By Yi Yan
Over the past year, our team spent some time discussing whether the future would belong to low-code platforms or high-code frameworks:
● Low-code platforms: a typical representative is Dify, with a low barrier to entry and high process determinism, but limited flexibility
● High-code frameworks: the core is the ReAct structure, LLM+Prompt+Tool, where the model makes autonomous decisions. The characteristics are strong flexibility and full use of AI’s generalized reasoning capabilities, but hallucination issues are more prominent, and Prompt debugging costs are high
Soon after, Anthropic introduced Skill, becoming a key balance point between the two: while preserving flexibility, it improves Agent determinism and reusability for specific tasks through capability encapsulation and boundary constraints. It has seen broad adoption among enterprise users. Before the Lunar New Year, OpenClaw quickly went viral, and the launch of public Skill marketplaces such as ClawHub and SkillHub has surged like mushrooms after rain. The number of Skills has exceeded tens of thousands, and the ecosystem is still expanding rapidly.
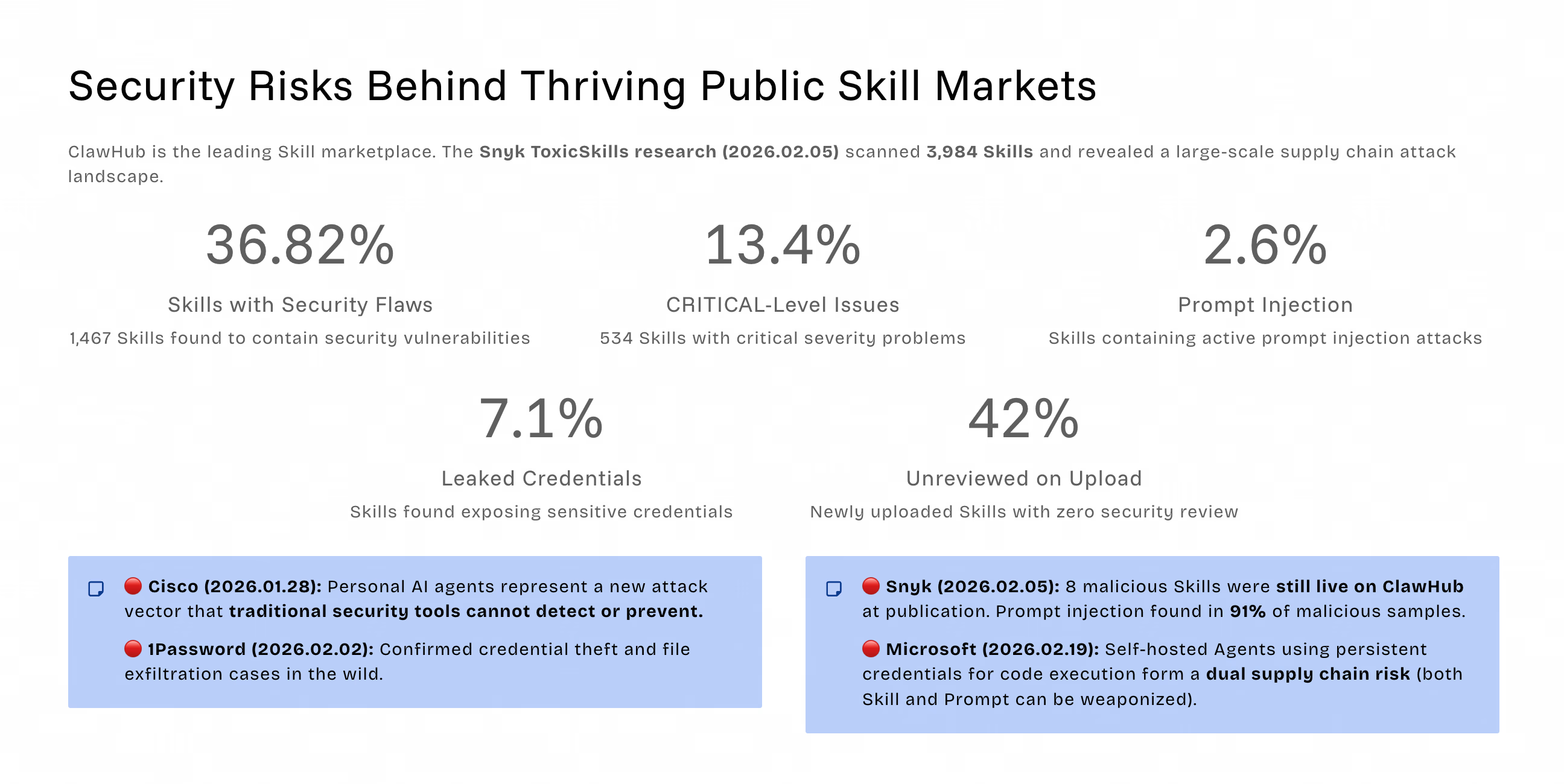
However, behind the prosperity of public Skill marketplaces, various security risks have also been exposed. According to Snyk’s sampling report on 3,984 Skills in ClawHub, 36.82% of Skills contain security flaws, with 13.4% at the CRITICAL level. Credential secret leaks, Prompt injection, and other issues also account for a relatively high proportion. These problems have become major challenges for enterprise Agent deployment.
