This topic describes other data security measures that are supported by MaxCompute.
Disable SELECT result downloads from DataWorks
By default, after developers analyze data in the DataWorks integrated development environment (IDE), the results of a SELECT statement can be downloaded to a local machine. This is true even when ProjectProtection is enabled for a project — enabling ProjectProtection alone does not prevent downloads if the user has read permissions on the table.
To prevent data from leaving the environment through this channel, disable the Download SELECT Result toggle in DataWorks.
Who can do this: DataWorks administrator.
To access the setting, log on to the DataWorks console and go to the Workspaces page. Find your workspace and click Details in the Actions column. In the left-side navigation pane, click General Configurations, then go to the Security Settings section.
Check the current setting
In the Security Settings section, check whether Download SELECT Result is turned on.
Turn off Download SELECT Result
In the Security Settings section, turn off Download SELECT Result.
Turn on Download SELECT Result
In the Security Settings section, turn on Download SELECT Result.
Improve security through RAM user management
When you use MaxCompute through the DataWorks console, project members are added as Resource Access Management (RAM) users. MaxCompute identifies RAM users but does not verify their RAM-level permissions — any RAM user under your Alibaba Cloud account can be added to a project. Because of this, the main attack surface to harden is RAM user logon security.
The following measures reduce the risk from compromised or over-privileged RAM user accounts.
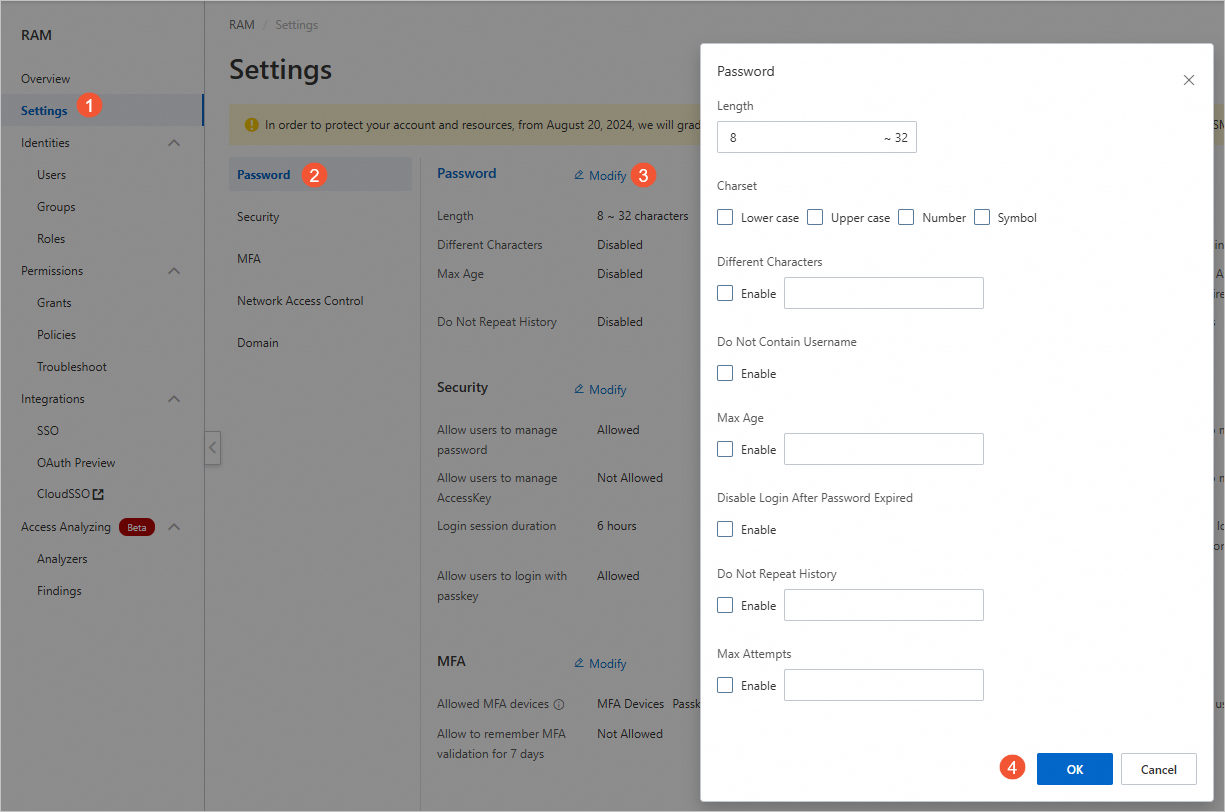
Configure password strength
Set a strong password policy for RAM users. Configurable options include minimum password length, whether non-letter characters are required, and how frequently passwords must be rotated. Configure these settings in the RAM console.
