Grant Resource Access Management (RAM) users access to Hologres to implement the principle of least privilege — without sharing your Alibaba Cloud account credentials or AccessKey pairs.
Two permission layers
Hologres uses two separate permission layers. Understanding the distinction upfront prevents most authorization errors:
| Layer | What it controls | Managed from |
|---|---|---|
| Console permissions (RAM policies) | Whether a RAM user can view instances, manage billing, and log on to HoloWeb | RAM console |
| Development permissions (instance-level) | Whether a RAM user can connect to an instance for data development | Hologres instance details page |
This topic covers console permissions. To grant development permissions, see Grant a RAM user development permissions on an instance.
Prerequisites
Before you begin, ensure that you have:
An Alibaba Cloud account with RAM administrator permissions
At least one RAM user or RAM user group to grant permissions to
Grant permissions to a RAM user
Log on to the RAM console as a RAM administrator.
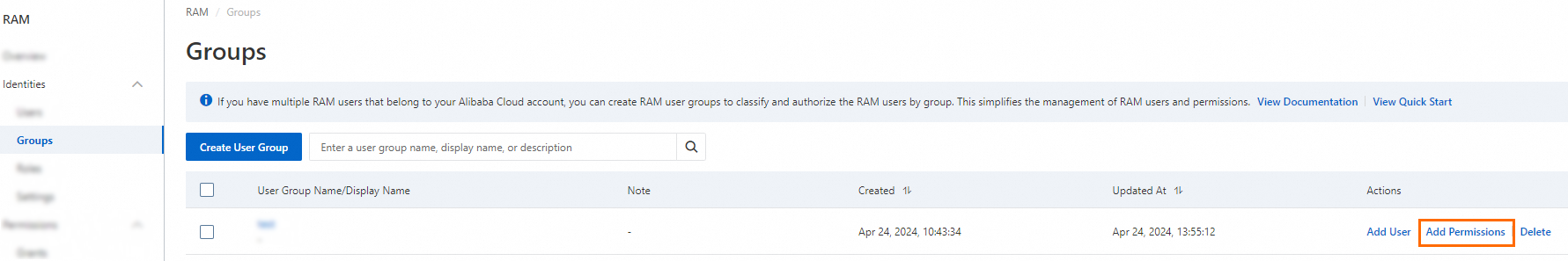
In the left navigation pane, choose Identities > Groups.
On the Groups page, find the RAM user group you want to manage, then click Attach Policy in the Actions column. To grant permissions to multiple groups at once, select multiple RAM user groups and click Attach Policy at the bottom of the page.
In the Add Permissions dialog box, configure the following parameters:
Select a resource scope: > Important: Resource group-level permissions are only available when the corresponding Alibaba Cloud service and resource type support resource groups. See Alibaba Cloud services that support resource groups. For an authorization example, see Use a resource group to control the permissions of a RAM user on specified ECS instances.
Account Level: permissions take effect across the current Alibaba Cloud account.
Resource Group Level: permissions take effect within the specified resource group.
ImportantYou can grant permissions based on a resource group only if the corresponding Alibaba Cloud service and resource type support resource groups. For more information, see Alibaba Cloud services that support resource groups. For an example of resource group authorization, see Use a resource group to control the permissions of a RAM user on specified ECS instances.
Select an authorization entity: the system auto-selects the current RAM user.
Select access policies: select one or more policies. Access policies fall into two types: system policies and custom policies.
HoloWeb cannot belong to a resource group. If permissions are granted at the resource group level, RAM users cannot log on to or use HoloWeb. The access policies below control whether a RAM user can log on to and use HoloWeb — not whether the user can connect to a Hologres instance. For instance-level access, grant development permissions from the instance details page.
Click Confirm Authorization Policy, then click Disable.
System policies
System policies are created and maintained by Alibaba Cloud. You can use them but cannot modify them. See Alibaba Cloud services that support RAM for the full list.
Always include AliyunRAMReadOnlyAccess in any policy configuration to make sure the RAM user can access the console.
The system automatically flags high-risk policies such as AdministratorAccess and AliyunRAMFullAccess. Avoid granting these unless explicitly required.
AliyunHologresFullAccess
Grants full management access to the Hologres service in the console.
After this policy is granted, the RAM user can:
View all instance information in the console (instance list, instance details, and monitoring pages)
Perform billing operations, including purchasing, upgrading, downgrading, renewing, stopping, and deleting instances
Log on to and use HoloWeb
Additional notes:
This policy does not include permissions to use instances. A superuser must create the RAM user in the instance before the user can connect. See FAQ: RAM user cannot log on to a Hologres instance.
When a RAM user purchases an instance, both the RAM user and the Alibaba Cloud account become superusers of that instance.
For instances purchased by the Alibaba Cloud account, RAM users have no instance permissions by default. Grant them separately from the instance details page.
To let the RAM user view all users on the Users page of the console, also grant
AliyunRAMReadOnlyAccess.
AliyunHologresWarehouseFullAccess
Grants full management access to Hologres virtual warehouses.