Based on our communication with both internal teams and external enterprises, we have summarized the key concerns around deploying Skills internally. The main challenges are as follows:
Security challenge: Risks such as malicious code, known vulnerabilities, and sensitive information leakage persist, while effective admission control mechanisms are lacking.
Permission challenge: Who can see, who can use, who can modify, who can publish—responsibility boundaries are unclear, making unauthorized access hard to prevent.
Stability challenge: Version confusion, uncontrollable upgrades, and difficult rollback of issues impact business continuity.
Governance challenge: Missing audit logs, incomplete traceability chains, and lack of compliance evidence chains make it impossible to pass regulatory reviews.
These four categories of issues are coupled with each other and cannot be solved by isolated capabilities. A platform-based governance system is required for coordinated response.
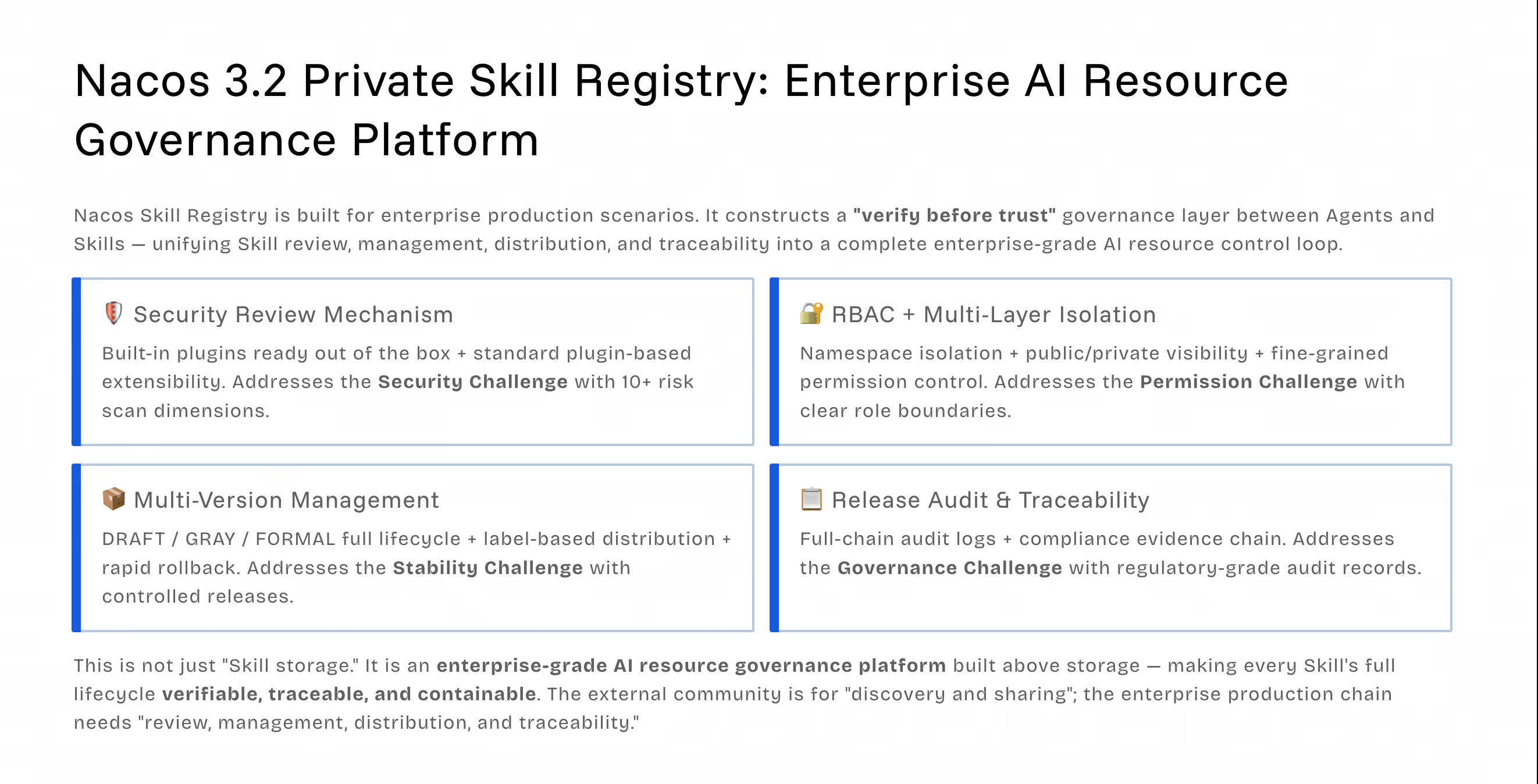
The privatized Skill Registry introduced in Nacos 3.2 is designed for enterprise production scenarios. It builds a governance layer of “trust after verification” between Agents and Skills, unifying Skill review, management, distribution, and traceability under centralized control to form a complete enterprise-grade AI resource control closed loop.
