Join us at the Alibaba Cloud ACtivate Online Conference on March 5-6 to challenge assumptions, exchange ideas, and explore what is possible through digital transformation.
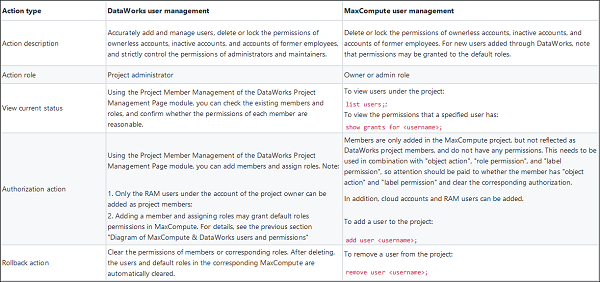
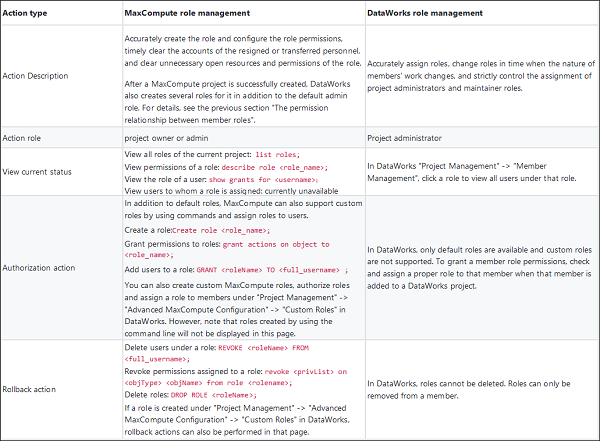
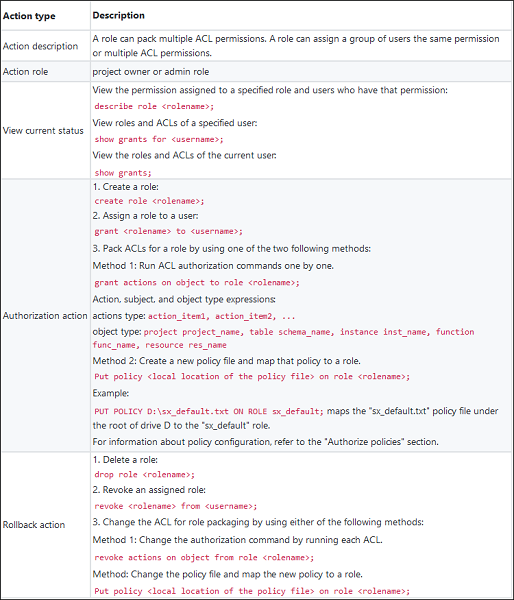
In this guide, we will share the basics of security management for MaxCompute and DataWorks. This guide is aimed at facilitating and assisting the project owner or security administrator of MaxCompute in the daily security operations of projects to ensure data security.
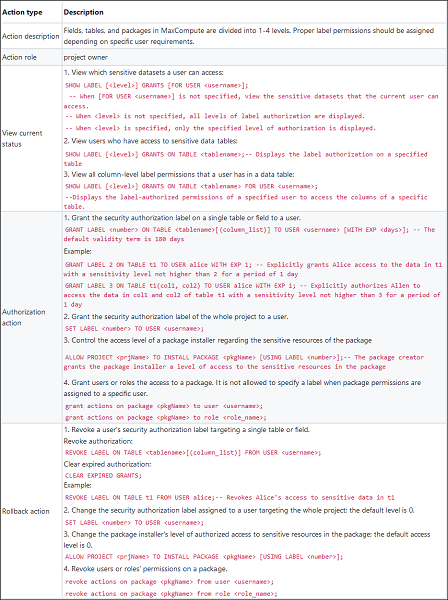
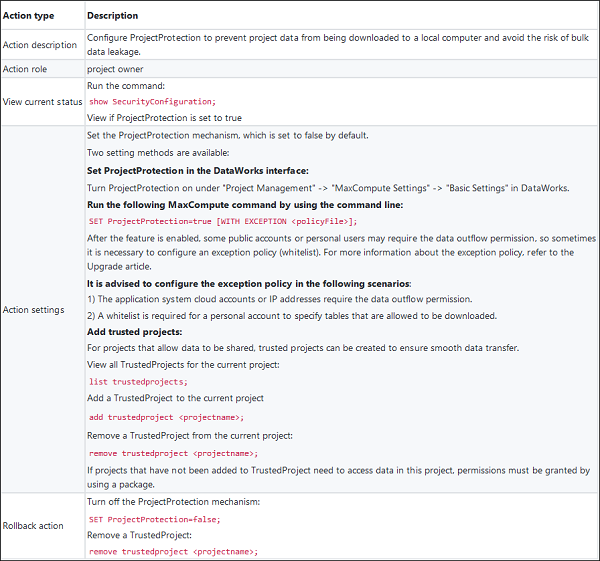
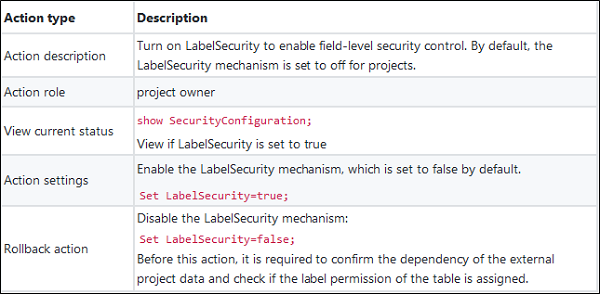
For more information about the action and subject types, refer to the official document.
