By Muhuan, Dahu, and Zhuanghuai
The China Academy of Information and Communications Technology believes that Alibaba Cloud Container Service takes the lead in the Chinese market and outperforms other competitors in the international market in the following areas: minimizing attack surfaces, verifying the signatures of binary images, and encrypting data by using the bring-your-own-key (BYOK) model.
Back in 2018, we were already prepared to meet security challenges of the container and cloud-native age. Containers and cloud-native computing have brought security challenges that were new to traditional environments.
High Density and Dynamicity
Each traditional server runs a few applications. With the introduction of containerization, hundreds of applications now can run on a single server. In addition, the automatic recovery of containers may result in their migration between servers at a moment's notice.
Fast and Agile Iteration
Containerized applications developed in the DevOps model are released several times more frequently than traditional applications.
More Risk Sources
In a time of open standards, and as the software industry makes increasing use of community-developed projects, the introduction of non-trusted, open-source third-party software leads to greater security risks. At the same time, containers by nature require a higher level of cloud-native security.
To deal with the unceasing difficulties brought by the preceding challenges, in 2018, the Alibaba Cloud Container Service team put forward the concept of end-to-end enterprise-grade security and developed a three-layer comprehensive, end-to-end cloud-native security architecture.
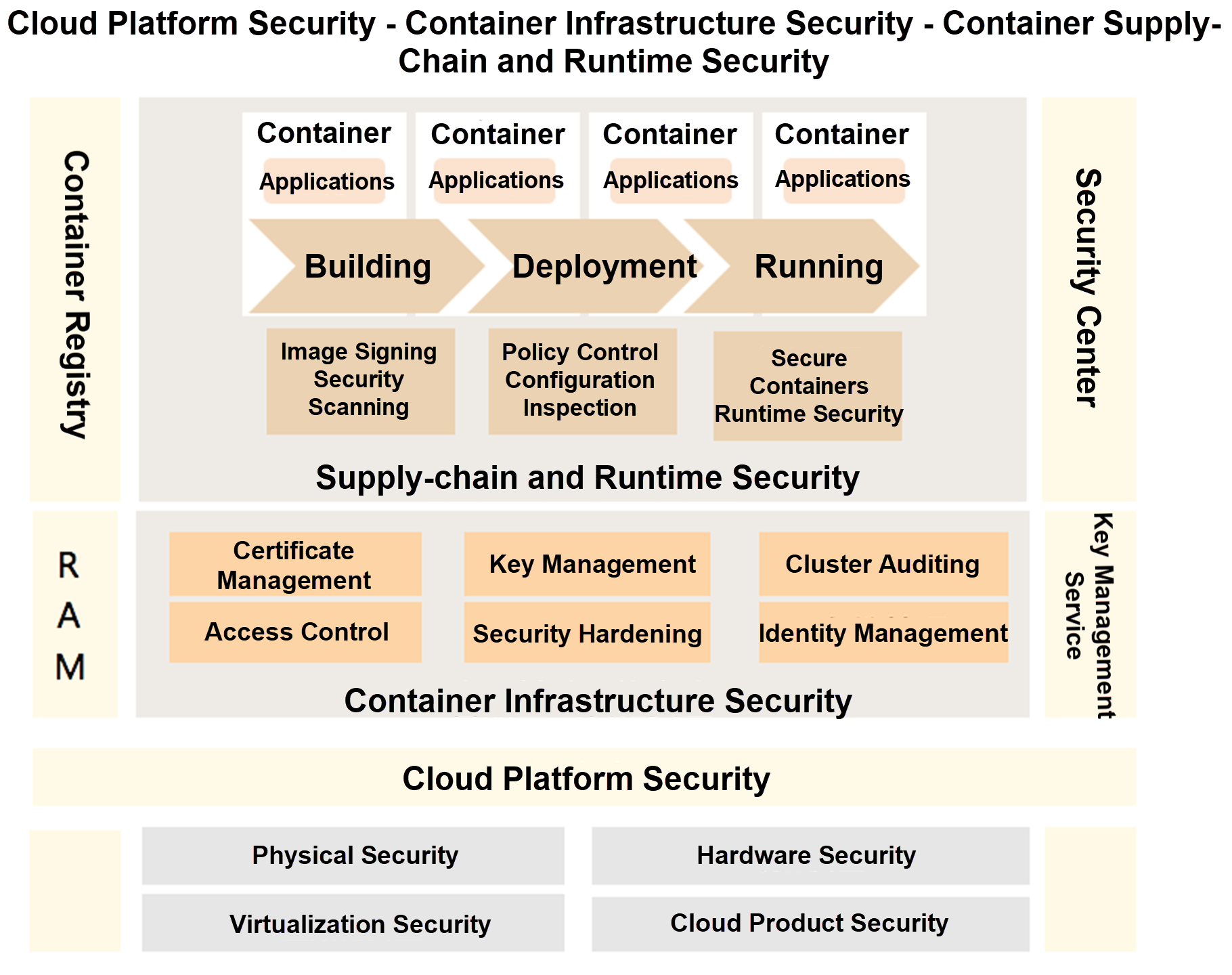
As shown in the preceding figure, the underlying layer of this architecture relies on the physical security, hardware security, virtualization security, and cloud product security capabilities provided by the Alibaba Cloud platform.
