ACK's authorization system has two independent layers: RAM authorization controls access to cloud resources and ACK API operations, while RBAC authorization controls access to Kubernetes resources inside a cluster. Most user roles require both layers to be configured. This topic walks through the required permissions for four common roles — read-only administrators, O&M engineers, developers, and permission administrators.
Authorization system

RAM authorization uses system policies and custom policies to control access to ACK API operations and other Alibaba Cloud services. It covers:
-
Creating, viewing, upgrading, and deleting clusters
-
Creating, modifying, and scaling node pools
-
Managing authorization
-
Monitoring clusters and collecting logs and events
RBAC authorization uses Kubernetes RBAC to control access to Kubernetes resources inside a cluster. It covers add, delete, modify, and query operations on the following resource types:
-
Workloads: Deployment, StatefulSet, DaemonSet, Job, CronJob, pod, and ReplicaSet
-
Network resources: Service, Ingress, and NetworkPolicy
-
Storage resources: persistent volume (PV), persistent volume claim (PVC), and StorageClass
-
Namespace, ConfigMap, and Secret
Prerequisites
Before you begin, ensure that you have:
-
Completed the necessary steps to be a permissions administrator, if you are performing these authorization tasks as a RAM user or RAM role (not as the Alibaba Cloud account owner). See Designate a RAM user or role as a permission administrator.
Use case 1: Grant read-only administrators the permissions to view cluster resources
Read-only administrators need read-only access to Kubernetes resources across all namespaces in a cluster. Assign them the Read-only Administrator predefined RBAC role — no RAM authorization step is required.
Assign the Read-only Administrator role
ACK console
See Grant RBAC permissions to a RAM user or RAM role.
Alibaba Cloud CLI
Call the GrantPermissions operation and set role_name to admin-view. Use the DescribeUserPermission operation to verify the assigned permissions.
aliyun cs POST /permissions/users/234xxxxxxxx --header "Content-Type=application/json;" --body "[{\"cluster\":\"c24xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx\",\"is_custom\":false,\"role_name\":\"admin-view\",\"role_type\":\"cluster\"}]"Terraform
resource "alicloud_cs_kubernetes_permissions" "default" {
uid = alicloud_ram_user.user.id
permissions {
cluster = alicloud_cs_managed_kubernetes.default.id
role_type = "cluster"
role_name = "admin-view"
namespace = ""
is_custom = false
is_ram_role = false
}
}Use case 2: Grant O&M engineers the permissions to manage clusters and applications
O&M engineers need to manage and maintain clusters and applications. This requires both RAM authorization and RBAC authorization.
Step 1: RAM authorization
ACK provides two system-managed RAM policies:
| Policy | Access level |
|---|---|
AliyunCSFullAccess |
Full read/write access to all ACK API operations |
AliyunCSReadOnlyAccess |
Read-only access to all ACK API operations |
In the RAM console, attach the appropriate policy to the RAM user or RAM role. See Grant permissions to a RAM user and Grant permissions to a RAM role.RAM consoleRAM console
For fine-grained access control, create a custom policy instead. See Use RAM to grant the permissions to access clusters and cloud resources. The following example policy covers the full set of O&M operations. For details on each action, see Action description.
