ACK One GitOps, built on ArgoCD, lets you manage application deployments declaratively using Git repositories as the single source of truth — no YAML templates to distribute across clusters. This topic walks you through deploying, updating, and rolling back an application using both the ArgoCD console and the ArgoCD command-line interface (CLI).
What you'll learn
-
Connect a Git repository to ACK One GitOps
-
Create an ArgoCD application and deploy it to a specific cluster
-
Verify the deployment using
kubectl amccommands -
Update an application by pushing a new image tag to Git
-
Roll back to a previous version using ArgoCD's history
Prerequisites
Before you begin, make sure you have:
-
Fleet management enabled
-
Two clusters associated with the Fleet instance — a service provider cluster and a service consumer cluster. See Associate clusters with a Fleet instance
-
The kubeconfig file of the Fleet instance downloaded from the ACK One console, with
kubectlconnected to the Fleet instance -
The latest Alibaba Cloud CLI installed and configured. See Install Alibaba Cloud CLI and Configure credentials. If you use a Resource Access Management (RAM) user, grant the RAM user the AliyunAdcpFullAccess permission. See Grant permissions to a RAM user
-
The latest ArgoCD CLI installed. Download from github.com/argoproj/argo-cd/releases
-
Logged on to the GitOps system. See Log on to the GitOps system
Deploy an application using the ArgoCD console
Step 1: Add a Git repository and deploy the application
1. Log on to the ArgoCD console.
Open the ArgoCD server domain in a browser. For the domain name, see Log on to the GitOps system.
On the ArgoCD homepage, click LOGIN VIA ALIYUN.
2. Add a source Git repository.
In the left-side navigation pane, choose Settings > Repositories and click + CONNECT REPO.
Fill in the repository details and click CONNECT.
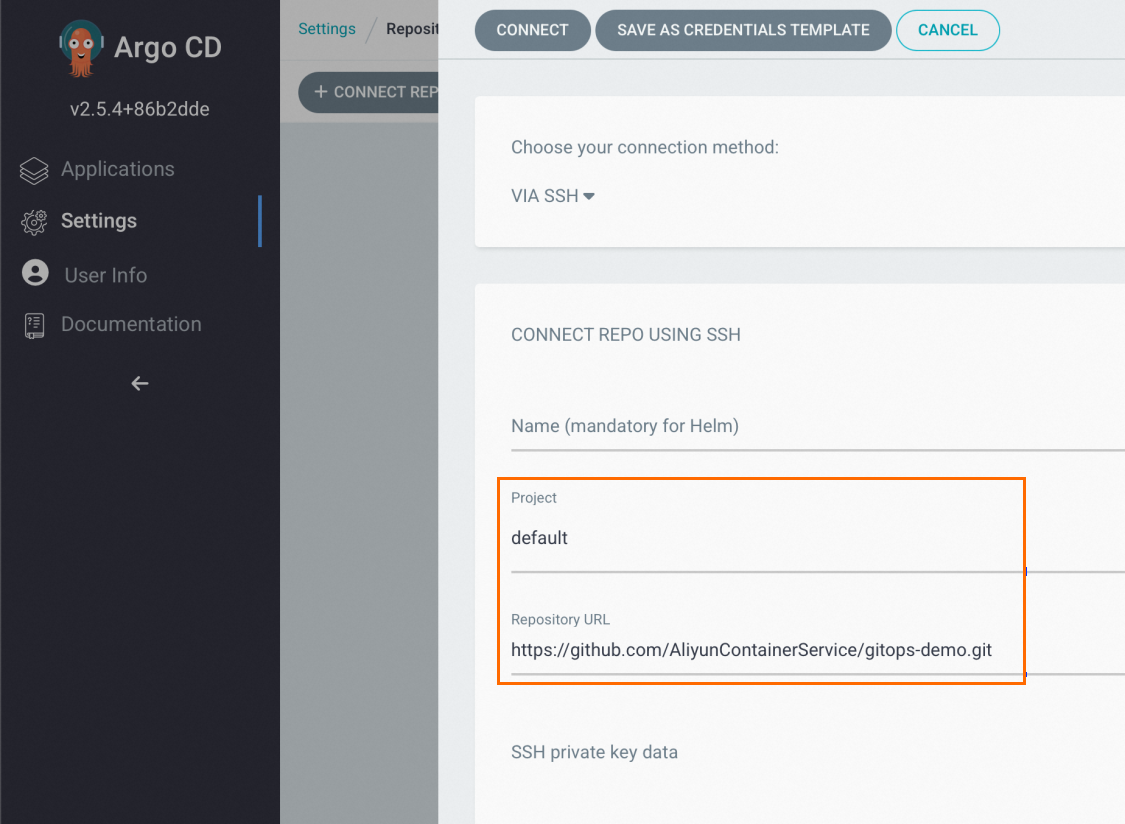
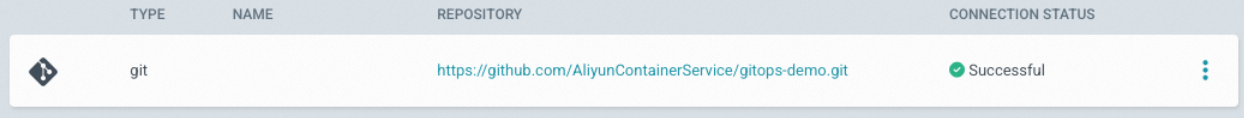
The CONNECTION STATUS column shows Successful when the repository is connected.
