Vulnerability Management automates the discovery, assessment, and remediation of security vulnerabilities on your servers. It covers operating systems (OS), Web Content Management Systems (Web-CMS), and various applications, replacing traditional manual patching with automated scanning and one-click fixes — making it practical for large-scale server fleets.
Use cases
Continuous monitoring for production servers
When to use: Critical business servers that require daily scanning and timely fixes to stay secure and stable.
Supported editions: Advanced, Enterprise, or Ultimate.
What you get: One automatic scan per day, unlimited vulnerability fixes, and on-demand manual scans for incident response.
Basic protection for dev/test environments or small fleets
When to use: Fewer than 10 servers, or development and testing environments, where minimizing cost is a priority.
Supported editions: Anti-virus, with the option to purchase vulnerability fixes on demand.
What you get: One automatic scan every two days. Fix individual vulnerabilities pay-as-you-go, or buy a fix package for predictable costs.
Emergency response to newly disclosed vulnerabilities
When to use: A high-profile vulnerability (such as Log4j2) is publicly disclosed and you need to immediately assess your exposure.
Supported editions: Enterprise or Ultimate.
What you get: Trigger a manual scan on all or a subset of servers right away. Scan results include detailed vulnerability information and official remediation guidance for manual fixes.
Core features
Vulnerability scan
Two scan methods are available: manual vulnerability scan and periodic automatic vulnerability scan.
| Manual vulnerability scan | Periodic automatic vulnerability scan | |
|---|---|---|
| Trigger | Initiated on demand from the console | Runs automatically at scheduled intervals based on a preset policy |
| Frequency | Any time, as often as needed | Advanced, Enterprise, and Ultimate: daily. Basic Edition and other editions: every two days. |
| Best for | Emergency response to newly disclosed high-risk CVEs; post-deployment verification | Ongoing compliance monitoring; regularly scheduled reports across all assets without manual effort |
Vulnerability fixing
Security Center provides One-click Fix, which automatically deploys a patch so you can resolve vulnerabilities without logging in to each server individually.
Application Vulnerability and Urgent Vulnerability do not support One-click Fix from the console. Log in to the server and fix them manually, following the guidance in the vulnerability details.
How fixes are counted
The minimum unit is one Security Notice fixed on one server, which counts as one fix.
A single Security Notice may bundle multiple related CVEs. Fixing the Security Notice counts as one fix, regardless of how many CVEs it includes.
The total number of fixes equals the sum of Security Notices with a Fixed status across all servers.
A fix is counted only after the server restarts and the status changes to Fixed. Failed fixes are not counted.
Example: If you fix 10 Security Notices on each of 5 servers, the total fix count is 5 x 10 = 50 fixes.
Fix priority
Security Center calculates a Vulnerability Remediation Urgency Score to help you decide what to fix first. The score combines the Alibaba Cloud Vulnerability Score (based on CVSS) with real-world cloud attack data:
Vulnerability Remediation Urgency Score = Alibaba Cloud Vulnerability Score x Time Factor x Environment Factor x Asset Importance Factor
Alibaba Cloud Vulnerability Score: Rates the inherent severity of the vulnerability.
Time Factor: Accounts for how long the vulnerability has been public and how widely its exploits have spread (range: 0-1).
Environment Factor: Reflects how exploitable the vulnerability is in your specific server environment — for example, whether the server is exposed to the public internet. This value is adjusted dynamically.
Asset Importance Factor: Scales the score based on how you've tagged the asset: Important (1.5), General (1), or Test (0.5).
| Priority | Remediation urgency score | Description | Recommendation |
|---|---|---|---|
| High | 13.5 or higher | Easily exploitable by an unauthenticated remote attacker with no user interaction required. Code execution or full compromise is possible. Commonly weaponized by worms and ransomware. | Fix as soon as possible |
| Medium | 7.1-13.5 | May compromise confidentiality, integrity, or availability. Often has a high official rating but no confirmed public exploit yet. | Can be fixed later |
| Low | Below 7.1 | Very low probability of successful exploitation, or negligible impact if exploited. Typically involves source code bugs or minor compliance issues. | Can be postponed |
| Special | — | Urgent Vulnerability and Web-CMS Vulnerability: high-risk vulnerabilities confirmed by Alibaba Cloud security engineers. If the Environment Factor cannot be calculated due to network issues, the recommendation may show as "Can be postponed." | Fix as soon as possible |
Detection rules and data management
Rule update schedule
Security Center regularly updates its vulnerability detection rules to cover new Security Notices from OS vendors.
Rule updates may be delayed during public holidays.
Linux: High-risk vulnerabilities are added within 48 hours of the vendor announcement. CVE vulnerabilities are added within 14 days.
Windows: CVE vulnerability detection rules are added within 48 hours of Microsoft's announcement.
Data retention policy
Security Center automatically removes stale vulnerability data to maintain system performance.
Active vulnerabilities: If a vulnerability's status (Fixed, Fixing Failed, Ignored, Unfixed, Fixing, or Verifying) remains unchanged for one year, the record is deleted automatically.