{
"Version": "1",
"Statement": [
{
"Effect": "Allow",
"Action": [
"cs:GetClusters",
"cs:ModifyCluster",
"cs:UpgradeCluster",
"cs:DescribeClusterDetail",
"cs:DescribeClusterVuls",
"cs:DescribeClusterSecuritySummary",
"cs:DescribeClusterUserKubeconfig",
"cs:RevokeK8sClusterKubeConfig",
"cs:CheckControlPlaneLogEnable",
"cs:DescribeClusterResources",
"cs:DescribeClusterEvents",
"cs:DescribeClusterLogs",
"cs:GetClusterAuditProject",
"cs:ListClusterChecks",
"cs:GetClusterCheck",
"cs:RunClusterCheck",
"cs:ModifyClusterAudit",
"cs:DescribeResourcesDeleteProtection",
"cs:UpdateResourcesDeleteProtection",
"cs:DescribeClusterNodePools",
"cs:DescribeClusterNodePoolDetail",
"cs:CreateClusterNodePool",
"cs:ModifyClusterNodePool",
"cs:UpgradeClusterNodepool",
"cs:DeleteClusterNodepool",
"cs:CreateAutoscalingConfig",
"cs:SyncClusterNodePool",
"cs:RepairClusterNodePool",
"cs:AttachInstancesToNodePool",
"cs:ModifyNodePoolNodeConfig",
"cs:DescribeClusterNodes",
"cs:RemoveClusterNodes",
"cs:RemoveNodePoolNodes",
"cs:DiagnoseClustersNode",
"cs:DescribeNodePoolVuls",
"cs:FixNodePoolVuls",
"cs:DrainNodes",
"cs:DescribeClusterAddonMetadata",
"cs:DescribeClusterAddonsVersion",
"cs:InstallClusterAddons",
"cs:UpgradeClusterAddons",
"cs:ModifyClusterAddon",
"cs:UnInstallClusterAddons",
"cs:DescribeClusterAddonInstance",
"cs:DescribeClusterAddonsUpgradeStatus",
"cs:DescribeClusterAddonUpgradeStatus",
"cs:ListClusterComponent",
"cs:GetClusterComponent",
"cs:DescribePolicyInstances",
"cs:DeployPolicyInstance",
"cs:ModifyPolicyInstance",
"cs:DeletePolicyInstance",
"cs:DescribePolicyGovernanceInCluster",
"cs:DescribePolicyInstancesStatus",
"cs:UpdateContactGroupForAlert",
"cs:StartAlert",
"cs:StopAlert",
"cs:ListAlertRules",
"cs:GetAlertHistory",
"cs:DescribeClusterTasks",
"cs:GetClusterBasicInfo",
"cs:ListClusterReportSummary",
"cs:GetClusterReportSummary",
"cs:ListReportTaskRule",
"cs:CreateTrigger",
"cs:DescribeKubernetesClusterHookTrigger",
"cs:CreateDiagnose",
"cs:CreateClusterOverviewReport",
"cs:GetAIDiagnosisResult",
"cs:CreateReportTaskRule",
"cs:CreateClusterReport",
"cs:GetClusterCheckResult",
"cs:GetClusterServices",
"cs:UpdateControlPlaneLog",
"cs:UpdateClusterName"
],
"Resource": "acs:cs:*:*:cluster/xxxxx"
},
{
"Effect": "Allow",
"Action": [
"cs:DescribeSubAccountHelmPermission",
"cs:CheckServiceRole",
"cs:DeleteTriggerHook",
"cs:QueryAlertContact",
"cs:QueryAlertContactGroup",
"cs:AddOrUpdateAlertContact",
"cs:AddOrUpdateAlertContactGroup",
"cs:DeleteAlertContact",
"cs:DeleteAlertContactGroup",
"cs:DescribeKubernetesVersionMetadata",
"cs:ListOperationPlans",
"cs:DescribeClusterEndpoints",
"cs:DescribeTaskInfo",
"cs:DescribeEvents",
"cs:DescribeUserQuota",
"cs:DescribeTasks",
"cs:PauseTask",
"cs:CancelTask",
"cs:DescribeAddons",
"cs:DeleteReportTaskRule",
"cs:CreateSessionMessage",
"cs:DescribePolicies",
"cs:DescribePolicyDetails"
],
"Resource": "*"
},
{
"Effect": "Allow",
"Action": [
"vpc:DescribeVSwitches",
"vpc:DescribeVpcs",
"vpc:DescribeEipAddresses"
],
"Resource": "*"
},
{
"Effect": "Allow",
"Action": "kms:ListKeys",
"Resource": "*"
},
{
"Effect": "Allow",
"Action": [
"arms:ListDashboards",
"arms:InstallAddon"
],
"Resource": "*"
},
{
"Effect": "Allow",
"Action": [
"cloudshell:CreateEnvironment",
"cloudshell:AttachStorage",
"cloudshell:DetachStorage",
"cloudshell:CreateSession"
],
"Resource": "*"
},
{
"Effect": "Allow",
"Action": [
"ess:DescribeScalingActivities",
"ess:DescribeScalingActivityDetail",
