The hub feature of VPN Gateway allows large-scale enterprises to connect multiple offices to each other and to a virtual private cloud (VPC). This topic describes how to use the hub feature of VPN Gateway to connect multiple offices to each other and to a VPC.
Overview of the hub feature
After you create a VPN gateway, the hub feature is automatically enabled. You need to only configure the customer gateway of each office and the IPsec-VPN connection from each office to the cloud. This way, the offices can communicate with each other and with the VPC.
By default, you can establish up to 10 IPsec-VPN connections to each VPN gateway. You can connect 10 offices in different regions to each VPN gateway.
You can use one of the following methods to increase the quota:
Go to the Quota Management page and request a quota increase. For more information, see the Increase quotas section of the "Manage VPN Gateway quotas" topic.
Go to the Quota Center console and request a quota increase. For more information, see the Increase quotas section of the "Manage VPN Gateway quotas" topic.
Sample scenario
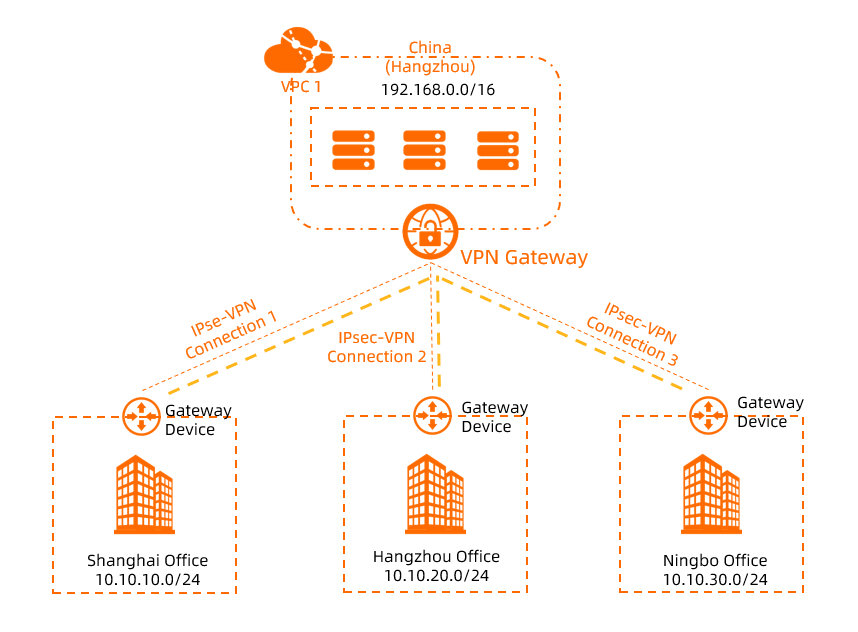
The preceding scenario is used as an example in this topic. A large enterprise has offices in Shanghai, Hangzhou, and Ningbo. The enterprise has deployed a VPC named VPC1 in the China (Hangzhou) region. Services are deployed on Elastic Compute Service (ECS) instances in VPC1. The offices cannot communicate with each other or with VPC1. Due to business development, the enterprise wants to use the hub feature of VPN Gateway to connect the offices to VPC1.
Prerequisites
The public IP addresses of the on-premises gateway devices in the offices are obtained.
VPC1 is created in the China (Hangzhou) region. Services are deployed on the ECS instances in VPC1. For more information, see Create an IPv4 VPC.
The following table describes the CIDR blocks of VPC1 and each office in this example.
NoteYou can plan the CIDR blocks based on your business requirements. Make sure that the CIDR blocks do not overlap with each other.
Site
VPC1
Shanghai office
Hangzhou office
Ningbo office
CIDR block to be connected
192.168.0.0/16
10.10.10.0/24
10.10.20.0/24
10.10.30.0/24
IP address of the ECS instance
192.168.20.121
N/A
N/A
N/A
Public IP address of the on-premises gateway device
N/A
1.XX.XX.1
2.XX.XX.2
3.XX.XX.3
You are aware of the security group rules that apply to the ECS instances in VPC1 and the access control rules that apply to each office. The security group rules and the access control rules allow the offices to communicate with each other and with VPC1. For more information, see View security group rules and Add a security group rule.