For more information about the action and subject types, refer to the official document.
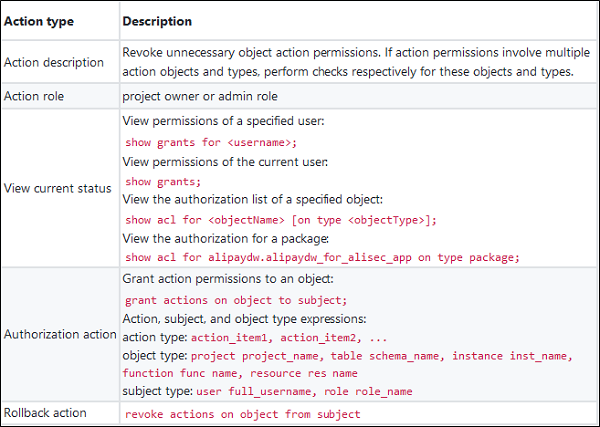
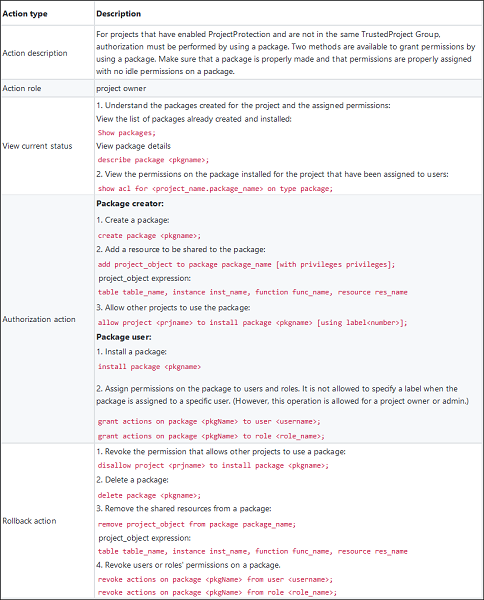
For more information about the action and subject types, refer to the official document.
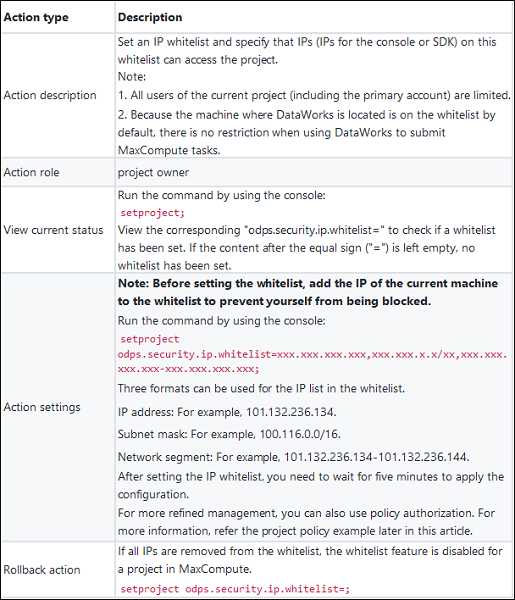
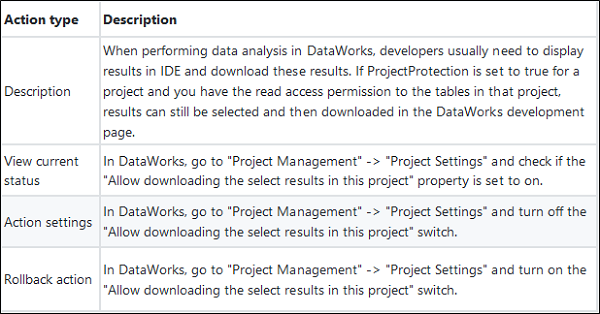
Project data protection is mainly to disallow users to transfer data from the project.
