In Windows, you can use tools like Task Manager, Resource Monitor, or Wireshark to view network traffic metrics. This topic describes how to identify and resolve issues related to high bandwidth utilization on a Windows ECS instance.
Symptoms
You may experience the following issues when using a Windows ECS instance.
Slow service response times or access timeouts.
When you monitor network metrics for the instance in the ECS console, you observe high network bandwidth utilization. Utilization greater than 80% is generally considered high.
You receive alerts indicating that network bandwidth utilization has exceeded the configured threshold.
Possible causes
High bandwidth utilization may be caused by the following:
Frequent access from normal services consumes high bandwidth.
Malicious activities, such as application-layer CC attacks, DDoS attacks, viruses, or trojans, trigger network traffic.
NoteIn some cases, third-party malware may disguise itself by using the names of operating system processes such as
svchost.exeortcpsvcs.exe, leading to high bandwidth utilization for these processes.Built-in Windows services, such as the Windows Update service, consume high network traffic.
Procedure
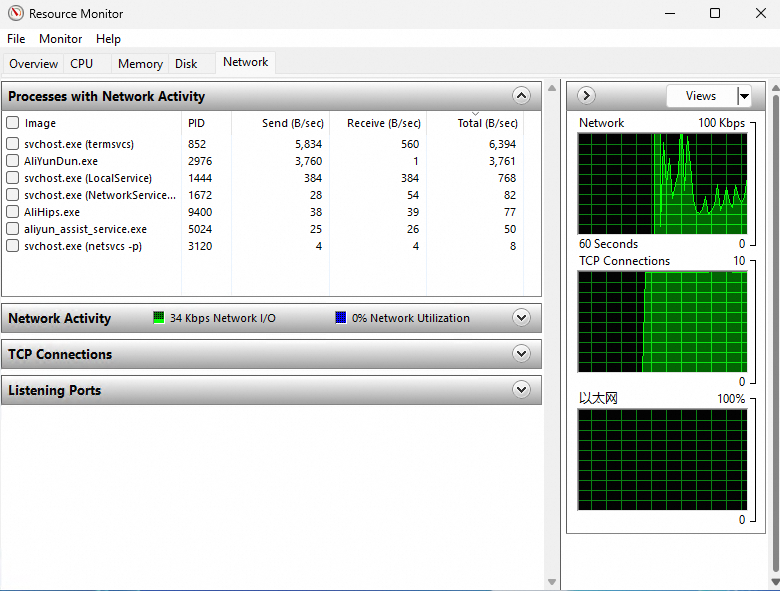
View network metrics in Resource Monitor
Windows provides several tools to identify the cause of high bandwidth utilization, including Task Manager, Resource Monitor, Performance Monitor, and Process Explorer. You can also use Wireshark to capture network packets over a period for in-depth traffic analysis.
In Windows Server 2008 and later, the built-in Resource Monitor is commonly used to monitor bandwidth.
On the taskbar, click Search, enter Resource Monitor, and press Enter.
In the Resource Monitor window, identify the processes that are consuming excessive bandwidth.
 Note
NoteTo view detailed information about a process, use Task Manager. In the Processes tab of Task Manager, find the abnormal process that you identified in Resource Monitor. Right-click the process name and select Properties, Go to details, or Open file location. Use this information to determine whether the process is malicious.
(Optional) Use TCPView for network connections
If Resource Monitor shows no processes with high bandwidth utilization but the instance's overall bandwidth utilization remains high, external services are likely accessing your instance. In this case, use Microsoft's official TCPView tool for further analysis. This tool displays a detailed list of all TCP and UDP network connections on your system, including local and remote addresses and the state of TCP connections.
Download and decompress the TCPView tool.
Visit the official Microsoft website to download the TCPView tool, and then decompress the downloaded package.
Double-click to open the TCPView tool and view network bandwidth details.
