ACK virtual nodes support service discovery through Alibaba Cloud DNS PrivateZone. When you add an annotation to a Service, the virtual node controller automatically syncs its DNS records to PrivateZone — allowing pods and other clients in your Virtual Private Cloud (VPC) to reach Elastic Container Instance (ECI)-backed Services by domain name.
Supported Service types: Headless, ClusterIP, and internal LoadBalancer.
Using PrivateZone incurs fees. For pricing details, see Billing.
How it works
PrivateZone is a private DNS resolution service for VPC environments. It provides domain name resolution and internal domain name acceleration services for clients such as ECS instances and containers running inside a VPC.
When you enable PrivateZone on a virtual node cluster, the virtual node controller creates a private DNS zone named svc.cluster.local.<clusterID> and syncs DNS records for annotated Services into that zone. The DNS record format is <service-name>.<namespace>.
| Service type | DNS records synced | Resolves to |
|---|---|---|
| Headless | One record per backend pod | Pod IP addresses |
| ClusterIP | One record | Cluster IP (virtual IP for intra-cluster communication) |
| Internal LoadBalancer | One record | Cluster IP (virtual IP for intra-cluster communication) |
After sync, Services are accessible by domain name inside the VPC:
| Access scope | Domain name format | Applies to |
|---|---|---|
| Within the cluster, same namespace | <service-name> | All Service types |
| Within the cluster, different namespace | <service-name>.<namespace> | All Service types |
| Outside the cluster (FQDN) | <service-name>.<namespace>.svc.cluster.local.<clusterID> | Headless Services only |
Prerequisites
Before you begin, make sure you have:
The ack-virtual-node component installed. See Deploy the ack-virtual-node component.
CoreDNS not installed in the cluster. This feature cannot be used with CoreDNS. Ensure that the CoreDNS component is not installed in the cluster.
PrivateZone activated in the Alibaba Cloud DNS console.
Enable PrivateZone
Log on to the ACK console and click Clusters in the left navigation pane.
Click the name of your cluster. In the left navigation pane, choose Configurations > ConfigMaps.
Set Namespace to kube-system, locate eci-profile, and click Edit.
Set
enablePrivateZonetotrue, then click OK.Verify that the zone was created:
In the Alibaba Cloud DNS console, click Private Zone in the left navigation pane.
Under the Authoritative Zone tab, go to User Defined Zones and confirm that a zone named `svc.cluster.local.<cluster ID>` appears.
Sync DNS records of Services to PrivateZone
DNS records are not synced to PrivateZone by default. To enable sync for a Service, add the following annotation:
service.beta.kubernetes.io/alibaba-cloud-private-zone-enable: "true"The following example creates one Deployment and three Services — one of each supported type — all with the annotation.
Save the following content as
test-pz.yaml:apiVersion: v1 kind: Service metadata: name: nginx-headless-service annotations: service.beta.kubernetes.io/alibaba-cloud-private-zone-enable: "true" spec: ports: - port: 80 protocol: TCP selector: app: nginx clusterIP: None --- apiVersion: v1 kind: Service metadata: name: nginx-clusterip-service annotations: service.beta.kubernetes.io/alibaba-cloud-private-zone-enable: "true" spec: ports: - port: 80 protocol: TCP selector: app: nginx type: ClusterIP --- apiVersion: v1 kind: Service metadata: name: nginx-intranet-service annotations: service.beta.kubernetes.io/alibaba-cloud-loadbalancer-address-type: "intranet" service.beta.kubernetes.io/alibaba-cloud-private-zone-enable: "true" spec: ports: - port: 80 protocol: TCP selector: app: nginx type: LoadBalancer --- apiVersion: apps/v1 kind: Deployment metadata: name: nginx-deployment labels: app: nginx spec: replicas: 3 selector: matchLabels: app: nginx template: metadata: labels: app: nginx alibabacloud.com/eci: "true" # Schedule pods to ECI spec: containers: - name: nginx image: anolis-registry.cn-zhangjiakou.cr.aliyuncs.com/openanolis/nginx:1.14.1-8.6 ports: - containerPort: 80Apply the manifest:
kubectl create -f test-pz.yamlVerify that the DNS records were synced:
In the Alibaba Cloud DNS console, click Private Zone.
Under User Defined Zones on the Authoritative Zone tab, find the zone named `svc.cluster.local.<cluster ID>` and click Settings.
On the Settings tab, confirm that three DNS records appear — one for each Service — in the format
<service-name>.default: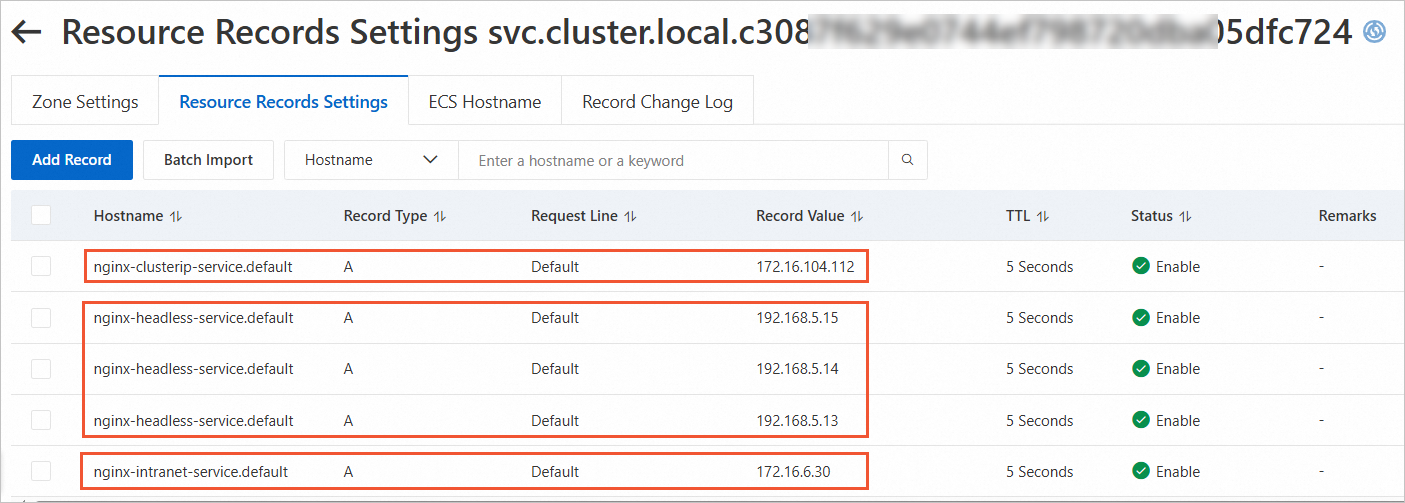
nginx-headless-service.default— multiple A records, one per pod IPnginx-clusterip-service.default— one A record pointing to the Cluster IPnginx-intranet-service.default— one A record pointing to the Cluster IP