After this policy is granted, the RAM user can:
Manage virtual warehouses, including creating, deleting, scaling out, scaling in, stopping, and resuming
Configure scheduled scaling
Log on to and use HoloWeb
This policy does not include permissions to use instances. A superuser must create the RAM user in the instance before the user can connect.
AliyunBSSOrderAccess
Grants permission to view, pay for, and cancel orders in User Center (BSS).
After this policy is granted, the RAM user can upgrade, downgrade, and renew instances in the console.
AliyunRAMReadOnlyAccess
Grants read-only access to RAM.
After this policy is granted, the RAM user can view all RAM users and RAM roles under the current Alibaba Cloud account when adding a user on the Users page of HoloWeb.
AliyunHologresReadOnlyAccess
Grants read-only access to Hologres.
After this policy is granted, the RAM user can:
View all instance information in the console (instance list and instance details)
Log on to and use HoloWeb
Restrictions:
No billing operations (purchasing, upgrading, or downgrading instances)
No instance management. The Alibaba Cloud account must grant instance-level permissions separately.
Cannot view RAM users on the User Management page without also having
AliyunRAMReadOnlyAccess.
Custom policies
Custom policies are managed by you. You can create, update, delete, and version them. See Create a custom policy for general instructions. To write policies directly in JSON, see the script mode guide.
Remove all comments from the policy JSON before saving. The policy will fail if comments are present.
The following custom actions are supported for Hologres:
{
"Statement": [
{
"Effect": "Allow",
"Action": "hologram:*",
"Resource": "acs:hologram:*:<AccountID>:instance/*"
},
{
"Effect": "Allow",
"Action": "hologram:*",
"Resource": "acs:hologram:cn-<region>:<AccountID>:instance/*"
},
{
"Effect": "Allow",
"Action": "hologram:DeleteInstance",
"Resource": "acs:hologram:cn-<region>:<AccountID>:instance/*"
},
{
"Effect": "Allow",
"Action": "bss:PayOrder",
"Resource": "acs:hologram:cn-<region>:<AccountID>:instance/*"
},
{
"Effect": "Allow",
"Action": "hologram:GetInstance",
"Resource": "acs:hologram:cn-<region>:<AccountID>:instance/*"
},
{
"Effect": "Allow",
"Action": "hologram:ListInstances",
"Resource": "acs:hologram:cn-<region>:<AccountID>:instance/*"
},
{
"Effect": "Allow",
"Action": "hologram:StopInstance",
"Resource": "acs:hologram:cn-<region>:<AccountID>:instance/*"
},
{
"Effect": "Allow",
"Action": "hologram:ResumeInstance",
"Resource": "acs:hologram:cn-<region>:<AccountID>:instance/*"
},
{
"Effect": "Allow",
"Action": "hologram:UpdateInstanceNetworkType",
"Resource": "acs:hologram:cn-<region>:<AccountID>:instance/*"
},
{
"Effect": "Allow",
"Action": "hologram:HoloWebAccess",
"Resource": "*"
}
],
"Version": "1"
}Replace the placeholders with your actual values:
| Placeholder | Description | Example |
|---|---|---|
<region> | Region name | beijing |
<AccountID> | Alibaba Cloud account ID | 4322xxxxx |
* in instance/* | All instances in the account. Can be replaced with a specific instance ID for most actions (see note below). | hhhgggxxxx |
Example resource string:
acs:hologram:cn-beijing:4322xxxxx:instance/hhhgggxxxxFor the following actions, the * in instance/* cannot be replaced with a specific instance ID — it must remain *:
hologram:*(all operations)hologram:ListInstanceshologram:DeleteInstance— Note: if this permission is not configured, delete operations will fail even though a success message is displayed.hologram:StopInstancehologram:ResumeInstancecms:DescribeMetricListandcms:QueryMetricList(for monitoring alerts)
FAQ: Console permissions {#faq-console}
RAM user cannot view the instance list
Error: You are not authorized to view all instances. Contact your Alibaba Cloud account to go to the RAM console and grant the hologram:ListInstances permission on the "xxx/*" resource to the current user.
The RAM user is missing the hologram:ListInstances permission.
Performed by the Alibaba Cloud account owner: Log on to the RAM console and grant the RAM user the AliyunHologresReadOnlyAccess policy.
RAM user cannot manage instances
Error: RAM user authentication failed.
FAQ: Instance usage permissions {#faq-instance-usage}
RAM user cannot log on to a Hologres instance
Error: role "<role_name>" does not exist
When a Hologres instance is created, only the Alibaba Cloud account and the RAM user who purchased the instance are added as superusers. Other RAM users must be explicitly created as instance users by a superuser before they can connect.
To check who the current superusers are, run: select * from pg_user;
Performed by a superuser: Ask a superuser to do one of the following:
On the Users page of HoloWeb, add the user and assign permissions. See Manage users.
Log on to the instance and run:
create user "<role_name>". See Hologres permission model.
All superusers were accidentally removed
If all superusers of an instance are changed to regular users, most operations — including user management and instance configuration — become unavailable.
Contact Hologres technical support through the official Q&A DingTalk group. See Online support.