Elastic Container Instance (ECI) can authenticate with Alibaba Cloud Container Registry (ACR) on your behalf using RAM roles, so pods and image caches can pull images without embedding registry credentials as Kubernetes Secrets. This eliminates the risk of credential leaks and removes the overhead of managing secret rotation.
This only works for images hosted in ACR. Images from external registries (such as Docker Hub) still require a Kubernetes Secret.
How it works
ECI uses the service-linked role AliyunServiceRoleForECI to obtain a temporary token from Container Registry when pulling images. The service-linked role acts as the credential — no registry secret is stored in the pod spec.
By default, AliyunServiceRoleForECI grants access to all Personal Edition instances and all Enterprise Edition instances that use a default domain name in the same Alibaba Cloud account. Fine-grained control over which instances a workload can access requires an explicit RAM role configuration.
Container Registry provides two editions: Personal Edition and Enterprise Edition. Enterprise Edition is an enterprise-grade platform for managing the lifecycle of cloud native application artifacts, including container images, Helm charts, and Open Container Initiative (OCI) artifacts. It is suitable for large-scale business deployment scenarios.
Which configuration applies to you
Use this table to identify your scenario before reading further.
| Scenario | Configuration required |
|---|---|
| Same account — Personal Edition or Enterprise Edition with a default domain name | Secret-free pull is already enabled. No action required. Optionally, scope down with a custom RAM role to restrict which instances are accessible. |
| Same account — Enterprise Edition with a custom domain name | Specify instance IDs using the k8s.aliyun.com/acr-instance-ids annotation. |
| Different accounts — any edition | Chain RAM roles across accounts using k8s.aliyun.com/acr-service-arns and k8s.aliyun.com/acr-user-arns. |
Prerequisites
Before you begin, ensure that you have:
-
A Container Registry instance with image repositories and images configured. See Use a Container Registry Personal Edition instance to push and pull images or Use a Container Registry Enterprise Edition instance to push and pull images
-
For Enterprise Edition instances: network access configured. By default, a newly created Enterprise Edition instance is disconnected from all networks. Configure at least one of the following:
-
Internet access: Enable access via public endpoints. See Enable Internet access. Supports cross-region image pulls.
-
VPC access: Enable access using the service-linked role
AliyunServiceRoleForContainerRegistryAccessCustomerPrivateZone. See Configure a VPC ACL
-
Scope down with a custom RAM role
When this applies: Your ECI workload and Container Registry instance are in the same Alibaba Cloud account, and the instance is a Personal Edition instance or an Enterprise Edition instance with a default domain name.
Secret-free pull is already enabled for this scenario — no configuration is required to start pulling images. However, the default AliyunServiceRoleForECI role grants access to all matching instances in the account. To restrict which instances a specific workload can pull from, create a custom RAM role with a scoped policy and reference it in the pod annotation.
