ACK uses two independent authorization layers: Resource Access Management (RAM) controls which Alibaba Cloud API actions a user can call, and role-based access control (RBAC) controls what Kubernetes resources that user can access inside a cluster. Most authorization errors result from a gap in one of these two layers. The questions below are organized by error type to help you pinpoint and resolve the issue quickly.
Authorization failures
ForbiddenQueryClusterNamespace: Forbidden query namespaces
The RAM user or RAM role lacks RBAC permissions on the cluster's namespaces. Go to Authorizations in the ACK console and assign an RBAC role to the RAM user or RAM role. For more information, see Grant RBAC permissions to RAM users or RAM roles.
APISERVER_403
The RAM user or RAM role lacks the required RBAC permissions on the cluster. Go to Authorizations in the ACK console and grant the required RBAC role. For more information, see Grant RBAC permissions to RAM users or RAM roles.
The current RAM user does not have management permissions
This error means the RAM user or RAM role cannot grant RBAC permissions to others. By default, only the Alibaba Cloud account owner or a RAM user with explicit delegation can do this.
To delegate RBAC management to a RAM user or RAM role (referred to as User A below), grant both of the following:
RBAC administrator permissions: In the ACK console under Authorizations, assign the predefined administrator role or cluster-admin role to User A for the target clusters and namespaces.
RAM permissions: In the RAM console, attach a custom policy to User A. The policy must allow User A to query other RAM users and roles in the same account, attach specified RAM policies, query RBAC permissions, and perform RBAC authorization. Use the following policy template:
{
"Statement": [{
"Action": [
"ram:Get*",
"ram:List*",
"cs:GetUserPermissions",
"cs:GetSubUsers",
"cs:GrantPermission"
],
"Resource": "*",
"Effect": "Allow"
},
{
"Action": [
"ram:AttachPolicyToUser",
"ram:AttachPolicyToRole"
],
"Effect": "Allow",
"Resource": [
"acs:ram:*:*:policy/xxxxxx",
"acs:*:*:*:user/*"
]
}
],
"Version": "1"
}Replacexxxxxxwith the name of the RAM policy that User A is allowed to attach to others. To allow User A to attach any RAM policy, replacexxxxxxwith*.
For more information, see Create a custom RAM policy and Grant RBAC permissions to RAM users or RAM roles.
How do I tell whether an error is caused by RAM or RBAC?
Look at the error message text:
RAM policy errors contain RAM policy Forbidden or STSToken policy Forbidden:
RAM policy Forbidden for action cs:DescribeEvents
STSToken policy Forbidden for action cs:DescribeClusterNodesThis means the RAM policy attached to the user or role does not include the listed action. Add the missing action to the RAM policy. For more information, see Create a custom RAM policy.
RBAC permission errors contain APISERVER_403, User "xxx" cannot xx resource, or ForbiddenQueryClusterNamespace:
events is forbidden: User "<uid>" cannot list resource "events" in API group "" at the cluster scope
ForbiddenQueryClusterNamespace, Forbidden query namespacesThis means the RAM user <uid> lacks the required Kubernetes RBAC permissions. Grant the required RBAC permissions. For more information, see Grant RBAC permissions to RAM users or RAM roles.
I attached AdministratorAccess or AliyunCSFullAccess to a RAM user, but it still cannot access clusters
ACK requires both RAM authorization and RBAC authorization. Attaching AdministratorAccess or AliyunCSFullAccess in the RAM console only covers the RAM layer. Go to Authorizations in the ACK console and assign RBAC roles to the RAM user as well. For more information, see Authorization overview and Grant RBAC permissions to RAM users or RAM roles.
ForbiddenCheckControlPlaneLog
The RAM user or RAM role is not assigned the predefined administrator or O&M engineer RBAC role. Go to Authorizations in the ACK console and assign the administrator or O&M engineer role. For more information, see Grant RBAC permissions to RAM users or RAM roles.
ForbiddenHelmUsage
The RAM user or RAM role is not assigned the predefined administrator RBAC role. Go to Authorizations in the ACK console and assign the administrator role. For more information, see Grant RBAC permissions to RAM users or RAM roles.
ForbiddenRotateCert
The RAM user or RAM role is not assigned the predefined administrator RBAC role. Go to Authorizations in the ACK console and assign the administrator role. For more information, see Grant RBAC permissions to RAM users or RAM roles.
ForbiddenAttachInstance
The RAM user or RAM role is not assigned the predefined administrator or O&M engineer RBAC role. Go to Authorizations in the ACK console and assign the administrator or O&M engineer role. For more information, see Grant RBAC permissions to RAM users or RAM roles.
