Data Security Center (DSC) allows you to configure data masking templates and algorithms. You can add data masking algorithms that are frequently used in the same scenario to a data masking template. You can use the template to configure a static data masking rule in an efficient manner. This topic describes how to configure data masking templates and algorithms.
Background information
DSC supports the following data masking algorithms: hashing, redaction, substitution, rounding, encryption, decryption, and shuffling. For more information, see Supported data masking algorithms.
Configure a data masking template
Create a data masking template
Log on to the DSC console.
In the left-side navigation pane, choose .
On the Data Desensitization page, click the Masking Configurations tab.
On the Desensitization Template tab, click New template.
In the New template panel, configure the parameters and click OK.
Parameter
Description
Template name
The name of the data masking template.
Template description
The description of the data masking template. You can enter information such as the scenario to which you want to apply the data masking template.
Matching mode
The mode that is used to match sensitive data. Valid values:
Sensitive type: If you select this mode, you must select a sensitive data type and configure a data masking algorithm in the Rule list section. For example, you can select Vehicle Identification Number and Unified Social Credit Code.
Field name: If you select this mode, you must specify a field name and configure a data masking algorithm in the Rule list section.
Rule list
The data masking rule. You can select a sensitive data type or specify a field name. Then, you can configure a data masking algorithm.
If you set the Matching mode parameter to Sensitive type, you can select the fields in the Data Feature column on the Identification Features tab. You can select built-in or custom fields.
You can click Increase algorithm to add a data masking rule.
Modify or delete a data masking template
On the Desensitization Template tab, you can modify or delete a data masking template based on your business requirements.
Modify a data masking template
If you want to update the description or data masking rules of a data masking template, you can perform the following operations to modify the template: Find the data masking template and click Edit in the Actions column. In the Edit panel, modify the description or rules.
Delete a data masking template
ImportantAfter you delete a data masking template, it cannot be restored. Proceed with caution.
If a data masking template is no longer suitable for the current business scenario, you can perform the following operations to delete the template: Find the data masking template and click Delete in the Actions column.
Configure a data masking algorithm
Log on to the DSC console.
In the left-side navigation pane, choose .
On the Data Desensitization page, click the Masking Configurations tab.
On the Masking Configurations tab, click the Data Masking Algorithm tab.
Click an algorithm tab to configure a data masking algorithm.
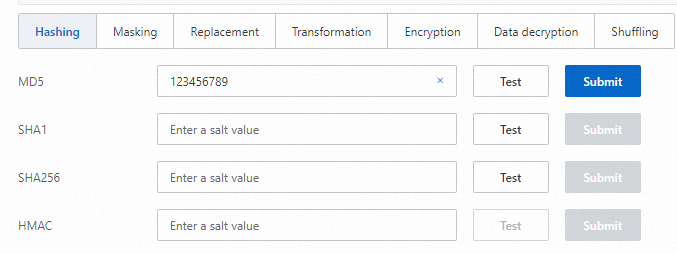
After you configure a data masking algorithm, click Test. In the Desensitization Algorithm Test panel, test the algorithm.
You can test only specific data masking algorithms. If Test is not displayed for an algorithm in the DSC console, you cannot perform the test.
Click Submit to the right of the algorithm.
References
After you configure a data masking algorithm, you can go to the tab to configure or modify a data masking algorithm for a static data masking task. For more information, see Perform static data masking.