After you add a service to Anti-DDoS Proxy, the proxy forwards all traffic to your origin server. Your origin server can retrieve the client's originating IP address by parsing the X-Forwarded-For header or installing a TOA module.
For non-website services (Layer 4)
For some non-website services, you can install the TOA module on your origin server to obtain the originating IP address. For instructions, see Obtain the originating IP address of a request by installing the TOA module. If you cannot install the TOA module in your environment, contact technical support.
Anti-DDoS Proxy IPv4 instance
Anti-DDoS Proxy uses the TCP Option field to transmit the originating IP address. After the proxy and your origin server complete a three-way handshake, the final ACK packet contains an 8-byte TCP option of Type 254. This option contains the source port number and source IP address. The following figure shows the location of this information.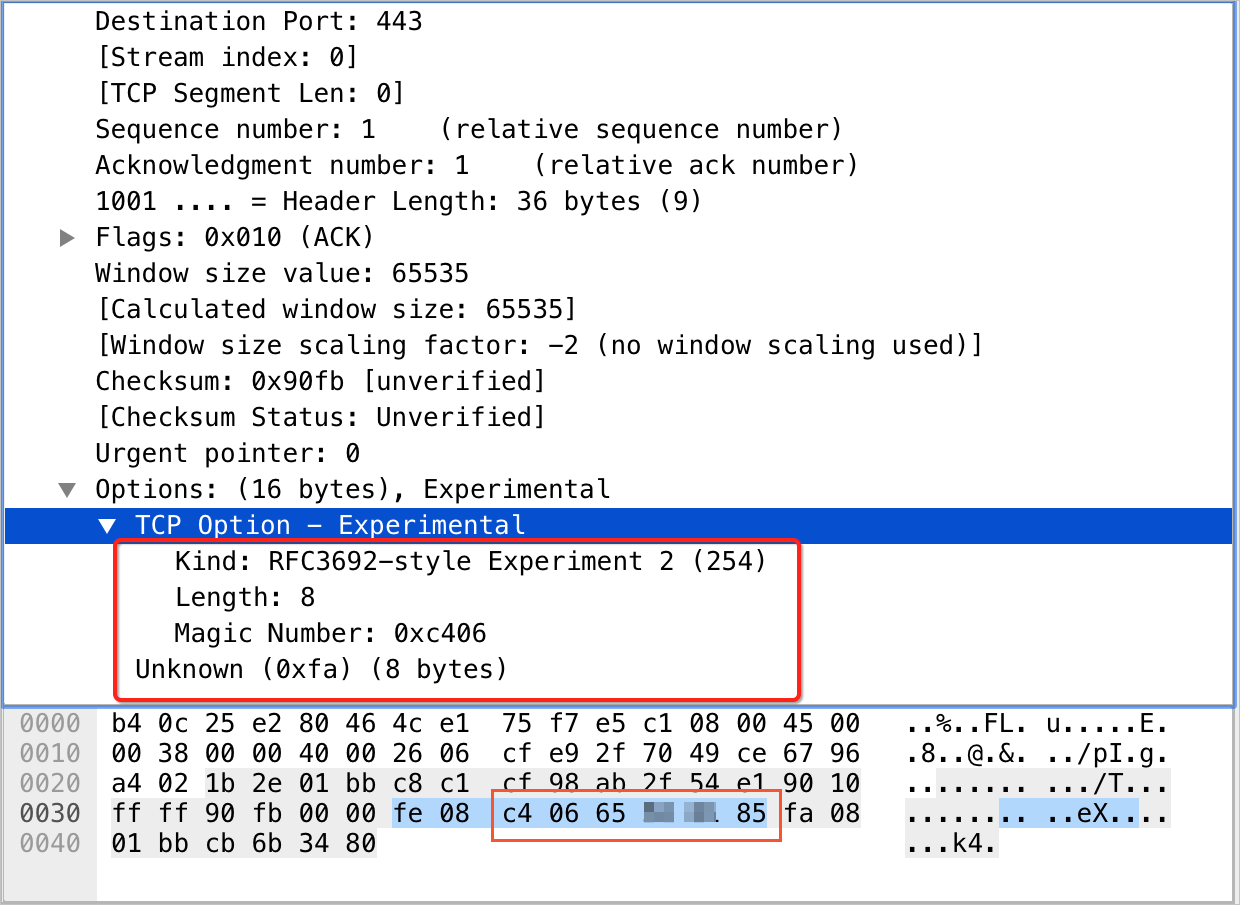
Port number: The
Magic Numberfield represents the port number and is expressed in hexadecimal characters. For example, the value c4 06 converts to the decimal port number 50182.Source IP address: The four consecutive bytes after the port number contain the source IP address in hexadecimal. For example,
65 ** ** 85converts to the decimal IP address101.***.***.133.