The middle layer of the architecture, container infrastructure security, is based on the idea of attack surface minimization. Many important security capabilities work at this layer, including access control, permission management, configuration hardening, and identity management. It also provides necessary elements for user access security, such as credential issuance, certificate and key management, and cluster audit. These elements together form an automated operations and maintenance (O&M) system.
At the top layer are runtime and supply-chain security capabilities that cover the lifecycle of containerized applications from building an application to running it. For example, image signing and security scanning are available in the building phase, and integrated security management capabilities are available in the deployment and runtime phases. These capabilities include runtime policy management, configuration inspection, and runtime security scanning. The architecture also supports sandboxed containers and a trusted execution environment (TEE). These features together provide enterprises with improved isolation and data security for containerized applications.
Container security now faces a host of new challenges. On one hand, critical vulnerabilities frequently occur in open-source projects such as Kubernetes, Helm, and etcd. On the other hand, containerized applications have increasingly short lifecycles and are more deployed on cluster nodes. These facts make it difficult for traditional security scanning on the supply-chain side to fully expose the risks associated with these applications.
To address these new challenges, we have used the three-layer cloud security architecture described in the preceding section with Alibaba Cloud Container Service for Kubernetes and Container Registry to conduct the following successful trials:
With these benefits, we have built the overall security architecture for Alibaba Cloud container services and can guarantee the security of containerized applications throughout their lifecycles.
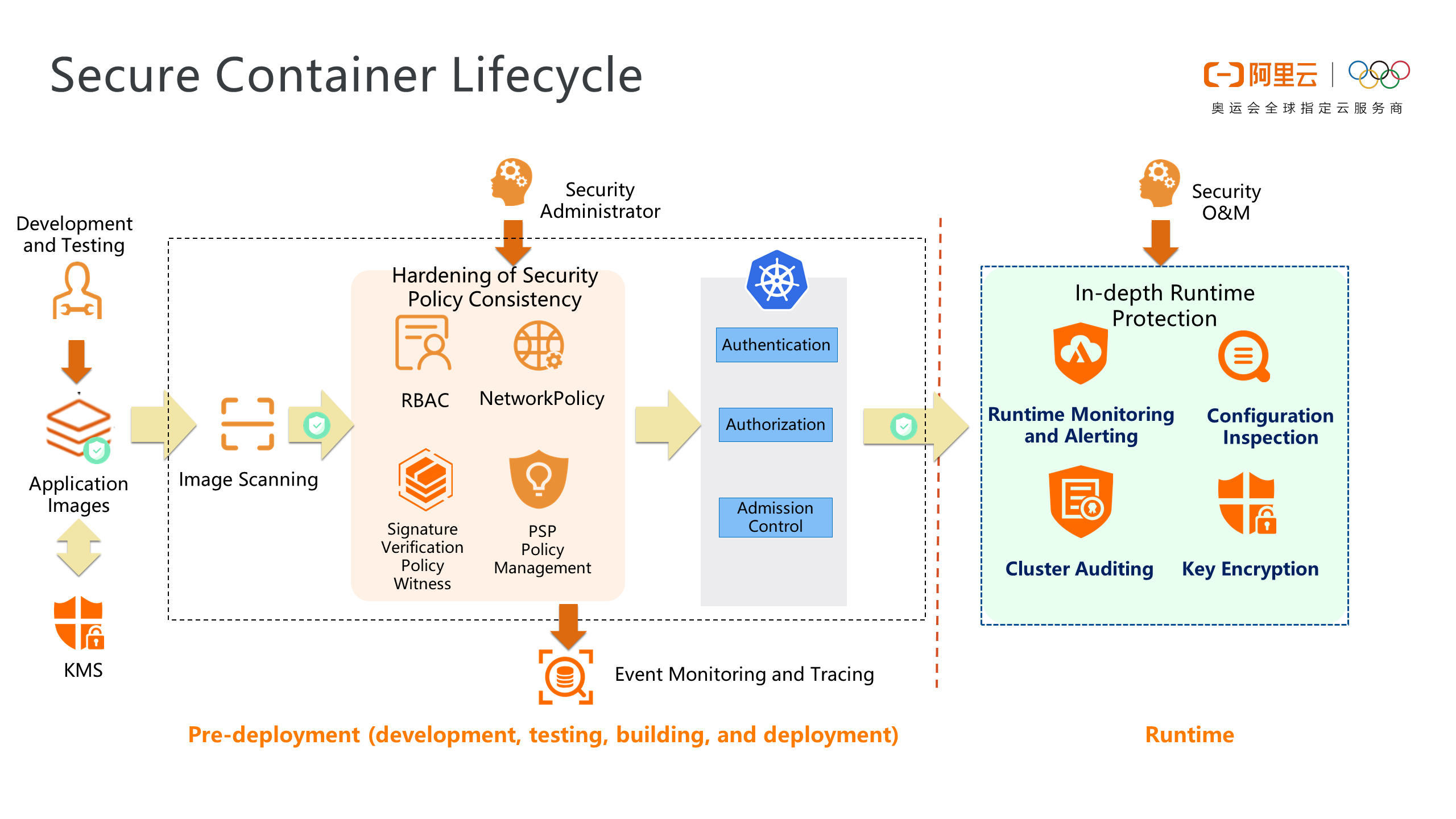
The overall security architecture for Alibaba Cloud container services provides the following benefits for user applications in different phases of their lifecycles:
Development, Testing, and Building Phases
Pre-deployment
With the centralized policy management platform in Alibaba Cloud Container Service, a cluster security administrator can implement customized security governance for application systems in different clusters.
Post-deployment
The Container Service security management center allows users to protect the runtime security of container applications and provides in-depth protection for overall container security.
Since the beginning of containerization in 2011, Alibaba has taken the lead among Chinese enterprises in applying cloud native technology on a large scale in various industries, including e-commerce, finance, and manufacturing.
Over the past decade, Alibaba Cloud has provided security solutions for Container Service customers in the following scenarios:
Security Protection for Corporate IT Assets