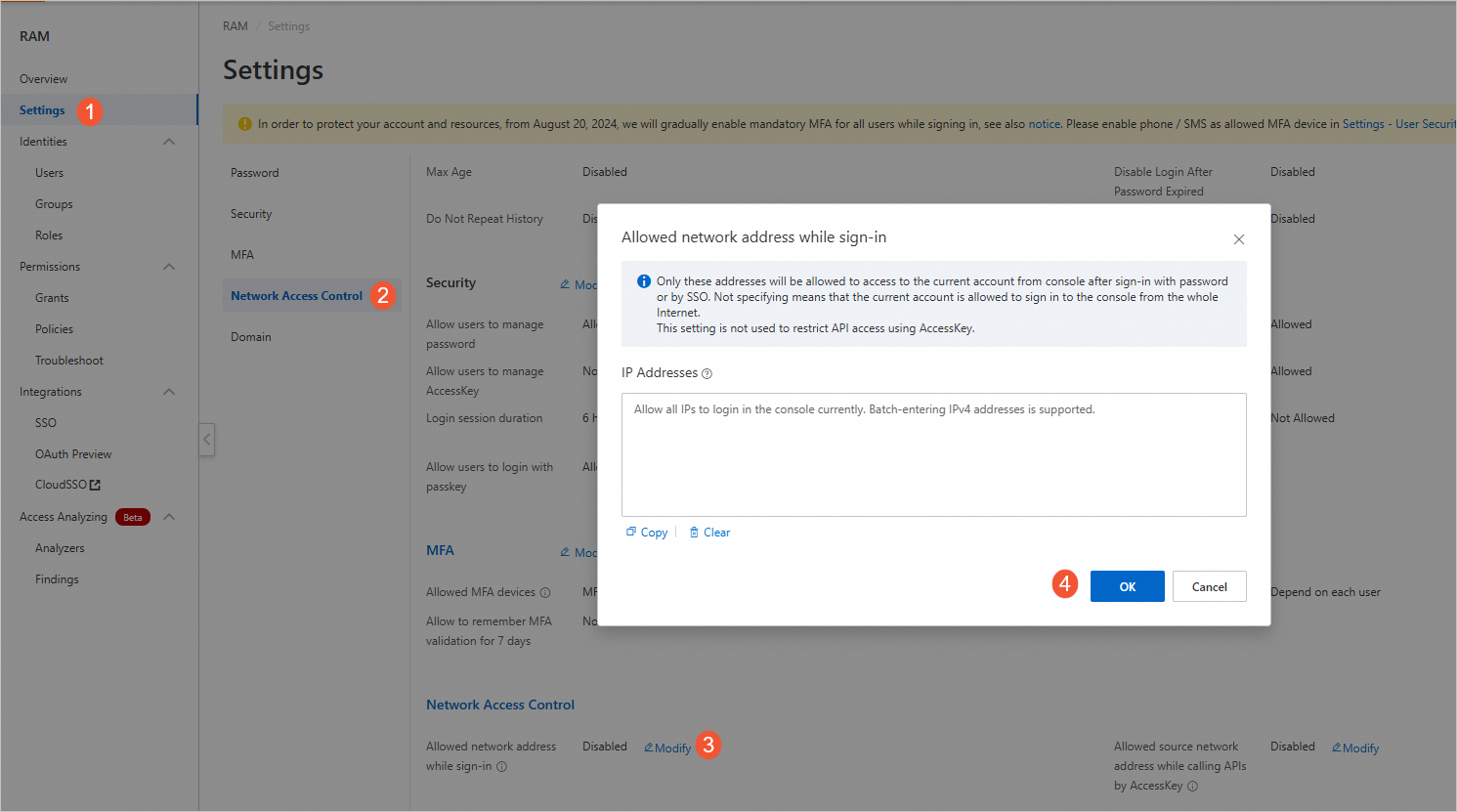
Configure logon address masks
Configure logon address masks to specify the IP addresses from which a RAM user can log on to the DataWorks console. This prevents access from unexpected locations even if credentials are compromised.
Revoke unused permissions
When a RAM user's permissions are no longer needed due to changing business requirements, revoke those permissions immediately. Unused permissions expand the blast radius of a compromised account — removing them limits what an attacker can access if credentials are exposed.