3. Create an ArgoCD application.
On the Applications page, click + NEW APP and fill in the application details. ArgoCD pulls the Helm chart from the source Git repository and deploys it to the default namespace of the specified cluster.
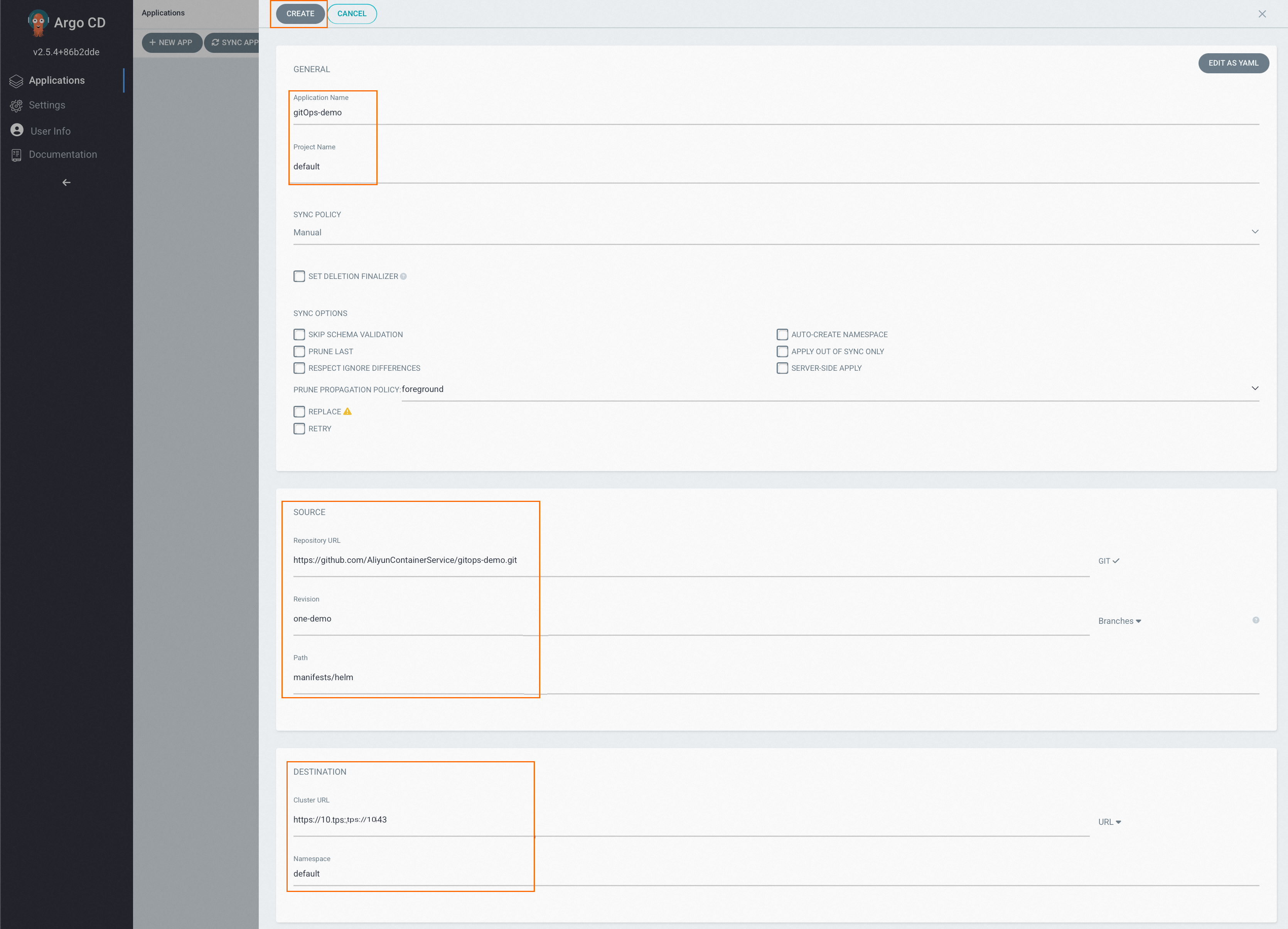
Click CREATE at the top of the panel.
The Applications page now shows the echo-server-app application.