ForbiddenUpdateKMSState
The RAM user or RAM role is not assigned the predefined administrator or O&M engineer RBAC role. Go to Authorizations in the ACK console and assign the administrator or O&M engineer role. For more information, see Grant RBAC permissions to RAM users or RAM roles.
Forbidden get trigger
The RAM user or RAM role is not assigned the predefined administrator, O&M engineer, or developer RBAC role. Go to Authorizations in the ACK console and assign one of those roles. For more information, see Grant RBAC permissions to RAM users or RAM roles.
RBAC authorization
Can I grant permissions on specific applications rather than all resources?
Yes. Create a custom ClusterRole with a rule that uses the resourceNames field to scope permissions to specific application names, then bind it to the RAM user or RAM role.
-
Log on to the ACK console.
-
In the left-side navigation pane, click Authorizations.
-
On the RAM Users tab, find the target RAM user and click Modify Permissions.
The account you use to make this change must have at least read-only permissions on the cluster and must be assigned the
cluster-adminor administrator role. For more information, see Create a custom RAM policy. -
Click Add Permissions, select the cluster, namespace, and authorization type, then click Submit. The following table describes the permissions that each predefined RBAC role has on clusters and namespaces. For subsequent steps, see Grant RBAC permissions to RAM users or RAM roles.
- Permissions can also be granted across all clusters for a RAM user. - A RAM user or RAM role can hold one predefined RBAC role and one or more custom RBAC roles for a given cluster or namespace.
Role RBAC permissions on cluster resources Administrator Read/write access to resources in all namespaces, and to nodes, volumes, namespaces, and quotas. O&M engineer Read/write access to Kubernetes resources visible in the console across all namespaces; read-only access to nodes, volumes, namespaces, and quotas. Developer Read/write access to resources visible in the console within specified namespaces only. Restricted user Read-only access to resources visible in the console within specified namespaces only. Custom role Permissions are determined by the ClusterRole you select. Review the ClusterRole's rules before assigning it. For more information, see Create a custom RAM policy. 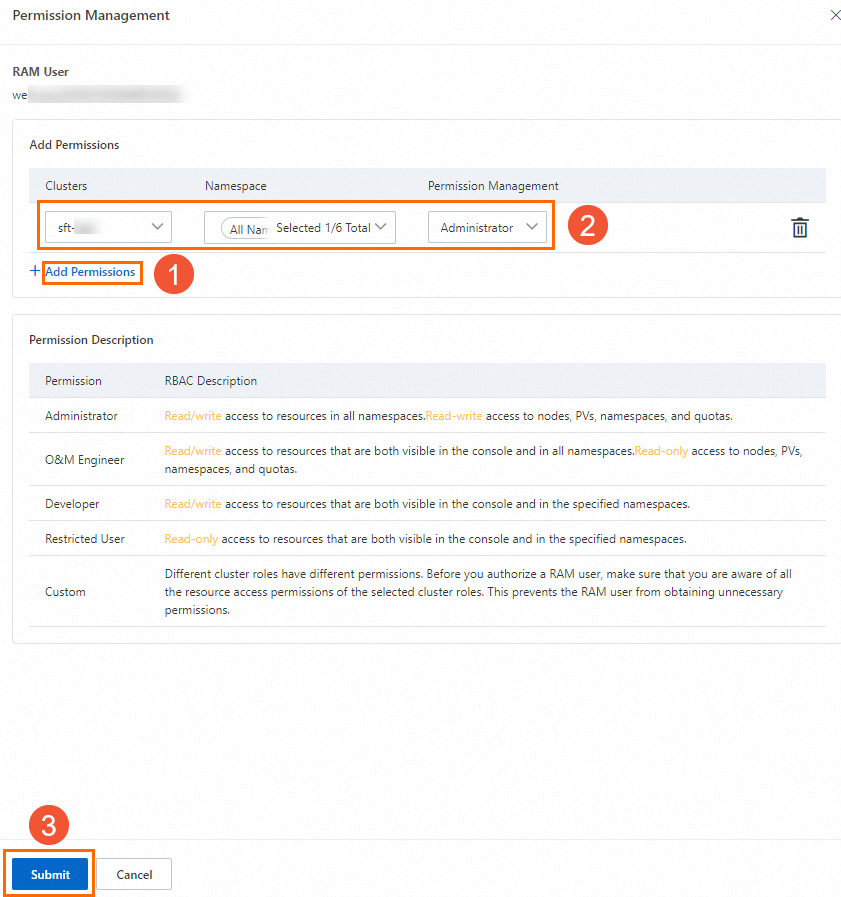
A RAM user assigned the cs:admin role cannot create CustomResourceDefinition (CRD) objects
This affects clusters created before May 2019. The default cs:admin ClusterRole in those clusters does not include permissions for certain Kubernetes resources, including CRD creation. Two options are available:
-
Assign the
cluster-adminrole to the RAM user or RAM role. -
Delete the existing
cs:adminClusterRole and recreate it with the following definition:
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
name: cs:admin
rules:
- apiGroups:
- '*'
resources:
- '*'
verbs:
- '*'
- nonResourceURLs:
- '*'
verbs:
- '*'How do I use a RAM user or RAM role to assign RBAC roles to other users?
