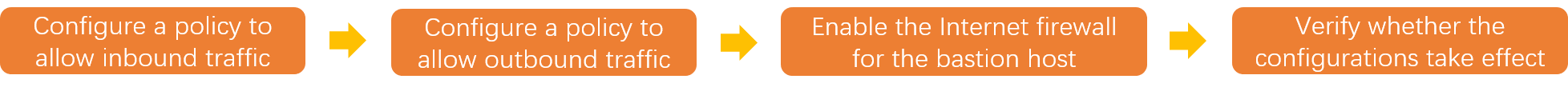
When Cloud Firewall and Bastionhost are deployed together, the Internet firewall blocks Bastionhost traffic by default. This topic explains how to configure inbound and outbound access control policies to keep Bastionhost fully operational while Cloud Firewall protection remains active.
Prerequisites
Before you begin, ensure that you have:
Cloud Firewall purchased. For more information, see Purchase Cloud Firewall.
A Bastionhost instance purchased and enabled. For more information, see Purchase a bastion host and Enable a bastion host.
How it works

Cloud Firewall sits at the Internet boundary and inspects all traffic entering and leaving your Bastionhost instance. Without explicit allow policies, the Internet firewall denies Bastionhost traffic by default, causing the following issues:
Service ports become inaccessible
Assets and users cannot be imported
Web page-based O&M cannot be performed
Videos cannot be played
To resolve this, configure two allow policies — one inbound and one outbound — before enabling Internet firewall protection for the Bastionhost instance.
Overview of required policies
The following table lists all policies you need to create. Configure them in the order shown.
| Step | Direction | Source | Destination | Ports | Protocol | Action | Priority |
|---|---|---|---|---|---|---|---|
| 1a | Inbound | Allowed public CIDR blocks | Bastionhost O&M IP | 60022, 63389, 9443, 443, 20045 | TCP | Allow | Highest |
| 1b | Inbound | 0.0.0.0/0 | Any | Any | Any | Deny | Lowest |
| 2a | Outbound | Bastionhost egress IPs | Alibaba credible domains | 443, 80 | TCP | Allow | Highest |
| 2b | Outbound | 0.0.0.0/0 | Any | Any | Any | Deny | Lowest |
Create all four policies before enabling Internet firewall protection in Step 3. Enabling protection before the allow policies are in place will immediately block all Bastionhost traffic.
Step 1: Create an inbound policy
Configure an inbound policy on the Internet firewall to allow traffic from authorized public IP addresses to reach the open ports of your Bastionhost instance.
Log on to the Cloud Firewall console.
In the left-side navigation pane, choose Prevention Configuration > Access Control > Internet Border.
On the Inbound tab, click Create Policy.
In the Create Inbound Policy panel, click the Create Policy tab and configure the following parameters. Then click OK.
NoteTo allow multiple ports without listing them individually, create an address book containing all required ports and select it as the Port type.
Parameter Value Why Source type IP Restricts access to specific IP ranges you control. Source Enter the public CIDR blocks allowed to access the Bastionhost instance. Only your authorized networks can reach the bastion host. Destination type IP Targets the specific IP address of the Bastionhost instance. Destination Enter the IP address to which the O&M address of the Bastionhost instance is resolved. To find this IP address, go to the Internet Border page and filter by Asset Type. You do not need to log on to the Bastionhost console. Ensures the policy targets only the Bastionhost instance. Protocol type TCP All Bastionhost services use TCP. Port type Port or Address Book Select Address Book to allow all required ports at once using a pre-configured address book. Select Port to specify ports individually. Port Specify ports based on the services to allow. Bastionhost uses the following default ports: SSH-based O&M: 60022, Remote Desktop Protocol (RDP)-based O&M:63389, Video playback:9443, Host O&M and O&M portal:443, Bastionhost Assistant:20045Each port corresponds to a specific Bastionhost function. Open only the ports your use case requires. Application ANY Allows all application-layer protocols on the specified ports. Action Allow Permits the specified CIDR blocks to reach the open ports of the Bastionhost instance. Description Enter a description to identify this policy. Helps you manage policies as their number grows. Priority Highest Ensures this allow policy is evaluated before the deny-all policy you create next. Enabling status On Activates the policy immediately after creation. Create a deny-all inbound policy to block all other public traffic. Click Create Policy again and configure the following parameters: Leave all other parameters at their defaults.
Source:
0.0.0.0/0Priority: Lowest
Action: Deny
Step 2: Create an outbound policy
The Bastionhost instance needs to reach Alibaba Cloud services over the Internet — for example, to import assets and users. Configure an outbound policy to allow this traffic.
On the Outbound tab, click Create Policy.
In the Create Outbound Policy panel, click the Create Policy tab and configure the following parameters. Then click OK.
Parameter Value Why Source type IP Targets traffic originating specifically from the Bastionhost instance. Source Enter the egress IP addresses of the Bastionhost instance. Ensures only Bastionhost traffic is covered by this allow policy. Destination type Address Book Covers the full range of Alibaba Cloud service endpoints without manual IP maintenance. Destination In the Select Address Book panel, select Cloud Service Address Book and search for Alibaba credible domains. Covers all Alibaba Cloud service domains that Bastionhost relies on. Protocol type TCP Alibaba Cloud services are accessed over TCP. Port type Port or Address Book Select Address Book to group ports for batch management. Port 443and80Port 443 (HTTPS) and port 80 (HTTP) are the standard ports for cloud service API communication. Application HTTP and HTTPS Matches the application protocols used by Alibaba Cloud service endpoints. Action Allow Permits the Bastionhost instance to reach Alibaba Cloud service endpoints. Description Enter a description to identify this policy. Helps you manage policies as their number grows. Priority Highest Ensures this allow policy is evaluated before the deny-all policy you create next. Enabling status On Activates the policy immediately after creation. Create a deny-all outbound policy to block all other Internet traffic from the Bastionhost instance. Click Create Policy again and configure the following parameters:
Source:
0.0.0.0/0Priority: Lowest
Action: Deny
Step 3: Enable the Internet firewall for the Bastionhost instance
After creating all four policies, enable Internet firewall protection for the Bastionhost instance.
In the left-side navigation pane, click Firewall Settings.
On the Internet Firewall tab, locate the IP address of the Bastionhost instance and click Enable Protection in the Actions column.
If the Bastionhost instance was recently purchased, its information is synchronized to Cloud Firewall after approximately 15 to 30 minutes. If the instance does not appear in the list, wait and refresh the page.
After protection is enabled, Cloud Firewall inspects all Bastionhost traffic using the policies you configured. The policies allow legitimate O&M traffic through while blocking everything else.
Step 4: Verify the configuration
Confirm that the policies are working correctly by checking the following:
The service ports of the Bastionhost instance are accessible.
Assets and users can be imported.
Web page-based O&M works as expected.
Videos can be played.
To review traffic logs, go to the Log Audit page in the Cloud Firewall console and open the Traffic Logs tab. For more information, see Log audit.