An international new-retail giant uses the image signing and scanning features of the Container Registry security software supply chain, resource access management (RAM) roles for RBAC, end-to-end mTLS authentication in Alibaba Cloud Service Mesh, and certificate management and auditing.
Data Operation Security
To implement fine-grained control of east-west application traffic, an international financial bank uses end-to-end data encryption in Container Service for Kubernetes and runtime alert monitoring in Security Center in conjunction with Alibaba Cloud Service Mesh.
Permission Management and Control
To protect sensitive data on containers from disclosure, an international game company uses permission-based isolation of control-plane cloud resources at the pod level, synchronously imports and updates keys from external key management systems, and implements data-plane permission control and key management.
The preceding scenarios are typical to our customers. With our experience dealing with the requirements of these scenarios, Alibaba Cloud has launched the most extensive cloud-native product family, made the most comprehensive open-source contributions to cloud-native computing, developed the largest container clusters, established the largest customer base, and acquired rich practical experience in deploying cloud-native applications.
In May 2020, Gartner released its report "Solution Comparison for the Native Security Capabilities", which was the first comprehensive assessment of the overall security capabilities of the world's top cloud vendors. Alibaba Cloud, the only Asian company made in to the report, ranked second in overall security capabilities, with 11 specific capabilities evaluated as the highest level (High).
The Alibaba Cloud Container Service team believes that these strengths awarded Alibaba Cloud with the certification for advanced trusted cloud security from the China Academy of Information and Communications Technology.
Source: Lingyun Moments (WeChat official account: linuxpk)
The Burgeoning Kubernetes Scheduling System – Part 3: Binpack Scheduling That Supports Batch Jobs
Fluid: An Important Piece for Big Data and AI to Embrace Cloud-Native

229 posts | 34 followers
FollowAlibaba Cloud Community - February 13, 2025
Alibaba Clouder - May 4, 2018
Alibaba Cloud Native Community - March 18, 2024
Alipay Technology - November 6, 2019
Alibaba Container Service - July 24, 2024
Alibaba Cloud Native - November 29, 2023

229 posts | 34 followers
Follow Container Service for Kubernetes
Container Service for Kubernetes
Alibaba Cloud Container Service for Kubernetes is a fully managed cloud container management service that supports native Kubernetes and integrates with other Alibaba Cloud products.
Learn More ACK One
ACK One
Provides a control plane to allow users to manage Kubernetes clusters that run based on different infrastructure resources
Learn More Container Compute Service (ACS)
Container Compute Service (ACS)
A cloud computing service that provides container compute resources that comply with the container specifications of Kubernetes
Learn More Container Registry
Container Registry
A secure image hosting platform providing containerized image lifecycle management
Learn MoreMore Posts by Alibaba Container Service