Use labels to enforce fine-grained access control
When you manage multiple teams or projects in one Alibaba Cloud account, maintaining separate Resource Access Management (RAM) policies for each cluster becomes difficult to scale. Tag-based authorization solves this by letting you attach tags to ACK clusters and reference those tags in RAM permission policies—so the same policy automatically covers any new cluster with the right tag, without manual updates.

How it works
Tag-based authorization uses the Condition element in a RAM permission policy to match tags on API requests or cluster resources:
| Condition key | Behavior | When authorization fails |
|---|---|---|
acs:RequestTag |
Requires that API requests include specific tags. | Requests that do not include tag parameters will fail authorization. |
acs:ResourceTag |
Restricts access to resources that have specific tags. | Requests that do not include a resource ID parameter will fail authorization. |
Only the resource types listed in Resource types that support tags support tag-based authorization. For all other actions, tag conditions have no effect—create a separate custom permission policy scoped to Account Level with no tag conditions.
Prerequisites
Before you begin, ensure that you have:
-
An Alibaba Cloud account with administrative permissions, or a RAM user with the
AdministratorAccesspolicy attached -
At least one ACK cluster to apply tags to
A RAM user or RAM role with account-level permissions can perform operations on all resources in the account. Follow the principle of least privilege when granting permissions.
Create and attach a tag-based permission policy
Step 1: Create a RAM user
Create a RAM user for the person or service that needs restricted cluster access.
Step 2: Create a custom permission policy with tag conditions
-
Log on to the RAM console with your Alibaba Cloud account.
-
Create a custom permission policy. For instructions, see Create custom policies.
-
In the policy, use the
Conditionelement to set tag conditions on your cloud resources. Refer to the Examples section for policy templates, and Actions that do not support tag-based authorization for actions that require separate policies.An Alibaba Cloud account has full administrative permissions over all resources in the account. Alternatively, you can create a RAM user and grant the
AdministratorAccesspermission to designate it as an account administrator. For more information, see Create a RAM user as an account administrator.
Step 3: Attach the policy to the RAM user
Attach the custom permission policy to the RAM user. For instructions, see Grant permissions to a RAM user.
Before granting permissions to an existing RAM user, review their current permission policies to avoid duplicates or conflicts.
Examples
Use these policy templates as a starting point. Adjust them according to the principle of least privilege.
Allow cluster creation only with a specific tag
This policy allows creating clusters only when the test:foo tag is included in the creation request.
{
"Version": "1",
"Statement": [{
"Effect": "Allow",
"Action": "cs:CreateCluster",
"Resource": "*",
"Condition": {
"StringEquals": {
"acs:RequestTag/test": "foo"
}
}
}]
}To verify: In the ACK console, create a cluster. In the advanced options section, add the test:foo tag. The cluster is created successfully. Attempt to create another cluster without the tag—the request fails with an authorization error.
Show only tagged clusters in the cluster list
This policy allows a RAM user to list and view only clusters that have the test:foo tag.
{
"Version": "1",
"Statement": [{
"Effect": "Allow",
"Action": [
"cs:DescribeClustersV1",
"cs:GetClusters"
],
"Resource": "*",
"Condition": {
"StringEquals": {
"acs:ResourceTag/test": "foo"
}
}
}]
}To verify:
-
Log on to the ACK console as the RAM user. In the left navigation pane, click Clusters.
-
If no clusters have the
test:footag, the list is empty. -
Add the
test:footag to a cluster. Refresh the page—the cluster appears in the list.
Prevent users from modifying tags
This policy denies all tag modification actions, ensuring that RAM users cannot remove or alter the tags that control their access.
{
"Version": "1",
"Statement": [{
"Effect": "Deny",
"Action": [
"cs:UntagResources",
"cs:ListTagResources",
"cs:TagResources",
"cs:ModifyClusterTags"
],
"Resource": "*"
}]
}To verify: As the RAM user, attempt to modify a tag on any cluster. The operation fails with an authorization error.
References
Resource types that support tags
Tag-based authorization in ACK applies only to the following resource types.
| Service name | Service code | Resource type |
|---|---|---|
| ACK | cs | cluster |
Actions that do not support tag-based authorization
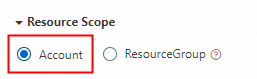
The following actions do not support tag-based authorization. For these actions, tag conditions have no effect. Create a separate custom permission policy, set the resource scope to Account Level, and do not specify tag conditions.
A RAM user or RAM role with account-level permissions can perform operations on all resources in the account. Make sure the permissions you grant follow the principle of least privilege.
The following two templates cover these actions. Modify them as needed.