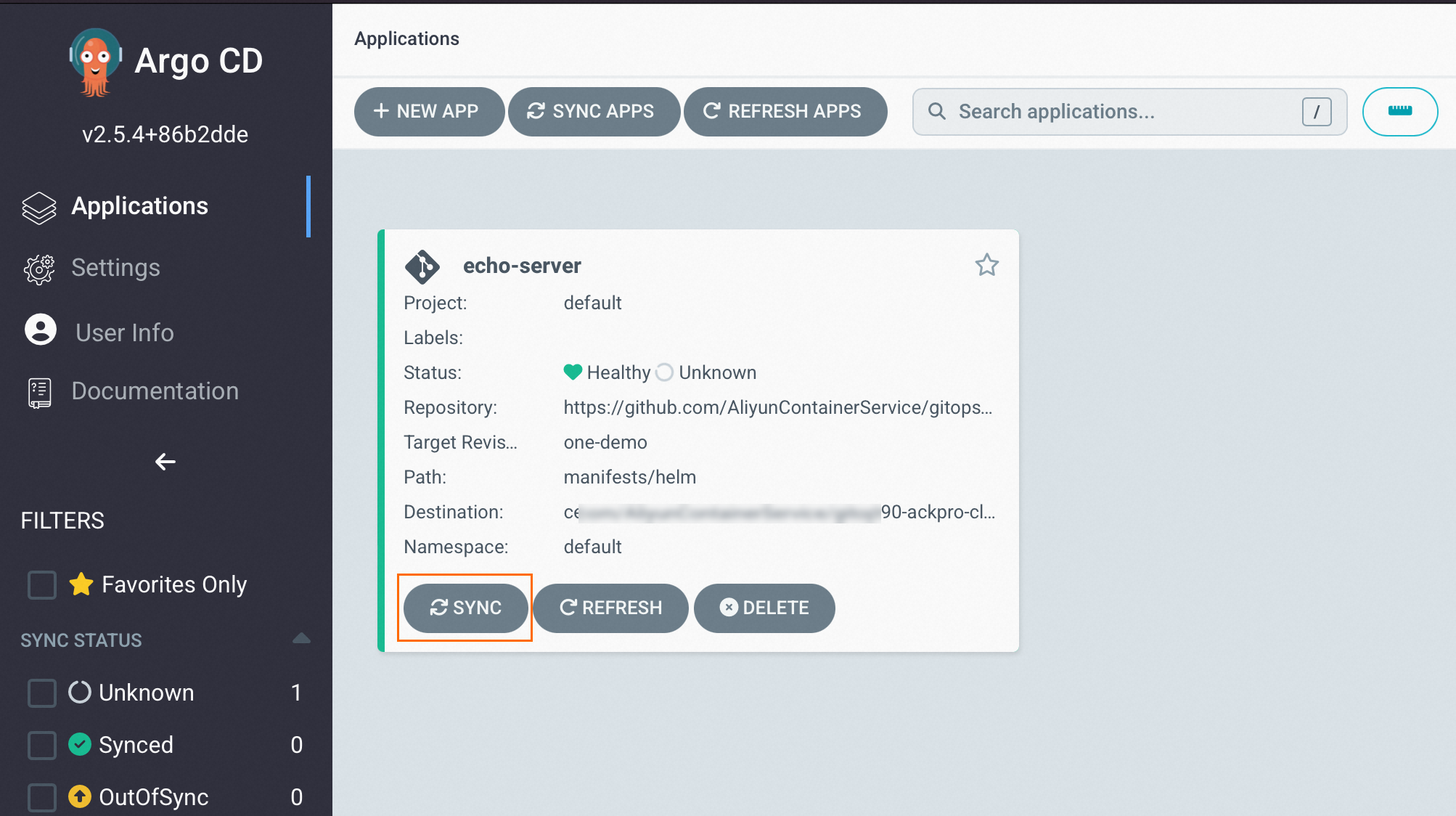
4. Sync the application to the cluster.
Click SYNC below the application to trigger deployment.
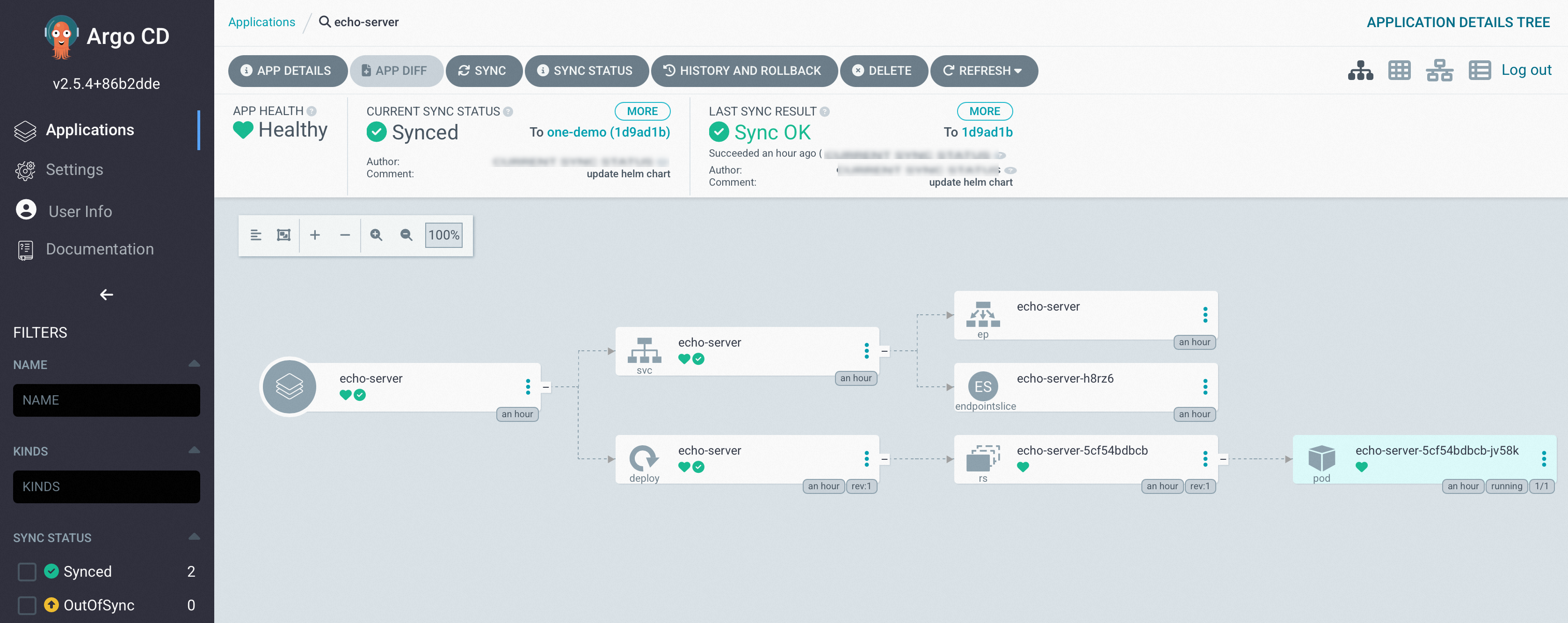
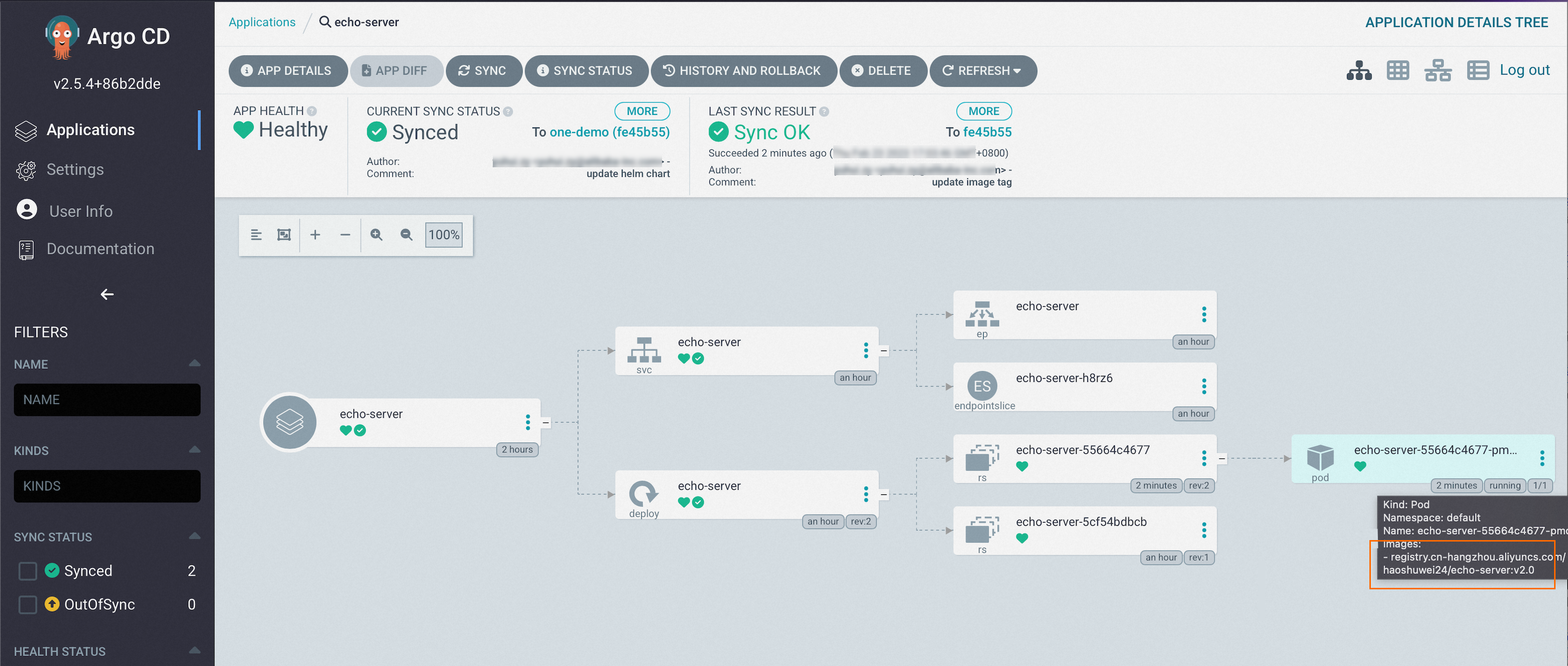
When Status shows Healthy and Synced, the application is running on the target cluster. Click the application name to see the topology and status of all Kubernetes resources.
Step 2: Verify the deployment
Use the Fleet instance kubeconfig to run these commands and confirm the application is running.
1. List clusters associated with the Fleet instance:
kubectl amc get managedclusterExpected output:
Name Alias HubAccepted
cd**** ackpro-cluster2 true
ce**** ackpro-cluster1 true // The cluster in which the application is deployed.The output lists all clusters registered with the Fleet instance. ce**** (ackpro-cluster1) is where the application was deployed.
2. Check resources in the target cluster:
kubectl amc get all -n default -m ce****The -m flag targets a specific managed cluster.
Expected output:
Run on ManagedCluster ce**** (ackpro-cluster1)
NAME READY STATUS RESTARTS AGE
pod/echo-server-5cf54bdbcb-jv58k 1/1 Running 0 59m
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
service/echo-server LoadBalancer 192.XX.XX.XX 39.XX.XX.XX 8080:31769/TCP 59m 21d
NAME READY UP-TO-DATE AVAILABLE AGE
deployment.apps/echo-server 1/1 1 1 59mThe pod shows 1/1 Running and the LoadBalancer Service has an external IP assigned. The application is ready to receive traffic.
3. Verify the application version:
curl http://39.XX.XX.XX:8080/versionExpected output:
"Hello Echo Server v1.0"The application is running at v1.0.
