Applies to: ACK managed clusters using the Terway network plugin
ack-kubernetes-webhook-injector automatically adds a pod's IP address to a cloud service whitelist when the pod starts, and removes it when the pod is deleted. This gives you fine-grained, lifecycle-aware access control for ApsaraDB RDS, ApsaraDB for Redis, and Server Load Balancer (SLB) — without manually maintaining whitelist entries.
How it works
When you add specific annotations to a pod spec, ack-kubernetes-webhook-injector intercepts pod creation and deletion events through an admission webhook and calls the corresponding Alibaba Cloud service API to update the whitelist.
Supported services:
| Service | What is controlled |
|---|---|
| ApsaraDB RDS | Named whitelist group |
| ApsaraDB for Redis | Named whitelist group |
| Server Load Balancer (SLB) | Access control list (ACL) |
Prerequisites
Before you begin, ensure that you have:
An ACK managed cluster. For more information, see Create an ACK managed cluster
A kubectl client connected to the cluster. For more information, see Obtain the kubeconfig file of a cluster and use kubectl to connect to the cluster
The Terway network plugin installed on the cluster. For more information, see Work with Terway
Limitations
The cluster must use the Terway network plugin. Other network plugins are not supported.
By default, ack-kubernetes-webhook-injector calls the public endpoint of Alibaba Cloud services. If your cluster has no public internet access, configure the component to use internal endpoints (see Use internal endpoints).
Some Alibaba Cloud services do not provide internal endpoints in all regions. Check OpenAPI Explorer to confirm endpoint availability before deploying in private clusters.
Install ack-kubernetes-webhook-injector
Log on to the ACK console. In the left-side navigation pane, choose Marketplace > Marketplace.
Find and click ack-kubernetes-webhook-injector. In the upper-right corner of the page, click Deploy.
In the panel that appears, specify a cluster and namespace for the component, enter a release name, and click Next.
On the Parameters wizard page, set
akandskin theopenapisection to your AccessKey ID and AccessKey Secret, then click OK. For more information, see Obtain an AccessKey pair.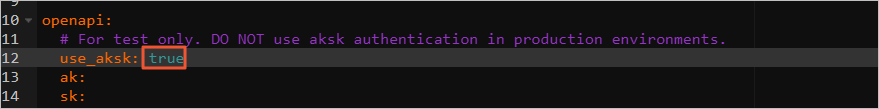
Add pod IP addresses to an ApsaraDB RDS whitelist
Add two annotations to your pod spec to specify the target ApsaraDB RDS instance and whitelist group:
| Annotation | Description |
|---|---|
ack.aliyun.com/rds_id | ID of the ApsaraDB RDS instance |
ack.aliyun.com/white_list_name | Name of the whitelist group |
ack-kubernetes-webhook-injector automatically adds the pod IP to the whitelist when the pod starts and removes it when the pod is deleted.
Example: deploy with RDS whitelist annotations
Create a Deployment using the following YAML. Replace
<rm-wz9nanjcud75b****>with your RDS instance ID and<rds_group>with your whitelist group name.apiVersion: apps/v1 kind: Deployment metadata: labels: app: inject-test name: inject-test spec: replicas: 1 selector: matchLabels: app: inject-test template: metadata: annotations: ack.aliyun.com/rds_id: <rm-wz9nanjcud75b****> ack.aliyun.com/white_list_name: <rds_group> labels: app: inject-test spec: containers: - command: - sleep - "3600" image: alpine:latest name: inject-testVerify the pod IP address:
kubectl --kubeconfig .kube/config_sts_test -n inject-test get pod -o wideThe output is similar to:
NAME READY STATUS RESTARTS AGE IP NODE inject-test-68cc8f9bbf-gj86n 1/1 Running 0 22s 172.25.0.28 cn-hangzhou.xxxThe pod IP address is
172.25.0.28.Log on to the ApsaraDB RDS console and check the whitelist of the specified RDS instance. Confirm that
172.25.0.28appears in the whitelist group. For more information, see Configure an enhanced IP address whitelist.Scale the Deployment to 0 replicas and check the RDS whitelist again. The pod IP address is automatically removed from the whitelist.