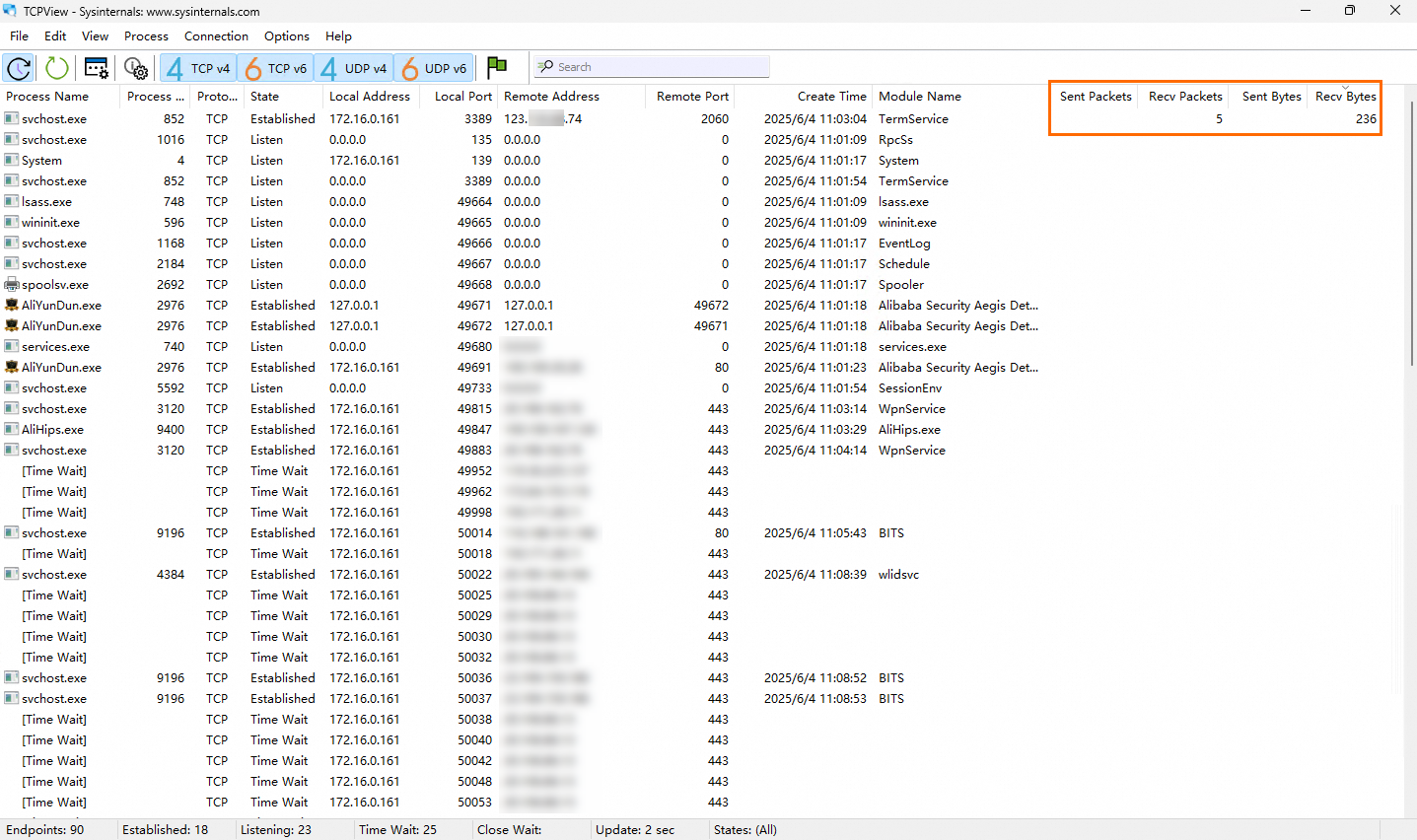
As shown in the figure, the remote address 123.xxx.xxx.74 is transferring data to the instance and consuming the most network bandwidth.
(Optional) Use Wireshark to analyze traffic
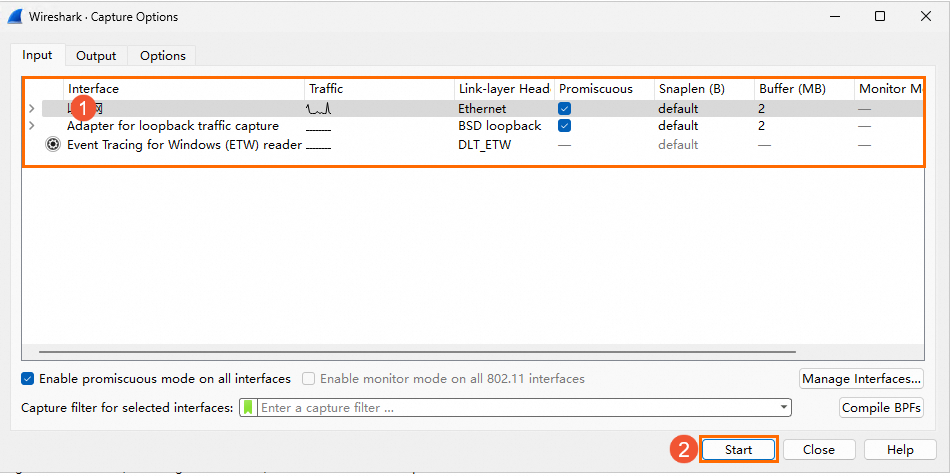
For in-depth analysis of traffic data, you can use Wireshark to capture and analyze network packets.
Install and start the Wireshark tool.
Visit the Wireshark official website, obtain the Wireshark installation package, and then install the Wireshark tool.
Choose Capture> Options.
On the Wireshark Capture Options page, select a network interface for packet capture based on the interface name or IP address and click Start.
In the Wireshark toolbar, choose Statistics>Conversations.
On the Conversations page, you can view all network communications and detailed traffic information for the data link, IP, and TCP layers, including traffic between both endpoints. Capturing packets over time allows you to analyze which connections and ports are consuming the most traffic.
