Use the Static Data Masking feature of Data Security Center (DSC) to mask sensitive data in structured files in TXT, CSV, XLSX, and XLS formats from a source OSS Bucket and save the masked files to a destination OSS Bucket within the same account for secure data sharing.
Overview
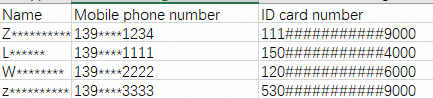
The following table shows an example of desensitized data.
Raw data | Desensitized data | ||||
Name | Mobile phone number | ID card number | Name | Mobile phone number | ID card number |
John Smith | 13900001234 | 111222190002309000 | J*** | 139****1234 | 111###########9000 |
Jane Doe | 13900001111 | 150802202207214000 | J*** | 139****1111 | 150###########4000 |
Richard Roe | 13900002222 | 120105195001066000 | R******* | 139****2222 | 120###########6000 |
To desensitize the data, complete these four steps
Create OSS Buckets and upload a file: Create a source OSS Bucket and a destination OSS Bucket, and then upload a tabular file that contains Sensitive Data to the source OSS Bucket.
Add OSS assets to DSC: Authorize DSC to access the OSS Buckets so that DSC can read from and write to the Buckets.
Add a Data Desensitization Task: Create a Data Desensitization Task, configure the Data Desensitization Algorithms and rules for Sensitive Data fields in the source file, and specify the storage location for the desensitized file.
Run the Data Desensitization Task: Run the task to desensitize the Sensitive Data in the tabular file in the source OSS Bucket and save the desensitized file to the destination OSS Bucket.

Prerequisites
You have purchased a Data Security Center instance and authorized it to access other Alibaba Cloud resources.
The data desensitization feature is available only in the Enterprise Edition of Data Security Center. Therefore, you must purchase the Enterprise Edition. For this example of data desensitization for OSS files, you only need to enable the OSS Data Management service and select the lowest tier for OSS Data Volume. You can disable the Database Management and Value-added Modules services.
You have activated Object Storage Service (OSS).
Step 1: Create OSS buckets and upload a file
1.1 Create source and destination OSS buckets
On the Object Storage Service (OSS) Console, go to the Buckets page and click Create Bucket.
In the Create Bucket panel, configure the required parameters and keep the default settings for other parameters. Then, click Create . This OSS Bucket will be used as the source OSS Bucket. 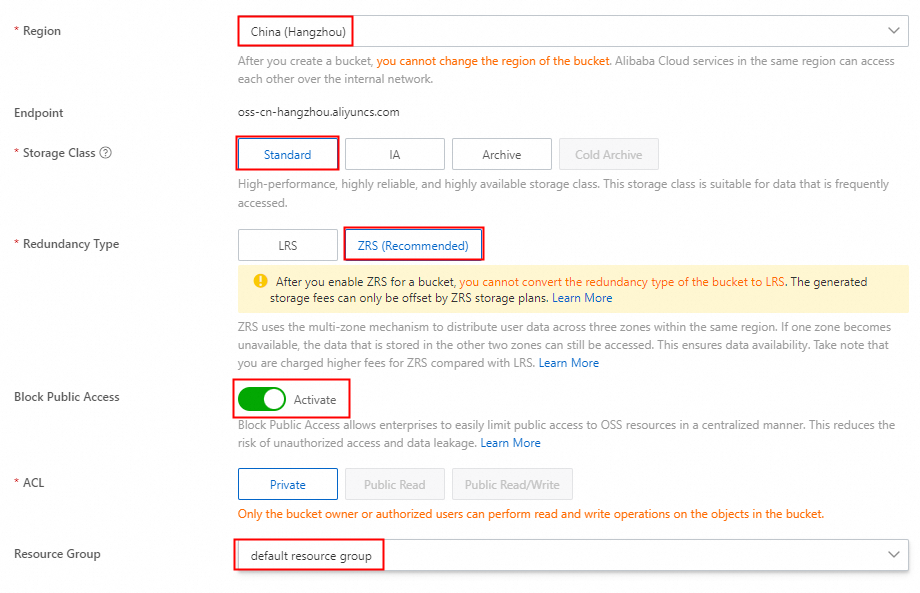
Repeat the preceding steps to create a destination OSS Bucket.
