After you add an object to an Anti-DDoS Origin instance for protection, the default mitigation policy is automatically applied to the object. This policy can effectively reduce the risks that are caused when an attack occurs. This topic describes how to change the default mitigation policy.
What is the default mitigation policy?
The default mitigation policy is a collection of common mitigation rules that are accumulated from a large number of daily attack and defense events handled by the anti-DDoS engine. The policy can mitigate volumetric attacks with known characteristics. When an attack with known characteristics occurs, the policy immediately takes effect and reduces the risks caused by the attack.
The default mitigation policy takes effect only when protected objects are under attack.
Built-in mitigation policies
The built-in mitigation policies are Normal, Loose, and Strict. After you add an object to your Anti-DDoS Origin instance for protection, the Normal mitigation policy is automatically applied.
Policy | Mitigation method | Description |
Loose |
| The Loose mitigation policy protects against only packets that have clear attack characteristics. However, traffic of complicated attacks may be transparently transmitted to your origin server. We recommend that you select this policy only if false positives are generated for your service. |
Normal |
| The Normal mitigation policy protects against common DDoS attacks and is suitable for most services. |
Strict |
| The Strict mitigation policy provides strong protection. In rare cases, false positives may be generated. We recommend that you select this policy only if attack traffic is transparently transmitted to your origin server. |
Scenario-specific mitigation policies
The following scenario-specific mitigation policies are provided to protect elastic IP addresses (EIPs) with Anti-DDoS (Enhanced) enabled.
Policy | Mitigation method | Description |
Policy for Office Network |
| The policy loosely limits outbound access and is suitable for office networks. |
TCP Game Policy |
| If your service is based on TCP, we recommend that you select this policy. |
UDP Game Policy |
| If your service is based on UDP, we recommend that you select this policy. |
Prerequisites
An Anti-DDoS Origin instance is purchased. For more information, see Purchase an Anti-DDoS Origin instance.
The assets that you want to protect are added to the Anti-DDoS Origin instance. For more information, see Add objects for protection.
Procedure
Log on to the Traffic Security console.
In the top navigation bar, select the resource group to which the instance belongs and the region in which the instance resides.
Anti-DDoS Origin 1.0 (Subscription) instance: Select the region in which the instance resides.
Anti-DDoS Origin 2.0 (Subscription) instance and Anti-DDoS Origin 2.0 (Pay-as-you-go) instance: Select All Regions.
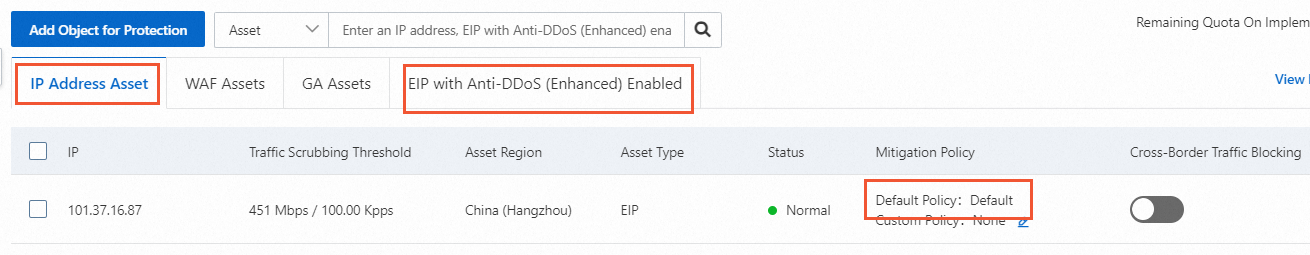
On the Protected Objects page, change Default Policy.
If your asset is an IP address, you can set Default Policy only to a built-in mitigation policy.
If your asset is an EIP with Anti-DDoS (Enhanced) enabled, you can set Default Policy to a built-in or scenario-specific mitigation policy.
References
You can also create a custom mitigation policy for a protected object based on your business requirements. For more information, see Custom mitigation policies.