MacOS/Linux
curl -fsSL https://nacos.io/nacos-installer.sh | bashWindows (PowerShell)
iwr -UseBasicParsing https://nacos.io/nacos-installer.ps1 | iexAfter the script runs, the Nacos console will open automatically:
Run nacos-setup --help and nacos-cli --help in the terminal to view more features
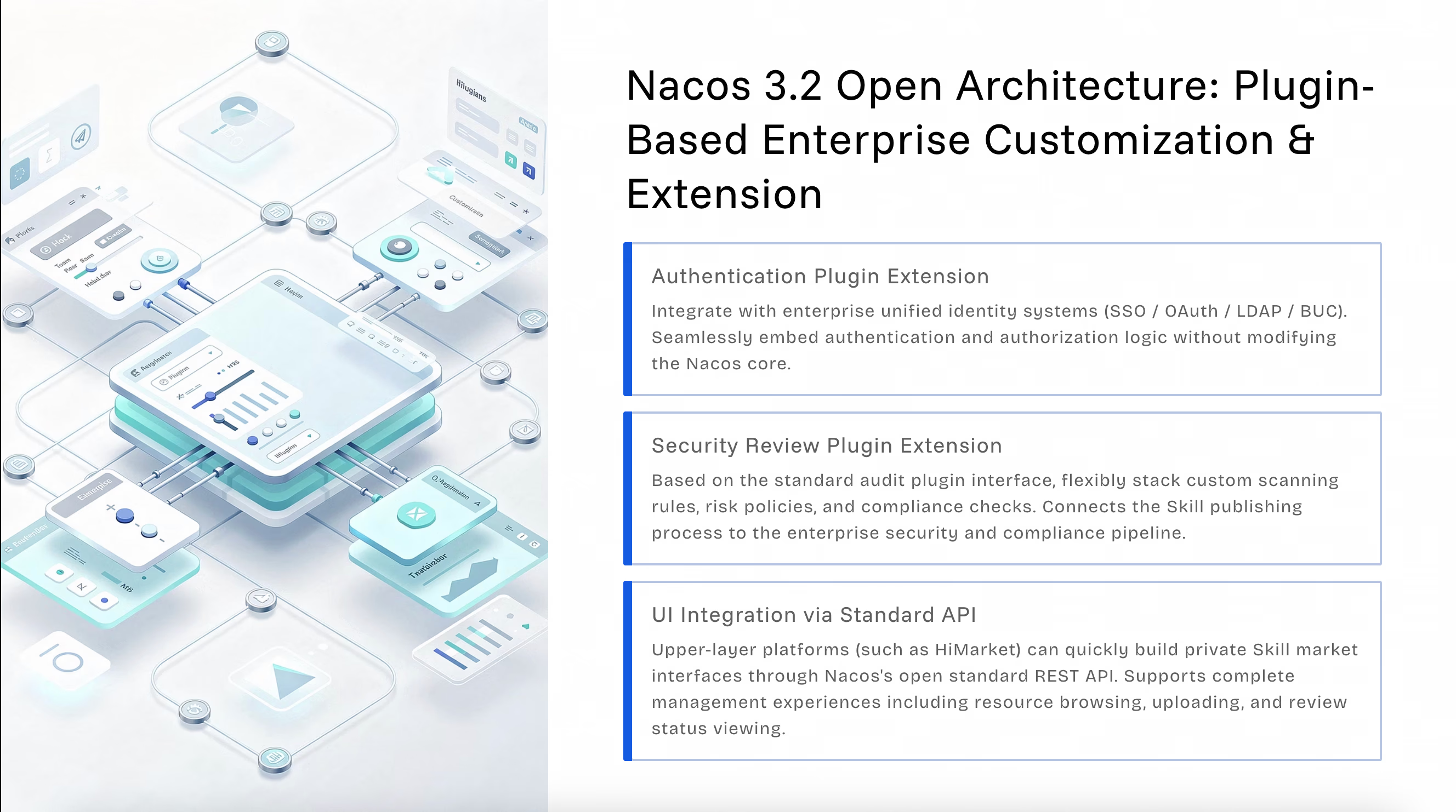
Nacos 3.2 comes with out-of-the-box security review plugins, covering 10+ common risk scans. It also provides standard interfaces for plugin-based extension to meet enterprise custom security policy requirements.
The review process follows the admission principle of “if it doesn’t pass, it won’t be published,” upgrading security requirements from “document conventions” to “strong system constraints” and completely eliminating risks of manual bypass. Before Skills are stored, they must go through an orchestratable, auditable, and upgradable review process, enabling end-to-end control of multi-dimensional scanning, risk grading, and review decision-making.

