When you use a custom Object Storage Service (OSS) bucket with Container Registry, you must grant Container Registry permission to access that bucket through a RAM role. This topic walks you through creating the required RAM role and attaching the access policy.
Storage options for Container Registry
Container Registry can store image data in either a system-managed bucket or a bucket you control:
| Storage option | What you need to do |
|---|---|
| Default OSS bucket | Grant Container Registry the permissions to access cloud resources. Container Registry then creates the bucket and initializes the instance automatically. |
| Custom OSS bucket | Create a RAM role named AliyunContainerRegistryCustomizedOSSBucketRole, attach the AliyunContainerRegistryCustomizedOSSBucketRolePolicy policy to it, and Container Registry assumes the role to access your bucket. |
Prerequisites
Before you begin, make sure you have:
-
An Alibaba Cloud account with administrative access to the RAM console
-
A custom OSS bucket that you want Container Registry to use
Step 1: Create a RAM role
Create a role named AliyunContainerRegistryCustomizedOSSBucketRole for the Alibaba Cloud account that owns your Container Registry instance.
-
Log on to the RAM console as a RAM user with administrative rights.
-
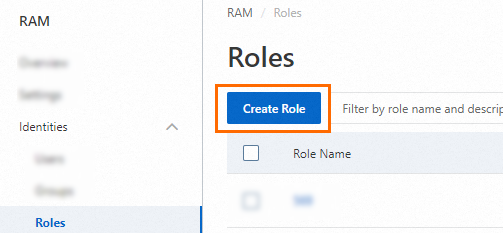
In the left-side navigation pane, choose Identities > Roles.
-
On the Roles page, click Create Role.
-
On the Create Role page, set Principal Type to Cloud Account, specify the trusted Alibaba Cloud account, and click OK.
-
Current Account: Select this option if the RAM user or RAM role that assumes this role belongs to your own Alibaba Cloud account.
-
Other Account: Select this option if the entity that assumes this role belongs to a different Alibaba Cloud account. Enter the Alibaba Cloud account ID. For details, see Use a RAM role to grant permissions across Alibaba Cloud accountsYou can view the ID of your Alibaba Cloud account on the Security Settings page.. You can find your account ID on the Security Settings page.

-
-
(Optional) To restrict which RAM user or RAM role can assume this role, click Switch to Policy Editor and update the trust policy. The editor supports Visual editor and JSON modes. The following example restricts role assumption to the RAM user
Alicein account100******0719:{ "Version": "1", "Statement": [ { "Effect": "Allow", "Principal": { "RAM": "acs:ram::100******0719:user/Alice" }, "Action": "sts:AssumeRole" } ] }In the Visual editor, set Principal to the target RAM user. In JSON mode, replace the account ID and username in the
RAMfield.

-
In the Create Role dialog box, set Role Name to
AliyunContainerRegistryCustomizedOSSBucketRoleand click OK.
Step 2: Attach the access policy
Attach the AliyunContainerRegistryCustomizedOSSBucketRolePolicy policy to the role you created in Step 1. This policy grants Container Registry the permissions it needs to read and write image data in your custom OSS bucket.
The policy contains five groups of permissions:
| Permission group | Actions | Purpose |
|---|---|---|
| Object operations | oss:GetObject, oss:PutObject, oss:DeleteObject, and related actions |
Read, write, and delete image layers and manifests stored as OSS objects |
| Bucket operations | oss:GetBucket, oss:PutBucketEncryption, oss:PutBucketVersioning, and related actions |
Inspect and configure the bucket's encryption, ACLs, versioning, lifecycle rules, and logging |
| List buckets | oss:ListBuckets |
Discover available buckets during instance initialization |
| VPC operations | vpc:DescribeVpcs |
Verify network connectivity for private access configurations |
| Monitoring | cms:QueryMetricLast, cms:QueryMetricList |
Query CloudMonitor metrics for the bucket |
Replace <YOUR_BUCKET_NAME> in the policy below with the name of your custom OSS bucket, then attach the policy to the role:
{
"Version": "1",
"Statement": [
{
"Action": [
"oss:GetObject",
"oss:PutObject",
"oss:DeleteObject",
"oss:ListParts",
"oss:AbortMultipartUpload",
"oss:InitiateMultipartUpload",
"oss:CompleteMultipartUpload",
"oss:DeleteMultipleObjects",
"oss:ListMultipartUploads",
"oss:ListObjects",
"oss:DeleteObjectVersion",
"oss:GetObjectVersion",
"oss:ListObjectVersions",
"oss:PutObjectTagging",
"oss:GetObjectTagging",
"oss:DeleteObjectTagging"
],
"Resource": [
"acs:oss:*:*:cri-*",
"acs:oss:*:*:cri-*/*",
"acs:oss:*:*:<YOUR_BUCKET_NAME>",
"acs:oss:*:*:<YOUR_BUCKET_NAME>/*"
],
"Effect": "Allow",
"Condition": {}
},
{
"Action": [
"oss:PutBucket",
"oss:GetBucket",
"oss:GetBucketLocation",
"oss:PutBucketEncryption",
"oss:GetBucketEncryption",
"oss:PutBucketAcl",
"oss:GetBucketAcl",
"oss:PutBucketLogging",
"oss:GetBucketReferer",
"oss:PutBucketReferer",
"oss:GetBucketLogging",
"oss:PutBucketVersioning",
"oss:GetBucketVersioning",
"oss:GetBucketLifecycle",
"oss:PutBucketLifecycle",
"oss:DeleteBucketLifecycle",
"oss:GetBucketTransferAcceleration"
],
"Resource": [
"acs:oss:*:*:cri-*",
"acs:oss:*:*:cri-*/*",
"acs:oss:*:*:<YOUR_BUCKET_NAME>",
"acs:oss:*:*:<YOUR_BUCKET_NAME>/*"
],
"Effect": "Allow",
"Condition": {}
},
{
"Effect": "Allow",
"Action": "oss:ListBuckets",
"Resource": [
"acs:oss:*:*:*",
"acs:oss:*:*:*/*"
],
"Condition": {}
},
{
"Action": [
"vpc:DescribeVpcs"
],
"Resource": "acs:vpc:*:*:vpc/*",
"Effect": "Allow",
"Condition": {}
},
{
"Action": [
"cms:QueryMetricLast",
"cms:QueryMetricList"
],
"Resource": "*",
"Effect": "Allow"
}
]
}To grant access to multiple custom buckets, add an entry for each additional bucket to the Resource array in the first two statements:
"acs:oss:*:*:<YOUR_SECOND_BUCKET_NAME>",
"acs:oss:*:*:<YOUR_SECOND_BUCKET_NAME>/*"