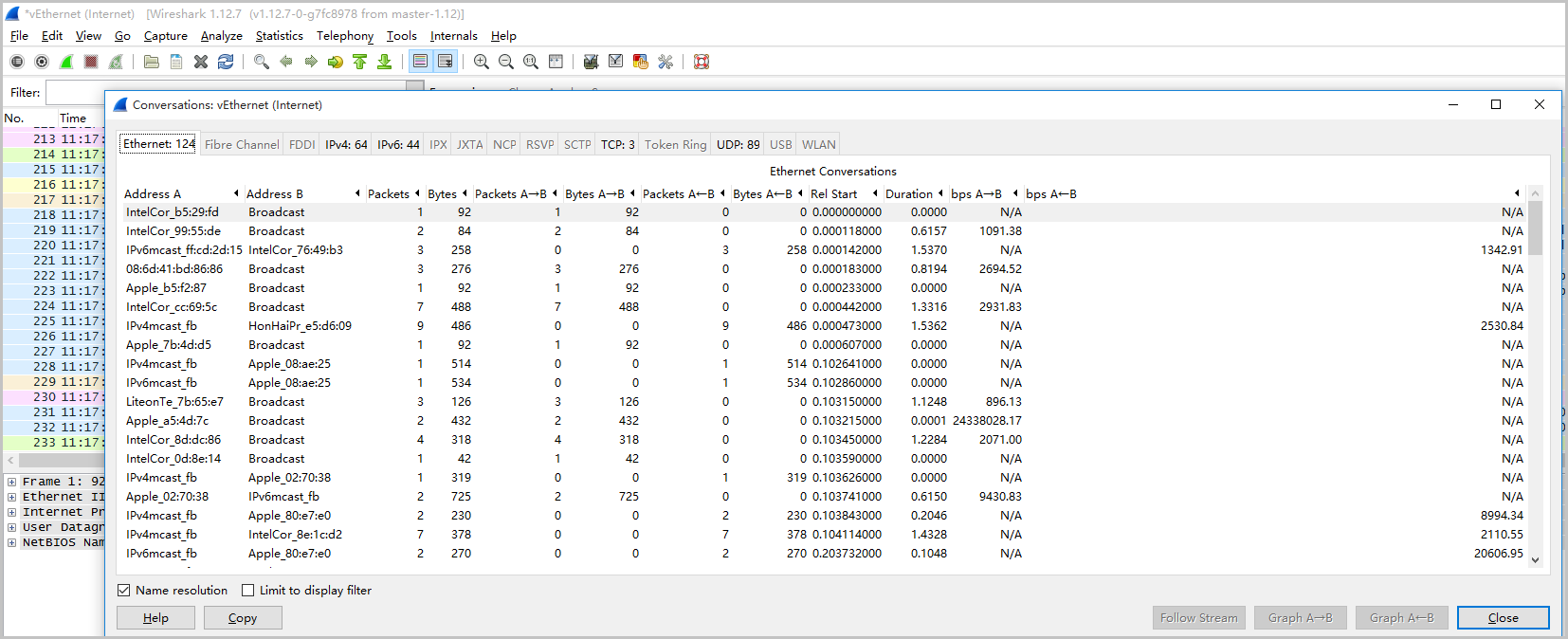
You can further analyze network data by capturing packets. For more information, see Use Wireshark on a Windows instance.
Resolve high network bandwidth
The following table describes common causes of high network bandwidth utilization and their solutions.
Problem description | Cause | Solution |
An abnormal user program or process consumes excessive network resources for an extended period, or an unauthorized IP address maliciously accesses the service, resulting in a high network load. | The program or process is abnormal and consumes excessive network resources at runtime. |
|
A normal user program or process consumes excessive network resources for an extended period, or a specific IP address accesses the service frequently, resulting in a high network load. | The program is a normal business process that consumes excessive network resources at runtime. | High network traffic and CPU usage can occur due to frequent business access or native Windows services, such as updates. If your instance experiences a network performance bottleneck, choose a solution based on your specific situation.
|
A single business program or process occasionally causes a brief and infrequent spike in network resource usage. | This issue indicates that the business application requires optimization to handle high network consumption triggered by specific scenarios, such as large file uploads or downloads. | Optimize your business application. Consider optimizing your code and adjusting application configuration parameters, such as the number of connections, cache settings, and web and database configurations. |
No single program or process is consuming excessive network resources, but the overall network load is high. | The network resources required by the services on the instance exceed its available network bandwidth. | If the instance experiences a network performance bottleneck, you can upgrade the bandwidth. For more information, see Modify the bandwidth configuration. Note If the instance's bandwidth reaches its maximum limit but still cannot meet your business needs, consider separating your applications. Host different services on different instances. For example, you can use RDS to host your database service, which reduces the resource consumption and internal calls on your ECS instance. |
Related documents
For information about how to troubleshoot and resolve high network bandwidth utilization on Linux systems, see Troubleshoot and resolve high network bandwidth utilization on a Linux instance.
If you need to collect network metrics in advance for anomaly analysis, you can use the atop tool. For more information, see Use the atop tool to monitor Linux system metrics.