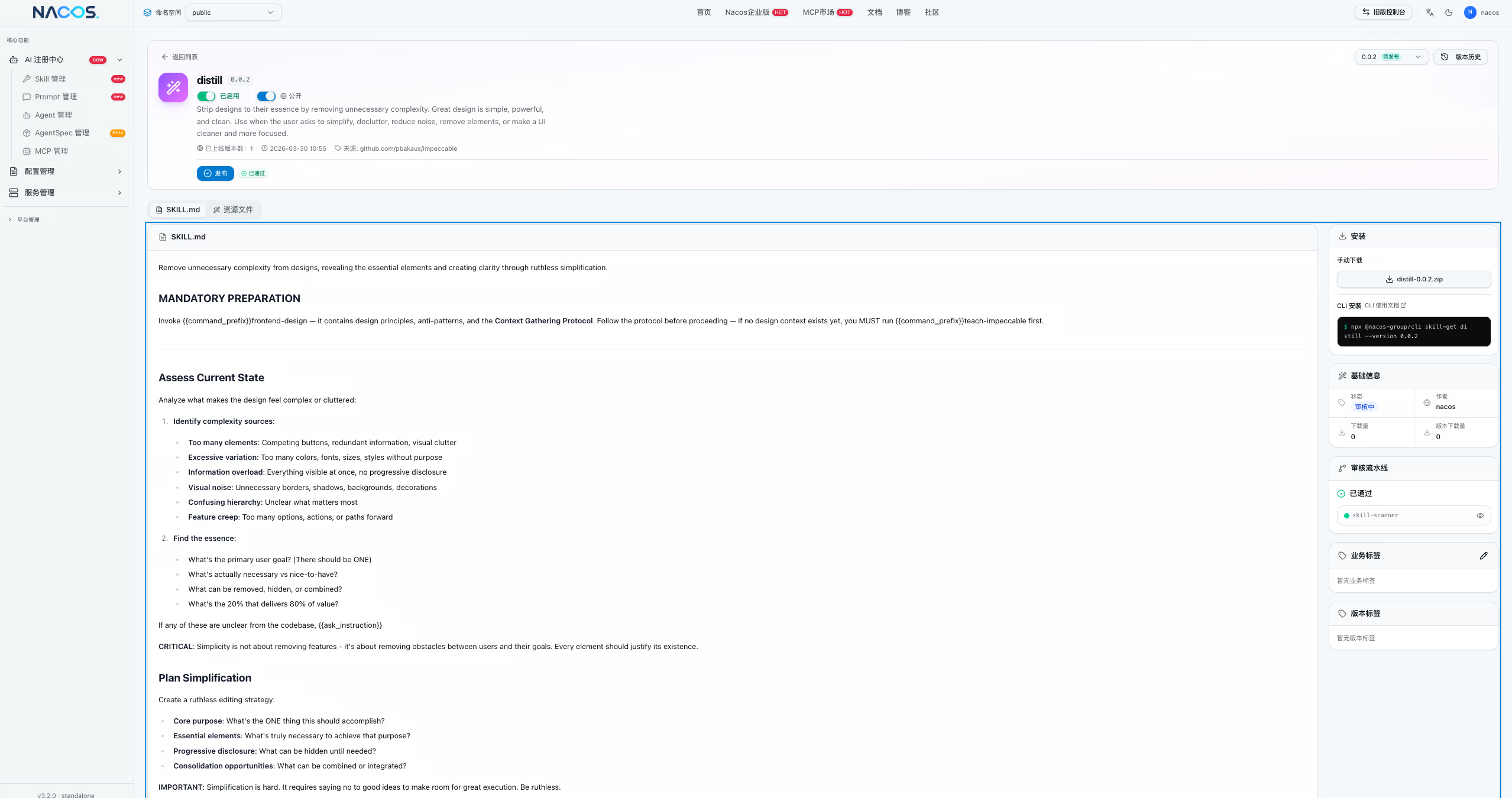
Version lifecycle management: Supports a complete lifecycle including Draft (DRAFT), Under Review, Gray (GRAY), Formal (FORMAL), and Offline. Each stage has a clear status, and versions are immutable.
Label-based canary rollout: Bind versions through labels such as dev/latest/stable to precisely control distribution scope. Supports gradual rollout to reduce new version release risks.
Fast rollback for anomalies: If issues are found during the gray phase, rollback can be completed within seconds by switching label mappings, without republishing, ensuring business stability.
Nacos 3.2 adopts a three-layer boundary design to achieve fine-grained permission control:
RBAC role permissions: Define roles such as publisher, reviewer, and read-only user, with clear responsibility boundaries.
Namespace isolation: Isolates different teams, environments, and tenants to prevent unauthorized access.
Skill-level visibility: Supports public, private, and scoped access settings at the single-Skill level. Who can view, use, modify, and publish is governed by explicit policies and responsibility ownership.
Nacos 3.2 provides comprehensive auditing capabilities covering the full Skill lifecycle:
● Upload records: Who uploaded which version and when; source is traceable
● Review logs: Reviewer, review conclusion, and review time are fully retained
● Release records: Who released, to which Agents, and archived release strategies
● Invocation traceability: Which Agents called which version, enabling evidence-based issue localization
Only by establishing a closed-loop audit can operations, compliance, and governance truly become systematic and meet regulatory requirements.