Procedure
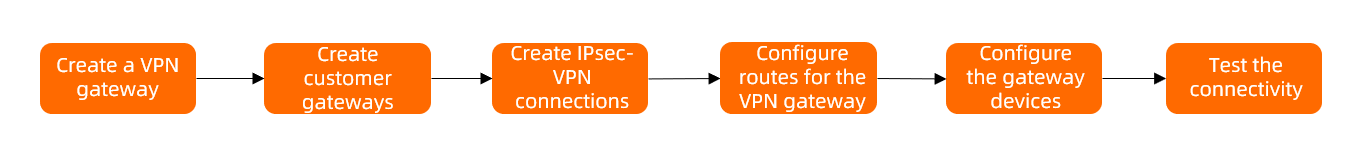
Step 1: Create a VPN gateway
Create a VPN gateway in the region to which VPC1 belongs. The Shanghai office, Hangzhou office, and Ningbo office use the VPN gateway to communicate with each other and with VPC1.
Log on to the VPN Gateway console.
In the top navigation bar, select the region where you want to create the VPN gateway.
In this example, the China (Hangzhou) region is selected.
On the VPN Gateways page, click Create VPN Gateway.
On the buy page, configure the following parameters, click Buy Now, and then complete the payment.
Parameter
Description
Name
Enter a name for the VPN gateway. In this example, VPN Gateway 1 is entered.
Region
Select the region where you want to deploy the VPN gateway. In this example, the China (Hangzhou) region is selected.
Gateway Type
Select a VPN gateway type. In this example, Standard is selected.
Network Type
Select the network type of the VPN gateway. In this example, Public is selected.
Tunnels
The supported tunnel modes are automatically displayed.
VPC
Select the VPC with which you want to associate the VPN gateway. In this example, VPC 1 is selected.
VSwitch
Select a vSwitch from the selected VPC.
If you select Single-tunnel, you need to specify only one vSwitch.
If you select Dual-tunnel, you need to specify two vSwitches.
After the IPsec-VPN feature is enabled, the system creates an elastic network interface (ENI) for each of the two vSwitches as an interface to communicate with the VPC over an IPsec-VPN connection. Each ENI occupies one IP address in the vSwitch.
NoteThe system selects a vSwitch by default. You can change or use the default vSwitch.
After a VPN gateway is created, you cannot modify the vSwitch associated with the VPN gateway. You can view the vSwitch associated with the VPN gateway, the zone to which the vSwitch belongs, and the ENI in the vSwitch on the details page of the VPN gateway.
vSwitch 2
Select another vSwitch from the selected VPC.
Ignore this parameter if you select Single-tunnel.
Maximum Bandwidth
Specify a maximum bandwidth value for the VPN gateway. Unit: Mbit/s.
Traffic
Select a metering method for the VPN gateway. Default value: Pay-by-data-transfer.
For more information, see Billing overview.
IPsec-VPN
Specify whether to enable IPsec-VPN. In this example, Enable is selected.
SSL-VPN
Specify whether to enable SSL-VPN. In this example, Disable is selected.
Duration
Select a billing cycle. Default value: By Hour.
Service-linked Role
Click Create Service-linked Role. Then, the system automatically creates the service-linked role AliyunServiceRoleForVpn.
The VPN gateway assumes this role to access other cloud resources. For more information, see AliyunServiceRoleForVpn.
If Created is displayed, it indicates that the service-linked role is created and you do not need to create it again.
For more information about the parameters, see Create a VPN gateway.
Return to the VPN Gateways page to view the VPN gateway.
After you create a VPN gateway, it is in the Preparing state. After 1 to 5 minutes, the VPN gateway changes to the Normal state. After the VPN gateway changes to the Normal state, the VPN gateway is ready for use.