Step 3: Update the application
1. Push an image tag change to Git.
In the Git repository, change the pod image tag from v1.0 to v2.0.
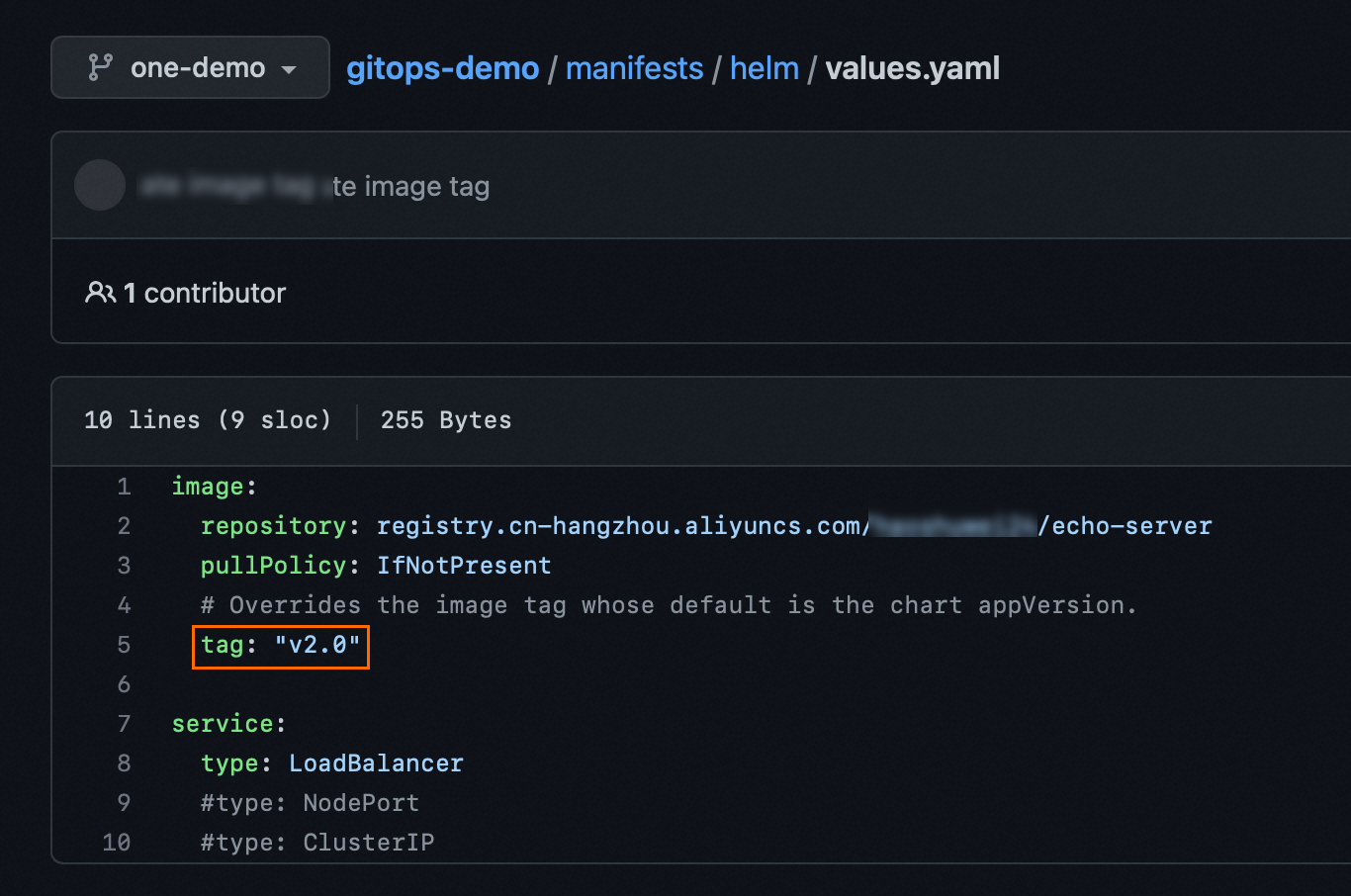
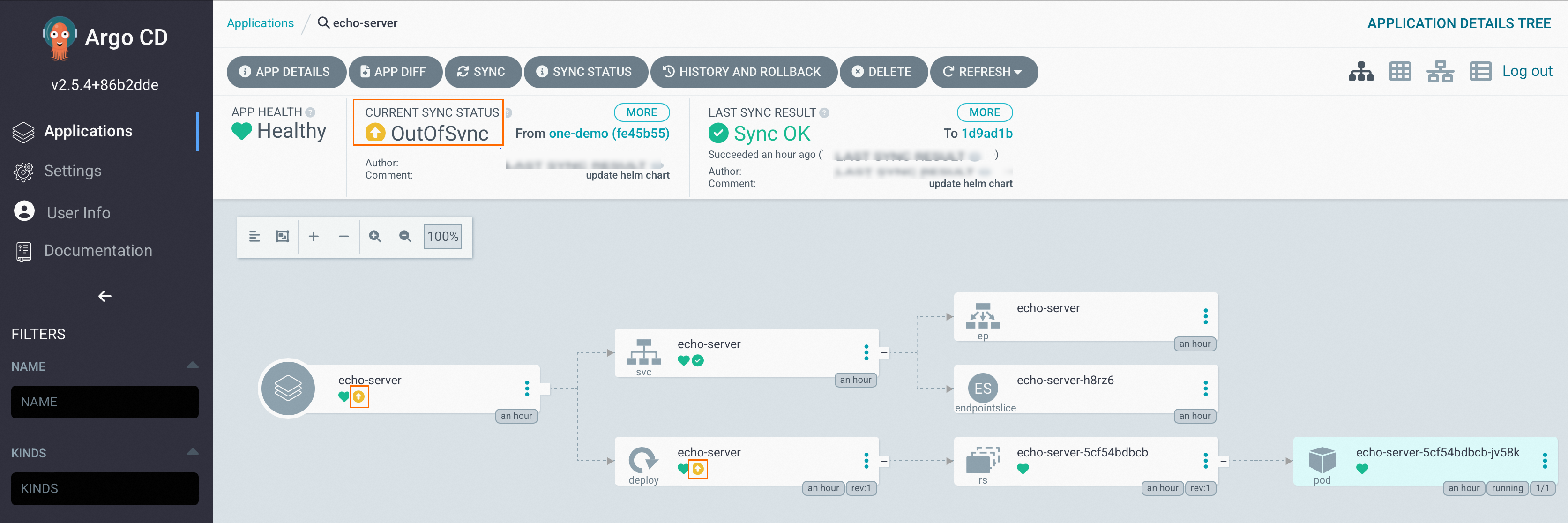
Due to the tag change in the Git repository, the ArgoCD application displays OutOfSync.