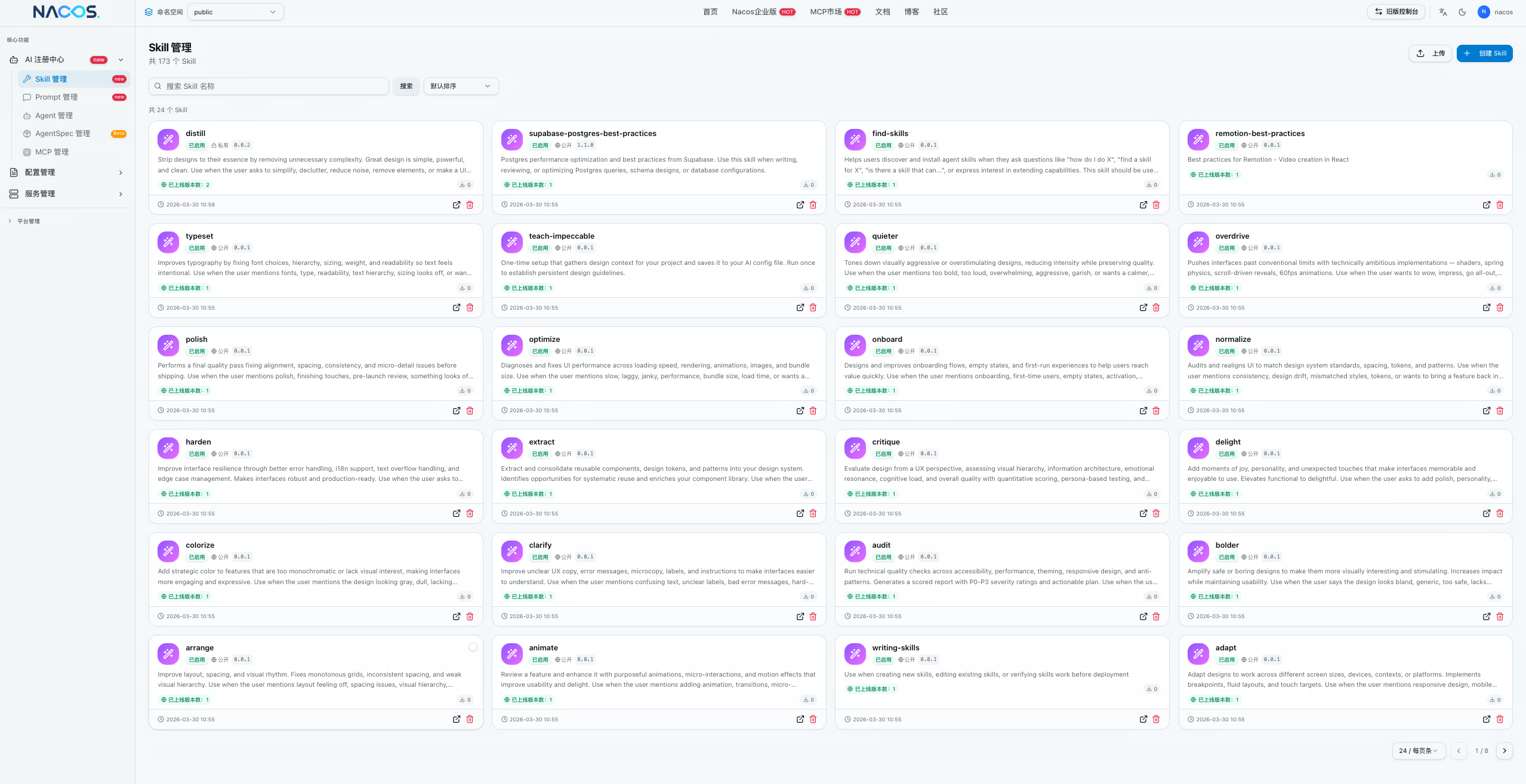
Nacos 3.2 provides multiple flexible ways to access Skills, meeting acquisition and installation needs in different scenarios:
● Agent self-discovery: Nacos provides a guide Skill, and Agents can automatically discover available capabilities through the following command:
curl -s https://download.nacos.io/SKILL.mdAfter execution, a Skill installation guide and list query method will be displayed, helping Agents quickly locate and obtain required capabilities.
● One-click CLI installation: Use the nacos-cli tool for fast Skill download and installation, supporting direct pull from Registry and local deployment.
# List all available Skills
nacos-cli skill-list
# Filter and query by name
nacos-cli skill-list --name mysql-query --page 1 --size 20
# Download a specific Skill to local directory
nacos-cli skill-get mysql-query -o ~/.skillsFor detailed commands, refer to the Nacos CLI Documentation.
● Batch pull via Shell script: Supports connecting to Nacos Registry through the skills.sh script to retrieve Skills in batch, suitable for automated deployment and CI/CD scenarios.
# Configure the Nacos Registry address
export SKILLS_API_URL=http://${nacos.host}:9080
# Use npx to run the skill command for installation
npx skills add mysql-query redis-queryFor implementation details, see GitHub Issue #14770.