"ess:DescribeLifecycleActions"
],
"Resource": "*"
},
{
"Effect": "Allow",
"Action": "oos:ListExecutions",
"Resource": "*"
},
{
"Effect": "Allow",
"Action": [
"ecs:DescribeKeyPairs",
"ecs:DescribeInstances",
"ecs:DescribeSecurityGroups",
"ecs:DescribeImages",
"ecs:DescribePrice"
],
"Resource": "*"
},
{
"Effect": "Allow",
"Action": [
"cr:ListInstance",
"cr:ListInstanceDomain",
"cr:ListRepository",
"cr:ListArtifactTag"
],
"Resource": "*"
},
{
"Effect": "Allow",
"Action": "ram:GetRole",
"Resource": "acs:ram:*:*:role/aliyuncisdefaultrole"
},
{
"Effect": "Allow",
"Action": [
"log:GetDashboard",
"log:GetSavedSearch",
"log:GetLogStore",
"log:GetIndex",
"log:UpdateIndex",
"log:GetLogStoreLogs",
"log:CreateDashboardSharing",
"log:ListProject",
"log:GetProjectLogs",
"log:GetResourceRecord",
"log:CreateResourceRecord",
"log:UpdateResourceRecord"
],
"Resource": "*"
}
]
}Replacexxxxxinacs:cs:*:*:cluster/xxxxxwith your cluster ID.
For a full reference on ACK API actions, see [Product Changes] ACK API enhances user authentication and List of operations by function.
Step 2: RBAC authorization
After RAM authorization, assign a predefined RBAC role to the RAM user or RAM role. The following table describes all predefined roles and their security scope.
| Predefined role | RBAC permissions on cluster resources | When to use |
|---|---|---|
| Administrator | Full read/write access to all Kubernetes resources in all namespaces, plus cluster-level resources: nodes, PVs, namespaces, and resource quotas | Cluster administrators who need unrestricted access. If you need permission management capabilities too, consider Custom > cluster-admin instead. |
| Read-only Administrator | Read-only access to all Kubernetes resources in all namespaces, plus cluster-level resources: nodes, PVs, namespaces, and resource quotas | Auditors or team leads who need cluster-wide visibility without write access. |
| O&M Engineer | Read/write access to all console-visible resources in all namespaces; read and update access to nodes, PVs, and namespaces; read-only access to all other resources | O&M engineers managing day-to-day cluster operations. Does not include permission management. |
| Developer | Read/write access to console-visible resources, scoped to all namespaces or a specified set | Developers deploying and managing applications. Scope can be limited to specific namespaces. |
| Restricted User | Read-only access to console-visible resources, scoped to all namespaces or a specified set | Developers or operators who only need to view resources, not modify them. |
| Custom | Permissions determined by the ClusterRole you select. Review the ClusterRole's permissions carefully before assigning it. For details, see Use custom RBAC roles to restrict resource operations in a cluster. | Fine-grained access control beyond the predefined roles. |
Assigning the cluster-admin ClusterRole grants the same permissions as the Alibaba Cloud account — full control over all resources in the cluster. Use caution.
To assign a role in the console:
-
Log on to the ACK consoleACK console. In the left navigation pane, click Authorizations.
-
On the Authorizations page, click the RAM Users or RAM Roles tab. Find the target user or role and click Modify Permissions.
-
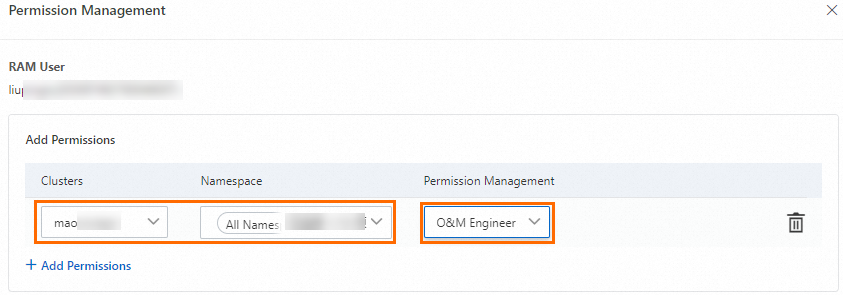
In the panel, click +Add Permissions, select O&M Engineer for the target cluster and namespace, and click Submit.
