Service Mesh (ASM) enforces zero trust security for cloud-native applications by moving identity authentication and authorization out of your application code and into the mesh infrastructure. Define security policies through ASM, update them at any time, and have them take effect immediately -- without redeploying your applications.
Why zero trust matters for microservices
Microservices deliver scalability, agility, independent scaling, business logic isolation, independent lifecycle management, and easier distributed development, but they also expand the attack surface. Each service is a potential target. Kubernetes is a competent platform to host and orchestrate microservices, but by default, services in a Kubernetes cluster communicate over plaintext HTTP. Perimeter-based security alone cannot protect this internal traffic -- if an attacker compromises one service, they can move laterally to any other service on the network.
Zero trust addresses this by requiring explicit authentication for every request and enforcing the principle of least privilege for all access. In addition to Kubernetes network policies that control traffic at Layer 3, ASM provides peer authentication, request authentication, authorization policies, and Open Policy Agent (OPA)-based fine-grained access control at higher layers.
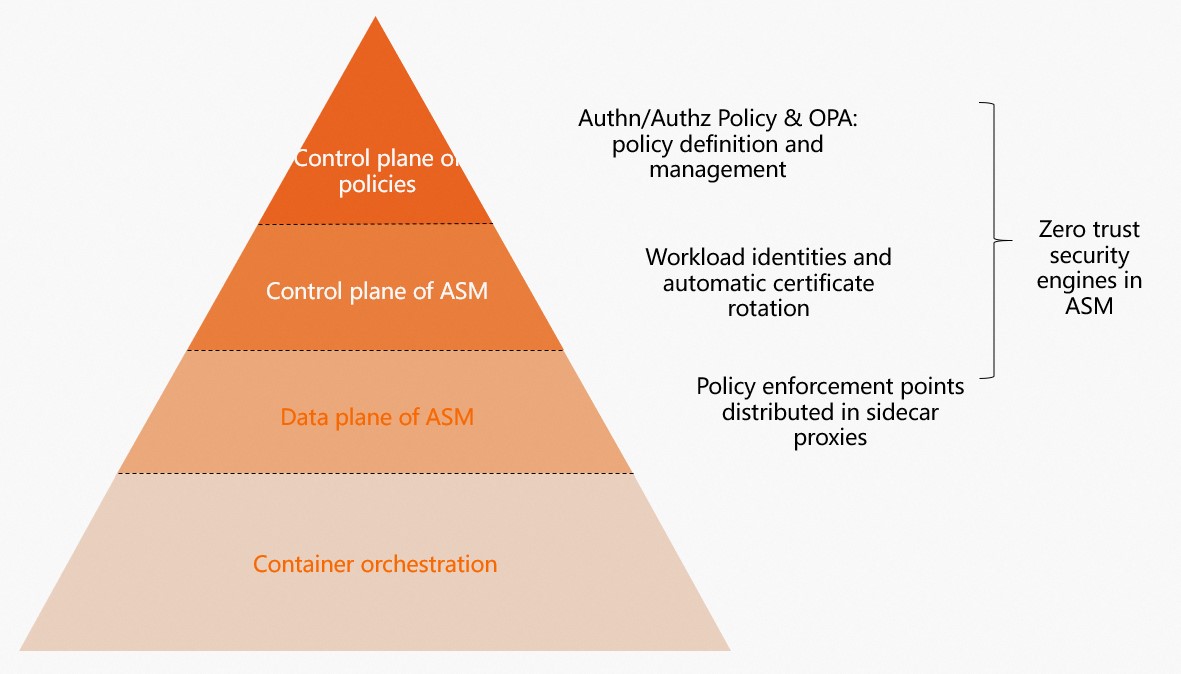
How ASM implements zero trust
ASM secures your microservices without requiring changes to application code. The zero trust system has four pillars:
| Pillar | What it does |
|---|---|
| Workload identity | Assigns a unique, SPIFFE-compliant identity to each workload. This identity is the foundation for all authentication and authorization decisions. |
| Certificate management | Issues TLS X.509 certificates that embed workload identities, and automatically rotates certificates and private keys. All sidecar proxies use these certificates. |
| Policy enforcement | Supports Istio Role Based Access Control (RBAC) policies and OPA-based fine-grained authorization policies. |
| Observability | Collects logs and metrics for policy execution, so you can analyze the effectiveness of each policy. |
Advantages over application-level security
Compared to implementing security in application code, ASM offers several advantages:
| Advantage | Description |
|---|---|
| Independent lifecycle management | Sidecar proxies are managed separately from applications. Update security policies without redeploying code. |
| Immediate policy enforcement | Configure or update policies and have them take effect instantly. |
| Centralized security governance | A single control plane lets security teams build, manage, and deploy enterprise-wide policies without requiring developers to implement security logic in each service. |
| Built-in credential validation | ASM supports JSON Web Token (JWT) authentication to validate user credentials in requests. |
| Defense in depth | Deploy identity authentication and authorization as services within ASM instances. These services benefit from ASM protections: encryption in transit, identity authentication, policy enforcement, and credential validation. |
ASM provides strict identity and access management, Transport Layer Security (TLS) encryption, authentication, authorization, and audit logging -- all out of the box.