Invalid vulnerabilities: Records with an Invalid status are deleted after the retention period configured in Retain Invalid Vulnerabilities For under Vulnerability Settings.
Billing
Security Center supports two billing models for vulnerability scanning and fixing:
Subscription: Purchase an edition or the Vulnerability Fixing value-added service.
Pay-as-you-go: Purchase Host and Container Security or the Vulnerability Fixing post-paid feature.
For pricing details, see Billing overview.
After purchase, associate your servers with an edition or protection level to activate scanning and fixing. See Manage host and container security quotas.
The capabilities available depend on your service model and edition:
| Service model | Edition / protection level | Manual scan scope | Periodic automatic scan scope | Vulnerability fixing |
|---|---|---|---|---|
| Subscription | Enterprise Edition, Ultimate Edition | All vulnerability types | All vulnerability types | Linux, Windows, and Web-CMS vulnerabilities |
| Subscription | Advanced Edition | All except Application Vulnerability | All except Application Vulnerability | Linux and Windows vulnerabilities |
| Subscription | Basic Edition, Value-added Edition, Anti-virus Edition | Urgent Vulnerability only | Linux Software Vulnerability, Windows System Vulnerability, Web-CMS Vulnerability | Requires a separate Vulnerability Fix value-added service. After purchase: Linux and Windows vulnerabilities. See Purchase Vulnerability Fixing (Subscription) and Activate Vulnerability Fixing (Pay-as-you-go). |
| Pay-as-you-go | Host Protection, Host and Container Protection | All vulnerability types | All vulnerability types | — |
| Pay-as-you-go | Unprotected, Anti-Virus | Urgent Vulnerability only | Linux Software Vulnerability, Windows System Vulnerability, Web-CMS Vulnerability | — |
Get started
Purchase and activate Vulnerability Management: Purchase Security Center.
Associate your servers with an edition or protection level: Manage licenses.
Scan for vulnerabilities: Scan for vulnerabilities.
View and handle vulnerabilities: View and handle vulnerabilities.
Troubleshoot failures: Troubleshoot issues that cause vulnerability fixing failures.
FAQ
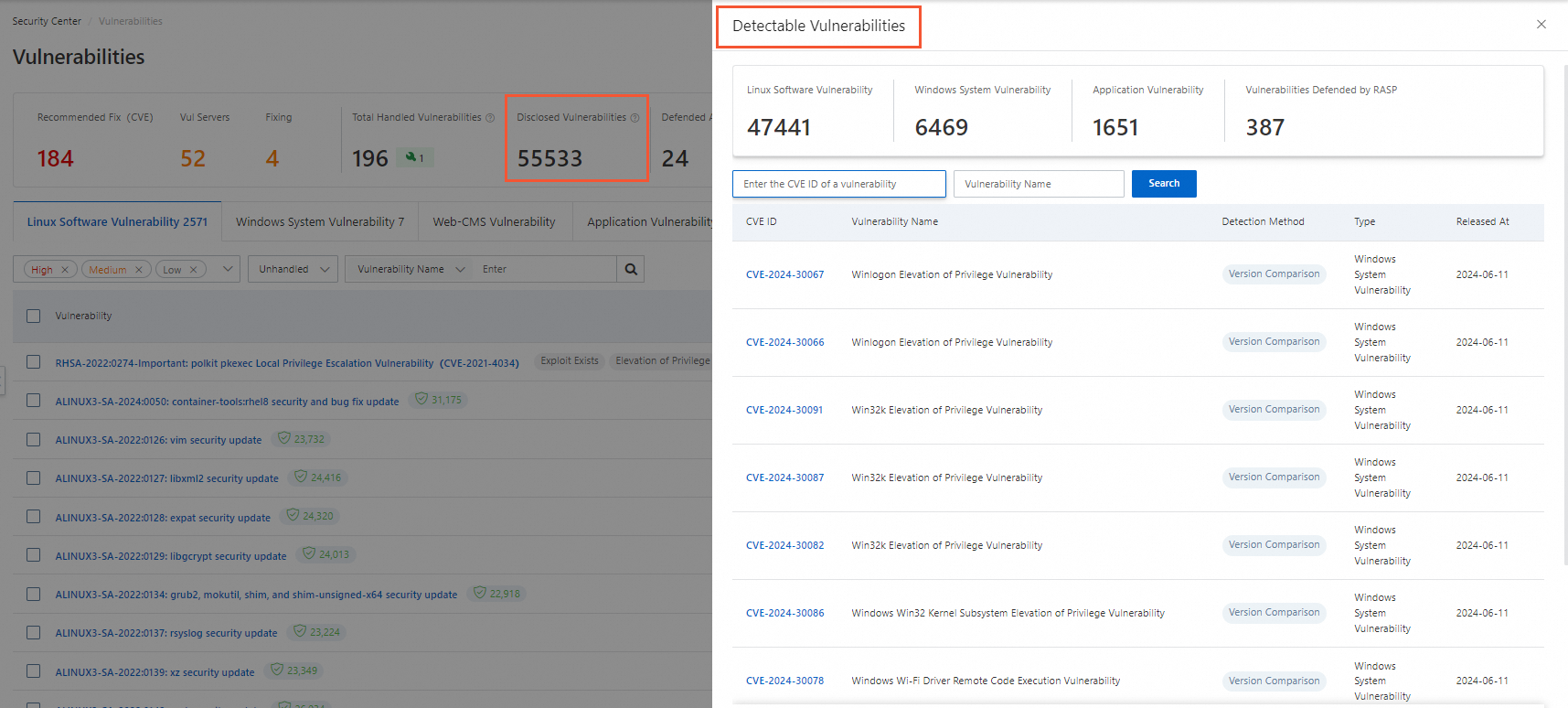
How do I see which vulnerabilities Security Center can detect?