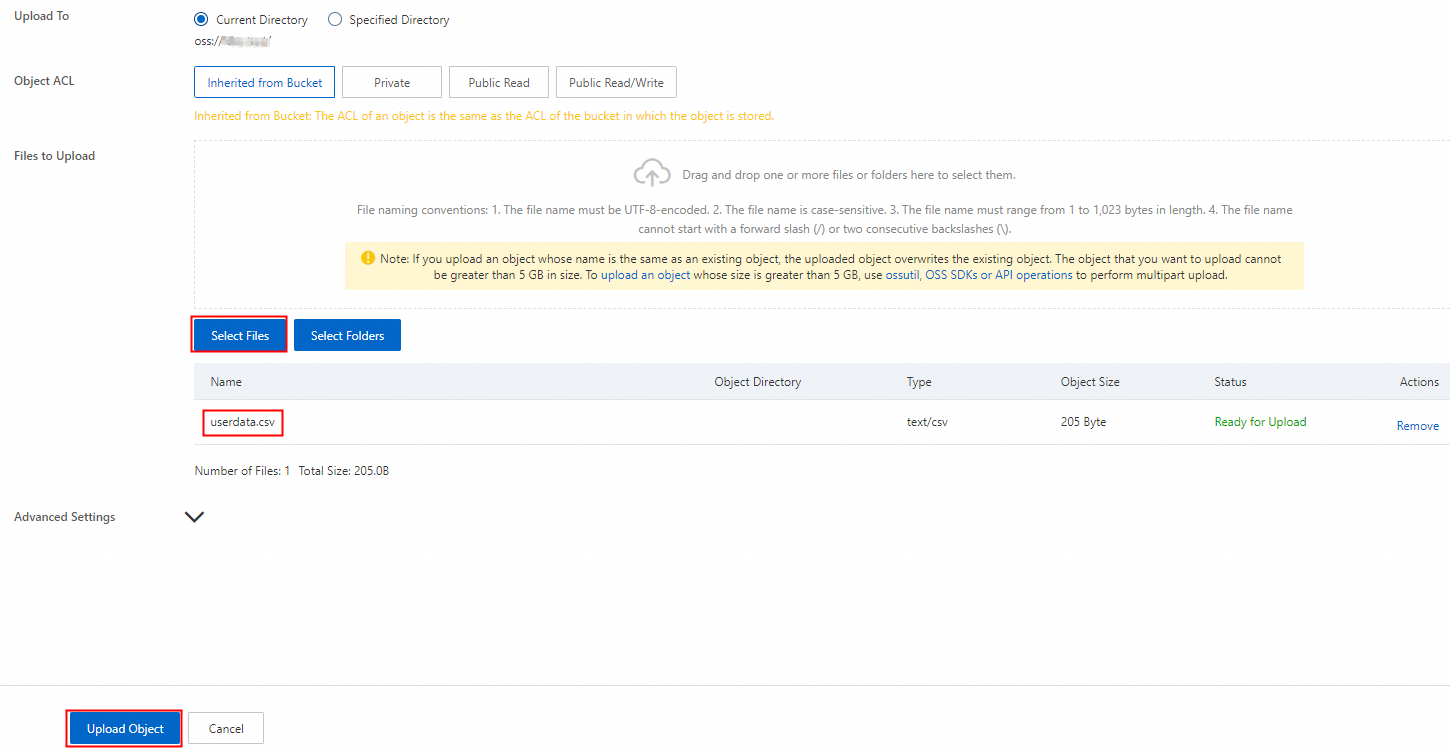
On the OSS Console, go to the Buckets page and click the name of the source OSS Bucket.
On the Objects page, click Upload Object.
Click Select Files, choose a local file, and then click Upload Object. Wait for the file to upload. This topic uses a sample file named userdata.csv that contains Sensitive Data such as names, mobile phone numbers, and ID card numbers.
Step 2: Add OSS assets to DSC
Log on to the Data Security Center console.
In the left-side navigation pane, select Asset Center.
On the Asset Center page, click OSS in the Unstructured Data section on the left, and then click Asset Authorization Management.