Security capabilities
ASM secures service-to-service communication through end-to-end encryption, service-level identity authentication, and fine-grained authorization policies.
Workload identity
ASM assigns a unique identifier to each microservice running in the mesh. Services use this identifier for mutual authentication and authorization decisions.
When managing workloads in Kubernetes clusters, ASM assigns a service identity based on the workload's service token. Service identities comply with the Secure Production Identity Framework for Everyone (SPIFFE) and use this format:
spiffe://<trust-domain>/ns/<namespace>/sa/<service-account>View workload identities in the console
Log on to the ASM console. In the left-side navigation pane, choose Service Mesh > Mesh Management.
On the Mesh Management page, click the name of the ASM instance. In the left-side navigation pane, choose Mesh Security Center > Workload Identity.
On the Workload Identity page, select a cluster from the Data Plane drop-down list and a namespace from the Namespace drop-down list to view workload identities.
Peer authentication
Peer authentication verifies the identity of both sides in a service-to-service interaction using mutual TLS (mTLS) or server-side TLS authentication. Certificate lifecycle management such as automatic certificate rotation is supported. The behavior depends on which services have sidecar proxies injected:
| Sidecar injection | Behavior |
|---|---|
| Both client and server | mTLS encryption is enabled for all communication. |
| Client only | The client enables mTLS based on the server's configuration. |
| Server only | The default mTLS mode is permissive: the server accepts both plaintext and encrypted traffic. If you set the mTLS mode to strict, requests from clients without sidecar proxies fail. |
Request authentication
Request authentication validates end-user or system credentials using JWTs. When a request authentication policy is applied to a service:
Requests with a valid JWT are allowed.
Requests with an invalid JWT are rejected (HTTP 403).
Requests without a JWT are allowed by default.
To require a valid JWT for all requests, combine a request authentication policy with an authorization policy. This blocks requests with an invalid JWT and requests without a JWT.
Example: Set up JWT authentication for a service
This example uses the Bookinfo sample application as the target service and a sleep pod as the client.
Prerequisites
Deploy the Bookinfo application. For details, see Deploy an application in an ASM instance.
Step 1: Deploy the sleep client
Create a
sleep.yamlfile with the following content:Use kubectl to connect to your Container Service for Kubernetes (ACK) cluster and deploy the sleep application:
kubectl apply -f sleep.yaml -n default
Step 2: Create a request authentication policy
Log on to the ASM console. In the left-side navigation pane, choose Service Mesh > Mesh Management.
On the Mesh Management page, click the name of the ASM instance. In the left-side navigation pane, choose Mesh Security Center > RequestAuthentication. Click Create.