See The current RAM user does not have management permissions for the required RAM permissions and RBAC role assignments.
How do I find the RAM user or RAM role associated with a ClusterRoleBinding or RoleBinding?
Check the subjects field in the ClusterRoleBinding or RoleBinding configuration. If kind is User and name consists entirely of digits (or digits and hyphens), that value is the RAM user ID or RAM role ID.
The following example shows a ClusterRoleBinding for RAM user 1*` and a RoleBinding for RAM user `2*:
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
name: 1***-cluster-admin-clusterrolebinding
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: cluster-admin
subjects:
- apiGroup: rbac.authorization.k8s.io
kind: User
name: 1***-1673419473
---
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
name: 2***-default-rolebinding
namespace: default
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: 'cs:ns:dev'
subjects:
- apiGroup: rbac.authorization.k8s.io
kind: User
name: '2***'Why can't I modify or revoke the RBAC permissions of a cluster creator?
ACK does not approve requests to modify or revoke the RBAC permissions of a cluster creator, to ensure the creator can always manage their own cluster.
To revoke a cluster creator's permissions, delete the ClusterRoleBinding directly:
-
Find the ClusterRoleBinding for the creator. Replace
<uid>with the Alibaba Cloud account UID.kubectl get clusterrolebinding | grep <uid> -
Back up and delete the ClusterRoleBinding. Replace
<name>with the name returned in the previous step.kubectl get clusterrolebinding <name> -o yaml > <name>.yaml kubectl delete clusterrolebinding <name>
What permissions are required to use the terminal feature?
Assign the predefined administrator, O&M engineer, or developer RBAC role to the RAM user or RAM role. In addition, grant the RAM permission to call cs:DescribeClusterUserKubeconfig. For more information, see Grant RBAC permissions to RAM users or RAM roles and Create a custom RAM policy.
How do I grant RBAC permissions to a user who logs on via CloudSSO?
CloudSSO users log on as RAM roles, not as individual RAM users. To grant RBAC permissions, grant them to the RAM role, not to the individual user account.
For example, if the user logs on as AliyunReservedSSO-Policy-foo-bar-admin/foo.bar, grant the RBAC permissions to the RAM role AliyunReservedSSO-Policy-foo-bar-admin. For more information, see Grant RBAC permissions to RAM users or RAM roles.
RAM authorization
A RAM user with read-only permissions on all clusters can no longer see some clusters
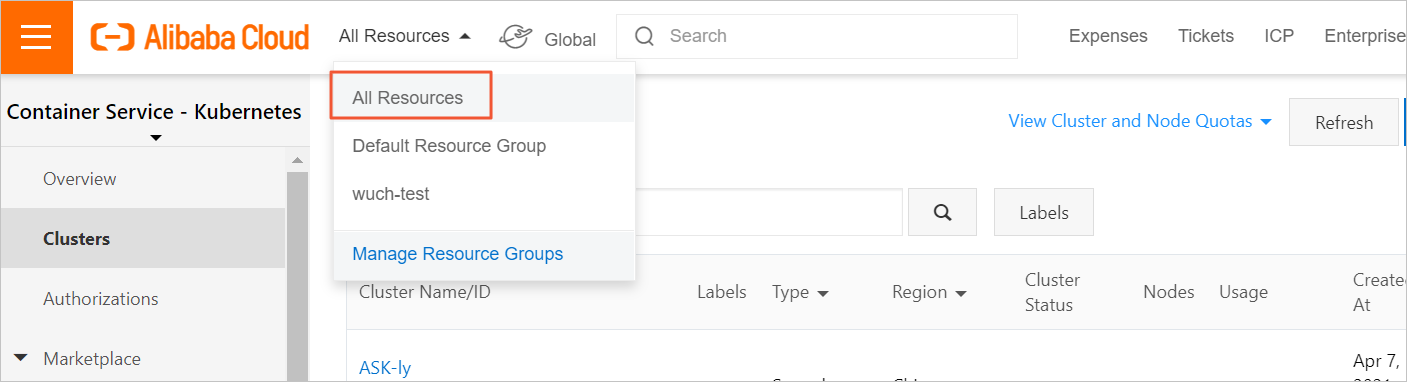
This is usually a console filter issue, not a permission change. Check two things:
-
Log on to the ACK console using the correct RAM user or RAM role.
