An Elastic Compute Service (ECS) security group is a virtual firewall that is used to control the inbound and outbound traffic of ECS instances in the security group. This topic describes how to configure a security group to allow the ECS instances in the security group to access a PolarDB for MySQL cluster.
Scenario
After you create a PolarDB for MySQL cluster, you cannot connect ECS instances to the cluster. You must add a security group to the whitelist of the PolarDB for MySQL cluster to allow the ECS instances in the security group to access the PolarDB for MySQL cluster.
For more information about security groups and how to configure a security group in the ECS console, see Create a security group.
You can also add the IP addresses of ECS instances to an IP whitelist. The ECS instances in the IP whitelist and the ECS instances in the security group that is added to the cluster whitelist can access the PolarDB for MySQL cluster.
Precautions
The network types of a PolarDB for MySQL cluster and the security groups that are added to its whitelist must be the same. For example, if your PolarDB for MySQL cluster is deployed in a virtual private cloud (VPC), you can add only security groups of the VPC type.
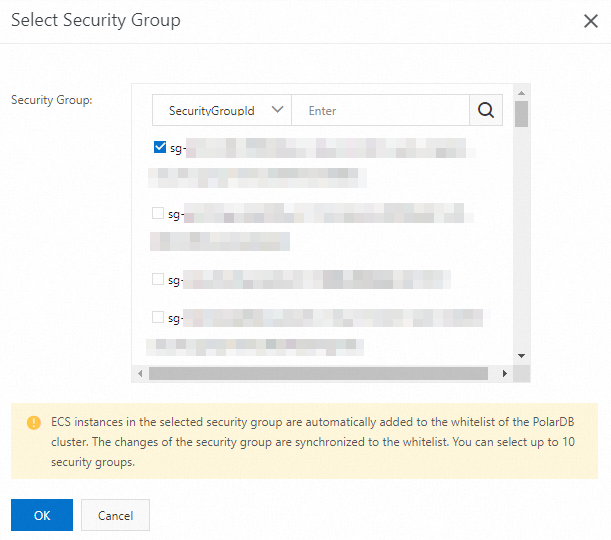
You can add up to 10 security groups to a PolarDB for MySQL cluster.
When a security group is added to a PolarDB for MySQL cluster, the IP addresses of the ECS instances in the security group are added to the whitelist of the cluster. The security group rules do not affect this operation.
Procedure
Log on to the PolarDB console.
In the left-side navigation pane, click Clusters.
In the upper-left corner, select the region where the cluster to which you want to connect is deployed.
Find the cluster and click its ID.
In the left-side navigation pane, choose .
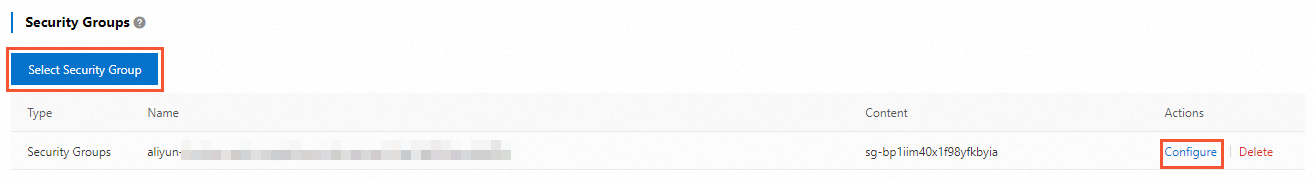
On the Cluster Whitelists page, you can click Select Security Group to add a security group. You can also click Configure in the Actions column to change the security groups.
In the Select Security Groups panel, select one or more security groups and click OK.
 Note
NoteFor more information about how to create a security group, see Create a security group.
Related API operations
API | Description |
Queries the IP addresses that are allowed to access a specified PolarDB for MySQL cluster. | |
Modifies the IP addresses that are allowed to access a specified PolarDB for MySQL cluster. |