This topic describes how to grant a RAM user the permissions on the Managed Service for OpenTelemetry feature by attaching a custom policy to the RAM user.
Prerequisites
You have a basic knowledge of policy elements, structure, and syntax before you create a custom policy. For more information, see Policy elements.
Make sure that the following system policies are not attached to the RAM user: AliyunTracingAnalysisFull-Access and AliyunTracingAnalysisReadOnlyAccess policies.
ImportantIf you attach a system policy of Managed Service for OpenTelemetry to a RAM user, you cannot attach a custom policy to the RAM user at the same time.
Background information
The system policies provided by Managed Service for OpenTelemetry are coarse-grained. If the system policies cannot meet your requirements, you can create custom policies to implement fine-grained access control. For example, if you need to grant the permissions on a specific application to a RAM user, you must create a custom policy.
Step 1: Create a custom policy
Log on to the RAM console as a RAM user who has administrative rights.
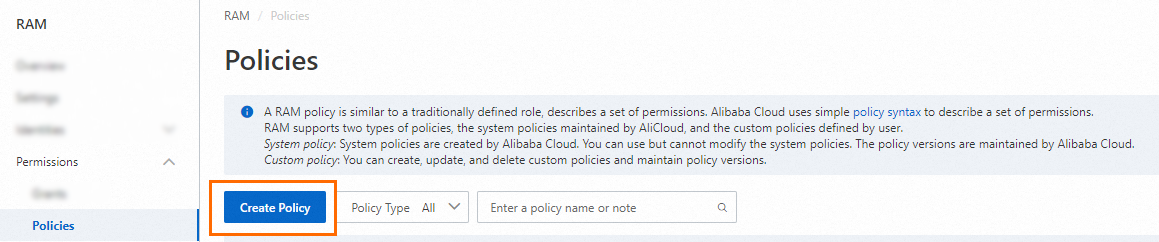
In the left-side navigation pane, choose .
On the Policies page, click Create Policy.
On the Create Policy page, click the JSON tab. Configure a permission policy in the editor.
For more information, see Policy elements.
Example: Create a custom policy that grants the read-only permissions on all applications in the China (Hangzhou) region.
{ "Version": "1", "Statement": [ { "Action": "xtrace:ReadXtraceApp", "Resource": "acs:xtrace:cn-hangzhou:*:xtrace/*", "Effect": "Allow" }, { "Action": "xtrace:Describe*", "Resource": "*", "Effect": "Allow" } ] }Example: Create a custom policy that grants the read-only permissions on the applications whose names start with demo in the China (Hangzhou) region.
{ "Version": "1", "Statement": [ { "Action": "xtrace:ReadXtraceApp", "Resource": "acs:xtrace:cn-hangzhou:*:xtrace/demo*", "Effect": "Allow" }, { "Action": "xtrace:Describe*", "Resource": "*", "Effect": "Allow" } ] }
Click Optional advanced optimize in the upper part. In the Optional advanced optimize message, click Perform to optimize the policy.
The system performs the following operations during the advanced optimization:
Split resources or conditions that are incompatible with actions.
Narrow down resources.
Deduplicate or merge policy statements.
On the Create Policy page, click OK.
In the Create Policy dialog box, configure the Name and Description parameters and click OK.
Step 2: Attach the custom policy to a RAM user
Log on to the RAM console as a RAM administrator.
In the left-side navigation pane, choose .
On the Users page, find the required RAM user, and click Add Permissions in the Actions column.

You can also select multiple RAM users and click Add Permissions in the lower part of the page to grant permissions to the RAM users at a time.
In the Grant Permission panel, grant permissions to the RAM user.
Configure the Resource Scope parameter.
Account: The authorization takes effect on the current Alibaba Cloud account.
ResourceGroup: The authorization takes effect on a specific resource group.
ImportantIf you select Resource Group for the Resource Scope parameter, make sure that the required cloud service supports resource groups. For more information, see Services that work with Resource Group. For more information about how to grant permissions on a resource group, see Use a resource group to grant a RAM user the permissions to manage a specific ECS instance.
Configure the Principal parameter.
The principal is the RAM user to which you want to grant permissions. The current RAM user is automatically selected.
Configure the Policy parameter.
A policy contains a set of permissions. Policies can be classified into system policies and custom policies. You can select multiple policies at a time.
System policies: policies that are created by Alibaba Cloud. You can use but cannot modify these policies. Version updates of the policies are maintained by Alibaba Cloud. For more information, see Services that work with RAM.
NoteThe system automatically identifies high-risk system policies, such as AdministratorAccess and AliyunRAMFullAccess. We recommend that you do not grant unnecessary permissions by attaching high-risk policies.
Custom policies: You can manage and update custom policies based on your business requirements. You can create, update, and delete custom policies. For more information, see Create a custom policy.
Click Grant permissions.
Click Close.
Policy elements
Effect
Specifies whether a statement result is an explicit allow or an explicit deny. Valid values: Allow and Deny.
Action
Action | Permission |
xtrace:Describe | The coarse-grained read-only permissions of Managed Service for OpenTelemetry and coarse-grained read permissions. Only the RAM users with this permission can log on to the Managed Service for OpenTelemetry console. |
xtrace:ReadXtraceApp | The read-only permissions of Managed Service for OpenTelemetry. You can use this permission to view information such as the applications, application details, and details of API calls. You can also use this permission to control RAM permissions on applications and regions. |
xtrace:SaveXtraceAppConfig | The permissions to save application configurations of Managed Service for OpenTelemetry. |
xtrace:DeleteXtraceApp | The permissions to delete applications from Managed Service for OpenTelemetry. |
Resources
Specifies the resources on which the policy takes effect.
Sample statement:
"Resource": [
"acs:xtrace:<regionid>:*:xtrace/<appname>"
]Replace
<regionid>with the specified region ID. If you want to grant the permissions on resources in all regions, replace <regionid> with*.Replace
<appname>with the specified application name. If you want to grant permissions on all applications, replace <appname> with*. If you want to specify applications that have the same name prefix, replace <appname> withName prefix*. Example:k8s*.