On the Asset Authorization Management page, click Asset synchronization.
After the asset synchronization is complete, find the newly created OSS Buckets and click Authorize in the Actions column.
Step 3: Add a data desensitization task
On the Data Desensitization page of the DSC Console, click Add Desensitization Task. Follow the on-screen instructions to configure the Data Desensitization Task.
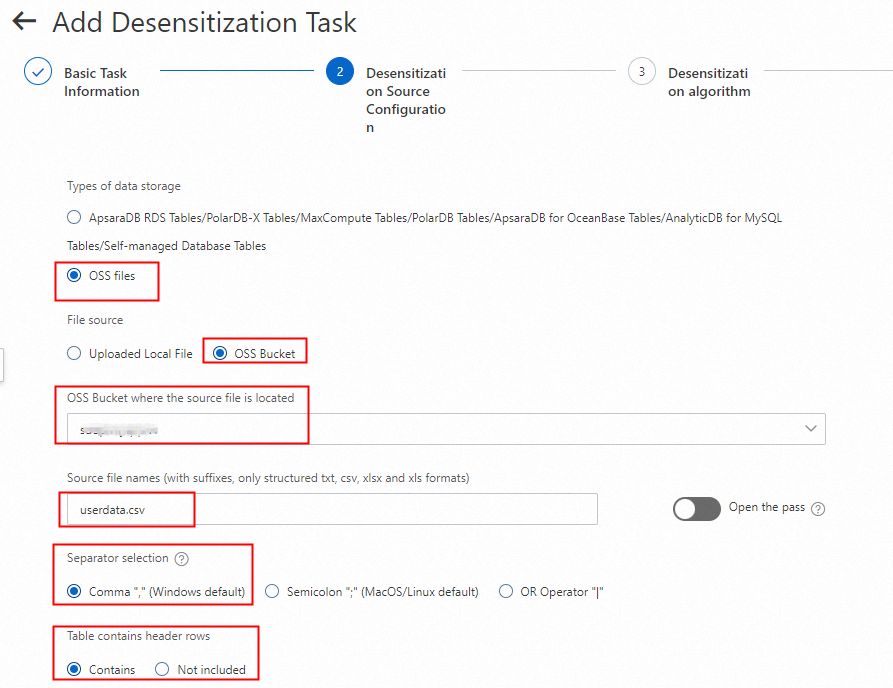
3.1 Configure the source file
Enter a task name and configure the desensitization source as the Sensitive Data file