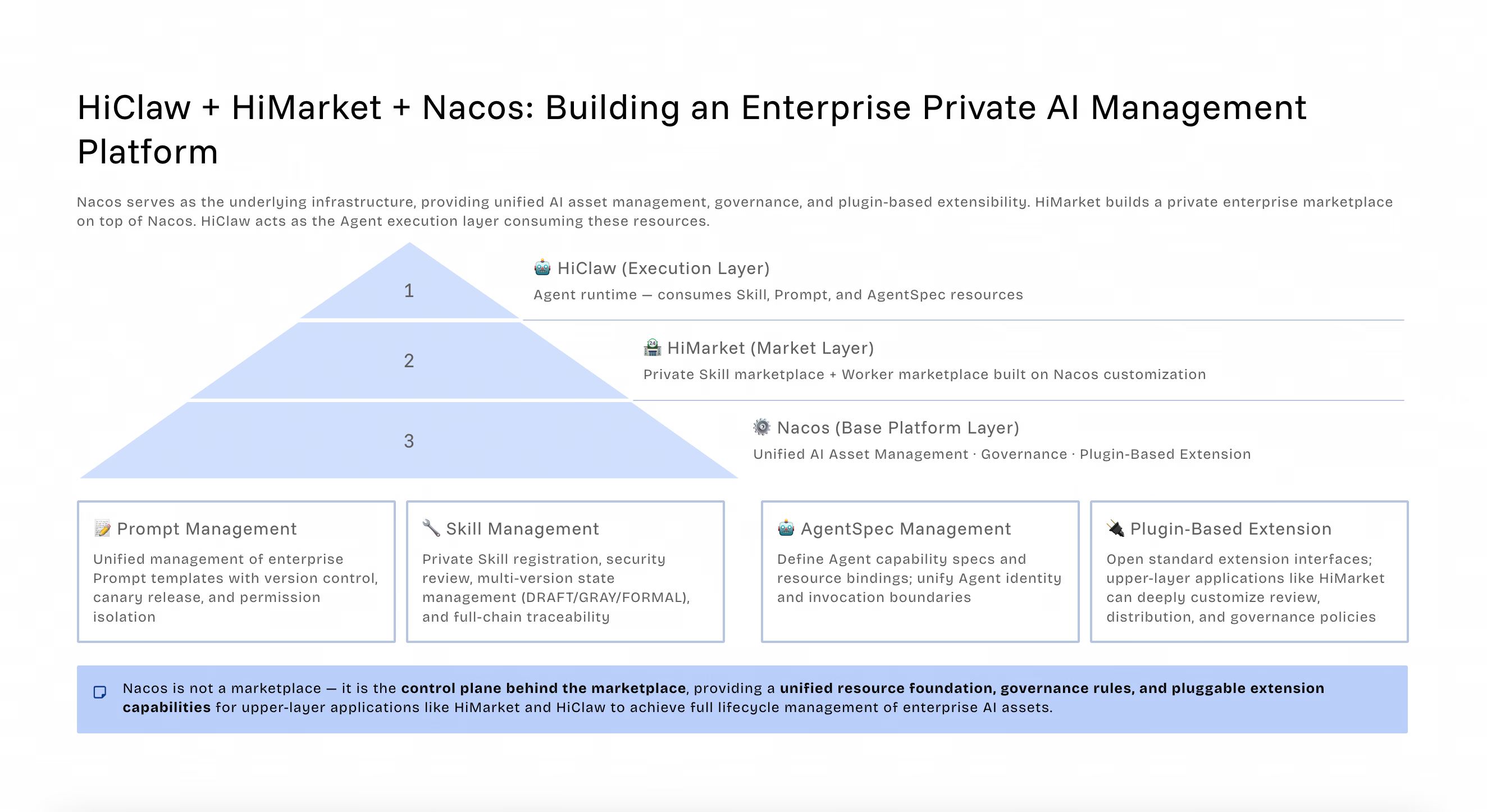
As the underlying infrastructure, Nacos 3.2 forms a complete enterprise private AI management platform ecosystem together with HiClaw (Agent execution layer) and HiMarket (private marketplace layer):
● HiClaw: Agent runtime, consuming Skill, Prompt, and AgentSpec resources
● HiMarket: Private Skill marketplace + Worker marketplace customized based on Nacos
● Nacos: Unified AI resource management (Prompt, Skill, MCP, AgentCard), governance, and plugin-based extension
Last September, we envisioned a configuration-driven Agent network architecture. Now, with Nacos+HiMarket+HiClaw, we have turned this architectural vision into reality.