2. Review the diff.
Click the OutOfSync icon to view what changed.
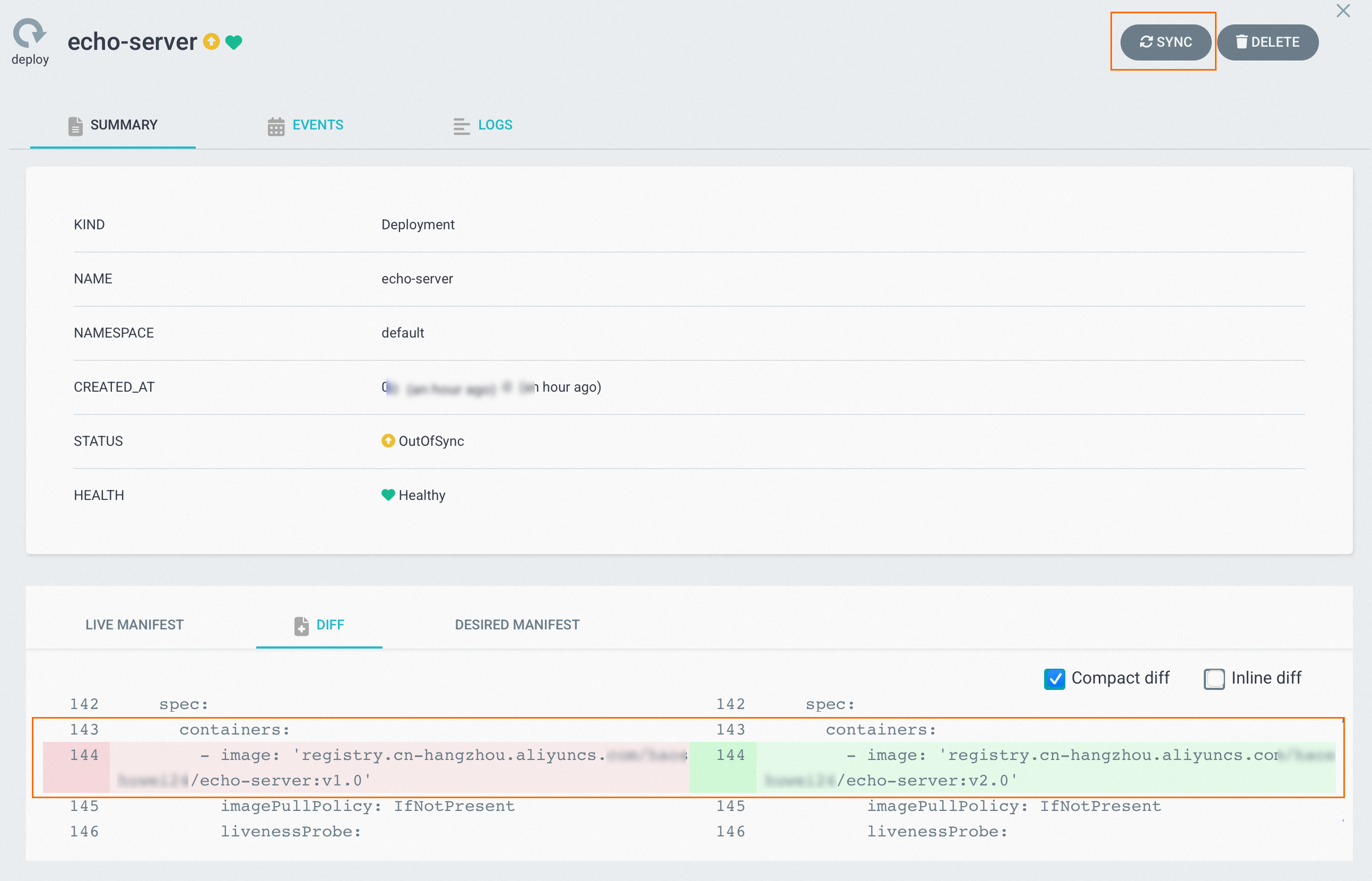
3. Sync the update.
Click SYNC. After the sync completes, the pod image tag is v2.0.