userdata.csv in the source OSS Bucket. For a csv file, you must specify the column delimiter as a comma. The sample file in this topic contains a header row.
3.2 Configure desensitization rules
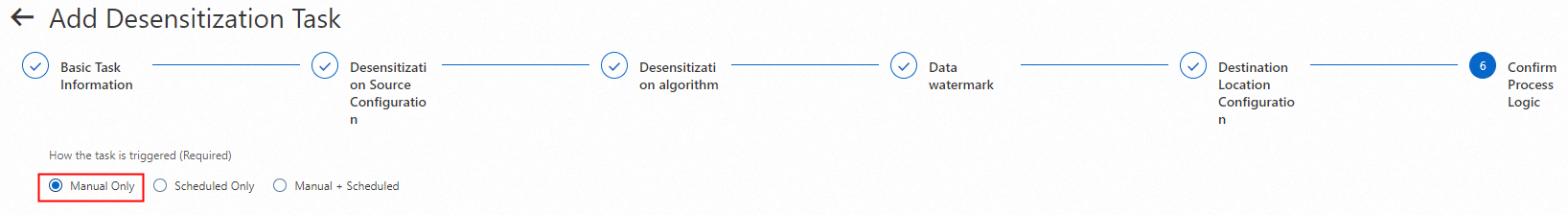
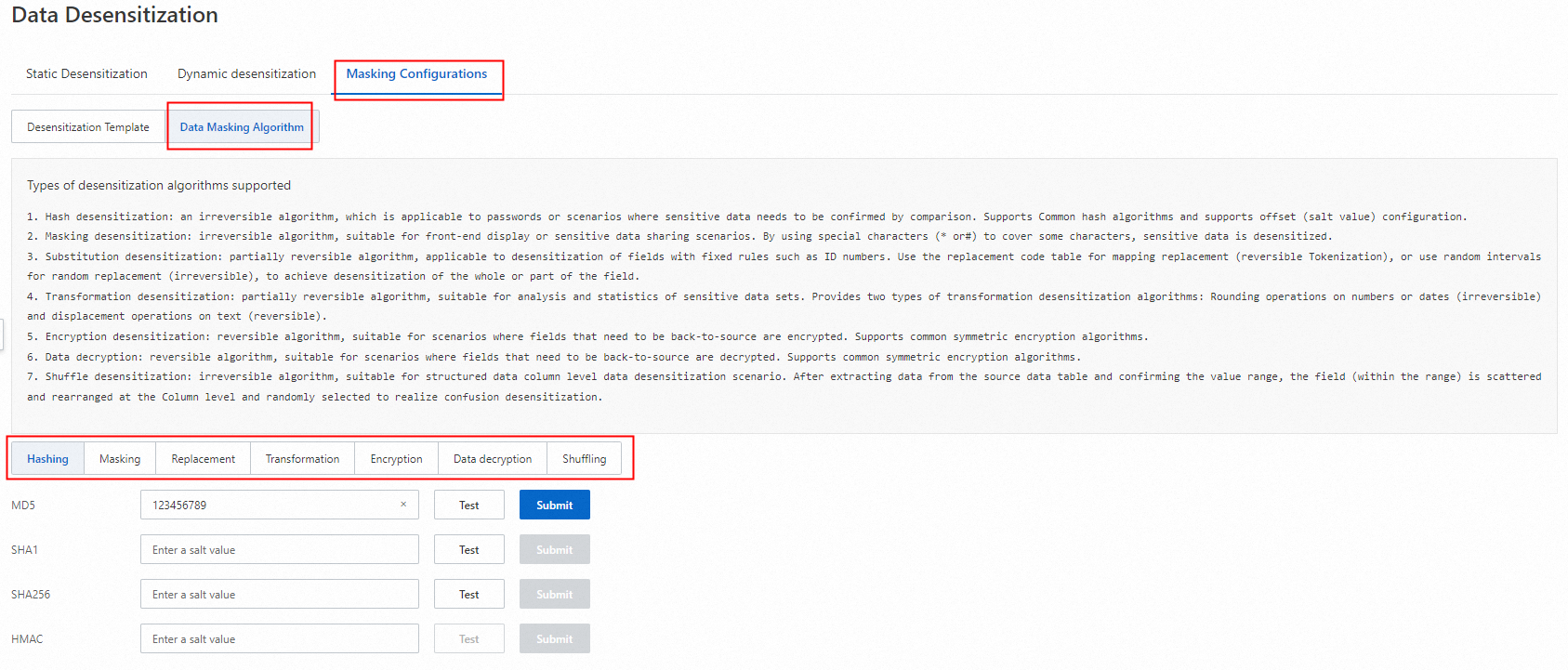
In the Data Desensitization Algorithm step, DSC automatically identifies the header fields from the userdata.csv file. This example uses Masking to desensitize the Name, Mobile phone number, and ID card number fields.
Enable desensitization for each field and select Masking.