On the Vulnerabilities page, click the number in the Disclosed Vulnerabilities section to see the full list.
Appendix
Supported operating systems
| OS | Supported versions |
|---|---|
| Windows Server | Windows Server 2008 (vulnerabilities before EOL), Windows Server 2012 (vulnerabilities before EOL), Windows Server 2016, Windows Server 2019, Windows Server 2022 |
| CentOS | CentOS 5 (vulnerabilities before EOL), CentOS 6 (vulnerabilities before EOL), CentOS 7, CentOS 8 (vulnerabilities before EOL) |
| Red Hat | Red Hat 5 (vulnerabilities before EOL), Red Hat 6 (vulnerabilities before EOL), Red Hat 7, Red Hat 8, Red Hat 9 |
| Ubuntu | Ubuntu 12 (vulnerabilities before EOL), Ubuntu 14 (vulnerabilities before EOL), Ubuntu 16 (vulnerabilities before EOL), Ubuntu 18 (vulnerabilities before EOL), Ubuntu 20, Ubuntu 21, Ubuntu 22.04 |
| Alibaba Cloud Linux | Alibaba Cloud Linux 2.1903, Alibaba Cloud Linux 3 |
| Anolis OS | Anolis OS 7, Anolis OS 8 |
| Debian | Debian 8, Debian 9, Debian 10 — scanning only; fixing is not supported |
| SUSE | openSUSE: 10.1 (before EOL), 10.2 (before EOL), 10.3 (before EOL), 11.0 (before EOL), 11.1 (before EOL), 11.2 (before EOL), 11.3 (before EOL), 11.4 (before EOL), 12.1 (before EOL), 12.2 (before EOL), 12.3 (before EOL), 13.1 (before EOL), 13.2 (before EOL), Leap 42.1 (before EOL), Leap 42.2 (before EOL), Leap 42.3 (before EOL), Leap 15.0 (before EOL), Leap 15.1 (before EOL), Leap 15.2 (before EOL), Leap 15.3 (before EOL), Leap 15.4, Leap 15.5. SUSE Linux Enterprise: SLES 6 (before EOL), SLES 10 (before EOL), SLES 10 SP2 (before EOL), SLES 10 SP3 (before EOL), SLES 10 SP4 (before EOL), SLES 11 SP1 (before EOL), SLES 11 SP2 (before EOL), SLES 11 SP3 (before EOL), SLES 11 SP4 (before EOL), SLES 12 (before EOL), SLES 12 SP1 (before EOL), SLES 12 SP2 (before EOL), SLES 12 SP3 (before EOL), SLES 12 SP4 (before EOL), SLES 12 SP5 |
| Kylin | Kylin Advanced Server OS V10 |
End-of-life OS support
After an OS reaches end of life (EOL), Security Center stops scanning, detecting, and fixing Linux Software Vulnerabilities and Windows System Vulnerabilities disclosed after the EOL date.
Scanning and fixing for Web-CMS Vulnerability, Application Vulnerability, Emergency Vulnerability, and other Security Center features are not affected.
| OS version | Official EOL date | Patch support cutoff |
|---|---|---|
| Windows Server 2003 | July 14, 2015 | July 14, 2015 |
| Windows Server 2008 | January 14, 2020 | January 14, 2020 |
| Windows Server 2008 R2 | January 14, 2020 | January 14, 2020 |
| Windows Server 2008 SP2 | January 14, 2020 | January 14, 2020 |
| Windows Server 2012 | October 10, 2023 | October 10, 2023 |
| Windows Server 2012 R2 | October 10, 2023 | October 10, 2023 |
| Ubuntu 12.04 LTS | April 28, 2017 | April 28, 2017 |
| Ubuntu 14.04 LTS | April 2019 | April 2019 |
| Ubuntu 16.04 LTS | April 2021 | April 2021 |
| Ubuntu 18.04 LTS | April 2023 | April 2023 |
| CentOS 5 | March 31, 2017 | March 31, 2017 |
| CentOS 6 | November 30, 2020 | November 30, 2020 |
| CentOS 8 | December 31, 2021 | December 31, 2021 |
| Red Hat 5 | March 31, 2017 | March 31, 2017 |
| Red Hat 6 | November 30, 2020 | November 30, 2020 |