4. Verify the updated version:
curl http://39.XX.XX.XX:8080/versionExpected output:
"Hello Echo Server v2.0"Step 4: Roll back to a previous version
After the application is updated to v2.0, ArgoCD retains the original ReplicaSet for rollback.
1. Confirm both ReplicaSets exist in the cluster:
kubectl amc get replicaset -n default -m ce****Expected output:
Run on ManagedCluster ce**** (ackpro-cluster1)
NAME DESIRED CURRENT READY AGE
echo-server-55664c4677 1 1 1 26m // The version is v2.0.
echo-server-5cf54bdbcb 0 0 0 109m // The version is v1.0.2. Roll back to v1.0.
On the application page, click HISTORY AND ROLLBACK to see all historical versions.
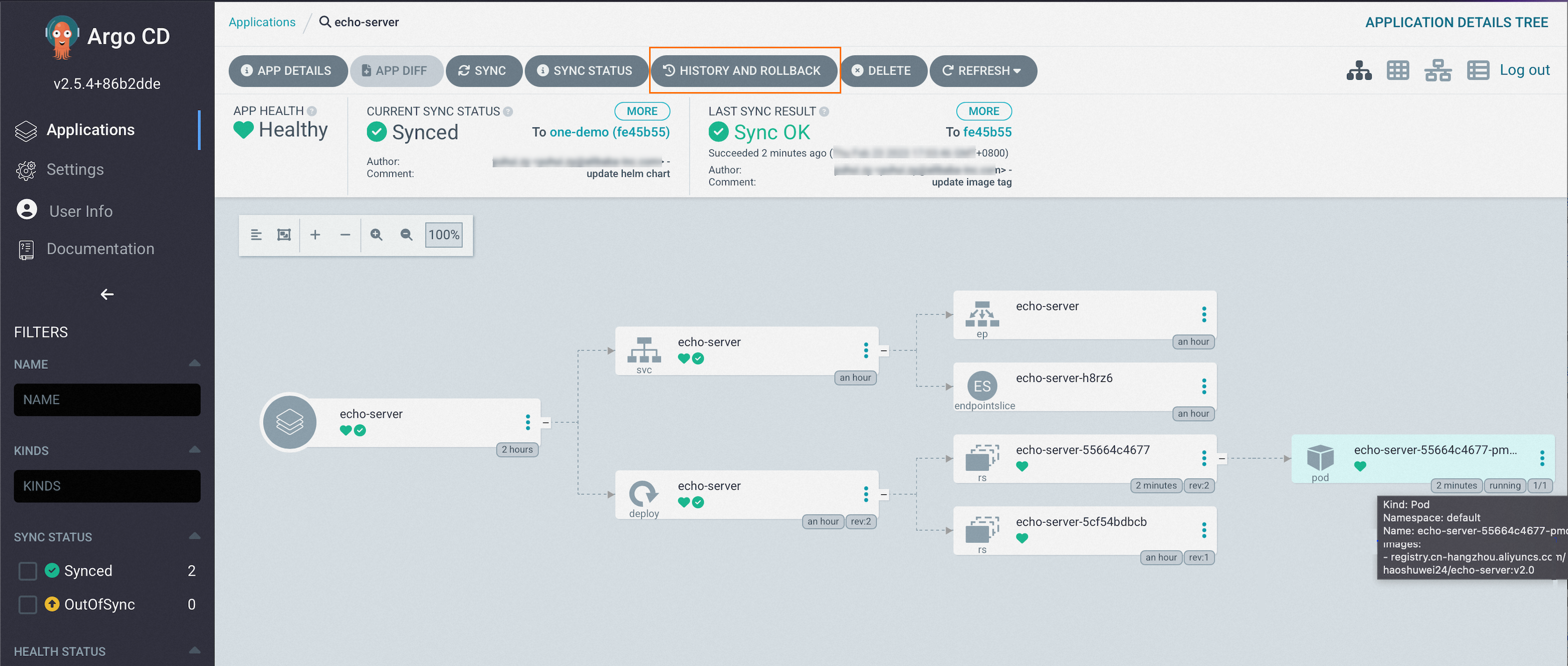
Select v1.0 and click Rollback.