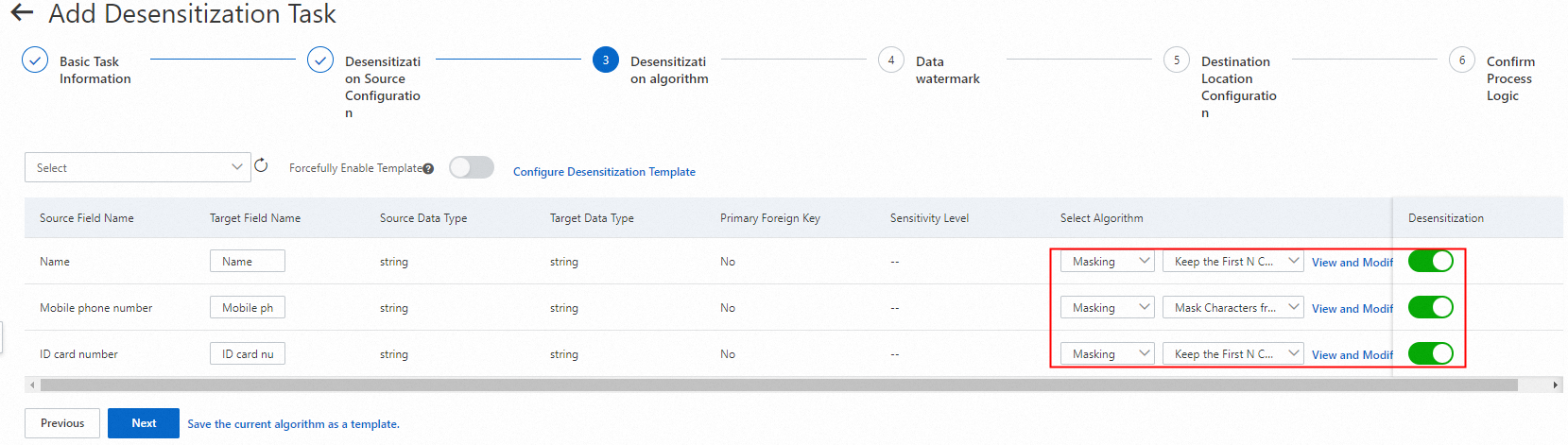
Next to Masking, click View and Modify Parameter, configure the algorithm rules, and then click Save. This example uses the following desensitization rules:
Name: Retain the first character and mask the rest with an asterisk (
*).Mobile phone number: Mask characters 4 through 7 with an asterisk (
*).ID card number: Retain the first 3 and last 4 characters, and mask the rest with a number sign (
#).
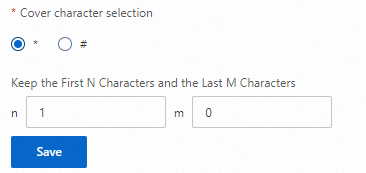
3.3 Configure the storage destination
Watermarks cannot be added to OSS data sources. Configure the desensitized file to be stored in the destination Bucket. In this example, the file is saved as a Result Set (csv,xls,txt format). You can customize the file name, but the file type must be csv, xls, or txt.
