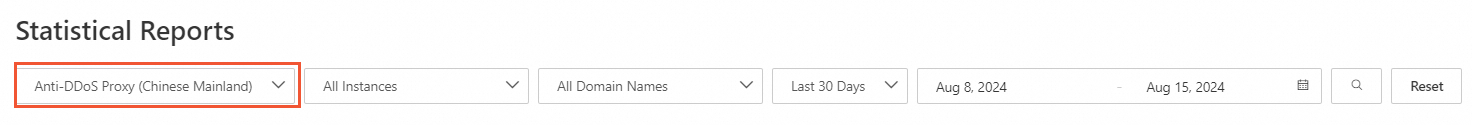
Select an instance type: Anti-DDoS Proxy (Chinese Mainland) or Anti-DDoS Proxy (Outside Chinese Mainland).
Select an instance and a domain name, specify a timestamp range, and click the search icon.
In the upper-right corner, click Export Report to download the report as an image or PDF.
Metric descriptions
Overall operational metrics
| Metric | Description |
|---|---|
| Peak traffic of single attack event | The peak inbound traffic in bit/s of a single attack event, compared across all network-layer attack events. Includes both attack traffic and service traffic. |
| Peak QPS of single attack event | Displayed only when the query includes a domain name. The peak queries per second (QPS) of a single attack event, compared across all application-layer attack events. |
| Peak pps of single attack event | The peak inbound traffic in packets per second (pps) of a single attack event, compared across all network-layer attack events. Includes both attack traffic and service traffic. |
| Blackhole filtering events | Displayed only when the query includes an instance. The number of blackhole filtering events for the selected instance within the specified timestamp range. |
| Blackhole filtering duration | Displayed only when the query includes an instance. The total duration of all blackhole filtering events for the selected instance within the specified timestamp range. |
| Anti-DDoS Proxy protection duration | The uptime of the current active instance. If multiple instances exist, the longest uptime is displayed. |
| Traffic scrubbing events | The total number and type distribution of all traffic scrubbing events. Types include volumetric, connection flood, and web resource exhaustion. Blackhole filtering events are not included. Data displayed varies by query scope: instance only shows volumetric and connection flood data; domain name only shows web resource exhaustion data; instance and domain name shows all three types. |
| Protected assets | The total number of protected assets, reflecting real-time data from the previous day (T-1). Independent of the selected timestamp range. Includes: IP (origin IP addresses for port forwarding) and domain name (protected domain names). |
Traffic metrics
| Metric | Description |
|---|---|
| Traffic trend in bit/s | Three traffic series are charted: Total inbound traffic — all traffic in bit/s from clients to Anti-DDoS Proxy, including attack and service traffic. Inbound service traffic — normal service traffic in bit/s from Anti-DDoS Proxy to the origin server. Outbound service traffic — normal service traffic in bit/s from the origin server to Anti-DDoS Proxy. Note If the query includes only a domain name, outbound service traffic is based on payload statistics. If the query includes an instance, it is based on network-layer traffic statistics. A drift may exist between the two measurement methods. |
| Request trend in QPS | Displayed only when the query includes a domain name. Max inbound QPS — the queries per second (QPS) from clients to Anti-DDoS Proxy, including attack QPS and clean QPS. Back-to-origin QPS — the QPS from Anti-DDoS Proxy to the origin server. |
| Top 5 source regions of network-layer attacks | Displayed only when the query includes an instance. The top five attack source regions ranked by number of requests from source IPs. China statistics are grouped by province; locations outside China are grouped by country. Statistical logic: (1) For each attack event, calculate the percentage of requests from each source IP by province or country. (2) Rank the percentages across all attack events and select the top five — one value per province or country, five distinct regions. |
| Top 5 source regions of application-layer attacks | Displayed only when the query includes a domain name. The top five attack source regions ranked by number of requests from source IPs in QPS. China statistics are grouped by province; locations outside China are grouped by country. Statistical logic: (1) For each attack event, calculate the number of requests from each source IP by province or country. (2) Compare request counts across all attack events and select the top five QPS values — one value per province or country, five distinct regions. |
Attack distribution
| Metric | Description |
|---|---|
| Attack type distribution | The distribution of attacks by number of occurrences per type, covering sub-types of volumetric, connection flood, and web resource exhaustion attacks. Blackhole filtering events are not included. |
| Top 10 attack source ISPs | The distribution of global Internet service providers (ISPs) for attack sources, ranked by number of requests from source IPs across all attack events. Includes both traffic scrubbing events and blackhole filtering events. |
| Volumetric attacks by peak attack throughput | The number of events in each peak throughput range. Blackhole filtering events are not included. Ranges: 0–30 Gbps, 30–100 Gbps, 100–300 Gbps, 300–600 Gbps, and over 600 Gbps. |
| Attack duration distribution | The number of events in each duration range, covering volumetric, connection flood, and web resource exhaustion events. Blackhole filtering events are not included. Ranges: 0–30 minutes, 30–60 minutes, 1–3 hours, 3–12 hours, and over 12 hours. |
Attack ranking metrics
| Metric | Description |
|---|---|
| Top 20 source IP addresses by peak attack throughput | Displayed only when the query includes an instance. The top 20 source IP addresses with the highest peak attack throughput. Statistical logic: (1) Based on sampled traffic, rank source IP addresses in each attack event by number of discarded requests. (2) Compare across attack events and select the top 20 — one value per IP address, up to 20 distinct source IPs. |
| Top 10 destination IP addresses by peak attack throughput | Displayed only when the query includes an instance. The top 10 destination IP addresses with the highest peak attack throughput. Statistical logic: (1) Based on sampled traffic, rank destination IP addresses in each attack event by peak inbound traffic in bit/s. (2) Compare across attack events and select the top 10 — one value per IP address, up to 10 distinct destination IPs. |
| Top 10 destination domain names by peak attack throughput | Displayed only when the query includes a domain name. The top 10 destination domain names with the highest peak attack throughput. Statistical logic: (1) Based on sampled traffic, rank destination domain names in each attack event by peak QPS. (2) Compare across attack events and select the top 10 — one value per domain name, up to 10 distinct destination domain names. |
Protection metrics
| Metric | Description |
|---|---|
| Top 10 destination ports by attack | Displayed only when the query includes an instance. The top 10 destination ports targeted by attacks. Statistical logic: (1) Based on sampled traffic, rank destinations (IP address and port) in each attack event by number of discarded requests. (2) Compare across attack events and select the top 10 — one value per destination, up to 10 distinct destinations. |
| Defense against application-layer attacks by module | Displayed only when the query includes a domain name. Shows which mitigation policies filtered the application-layer attacks. |
Attack events
This section lists all attack events for the selected instance or domain name within the specified time range. Click View Details in the Actions column to open the Attack Analysis page for full event details.
What's next
For report metrics specific to Anti-DDoS Origin, see Statistical report (Anti-DDoS Origin).