Step 2: Create a customer gateway for each office
To enable the offices to communicate with each other by using the VPN gateway, you must create a customer gateway for each office.
In the left-side navigation pane, choose .
In the top navigation bar, select the region where you want to create the customer gateways.
NoteThe customer gateways and the VPN gateway to be connected must be deployed in the same region.
On the Customer Gateway page, click Create Customer Gateway.
In the Create Customer Gateway panel, configure the following parameters and click OK.
You must create a customer gateway for each office. For more information, see the following table.
Parameter
Description
Shanghai office
Hangzhou office
Ningbo office
Name
Enter a name for the customer gateway.
Shanghai-customer1
Hangzhou-customer2
Ningbo-customer3
IP Address
Enter the public IP address of the customer gateway.
In this example, 1.XX.XX.1 is entered. This is the public IP address of the on-premises gateway device in the Shanghai office.
In this example, 2.XX.XX.2 is entered. This is the public IP address of the on-premises gateway device in the Hangzhou office.
In this example, 3.XX.XX.3 is entered. This is the public IP address of the on-premises gateway device in the Ningbo office.
For more information about the parameters, see Create a customer gateway.
Step 3: Create an IPsec-VPN connection for each office
Create an IPsec-VPN connection for each office to connect the offices to Alibaba Cloud.
In the left-side navigation pane, choose .
On the IPsec Connections page, click Bind VPN Gateway.
On the Create Ipsec-vpn Connection (VPN) page, configure the parameters and click OK.
The following table describes the configuration of the IPsec-VPN connection for each office.
Parameter
Description
Shanghai office
Hangzhou office
Ningbo office
Name
Enter a name for the IPsec-VPN connection.
IPsec-VPN Connection 1
IPsec-VPN Connection 2
IPsec-VPN Connection 3
Region
Select the region where the VPN gateway to be associated with the IPsec-VPN connection is deployed.
China (Hangzhou)
Bind VPN Gateway
Select the VPN gateway that you created.
VPN Gateway 1
Customer Gateway
Select the customer gateway that you created.
Shanghai-customer1
Hangzhou-customer2
Ningbo-customer3
Routing Mode
Select a routing mode.
Destination Routing Mode
Destination Routing Mode
Protected Data Flows
Local Network
Enter the CIDR block to be connected to the offices. The CIDR block is used in Phase 2 negotiations.
N/A
N/A
192.168.0.0/16
Remote Network
Enter the CIDR block to be connected to the VPC. This CIDR block is used in Phase 2 negotiations.
10.10.30.0/24
Effective Immediately
Specify whether to start connection negotiations immediately.
Yes: starts negotiations after the configuration is complete.
No: starts negotiations when inbound traffic is detected.
Yes
Yes
Yes
Pre-Shared Key
Enter a pre-shared key.
If you do not enter a value, the system generates a random 16-bit string as the pre-shared key.
ImportantMake sure that the on-premises device and the IPsec-VPN connection use the same pre-shared key.
fddsFF123****
TTTddd321****
PPPttt456****
Encryption Configuration
Configure the IKE, IPsec, DPD, and NAT traversal features.
In this example, IKEv1 is used and the other parameters use the default values.
In this example, IKEv1 is used and the other parameters use the default values.
In this example, IKEv1 is used and the other parameters use the default values.
Use the default settings for the other parameters. For more information, see Create and manage IPsec-VPN connections in single-tunnel mode.
To configure VPN gateway routes later, click Cancel in the dialog box that appears.
Step 4: Configure routes for the VPN gateway
After you create the IPsec-VPN connections, you must add the CIDR blocks of the Shanghai and Hangzhou offices to the destination-based route table of the VPN gateway, and advertise the CIDR blocks of the Shanghai, Hangzhou, and Ningbo offices to VPC1.