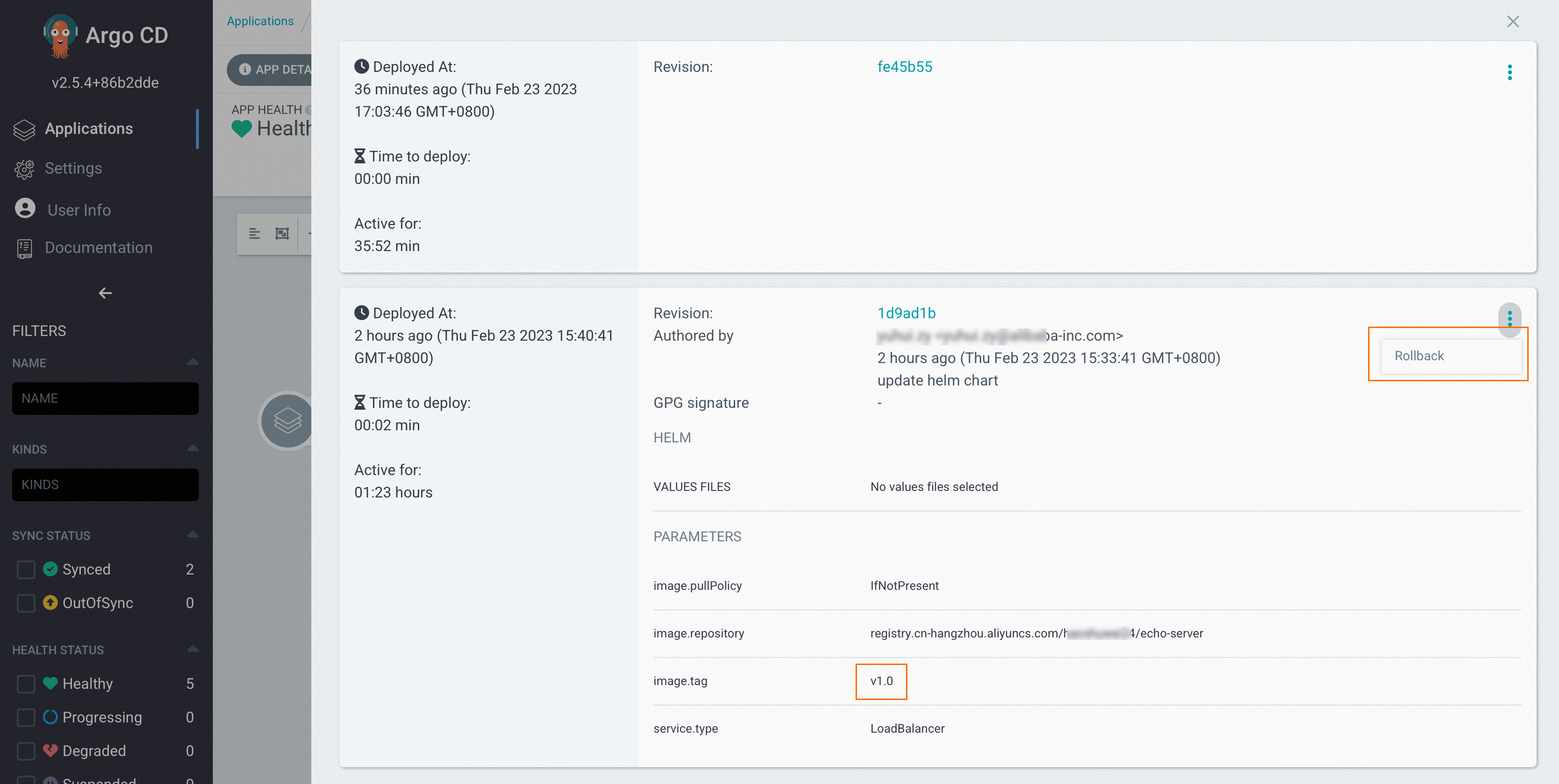
The pod image tag reverts to v1.0. Because the cluster state now differs from the Git repository (which still has v2.0), the application status changes to OutOfSync. Click SYNC to initiate a synchronization task.
ArgoCD automatically synchronizes information from the source Git repository.
Deploy an application using the ArgoCD CLI
Step 1: Log on to the ArgoCD server
1. Get the ArgoCD server load balancer IP:
kubectl get svc -nargocd argocd-server -ojsonpath='{.status.loadBalancer.ingress[0].ip}'2. Get the admin password:
kubectl -nargocd get secret argocd-initial-admin-secret -ojsonpath='{.data.password}' |base64 -d3. Log on:
argocd login <argocd server lb ip>
Username: admin
Password:
'admin:login' logged in successfully
Context '<argocd server lb ip>' updatedStep 2: Add a Git repository
argocd repo add https://github.com/AliyunContainerService/gitops-demo.git --name echo-serverExpected output:
Repository 'https://github.com/AliyunContainerService/gitops-demo.git' addedVerify the repository is connected:
argocd repo listExpected output:
TYPE NAME REPO INSECURE OCI LFS CREDS STATUS MESSAGE PROJECT
git https://github.com/AliyunContainerService/gitops-demo.git false false false false Successful defaultStep 3: Check available clusters
argocd cluster listExpected output:
SERVER NAME VERSION STATUS MESSAGE PROJECT
https://10.XX.XX.XX:XX ce****-ackpro-cluster1 Unknown Cluster has no applications and is not being monitored.
https://10.XX.XX.XX:XX cd****-ackpro-cluster2 Unknown Cluster has no applications and is not being monitored.
https://kubernetes.default.svc in-cluster Unknown Cluster has no applications and is not being monitored.ACK One automatically synchronizes information about newly associated clusters to ArgoCD, so any cluster added to the Fleet instance appears here.
Step 4: Create and deploy the application
1. Create the application:
argocd app create echo-server --repo https://github.com/AliyunContainerService/gitops-demo.git --path manifests/helm --revision one-demo --dest-namespace default --dest-server https://10.0.XX.XX:6443Expected output:
application 'echo-server' created2. Sync the application to pull the configuration from Git and deploy it to the target cluster:
argocd app sync echo-serverMore operations
-
Deploy to multiple clusters: Use an ArgoCD ApplicationSet to deploy the same application to multiple clusters simultaneously. See Use an ApplicationSet to create multiple applications.
-
Deploy OCI Helm charts: Deploy a Container Registry Enterprise Edition OCI Helm chart using ACK One GitOps. See Use ACK One GitOps to deploy a Container Registry Enterprise Edition OCI Helm chart.