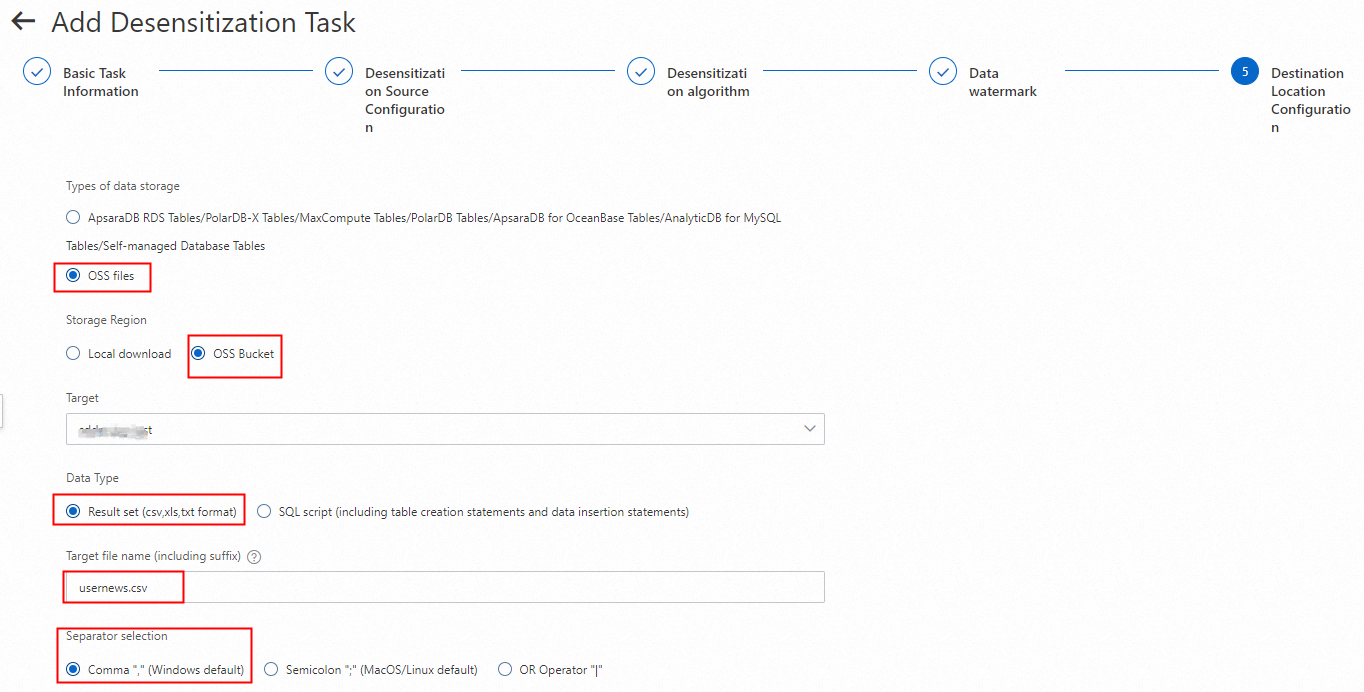
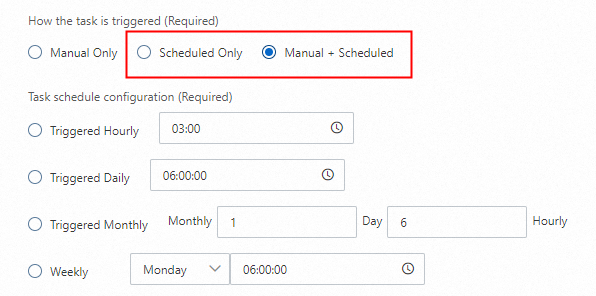
3.4 Configure the task trigger method
For OSS Data Desensitization Tasks, only the How the task is triggered (Required) setting is effective. Other settings are ignored.
Set How the task is triggered (Required) to Manual Only.
Click Submit.
Step 4: Run the data desensitization task
4.1 Run the task
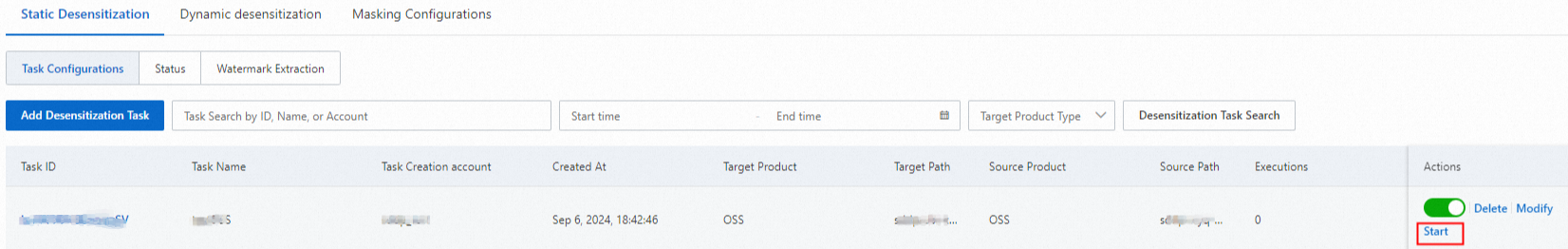
On the Static Desensitization tab, click the Task Configurations tab. Find the Data Desensitization Task you created and click Start in the Actions column to run the task.
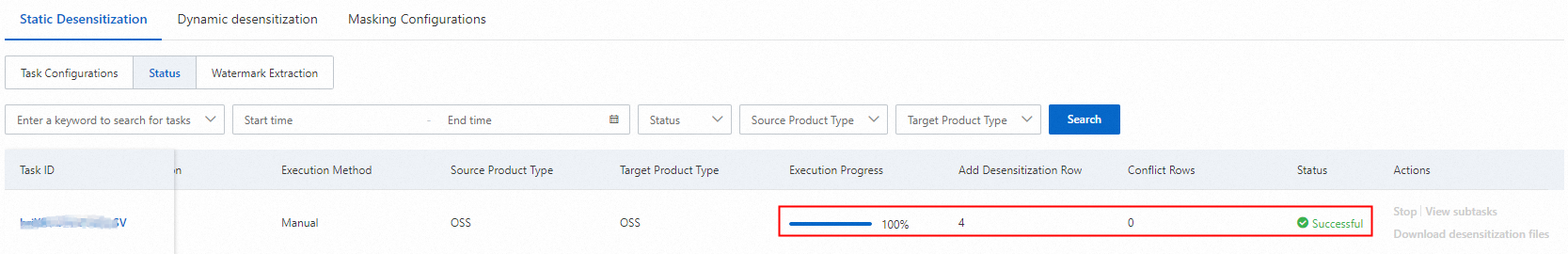
On the Static Desensitization tab, click the Status tab. Wait until the task progress reaches 100% and the status changes to Successful.