The routing mode of the IPsec-VPN connection that you created for the Ningbo office is set to Protected Data Flows. After the IPsec-VPN connection is created, the system automatically adds the local route and the peer route to the policy-based route table of the VPN gateway. Therefore, you need to only advertise the CIDR block of the Ningbo office to VPC1 in the policy-based route table. You do not need to add a route.
In the left-side navigation pane, choose .
In the top menu bar, select the region of the VPN gateway.
On the VPN Gateway page, find the VPN gateway that you want to manage and click its ID.
Add and advertise the CIDR blocks of the Shanghai and Hangzhou offices on the Destination-based Route Table tab of the VPN gateway.
On the Destination-based Route Table tab, click Add Route Entry.
In the Add Route Entry panel, configure the following parameters and click OK.
Parameter
Description
Route 1
Route 2
Destination CIDR Block
Enter the destination CIDR block to be connected.
Enter 10.10.10.0/24, the private CIDR block of the Shanghai office.
Enter 10.10.20.0/24, the private CIDR block of the Hangzhou office.
Next Hop Type
Select the next hop type.
Select IPsec-VPN connection.
Select IPsec-VPN connection.
Next Hop
Select the next hop.
In this example, IPsec-VPN Connection 1 is selected.
In this example, IPsec-VPN Connection 2 is selected.
Advertise to VPC
Specify whether to advertise the route to the route table of VPC1, the VPC that is associated with the VPN gateway.
Yes
Yes
Weight
Select a weight for the route. Valid values:
100: specifies a high priority for the route.
0: specifies a low priority for the route.
The default value 100 is used in this example.
The default value 100 is used in this example.
For more information, see Add a destination-based route.
Advertise the CIDR block of the Ningbo office on the Policy-based Route Table tab of the VPN gateway.
On the Policy-based Route Table tab, find the route whose destination CIDR block is the CIDR block of the Ningbo office and click Advertise in the Actions column.
In the Advertise Route message, click OK.
Step 5: Configure the on-premises gateway device
After you configure the VPN gateway, you must configure the on-premises gateway device of each office. You must download the configurations of the on-premises gateway devices on the IPsec Connections page and add the configurations to the on-premises gateway devices. This way, the offices can communicate with each other and with VPC1.
In the left-side navigation pane, choose .
On the IPsec Connections page, find the IPsec-VPN connection that you want to manage and click Generate Peer Configuration in the Actions column.
Download the peer configurations of IPsec-VPN Connection 1, IPsec-VPN Connection 2, and IPsec-VPN Connection 3.
Load the configurations to the on-premises gateway devices. For more information, see Configure an on-premises gateway device.
Add the configuration downloaded from IPsec-VPN Connection 1 to the on-premises gateway device of the Shanghai office.
Add the configuration downloaded from IPsec-VPN Connection 2 to the on-premises gateway device of the Hangzhou office.
Add the configuration downloaded from IPsec-VPN Connection 3 to the on-premises gateway device of the Ningbo office.
Step 6: Test the network connectivity
After you complete the preceding configurations, the Shanghai office, Hangzhou office, Ningbo office, and VPC1 can communicate with each other. The following content describes how to test the network connectivity.
Test the network connectivity between the offices and VPC1.
Log on to the ECS instance that is deployed in VPC1.
For more information about how to log on to an ECS instance, see Methods used to connect to ECS instances.
Run the ping command to ping a client in each of the Shanghai office, Hangzhou office, and Ningbo office.
ping <the IP address of a client>If you can receive echo reply packets from the offices, the offices can communicate with VPC1.
Test the network connectivity among the offices.
Open the CLI on a client in the Shanghai office.
Run the ping command to ping a client in each of the Hangzhou office and the Ningbo office.
ping <the IP address of a client>If you can receive echo reply packets from the offices, the Shanghai office can communicate with the Hangzhou office and the Ningbo office.
Open the CLI on a client in the Hangzhou office.
Run the ping command to ping a client in the Ningbo office.
ping <the IP address of a client>If you can receive echo reply packets from the Ningbo office, the Hangzhou office can communicate with the Ningbo office.