After assigning the role, ACK automatically creates a ClusterRoleBinding for the RAM user or RAM role. The following shows the full ClusterRole definition for the O&M Engineer role (cs:ops):
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
name: cs:ops
rules:
- apiGroups: [""]
resources: ["pods", "pods/attach", "pods/exec", "pods/portforward", "pods/proxy"]
verbs: ["create", "delete", "deletecollection", "get", "list", "patch", "update", "watch"]
- apiGroups: [""]
resources: ["configmaps", "endpoints", "persistentvolumeclaims", "replicationcontrollers", "replicationcontrollers/scale", "secrets", "serviceaccounts", "services", "services/proxy"]
verbs: ["create", "delete", "deletecollection", "get", "list", "patch", "update", "watch"]
- apiGroups: [""]
resources: ["bindings", "events", "limitranges", "namespaces/status", "replicationcontrollers/status", "pods/log", "pods/status", "resourcequotas", "resourcequotas/status", "componentstatuses"]
verbs: ["get", "list", "watch"]
- apiGroups: [""]
resources: ["namespaces", "nodes", "persistentvolumes"]
verbs: ["get", "list", "watch", "patch"]
- apiGroups: ["coordination.k8s.io"]
resources: ["leases"]
verbs: ["get"]
- apiGroups: ["apps"]
resources: ["daemonsets", "deployments", "deployments/rollback", "deployments/scale", "replicasets", "replicasets/scale", "statefulsets"]
verbs: ["create", "delete", "deletecollection", "get", "list", "patch", "update", "watch"]
- apiGroups: ["autoscaling"]
resources: ["horizontalpodautoscalers"]
verbs: ["create", "delete", "deletecollection", "get", "list", "patch", "update", "watch"]
- apiGroups: ["batch"]
resources: ["cronjobs", "jobs"]
verbs: ["create", "delete", "deletecollection", "get", "list", "patch", "update", "watch"]
- apiGroups: ["extensions"]
resources: ["daemonsets", "deployments", "deployments/rollback", "deployments/scale","ingresses","replicasets", "replicasets/scale", "replicationcontrollers/scale"]
verbs: ["create", "delete", "deletecollection", "get", "list", "patch", "update", "watch"]
- apiGroups: ["networking.k8s.io"]
resources: ["*"]
verbs: ["create", "delete", "deletecollection", "get", "list", "patch", "update", "watch"]
- apiGroups: ["servicecatalog.k8s.io"]
resources: ["clusterserviceclasses", "clusterserviceplans", "clusterservicebrokers", "serviceinstances", "servicebindings"]
verbs: ["create", "delete", "get", "list", "patch", "update", "watch"]
- apiGroups: ["servicecatalog.k8s.io"]
resources: ["clusterservicebrokers/status", "clusterserviceclasses/status", "clusterserviceplans/status", "serviceinstances/status", "serviceinstances/reference", "servicebindings/status",]
verbs: ["update"]
- apiGroups: ["storage.k8s.io"]
resources: ["storageclasses"]
verbs: ["get", "list", "watch"]
- apiGroups: ["alicloud.com"]
resources: ["*"]
verbs: ["create", "delete", "get", "list", "patch", "update", "watch"]
- apiGroups: ["policy"]
resources: ["poddisruptionbudgets"]
verbs: ["create", "delete", "deletecollection", "get", "list", "patch", "update", "watch"]
- apiGroups: ["metrics.k8s.io"]
resources: ["pods", "nodes"]
verbs: ["get", "watch", "list"]
- apiGroups: ["networking.istio.io"]
resources: ["*"]
verbs: ["create", "delete", "deletecollection", "get", "list", "patch", "update", "watch"]
- apiGroups: ["config.istio.io"]
resources: ["*"]
verbs: ["create", "delete", "deletecollection", "get", "list", "patch", "update", "watch"]
- apiGroups: ["rbac.istio.io"]
resources: ["*"]