Step 1: Create and configure the RAM role
-
Create a RAM role for a trusted Alibaba Cloud service. See Create a RAM role for a trusted Alibaba Cloud service. Use the following parameters:
Parameter Value Select Trusted Entity Alibaba Cloud Service Role Type Normal Service Role RAM Role Name Example: acr-testSelect Trusted Service ECI -
Create a custom permission policy. See Create a custom policy. The following policy allows listing all instances (
cr:Get*,cr:List*) but restricts image pulls to a single specified instance:{ "Version": "1", "Statement": [ { "Effect": "Allow", "Action": [ "cr:Get*", "cr:List*" ], "Resource": "*" }, { "Effect": "Allow", "Action": [ "cr:Pull*" ], "Resource": [ "acs:cr:cn-hangzhou:1609982529******:instance/cri-nwj395hgf6f3****" ] } ] }Replace the
ResourceARN with the ARN of your Container Registry instance. For the policy syntax, see Policy elements. -
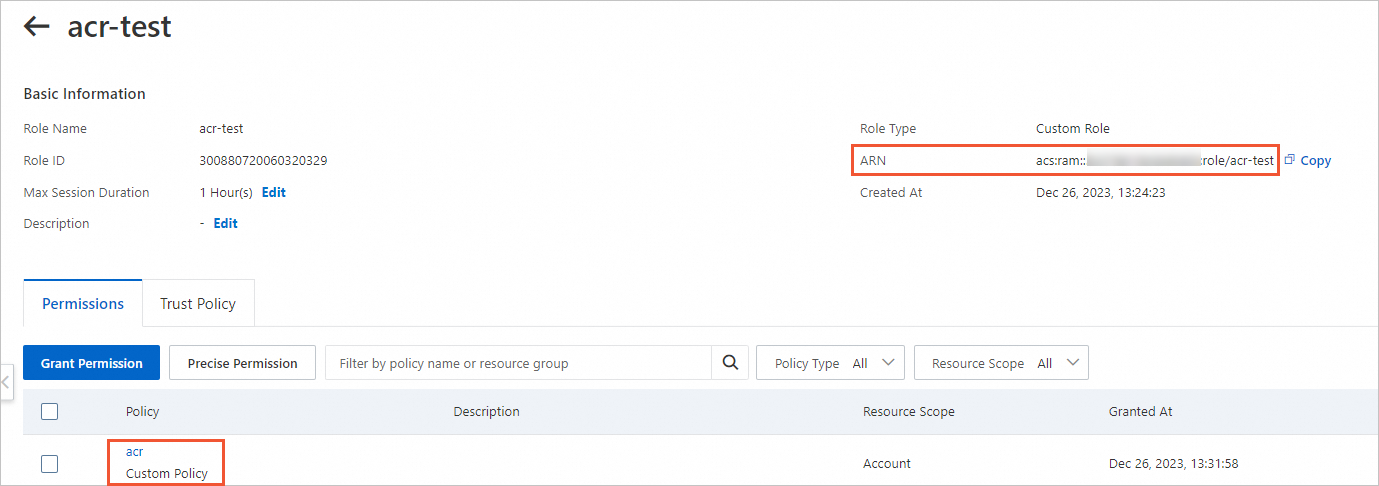
Attach the custom policy to the RAM role. See Grant permissions to a RAM role.
-
On the role details page, verify the permissions and copy the Alibaba Cloud Resource Name (ARN) of the role. You need this ARN in the next step.
Step 2: Reference the RAM role in your workload
Add the k8s.aliyun.com/acr-service-arns annotation to your pod spec, referencing the ARN from Step 1.
-
Add annotations to
metadatain the pod configuration. For a Deployment, add them tospec.template.metadata. -
Annotations only take effect when you create an ECI-based pod. Adding or modifying annotations on an existing pod has no effect.
apiVersion: apps/v1
kind: Deployment
metadata:
name: test
labels:
app: test
spec:
replicas: 2
selector:
matchLabels:
app: nginx
template:
metadata:
name: nginx-test
labels:
app: nginx
alibabacloud.com/eci: "true"
annotations:
k8s.aliyun.com/acr-service-arns: "acs:ram::1609982529******:role/acr-test" # ARN of the RAM role
spec:
containers:
- name: nginx
image: test****-registry.cn-hangzhou.cr.aliyuncs.com/eci_test/nginx:1.0 # Image in the allowed instance
ports:
- containerPort: 80Specify instance IDs for custom-domain Enterprise Edition
When this applies: Your ECI workload and Container Registry Enterprise Edition instance are in the same Alibaba Cloud account, and the instance uses a custom domain name.
Secret-free pull is not enabled by default for this scenario. Add the k8s.aliyun.com/acr-instance-ids annotation to specify which instances are accessible.
Enterprise Edition instances can be used across regions. To pull from an instance in a different region, prefix the instance ID with the region ID: cn-beijing:cri-j36zhodptmyq****.
