Alibaba Cloud have conjured up a sort of "cloak of invisibility" for its users-with next-generation encrypted computing based on Intel's Software Guard Extensions (SGX).
In fact, a few days ago, the global research and advisory firm Gartner published the Hype Cycle for Cloud Security, 2019 report (Gartner, Hype Cycle for Cloud Security, 2019, Jay Heiser, Steve Riley, 23 July 2019), in which confidential computing (or encrypted computing) was included for the first time-thus officially recognizing the capabilities of Alibaba Cloud's cloack of invisibility.
As the first cloud vendor offering encrypted computing services in the Asia Pacific region, Alibaba Cloud was named a Sample Vendor of confidential computing in the article.
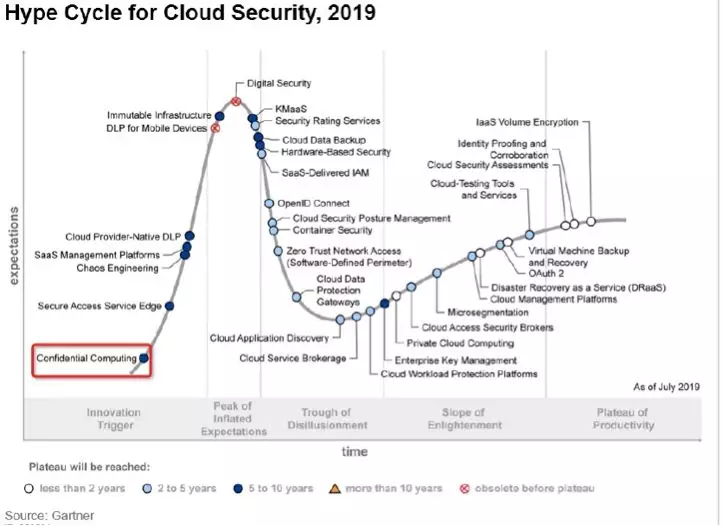
Gartner including confidential computing in its Hype Cycle report this year-and also labelling it as an Innovation Trigger-for the first time shows that confidential computing has begun to play a fundamental role in end-to-end cloud security.
Why can we say that encrypted computing is comparable to the cloak of invisibility?
Well, confidential computing is a cloak of invisibility when it comes to data at runtime. The cloak is owned by all users on the cloud and prevents others from seeing or disturbing a specific user's actions. In a word, encrypted computing is a solution to users' concern about their data at runtime.

As described in the Gartner report, Alibaba Cloud uses the Fortanix runtime encryption solution and reduces unnecessary modifications to applications through the runtime abstraction interface. This in turn minimizes the cloud service provider's implementation dependency on any single piece of hardware. Therefore, other CPU providers also use chips to provide a trusted execution environment similar to an SGX-enabled environment. With these obvious technology advantages, confidential computing is being used in many enterprises and organizations.
What all of this means is that developers working on Alibaba Cloud can use SGX to create a trusted execution environment based on the SGX encrypted computing technology and protect critical code and data in memory. Even system components with higher privileges, including Basic Input/Output Systems (BIOS), virtual underlying layers, OS kernels, and high-privileged processes, do not have access to you critical code and data. In this way, users on the cloud are no longer dependent on cloud platforms and can ensure that their data is running in their own environments to prevent data theft or tampering by having their own trusted environments on the cloud.
As confidential computing is a cutting-edge technology, enterprises need complicated modifications to their applications to "wear the cloak of invisibility". This means only enterprises with professional technicians are ready to embrace this new technology for the time being. However, in an effort to make this high-level protection ability widely applicable, in July 2019, Alibaba Cloud and Intel jointly launched the open-source Graphene Golang solution for protecting cloud-native Golang applications. This solution allows cloud-native applications in Golang on Alibaba Cloud to be protected by the SGX technology without having to make any application modifications and allows more enterprises to benefit from this technology.
Data security has always been a top priority at Alibaba Cloud. Confidential computing is one of the basic security features that Alibaba Cloud enables at the cloud platform level. Currently, Alibaba Cloud provides a comprehensive horizontal data security system that spans from underlying cloud platforms to upper-layer on-cloud environments and integrated vertical data security capabilities including verification, authorization, access control and log auditing. These capabilities help on-cloud users create trusted, controllable and compliant data security systems.
How Algorithms Will Win the Fight Against Gestational Diabetes

2,593 posts | 794 followers
FollowAliware - November 4, 2021
Alibaba Clouder - December 4, 2020
Alibaba Clouder - December 28, 2020
Alibaba Cloud Community - May 6, 2022
Alibaba Cloud ECS - September 10, 2020
Alibaba Cloud Security - October 30, 2020

2,593 posts | 794 followers
Follow Cloud Hardware Security Module (HSM)
Cloud Hardware Security Module (HSM)
Industry-standard hardware security modules (HSMs) deployed on Alibaba Cloud.
Learn More Security Center
Security Center
A unified security management system that identifies, analyzes, and notifies you of security threats in real time
Learn More Security Solution
Security Solution
Alibaba Cloud is committed to safeguarding the cloud security for every business.
Learn More Data Security Center (Original SDDP)
Data Security Center (Original SDDP)
An all-in-one data security solution that provides various features, such as sensitive data detection, classification, grading, and de-identification, to help you meet compliance requirements specified in General Data Protection Regulation (GDPR) and personal information protection
Learn MoreMore Posts by Alibaba Clouder