verbs: ["create", "delete", "deletecollection", "get", "list", "patch", "update", "watch"]
- apiGroups: ["istio.alibabacloud.com"]
resources: ["*"]
verbs: ["create", "delete", "deletecollection", "get", "list", "patch", "update", "watch"]
- apiGroups: ["authentication.istio.io"]
resources: ["*"]
verbs: ["create", "delete", "deletecollection", "get", "list", "patch", "update", "watch"]
- apiGroups: ["log.alibabacloud.com"]
resources: ["*"]
verbs: ["create", "delete", "deletecollection", "get", "list", "patch", "update", "watch"]
- apiGroups: ["monitoring.kiali.io"]
resources: ["*"]
verbs: ["create", "delete", "deletecollection", "get", "list", "patch", "update", "watch"]
- apiGroups: ["kiali.io"]
resources: ["*"]
verbs: ["create", "delete", "deletecollection", "get", "list", "patch", "update", "watch"]
- apiGroups: ["apiextensions.k8s.io"]
resources: ["customresourcedefinitions"]
verbs: ["get", "list", "create", "watch", "patch", "update", "delete", "deletecollection"]
- apiGroups: ["serving.knative.dev"]
resources: ["*"]
verbs: ["get", "list", "create", "watch", "patch", "update", "delete", "deletecollection"]
- apiGroups: ["eventing.knative.dev"]
resources: ["*"]
verbs: ["get", "list", "create", "watch", "patch", "update", "delete", "deletecollection"]
- apiGroups: ["messaging.knative.dev"]
resources: ["*"]
verbs: ["get", "list", "create", "watch", "patch", "update", "delete", "deletecollection"]
- apiGroups: ["sources.eventing.knative.dev"]
resources: ["*"]
verbs: ["get", "list", "create", "watch", "patch", "update", "delete", "deletecollection"]
- apiGroups: ["tekton.dev"]
resources: ["*"]
verbs: ["get", "list", "create", "watch", "patch", "update", "delete", "deletecollection"]
- apiGroups: ["alert.alibabacloud.com"]
resources: ["*"]
verbs: ["get", "list", "create", "watch", "patch", "update", "delete", "deletecollection"]For fine-grained control, create a custom ClusterRole using Kubernetes RBAC, then select it from the Authorizations page in the ACK consoleACK console. See Use custom RBAC roles to restrict resource operations in a cluster.
Use case 3: Grant developers the permissions to manage clusters and applications
Developers need RBAC authorization to manage Kubernetes resources and read-only RAM authorization on the cluster.
Complete RAM authorization before RBAC authorization. Developers must have at least read-only RAM permissions on the cluster for RBAC authorization to take effect.
Step 1: RAM authorization
In the RAM console, create a custom policy and attach it to the RAM user or RAM role. See Grant access to clusters and cloud resources using RAM. The following example grants the minimum read-only permissions required:
{
"Statement": [
{
"Action": [
"cs:GetClusters",
"cs:DescribeClusterDetail",
"cs:GetClusterAuditProject",
"cs:DescribeResourcesDeleteProtection"
],
"Resource": "acs:cs:*:*:cluster/xxxxx",
"Effect": "Allow"
}
],
"Version": "1"
}Replacexxxxxwith your cluster ID. To grant read-only permissions on all ACK clusters instead, attach theAliyunCSReadOnlyAccesssystem policy.
Step 2: RBAC authorization
-
Log on to the ACK consoleACK console. In the left navigation pane, click Authorizations.
-
On the Authorizations page, click the RAM Users or RAM Roles tab. Find the target user or role and click Modify Permissions.
-
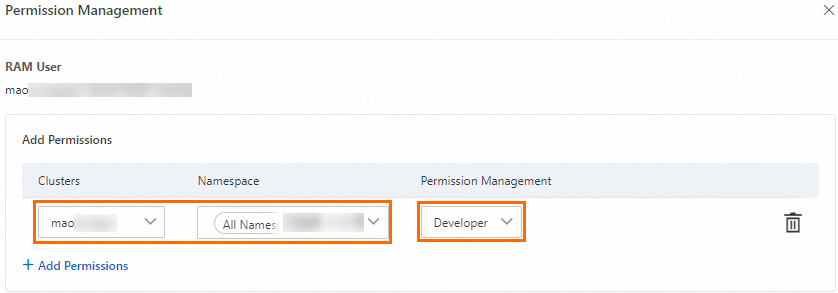
In the panel, click +Add Permissions, select Developer for the target cluster and namespace, and click Submit.