Create a pod
Add the k8s.aliyun.com/acr-instance-ids annotation to spec.template.metadata in your Deployment:
-
Add annotations to
metadatain the pod configuration. For a Deployment, add them tospec.template.metadata. -
Annotations only take effect when you create an ECI-based pod. Adding or modifying annotations on an existing pod has no effect.
apiVersion: apps/v1
kind: Deployment
metadata:
name: test
labels:
app: test
spec:
replicas: 2
selector:
matchLabels:
app: nginx
template:
metadata:
name: nginx-test
labels:
app: nginx
alibabacloud.com/eci: "true"
annotations:
k8s.aliyun.com/acr-instance-ids: "cri-j36zhodptmyq****" # Container Registry instance ID
spec:
containers:
- name: nginx
image: test****-registry.example.com/eci_test/nginx:1.0 # Image using a custom domain name
ports:
- containerPort: 80Create an image cache
Add the same k8s.aliyun.com/acr-instance-ids annotation to the image cache metadata:
apiVersion: eci.alibabacloud.com/v1
kind: ImageCache
metadata:
name: imagecache-sample
annotations:
k8s.aliyun.com/acr-instance-ids: "cri-j36zhodptmyq****" # Container Registry instance ID
spec:
images:
- test****-registry.example.com/eci_test/nginx:1.0 # Image using a custom domain name
imagePullSecrets:
- default:secret1
- default:secret2
- kube-system:secret3
imageCacheSize: 25
retentionDays: 7Pull images across Alibaba Cloud accounts
When this applies: Your Container Registry instance and ECI workload belong to different Alibaba Cloud accounts.
Secret-free pull is not enabled by default for this scenario. Chain RAM roles across the two accounts using Security Token Service (STS).
The setup requires two roles:
-
Account A (the account running ECI): a role with permission to call the STS
AssumeRoleAPI. -
Account B (the account owning the Container Registry instance): a role that trusts Account A's role and grants Container Registry access.
Step 1: Create RAM roles in both accounts