Configure access control for other services
Use the following annotations to configure access control for ApsaraDB for Redis and SLB.
ApsaraDB for Redis whitelist
| Annotation | Description |
|---|---|
ack.aliyun.com/redis_id | ID of the ApsaraDB for Redis instance |
ack.aliyun.com/white_list_name | Name of the whitelist group |
SLB access control list
| Annotation | Description |
|---|---|
ack.aliyun.com/access_control_policy_id | ID of the SLB ACL |
Use internal endpoints
By default, ack-kubernetes-webhook-injector uses the public endpoint of Alibaba Cloud services. If your cluster has public internet access disabled, configure the component to use internal endpoints instead.
Check OpenAPI Explorer to confirm that the target service provides an internal endpoint in your region before making this change.
Log on to the ACK console. In the left-side navigation pane, click Clusters.
On the Clusters page, click the name of your cluster. In the left-side navigation pane, choose Workloads > Deployments.
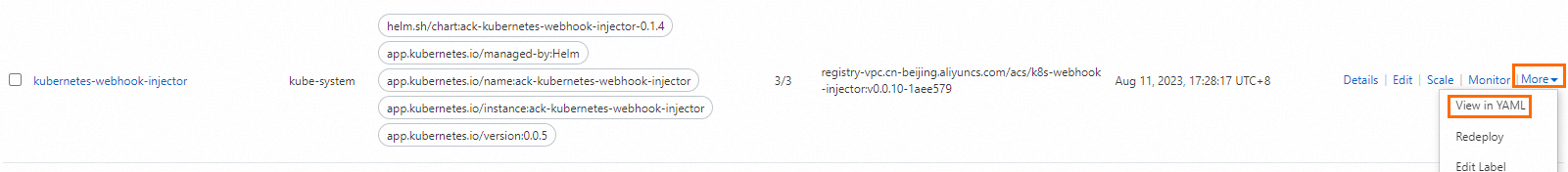
In the top navigation bar, select kube-system from the Namespace drop-down list. Find the kubernetes-webhook-injector Deployment and choose More > View in YAML in the Actions column.
Add
- '--intranet-access'underspec.template.spec.containers.command, then click Update.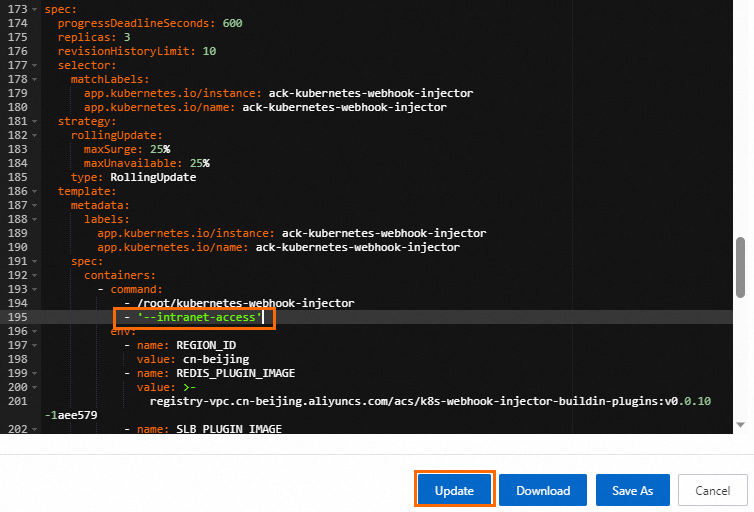
Uninstall ack-kubernetes-webhook-injector
Uninstall ack-kubernetes-webhook-injector using the Helm release feature in ACK. For more information, see Manage releases by using Helm.
After uninstalling, run the following commands to delete the related configurations:
kubectl -n kube-system delete secret kubernetes-webhook-injector-certs
kubectl delete mutatingwebhookconfigurations.admissionregistration.k8s.io kubernetes-webhook-injector