Anti-DDoS Proxy IPv6 instance
v6tov4 mode
In v6tov4 mode, where the proxy has an IPv6 address and the origin server has an IPv4 address, the proxy uses the TCP Option field. After a three-way handshake, the final ACK packet contains a 40-byte TCP option of Type 249. This option contains the source port, source IP, and the Anti-DDoS Proxy IP address. The following figure shows the location of this information.
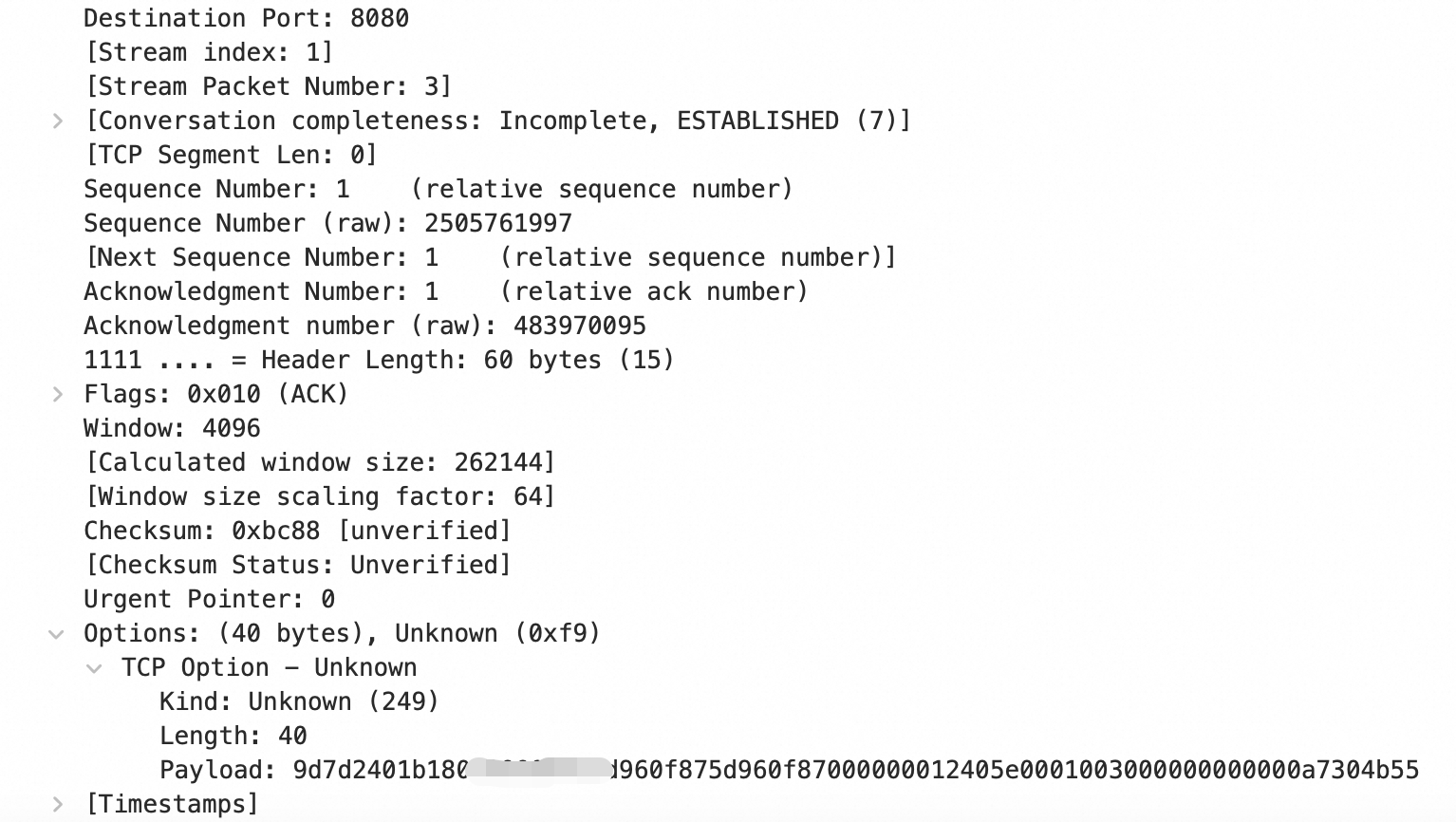
Port number: In the
Payload, the first two bytes represent the port number in hexadecimal format. For example,9d7dconverts to the decimal value 40317.Source IP address: The 16 consecutive bytes after the port number contain the source IPv6 address in hexadecimal. For example,
2401*****0f87corresponds to the IP address2401:b180:100*:*:*:f87:5d96:f87.NoteIn the
Payload, apart from the port number and source IP address, the remaining twenty bytes contain the Anti-DDoS IP information.