-
In the top navigation bar, set the resource scope to All Resources > All Resources.
-
Hover over the avatar in the upper-right corner to confirm you are logged on with the correct identity.
If a resource group filter is active, clusters outside that group are hidden even if permissions are correct.
How do I grant a RAM user or RAM role permission to create clusters?
Two steps are required:
-
Assign system roles to ACK using your Alibaba Cloud account. System roles only need to be assigned once. If you are unsure whether they are already assigned, log on with your Alibaba Cloud account, click Cloud Resource Access Authorization, and complete the authorization. For more information about the default system roles, see ACK default roles.
-
Attach a custom RAM policy to the RAM user or RAM role that includes the
cs:CreateClusterpermission:- Cluster creation associates cloud resources such as virtual private clouds (VPCs) with the cluster. Make sure the RAM user or RAM role has the required permissions to access those resources. - Grant the RAM user the
AliyunVPCReadOnlyAccesspolicy to allow listing VPCs. - For other resource types, check the documentation for the relevant cloud services. For more information, see RAM authorization.{ "Statement": [{ "Action": [ "cs:CreateCluster" ], "Effect": "Allow", "Resource": [ "*" ] }], "Version": "1" }For more information, see Create a custom RAM policy.
What error codes mean the Alibaba Cloud account is missing required ACK service roles?
The following error codes indicate that ACK service roles have not been assigned to the current account. Log on with an Alibaba Cloud account or a RAM user attached with AdministratorAccess, then click the link in the error message to complete the role assignment.
| Error code | Sample error message |
|---|---|
| ErrManagedKuberneteRoleNotAttach | please complete the cluster addon's service ramrole authorization at https://\*\*\* |
| ErrKubernetesAuditRoleNotAttach | please complete the cluster addon's service ramrole authorization at https://\*\*\* |
| ErrManagedAddonRoleNotAttach | please complete the cluster addon's service ramrole authorization at https://\*\*\* |
| ErrManagedSecurityRoleNotAttach | please complete the security ramrole authorization at https://\*\*\* |
| ErrEdgeAddonRoleNotAttach | please complete the edge cluster addon's service ramrole authorization at https://\*\*\* |
| ErrAutoScalerRoleNotAttach | please complete the cluster addon's service ramrole authorization at https://\*\*\* |
| ErrAcrHelperRoleNotAttach | please complete the cluster addon's service ramrole authorization at https://\*\*\* |
| ErrCostExporterRoleNotAttach | please complete the cluster addon's service ramrole authorization at https://\*\*\* |
| MissingAuth.AliyuncsManagedSecurityRole | please complete the security ramrole authorization at https://\*\*\* |
How do I navigate to the system role assignment page for ACK?
If ACK system roles have been revoked, reassign them following the steps in Quickly create an ACK managed cluster.
Only an Alibaba Cloud account (not a RAM user) can reassign system roles.
A RAM role was revoked from an ECS instance — what should I do?
When an application on an Elastic Compute Service (ECS) instance calls metadata api 100 and the RAM role has been removed, the request returns a 404 error or a message like:
Message:Node condition RAMRoleError is now: True, reason: NodeHasNoRAMRoleReassign the RAM role to the ECS instance:
-
Master node (ACK dedicated clusters only): On the Cluster Information page, go to the Basic Information tab and assign the Master RAM Role.
-
Worker node: On the Cluster Information page, go to the Basic Information tab and assign the Worker RAM Role.
For more information, see Replace an instance RAM role.
If you modified the content of the policy attached to the RAM role, check whether the modified content still contains the required permissions. If you modified the policy before the error occurred, try rolling back the policy to the original version.
How do I assign a custom RAM role to an ACK cluster?
Use a custom Worker RAM role. For more information, see Use custom worker RAM roles.
Will online workloads be affected after I delete a RAM user for a resigned employee?
You can use other RAM users to manage clusters as normal after you delete a RAM user. However, you must use an Alibaba Cloud account to revoke the kubeconfig file issued to the RAM user that you deleted. For more information, see Revoke the kubeconfig file of a cluster.
Before revoking the kubeconfig file issued to the deleted RAM user, replace it in any applications that use it with a new kubeconfig file. Otherwise, those applications will lose cluster access.