In Account A (ECI account):
-
Create a RAM role for a trusted Alibaba Cloud service. See Create a RAM role for a trusted Alibaba Cloud service.
Parameter Value Select Trusted Entity Alibaba Cloud Service Role Type Normal Service Role RAM Role Name Example: role-assumeSelect Trusted Service ECI -
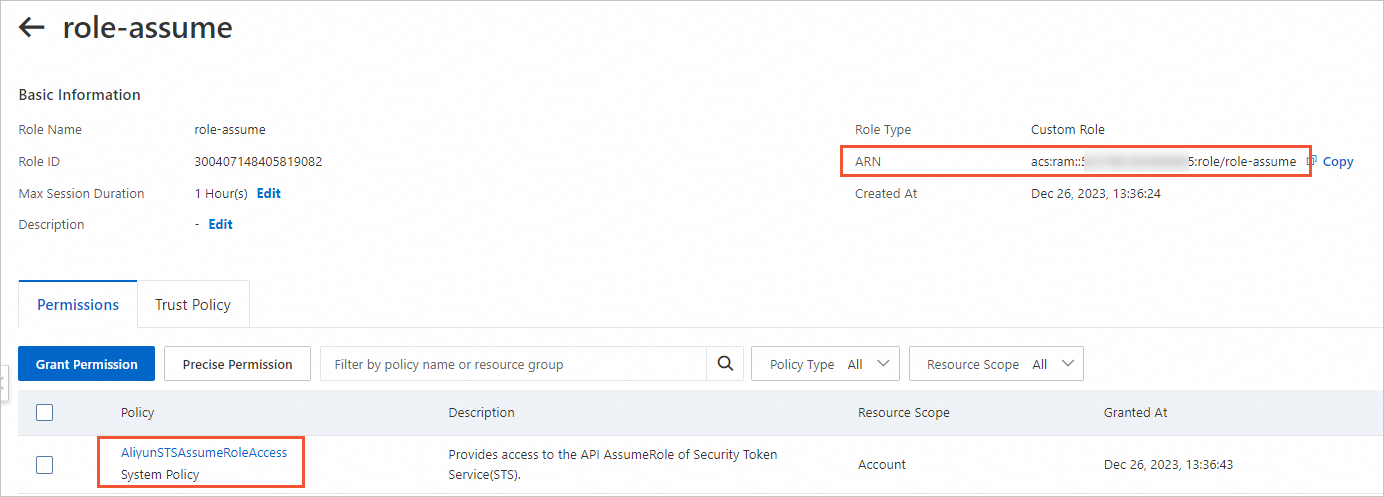
Grant the
role-assumerole theAliyunSTSAssumeRoleAccesssystem policy. See the "Method 2" section of Grant permissions to a RAM role. -
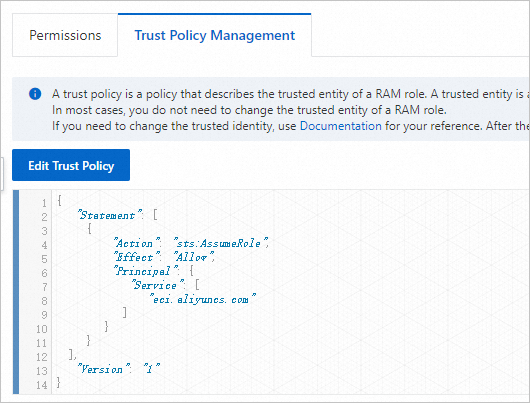
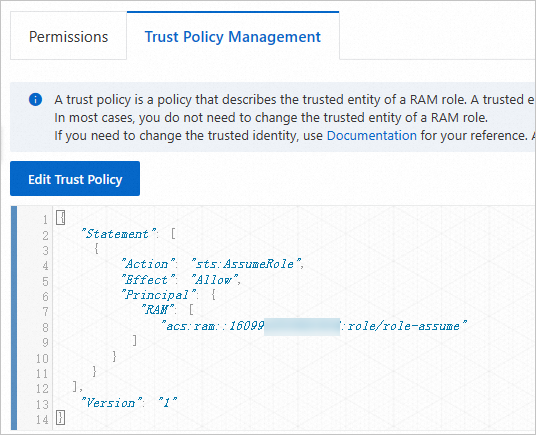
On the role details page, verify the permissions and trust policy, and copy the ARN of
role-assume.-
Permissions and ARN:
-
Trust policy:
-
In Account B (Container Registry account):
-
Create a RAM role for a trusted Alibaba Cloud account. See Create a RAM role for a trusted Alibaba Cloud account.
Parameter Value Select Trusted Entity Alibaba Cloud Account RAM Role Name Example: role-acrSelect Trusted Alibaba Cloud Account Other Alibaba Cloud Account — enter Account A to which the ECI resource belongs -
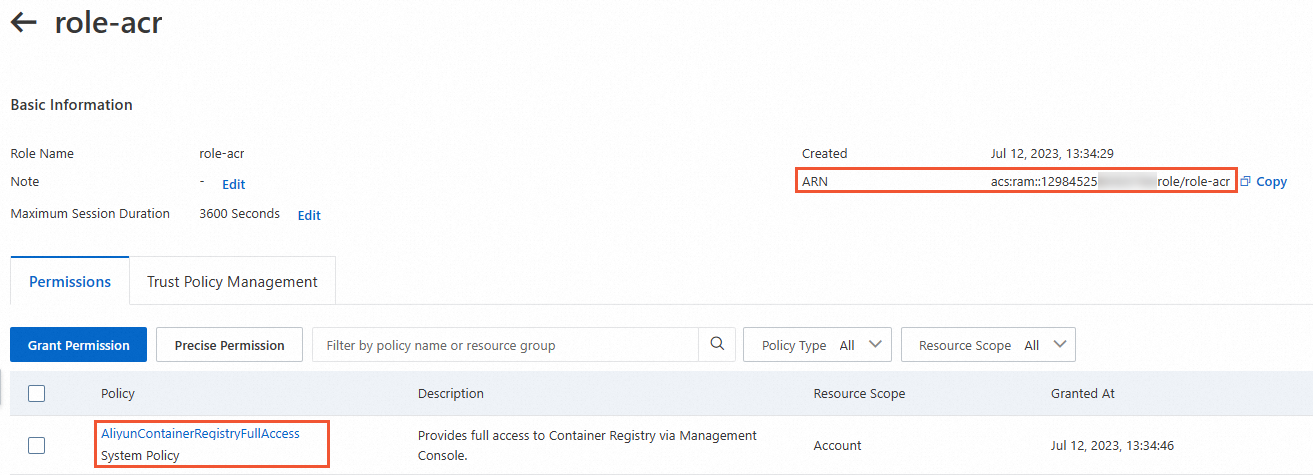
Grant the
role-acrrole theAliyunContainerRegistryFullAccesssystem policy. See the "Method 2" section of Grant permissions to a RAM role. -
Edit the trust policy of
role-acrto restrict assumption torole-assumeonly. See Edit the trust policy of a RAM role. By default,role-acrcan be assumed by any RAM user or role in Account A. To restrict access, set theRAMfield in thePrincipalelement to the ARN ofrole-assume:"Principal": { "RAM": [ "acs:ram::1609982529******:role/role-assume" ] } -
Verify the permissions and trust policy, and copy the ARN of
role-acr.-
Permissions and ARN:
-
Trust policy:
-
Step 2: Reference both RAM roles in your workload
Add the following annotations to your pod or image cache. All three annotations are required when the Container Registry instance uses a custom domain name:
| Annotation | Value |
|---|---|
k8s.aliyun.com/acr-instance-ids |
ID of the Container Registry Enterprise Edition instance (required for custom domain names) |
k8s.aliyun.com/acr-service-arns |
ARN of the RAM role in Account A (role-assume) |
k8s.aliyun.com/acr-user-arns |
ARN of the RAM role in Account B (role-acr) |
Enterprise Edition instances can be used across regions. To pull from an instance in a different region, prefix the instance ID with the region ID: cn-beijing:cri-j36zhodptmyq****.
-
Add annotations to
metadatain the pod configuration. For a Deployment, add them tospec.template.metadata. -
Annotations only take effect when you create an ECI-based pod. Adding or modifying annotations on an existing pod has no effect.
Create a pod:
apiVersion: apps/v1
kind: Deployment
metadata:
name: test
labels:
app: test
spec:
replicas: 1
selector:
matchLabels:
app: nginx
template:
metadata:
name: nginx-test
labels:
app: nginx
alibabacloud.com/eci: "true"
annotations:
k8s.aliyun.com/acr-instance-ids: "cri-j36zhodptmyq****"
k8s.aliyun.com/acr-service-arns: "acs:ram::1609982529******:role/role-assume"
k8s.aliyun.com/acr-user-arns: "acs:ram::1298452580******:role/role-acr"
spec:
containers:
- name: nginx
image: test****-registry.example.com/eci_test/nginx:1.0 # Image using a custom domain name
ports:
- containerPort: 80Create an image cache:
apiVersion: eci.alibabacloud.com/v1
kind: ImageCache
metadata:
name: imagecache-sample
annotations:
k8s.aliyun.com/acr-instance-ids: "cri-j36zhodptmyq****"
k8s.aliyun.com/acr-service-arns: "acs:ram::1609982529******:role/role-assume"
k8s.aliyun.com/acr-user-arns: "acs:ram::1298452580******:role/role-acr"
spec:
images:
- test****-registry.example.com/eci_test/nginx:1.0 # Image using a custom domain name
imagePullSecrets:
- default:secret1
- default:secret2
- kube-system:secret3
imageCacheSize: 25
retentionDays: 7