4.2 Verify the desensitization result
Go to the Buckets page on the OSS Console, click the name of the destination Bucket, and find the desensitized file in the object list. The file name is in the format
<DestinationFileName>_<TaskExecutionTime>.<FileType>. For example, inusernews_20240808150643.csv,20240808150643indicates that the task was run at 15:06:43 on August 8, 2024. You can click Download to obtain the file.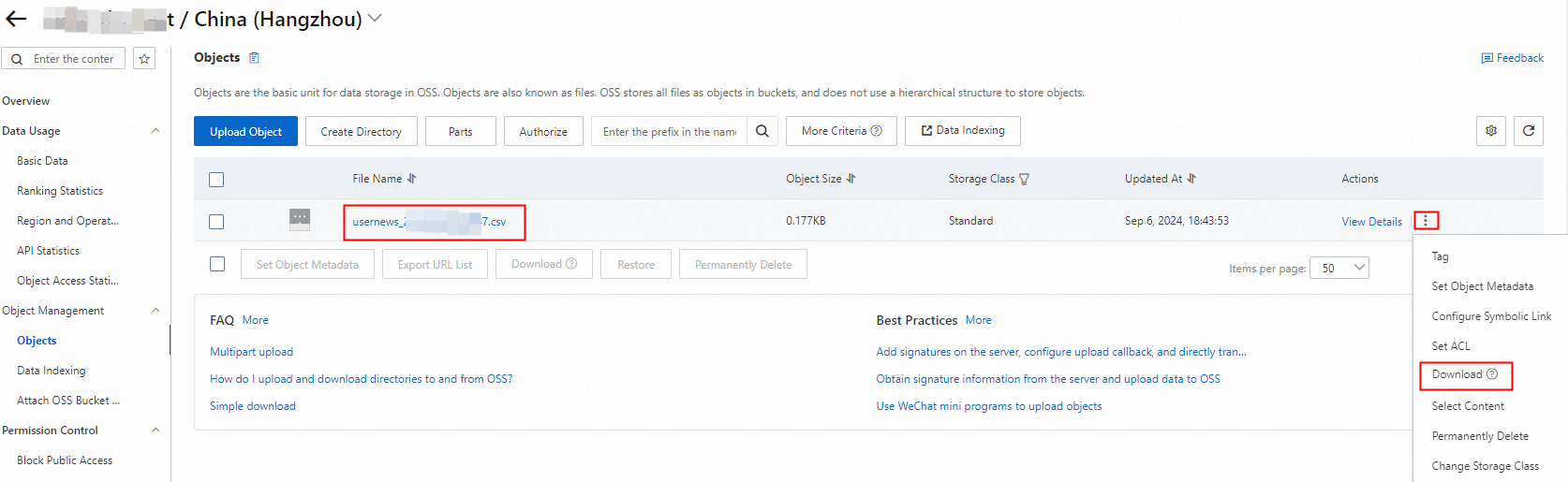
After you download and open the file, you can see that the data in the Name, Mobile phone number, and ID card number columns has been desensitized.
Summary
Before sharing, desensitize raw data stored in an OSS Bucket and save it to a destination OSS Bucket. After desensitization, no
Flexible desensitization algorithms
Efficient rule configuration
DSC also supports Data Desensitization Templates.
Scheduled desensitization tasks
You can schedule Data Desensitization Tasks to run at specific times, such as hourly, daily, weekly, or monthly. This feature promptly desensitizes new and updated data.