After assigning the role, ACK automatically creates a ClusterRoleBinding for the RAM user or RAM role. The following shows the full ClusterRole definition for the Developer role (cs:ns:dev):
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
name: cs:ns:dev
rules:
- apiGroups: [""]
resources: ["pods", "pods/attach", "pods/exec", "pods/portforward", "pods/proxy"]
verbs: ["create", "delete", "deletecollection", "get", "list", "patch", "update", "watch"]
- apiGroups: [""]
resources: ["configmaps", "endpoints", "persistentvolumeclaims", "replicationcontrollers", "replicationcontrollers/scale", "secrets", "serviceaccounts", "services", "services/proxy"]
verbs: ["create", "delete", "deletecollection", "get", "list", "patch", "update", "watch"]
- apiGroups: [""]
resources: ["events", "replicationcontrollers/status", "pods/log", "pods/status"]
verbs: ["get", "list", "watch"]
- apiGroups: ["apps"]
resources: ["daemonsets", "deployments", "deployments/rollback", "deployments/scale", "replicasets", "replicasets/scale", "statefulsets"]
verbs: ["create", "delete", "deletecollection", "get", "list", "patch", "update", "watch"]
- apiGroups: ["autoscaling"]
resources: ["horizontalpodautoscalers"]
verbs: ["create", "delete", "deletecollection", "get", "list", "patch", "update", "watch"]
- apiGroups: ["batch"]
resources: ["cronjobs", "jobs"]
verbs: ["create", "delete", "deletecollection", "get", "list", "patch", "update", "watch"]
- apiGroups: ["extensions"]
resources: ["daemonsets", "deployments", "deployments/rollback", "deployments/scale","ingresses","replicasets", "replicasets/scale", "replicationcontrollers/scale"]
verbs: ["create", "delete", "deletecollection", "get", "list", "patch", "update", "watch"]
- apiGroups: ["networking.k8s.io"]
resources: ["*"]
verbs: ["create", "delete", "deletecollection", "get", "list", "patch", "update", "watch"]
- apiGroups: ["servicecatalog.k8s.io"]
resources: ["clusterserviceclasses", "clusterserviceplans", "clusterservicebrokers", "serviceinstances", "servicebindings"]
verbs: ["create", "delete", "get", "list", "patch", "update", "watch"]
- apiGroups: ["servicecatalog.k8s.io"]
resources: ["clusterservicebrokers/status", "clusterserviceclasses/status", "clusterserviceplans/status", "serviceinstances/status", "serviceinstances/reference", "servicebindings/status",]
verbs: ["update"]
- apiGroups: ["alicloud.com"]
resources: ["*"]
verbs: ["create", "delete", "get", "list", "patch", "update", "watch"]
- apiGroups: ["policy"]
resources: ["poddisruptionbudgets"]
verbs: ["create", "delete", "deletecollection", "get", "list", "patch", "update", "watch"]
- apiGroups: ["networking.istio.io"]
resources: ["*"]
verbs: ["create", "delete", "deletecollection", "get", "list", "patch", "update", "watch"]
- apiGroups: ["config.istio.io"]
resources: ["*"]
verbs: ["create", "delete", "deletecollection", "get", "list", "patch", "update", "watch"]
- apiGroups: ["rbac.istio.io"]
resources: ["*"]
verbs: ["create", "delete", "deletecollection", "get", "list", "patch", "update", "watch"]
- apiGroups: ["istio.alibabacloud.com"]
resources: ["*"]
verbs: ["create", "delete", "deletecollection", "get", "list", "patch", "update", "watch"]
- apiGroups: ["authentication.istio.io"]
resources: ["*"]
verbs: ["create", "delete", "deletecollection", "get", "list", "patch", "update", "watch"]
- apiGroups: ["log.alibabacloud.com"]
resources: ["*"]
verbs: ["create", "delete", "deletecollection", "get", "list", "patch", "update", "watch"]
- apiGroups: ["monitoring.kiali.io"]