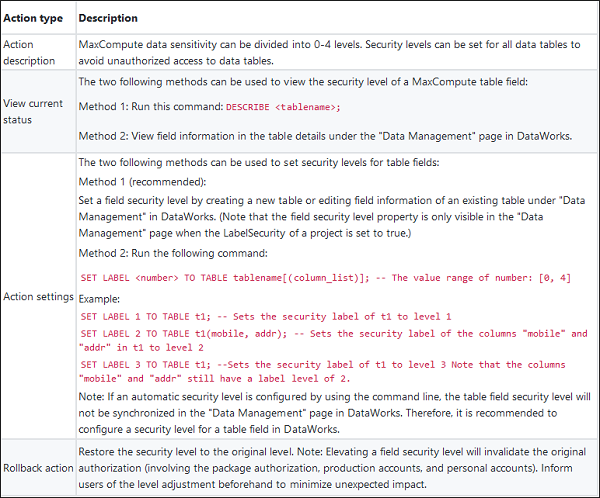
Label-based security (LabelSecurity) is a mandatory access control (MAC) policy at the project level. It allows project administrators to control the user access to column-level sensitive data with improved flexibility.
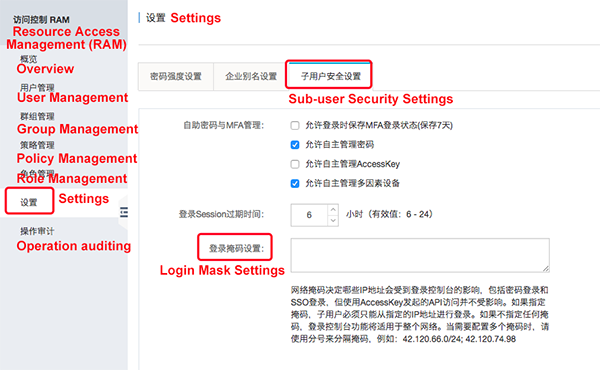
Since other cloud services may be used together with MaxCompute, we should consider how to improve security management in MaxCompute by using other cloud services. A Resource Access Management (RAM) user is required when a project member is added if MaxCompute is used with DataWorks. This section mainly describes how to improve security management on a RAM user.
For MaxCompute user authentication, the preceding "MaxCompute security model" section mentions "two account systems, cloud accounts and RAM accounts, are supported. For RAM accounts, any RAM user of the primary account can be added to a certain project of MaxCompute only by identifying the account system but not the RAM permission system. However, MaxCompute does not consider the permission definition in RAM when verifying the permission of the RAM user." Therefore, we can implement security control simply by using the RAM user login verification.
If you allow a RAM user to change his or her logon password, you should require the user to create a strong logon password and encourage frequent password rotation.
You can create password policies, such as the minimum length, whether non-letter characters are required, and the rotation cycle, for RAM users on the RAM console.

Set a netmask to determine which IP addresses will be influenced by the login console. Sub-users can only log on from the specified IP.
If the employee owner of a RAM user no longer requires original permissions due to change in duties and responsibilities, the original permissions granted to the RAM user should be revoked in a timely manner.
MaxCompute and DataWorks Security Management Guide: Basics (1)
MaxCompute and DataWorks Security Management Guide: Examples

137 posts | 21 followers
FollowAlibaba Cloud MaxCompute - February 15, 2019
Alibaba Cloud MaxCompute - February 19, 2019
Alibaba Clouder - July 10, 2020
Alibaba Cloud MaxCompute - March 4, 2019
Farah Abdou - October 23, 2024
Alibaba Clouder - September 26, 2019

137 posts | 21 followers
Follow Big Data Consulting for Data Technology Solution
Big Data Consulting for Data Technology Solution
Alibaba Cloud provides big data consulting services to help enterprises leverage advanced data technology.
Learn More MaxCompute
MaxCompute
Conduct large-scale data warehousing with MaxCompute
Learn More Big Data Consulting Services for Retail Solution
Big Data Consulting Services for Retail Solution
Alibaba Cloud experts provide retailers with a lightweight and customized big data consulting service to help you assess your big data maturity and plan your big data journey.
Learn More Data Security Center (Original SDDP)
Data Security Center (Original SDDP)
An all-in-one data security solution that provides various features, such as sensitive data detection, classification, grading, and de-identification, to help you meet compliance requirements specified in General Data Protection Regulation (GDPR) and personal information protection
Learn MoreMore Posts by Alibaba Cloud MaxCompute