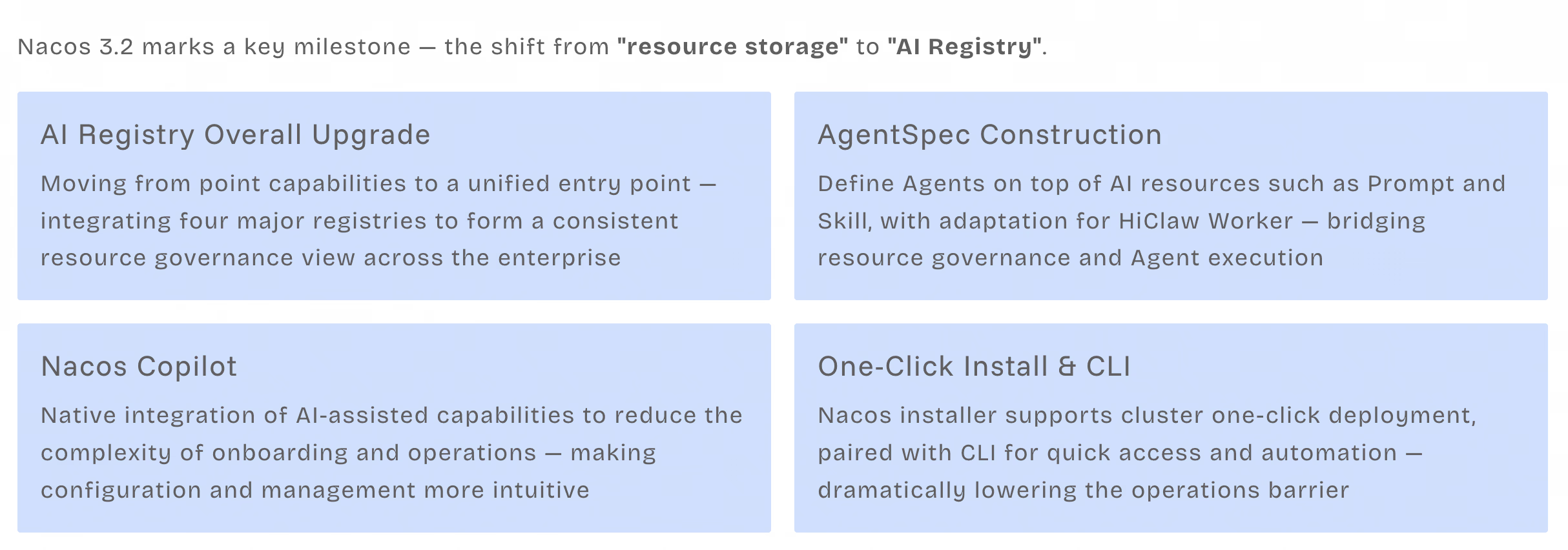
Nacos 3.2 is a starting point, completing the first step in fully embracing the AI era.
We hope that in the future, Nacos will become part of the resource governance infrastructure for enterprises in the AI era, and serve as the collaboration hub for multi-Agent architecture networks.
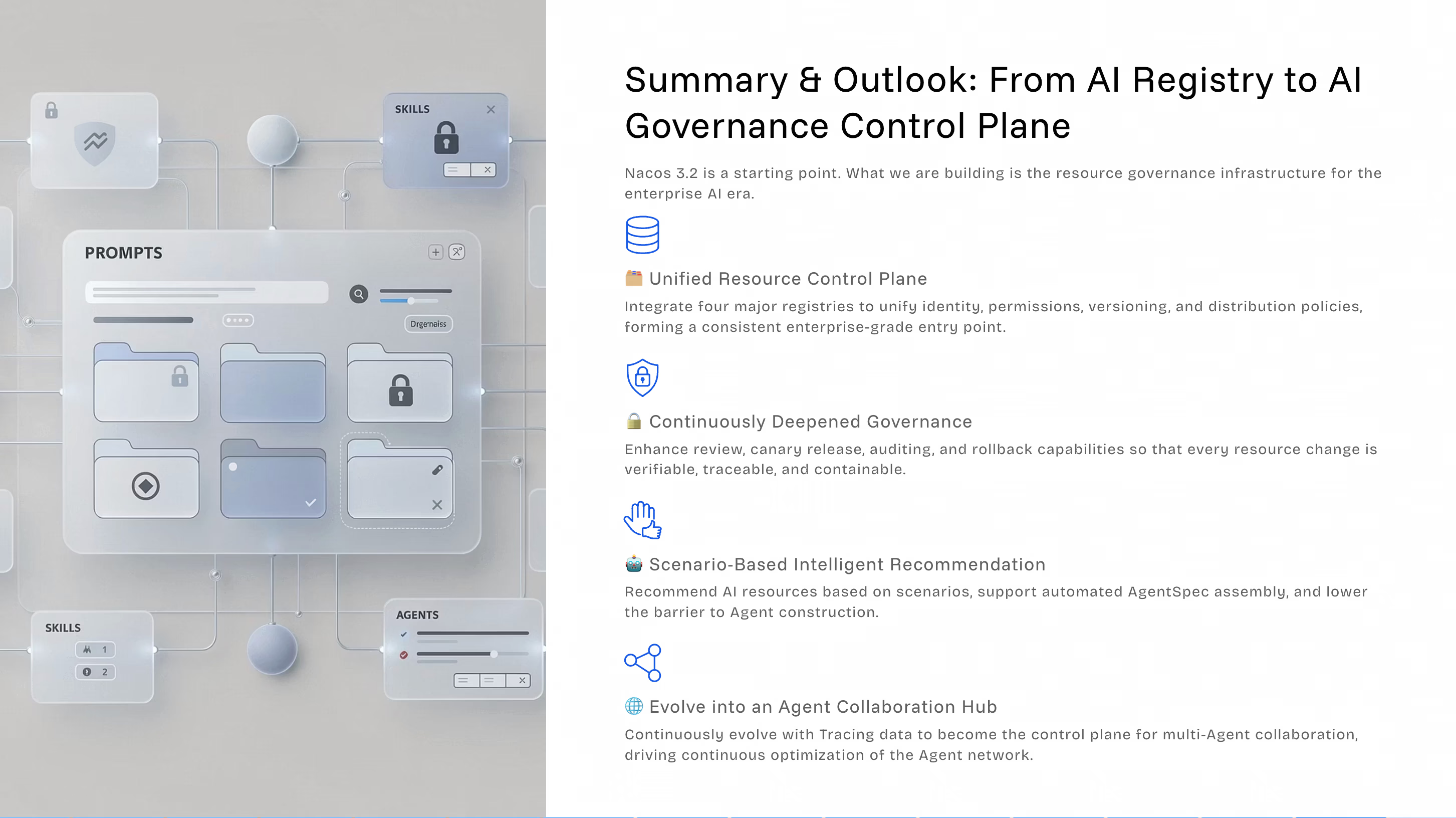
Integrate the four major registries, unify identity, permissions, versioning, and distribution policies, and form a consistent enterprise-grade entry point.
Strengthen review, canary rollout, audit, and rollback capabilities so every resource change is verifiable, traceable, and loss-controllable.
Provide AI resource recommendations based on scenarios, support automated AgentSpec assembly, and lower the barrier to building Agents.
Build Agent Team Spec on top of AgentSpec to form a system of foundational AI resources + single-Agent assembly/orchestration + multi-Agent collaborative network construction. Integrate Agent runtime data based on the OT protocol, upgrade Nacos Copilot for intelligent data analysis, and enable secure, controllable self-evolution of multi-Agent collaboration.
To achieve the above goals, based on community feedback and roadmap planning, AI Registry will continue to evolve in future versions:
AI resource lifecycle management: Introduce an activity detection mechanism to enable hot data startup loading, cold data delayed on-demand loading, and automatic offlining, optimizing resource usage.
Data intelligence layer: Integrate Tracing data based on the OT protocol to build Copilot intelligent analysis capabilities without local storage, enabling observability of AI resource runtime states.
End-to-end audit traceability: Complete full audit logs and end-to-end traceability for AI resource operations to meet enterprise compliance requirements.
Semantic intelligent search: Use vector databases and large models to enable natural language search, automated AgentSpec assembly, and intelligent routing.
Multi-protocol adaptation and open ecosystem: In addition to adapting A2A Protocol 1.0.0, we will explore integration with mainstream Agent communication protocols such as ACP and Matrix, support the evolution of AgentCard field standards, and enable cross-platform Agent interoperability to build an open Agent collaboration ecosystem.