v6tov6 mode
In v6tov6 mode, where both the proxy and the origin server use IPv6 addresses, the proxy uses the TCP Option field. After a three-way handshake, the final ACK packet contains a 20-byte TCP option of Type 253 that contains the source port and source IP address. The following figure shows the location of this information.

Port number: The
Experiment Identifierfield specifies the port number in hexadecimal characters. For example, the hexadecimal value eb98 corresponds to the decimal port number 60312.Source IP address: The
Datafield represents the source IP address as a hexadecimal string that directly corresponds to the IPv6 address. For example, the value 2401*****0f87 means the source IP address is 2401:b180:100*:*:*:f87:5d96:f87.
To prevent back-to-origin traffic from Anti-DDoS Proxy from being blocked, you must add the back-to-origin CIDR blocks of Anti-DDoS Proxy to the whitelist on your origin server. To find the back-to-origin CIDR blocks, see Allow back-to-origin CIDR blocks to access the origin server.
If your network architecture is Anti-DDoS Proxy -> ECS, add the back-to-origin CIDR blocks of Anti-DDoS Proxy to the security group of the ECS instance. For more information, see Add a security group rule.
If your network architecture is Anti-DDoS Proxy -> SLB -> ECS, add the back-to-origin CIDR blocks of Anti-DDoS Proxy to the access control whitelist of the SLB instance. For more information, see Enable access control.
For website services (Layer 7)
Method 1: Use the X-Forwarded-For header
How it works
When a Layer 7 proxy server, such as Anti-DDoS Proxy, forwards a request to an origin server, the origin server perceives the request as originating from the proxy's IP address. The
X-Forwarded-ForHTTP header records the client's actual originating IP address. The format is:X-Forwarded-For: <originating_IP_address>.If a request passes through one or more proxy servers (such as WAF or CDN) before it reaches an origin server, the
X-Forwarded-ForHTTP header records the real source IP and the IPs of all proxy servers that the request passes through. The format isX-Forwarded-For: real-client-IP, proxy-server-1-IP, proxy-server-2-IP, proxy-server-3-IP, .... When a proxy node forwards the request to the origin server, it appends the address of the previous node to theX-Forwarded-Forheader but does not append its own IP.
Retrieval methods
The following code snippets show how to retrieve the X-Forwarded-For header value in various programming languages:
After you retrieve the value of the
X-Forwarded-Forheader, take the first IP address in the comma-separated list. This IP address is the client's originating IP address.You can also configure your web server (such as Nginx, IIS 6, IIS 7, Apache, or Tomcat) to parse the
X-Forwarded-Forheader to obtain the originating IP address. For more information, see Retrieve the originating IP addresses of clients.
ASP
Request.ServerVariables("HTTP_X_FORWARDED_FOR")ASP.NET (C#)
Request.ServerVariables["HTTP_X_FORWARDED_FOR"]PHP
$_SERVER["HTTP_X_FORWARDED_FOR"]JSP
request.getHeader("HTTP_X_FORWARDED_FOR")
Method 2: Use a custom HTTP header
Overview
In complex network architectures, relying on the standard X-Forwarded-For (XFF) header can introduce risks such as header forgery, IP address confusion from multiple proxy layers, and complex parsing logic. To enhance security and control, you can use a custom HTTP header to transmit the client's originating IP address.
Procedure
You can configure Anti-DDoS Proxy to write the client IP address to a custom HTTP header. For more information, see Configure back-to-origin settings.
Log on to the Website Config page in the Anti-DDoS Proxy console.
On the Website Config page, click Add Website.
On the Website Config page, in the Forwarding Settings section, set Traffic Marking to Custom Header (for example,
Custom-True-IP).In your application code, retrieve the value of the custom header, for example:
request.getHeader("Custom-True-IP").