resources: ["*"]
verbs: ["create", "delete", "deletecollection", "get", "list", "patch", "update", "watch"]
- apiGroups: ["kiali.io"]
resources: ["*"]
verbs: ["create", "delete", "deletecollection", "get", "list", "patch", "update", "watch"]
- apiGroups: ["apiextensions.k8s.io"]
resources: ["customresourcedefinitions"]
verbs: ["get", "list", "create", "watch", "patch", "update", "delete", "deletecollection"]
- apiGroups: ["serving.knative.dev"]
resources: ["*"]
verbs: ["get", "list", "create", "watch", "patch", "update", "delete", "deletecollection"]
- apiGroups: ["eventing.knative.dev"]
resources: ["*"]
verbs: ["get", "list", "create", "watch", "patch", "update", "delete", "deletecollection"]
- apiGroups: ["messaging.knative.dev"]
resources: ["*"]
verbs: ["get", "list", "create", "watch", "patch", "update", "delete", "deletecollection"]
- apiGroups: ["sources.eventing.knative.dev"]
resources: ["*"]
verbs: ["get", "list", "create", "watch", "patch", "update", "delete", "deletecollection"]
- apiGroups: ["tekton.dev"]
resources: ["*"]
verbs: ["get", "list", "create", "watch", "patch", "update", "delete", "deletecollection"]
- apiGroups: ["alert.alibabacloud.com"]
resources: ["*"]
verbs: ["get", "list", "create", "watch", "patch", "update", "delete", "deletecollection"]For fine-grained control, create a custom ClusterRole using Kubernetes RBAC, then select it from the Authorizations page in the ACK consoleACK console. See Use custom RBAC roles to restrict resource operations in a cluster.
Use case 4: Grant permission administrators the permissions to manage RAM user and RAM role permissions
Permission administrators need to manage the RBAC permissions of other RAM users and RAM roles. By default, a RAM user or RAM role cannot grant RBAC permissions to others. On the Authorizations page, the console displays: The current RAM user account has no permission to manage authorizations. Contact the Alibaba Cloud account owner or authorized RAM user to request permission.
This requires both RAM authorization and RBAC authorization.
Step 1: RAM authorization
The RAM policy must include permissions to:
-
Query other RAM users and RAM roles in the same Alibaba Cloud account
-
Query the RBAC permissions of a RAM user or RAM role
-
Grant RBAC permissions to other RAM users or RAM roles
In the RAM console, attach the following policy to the RAM user or RAM role:RAM console
{
"Statement": [
{
"Action": [
"ram:ListRoles",
"ram:ListUserBasicInfos",
"cs:GetClusters",
"cs:DescribeUserPermission",
"cs:DescribeClusterDetail",
"cs:GrantPermissions",
"cs:UpdateUserPermissions",
"cs:GetClusterAuditProject",
"cs:DescribeResourcesDeleteProtection",
"cs:UpdateResourcesDeleteProtection",
"cs:DescribeClusterAddonUpgradeStatus"
],
"Resource": "*",
"Effect": "Allow"
}
],
"Version": "1"
}Step 2: RBAC authorization
-
Log on to the ACK consoleACK console. In the left navigation pane, click Authorizations.
-
On the Authorizations page, click the RAM Users or RAM Roles tab. Find the target user or role and click Modify Permissions.
-
In the panel, click Add Permissions, select Administrator or
cluster-adminunder Custom, and click Submit.
By default, Alibaba Cloud accounts and cluster owners are assigned the cluster-admin role and have full access to all Kubernetes resources in the cluster.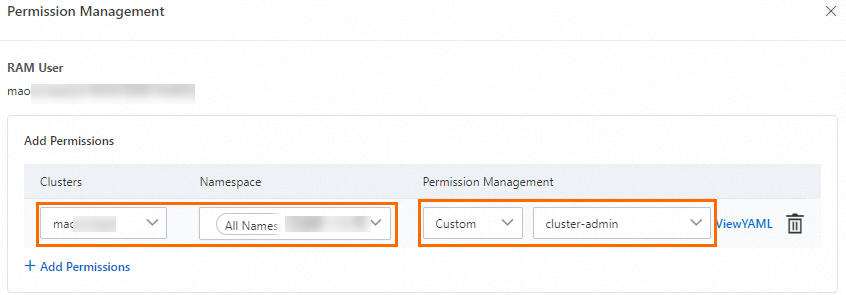
After completing both authorization steps, the RAM user or RAM role can grant other RAM users or RAM roles RBAC permissions within the configured scope.