Coding Agent plugin: Evolve Coding Agent capabilities in phases, from Markdown instructions to MCP protocol support, and ultimately provide native remote MCP endpoints to directly operate Nacos resources in tools such as Claude Code and Cursor.
Related Issues: #14801 #14792 #14790 #14789 #14621 #14603
Over the past 8 years, Nacos has become one of the infrastructures of the microservices era and has received broad support from developers in the open-source community. We hope that in the AI era, Nacos will also continue to grow together with everyone. Welcome to scan the QR codes below to contact us.

DingTalk Group

WeChat Group
LoongSuite Python Agent Launches: Observability Into Every AI Agent Action, Zero-code Integration
Revelations from the AI Open-Source Library Poisoning Event and Alibaba Cloud AI Gateway’s Answer

689 posts | 56 followers
FollowAlibaba Cloud Native Community - March 13, 2026
Alibaba Cloud Native Community - February 3, 2026
Alibaba Cloud Native Community - April 3, 2026
Alibaba Cloud Native Community - September 29, 2025
Alibaba Cloud Native Community - September 3, 2025
Alibaba Cloud Native Community - January 22, 2026

689 posts | 56 followers
Follow Container Compute Service (ACS)
Container Compute Service (ACS)
A cloud computing service that provides container compute resources that comply with the container specifications of Kubernetes
Learn More Container Service for Kubernetes
Container Service for Kubernetes
Alibaba Cloud Container Service for Kubernetes is a fully managed cloud container management service that supports native Kubernetes and integrates with other Alibaba Cloud products.
Learn More Microservices Engine (MSE)
Microservices Engine (MSE)
MSE provides a fully managed registration and configuration center, and gateway and microservices governance capabilities.
Learn More DevOps Solution
DevOps Solution
Accelerate software development and delivery by integrating DevOps with the cloud
Learn MoreMore Posts by Alibaba Cloud Native Community