The Action list includes all read-only actions that do not support tag-based authorization:
{
"Version": "1",
"Statement": [
{
"Effect": "Allow",
"Action": [
"cs:CheckServiceRole",
"cs:CheckUserClustersActivity",
"cs:DescribeAddon",
"cs:DescribeAddons",
"cs:DescribeEvents",
"cs:DescribeEventsForRegion",
"cs:DescribeKubeConfigManagementTaskList",
"cs:DescribeKubernetesVersionMetadata",
"cs:DescribePatternTypes",
"cs:DescribePolicies",
"cs:DescribePolicyDetails",
"cs:DescribeTaskInfo",
"cs:DescribeTemplateAttribute",
"cs:DescribeTemplates",
"cs:DescribeTasks",
"cs:DescribeUserInstances",
"cs:DescribeUserPermission",
"cs:DescribeUserQuota",
"cs:ListAddons",
"cs:ListHaveKubeconfigDeletedAccounts",
"cs:ListKubeConfigRecycle",
"cs:ListOperationPlans",
"cs:ListUserKubeConfigStates",
"cs:QueryAlertContact",
"cs:QueryAlertContactGroup"
],
"Resource": "*"
}
]
}The Action list includes all actions (read and write) that do not support tag-based authorization:
{
"Version": "1",
"Statement": [
{
"Effect": "Allow",
"Action": [
"cs:AddOrUpdateAlertContact",
"cs:AddOrUpdateAlertContactGroup",
"cs:CancelOperationPlan",
"cs:CancelTask",
"cs:CheckServiceRole",
"cs:CheckUserClustersActivity",
"cs:CleanUserPermissions",
"cs:CreateKubernetesTrigger",
"cs:CreateSessionMessage",
"cs:CreateTemplate",
"cs:DeleteAlertContact",
"cs:DeleteAlertContactGroup",
"cs:DeleteKubeConfigRecycleItem",
"cs:DeleteTemplate",
"cs:DeleteTriggerHook",
"cs:DescribeAddon",
"cs:DescribeAddons",
"cs:DescribeEvents",
"cs:DescribeEventsForRegion",
"cs:DescribeKubeConfigManagementTaskList",
"cs:DescribeKubernetesVersionMetadata",
"cs:DescribePatternTypes",
"cs:DescribePolicies",
"cs:DescribePolicyDetails",
"cs:DescribeTaskInfo",
"cs:DescribeTemplateAttribute",
"cs:DescribeTemplates",
"cs:DescribeTasks",
"cs:DescribeUserInstances",
"cs:DescribeUserPermission",
"cs:DescribeUserQuota",
"cs:ListAddons",
"cs:ListHaveKubeconfigDeletedAccounts",
"cs:ListKubeConfigRecycle",
"cs:ListOperationPlans",
"cs:ListUserKubeConfigStates",
"cs:OpenAckService",
"cs:PauseTask",
"cs:QueryAlertContact",
"cs:QueryAlertContactGroup",
"cs:RestoreKubeConfigRecycleItem",
"cs:RestoreMultiKubeConfigRecycleItems",
"cs:ResumeTask",
"cs:UpdateMessageFeedback",
"cs:UpdateTemplate",
"cs:UpdateUserPermissions"
],
"Resource": "*"
}
]
}Full list of actions that do not support tag-based authorization
| Action | Description |
|---|---|
| cs:OpenAckService | Enable ACK |
| cs:ListOperationPlans | Query the automatic operations and maintenance (O&M) schedules of a cluster |
| cs:CancelOperationPlan | Cancel a pending automatic O&M plan |
| cs:DescribeTaskInfo | Query the details of a task |
| cs:PauseTask | Pause a task |
| cs:CancelTask | Cancel a task |
| cs:ResumeTask | Resume a task |
| cs:CreateKubernetesTrigger | Create an application trigger |
| cs:DeleteTriggerHook | Delete a trigger |
| cs:CreateTemplate | Create an orchestration template |
| cs:DeleteTemplate | Delete an orchestration template |
| cs:UpdateTemplate | Update an orchestration template |
| cs:DescribeTemplates | Query all orchestration templates |
| cs:DescribeTemplateAttribute | Query the details of an orchestration template |
| cs:ListUserKubeConfigStates | Query the kubeconfig status list of all clusters for a specific user |
| cs:ListAddons | Query the list of available add-ons |
| cs:DescribeAddon | Query information about a specific add-on |
| cs:DescribeAddons | Query information about all add-ons |
| cs:DescribeEvents | Query event details |
| cs:DescribeEventsForRegion | Query events in a specific region |
| cs:DescribeKubernetesVersionMetadata | Query the details of a Kubernetes version |
| cs:CheckServiceRole | Check whether a specific service role is assigned |
| cs:DescribePatternTypes | Query instance types |
| cs:CheckUserClustersActivity | Check the active status of a user in a specific cluster |
| cs:CreateSessionMessage | Create an ACK AI Assistant session |
| cs:UpdateMessageFeedback | Update ACK AI Assistant message feedback |
| cs:DescribeKubeConfigManagementTaskList | List the tasks related to kubeconfig files |
| cs:ListHaveKubeconfigDeletedAccounts | Query users whose RAM user or RAM role accounts have been deleted but whose kubeconfig files remain active |
| cs:ListKubeConfigRecycle | List the kubeconfig files in the recycle bin within the current Alibaba Cloud account |
| cs:RestoreKubeConfigRecycleItem | Restore a deleted kubeconfig file from the recycle bin |
| cs:RestoreMultiKubeConfigRecycleItems | Batch restore deleted kubeconfig files from the recycle bin |
| cs:DeleteKubeConfigRecycleItem | Permanently delete a kubeconfig file from the recycle bin |
| cs:DescribePolicies | Query the policy list |
| cs:DescribePolicyDetails | Query the details of a specific policy |
| cs:DescribeUserInstances | Get the node list required to add an existing node |
| cs:DescribeUserPermission | Query the permissions of a RAM user or RAM role |
| cs:UpdateUserPermissions | Update the Role-Based Access Control (RBAC) permissions of a specific RAM user or RAM role |
| cs:CleanUserPermissions | Clear the certificate of a specific user and the related RBAC permissions |
| cs:QueryAlertContact | Query an alert contact |
| cs:AddOrUpdateAlertContact | Add or update an alert contact |
| cs:DeleteAlertContact | Delete an alert contact |
| cs:QueryAlertContactGroup | Query alert contact groups |
| cs:AddOrUpdateAlertContactGroup | Add or update an alert contact group |
| cs:DeleteAlertContactGroup | Delete an alert contact group |
| cs:DescribeUserQuota | Query quota information |
| cs:DescribeTasks | Query the task list |