Define a JWT rule for the
detailsworkload with the following parameters, then click Create. Key parameters: JWKS value: For more information, see jwks.json.Parameter Value Description issuer testing@asm.istio.ioThe JWT issuer. audiences (blank) Leave blank to allow all services to use this JWT. jwks See below The JSON Web Key Set used to verify JWT signatures. { "keys":[ {"e":"AQAB","kid":"DHFbpoIUqrY8t2zpA2qXfCmr5VO5ZEr4RzHU_-envvQ","kty":"RSA","n":"xAE7eB6qugXyCAG3yhh7pkDkT65pHymX-P7KfIupjf59vsdo91bSP9C8H07pSAGQO1MV_xFj9VswgsCg4R6otmg5PV2He95lZdHtOcU5DXIg_pbhLdKXbi66GlVeK6ABZOUW3WYtnNHD-91gVuoeJT_DwtGGcp4ignkgXfkiEm4sw-4sfb4qdt5oLbyVpmW6x9cfa7vs2WTfURiCrBoUqgBo_-4WTiULmmHSGZHOjzwa8WtrtOQGsAFjIbno85jp6MnGGGZPYZbDAa_b3y5u-YpW7ypZrvD8BgtKVjgtQgZhLAGezMt0ua3DRrWnKqTZ0BJ_EyxOGuHJrLsn00fnMQ"}]}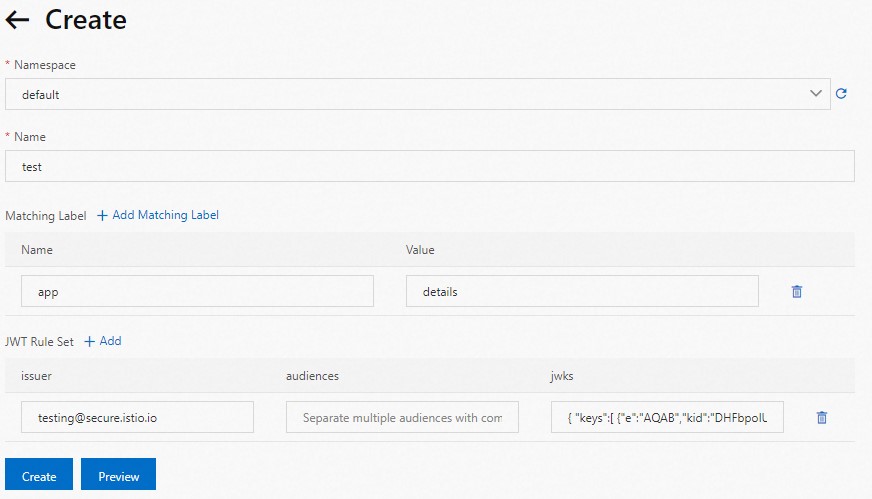
Step 3: Verify the policy
Use a JWT tool to encode the JWKS into a JWT string. Expected result:
eyJhbGciOiJSUzI1NiIsImtpZCI6IkRIRmJwb0lVcXJZOHQyenBBMnFYZkNtcjVWTzVaRXI0UnpIVV8tZW52dlEiLCJ0eXAiOiJKV1QifQ.eyJleHAiOjQ2ODU5ODk3MDAsImZvbyI6ImJhciIsImlhdCI6MTUzMjM4OTcwMCwiaXNzIjoidGVzdGluZ0BzZWN1cmUuaXN0aW8uaW8iLCJzdWIiOiJ0ZXN0aW5nQHNlY3VyZS5pc3Rpby5pbyJ9.CfNnxWP2tcnR9q0vxyxweaF3ovQYHYZl82hAUsn21bwQd9zP7c-LS9qd_vpdLG4Tn1A15NxfCjp5f7QNBUo-KC9PJqYpgGbaXhaGx7bEdFWjcwv3nZzvc7M__ZpaCERdwU7igUmJqYGBYQ51vr2njU9ZimyKkfDe3axcyiBZde7G6dabliUosJvvKOPcKIWPccCgefSj_GNfwIip3-SsFdlR7BtbVUcqR-yv-XOxJ3Uc1MI0tz3uMiiZcyPV7sNCU4KRnemRIMHVOfuvHsU60_GhGbiSFzgPTAa9WTltbnarTbxudb_YEOx12JiwYToeX0DCPb43W1tzIBxgm8NxUgSend a request with the valid JWT: Expected output:
200. The valid JWT was accepted.export TOKEN=eyJhbGciOiJSUzI1NiIsImtpZCI6IkRIRmJwb0lVcXJZOHQyenBBMnFYZkNtcjVWTzVaRXI0UnpIVV8tZW52dlEiLCJ0eXAiOiJKV1QifQ.eyJleHAiOjQ2ODU5ODk3MDAsImZvbyI6ImJhciIsImlhdCI6MTUzMjM4OTcwMCwiaXNzIjoidGVzdGluZ0BzZWN1cmUuaXN0aW8uaW8iLCJzdWIiOiJ0ZXN0aW5nQHNlY3VyZS5pc3Rpby5pbyJ9.CfNnxWP2tcnR9q0vxyxweaF3ovQYHYZl82hAUsn21bwQd9zP7c-LS9qd_vpdLG4Tn1A15NxfCjp5f7QNBUo-KC9PJqYpgGbaXhaGx7bEdFWjcwv3nZzvc7M__ZpaCERdwU7igUmJqYGBYQ51vr2njU9ZimyKkfDe3axcyiBZde7G6dabliUosJvvKOPcKIWPccCgefSj_GNfwIip3-SsFdlR7BtbVUcqR-yv-XOxJ3Uc1MI0tz3uMiiZcyPV7sNCU4KRnemRIMHVOfuvHsU60_GhGbiSFzgPTAa9WTltbnarTbxudb_YEOx12JiwYToeX0DCPb43W1tzIBxgm8NxUg kubectl exec $(kubectl get pod -l app=sleep -o jsonpath={.items..metadata.name}) -c sleep \ -- curl http://details:9080/details/1 -o /dev/null \ --header "Authorization: Bearer $TOKEN" -s -w '%{http_code}\n'Send a request with an invalid JWT: Expected output:
403. The invalid token was rejected.kubectl exec $(kubectl get pod -l app=sleep -o jsonpath={.items..metadata.name}) -c sleep \ -- curl http://details:9080/details/1 -o /dev/null \ --header "Authorization: Bearer badtoken" -s -w '%{http_code}\n'Send a request without a JWT: Expected output:
200. Without a JWT, the request bypasses JWT validation and is allowed through.kubectl exec $(kubectl get pod -l app=sleep -o jsonpath={.items..metadata.name}) -c sleep \ -- curl http://details:9080/details/1 -o /dev/null -s -w '%{http_code}\n'
These results confirm the policy works as expected: valid JWTs pass, invalid JWTs are rejected, and requests without JWTs are allowed unless restricted by an authorization policy.
Authorization policies
Authorization policies control which requests can access a service based on criteria such as source identity, port, IP address, or JWT claims. Use authorization policies together with request authentication to enforce that only authenticated requests reach your services.
An authorization policy consists of three parts:
| Field | Purpose |
|---|---|
selector | Specifies the target workload for the policy. |
action | Specifies whether to ALLOW or DENY requests. |
rules | Defines when to trigger the action. Contains from (request source), to (request operation), and when (additional conditions). |
Example: Require a valid JWT for all requests
This example builds on the request authentication setup above. It adds an authorization policy that blocks requests without a valid JWT.
Prerequisites
Deploy the Bookinfo application. For details, see Deploy an application in an ASM instance.
Deploy the sleep client as described in the request authentication section above.
Step 1: Create the authorization policy
Log on to the ASM console. In the left-side navigation pane, choose Service Mesh > Mesh Management.
On the Mesh Management page, click the name of the ASM instance. In the left-side navigation pane, choose Mesh Security Center > AuthorizationPolicy. Click Create from YAML.
Select default from the Namespace drop-down list, paste the following YAML, and click Create. This policy allows requests to the
detailsservice only when the request principal matchestesting@secure.istio.io/testing@secure.istio.io-- meaning the request must carry a valid JWT issued by this identity. For more information about authorization policy fields, see Authorization Policy.apiVersion: security.istio.io/v1beta1 kind: AuthorizationPolicy metadata: name: require-jwt namespace: default spec: action: ALLOW rules: - from: - source: requestPrincipals: - testing@secure.istio.io/testing@secure.istio.io selector: matchLabels: app: details
Step 2: Verify the policy
Send a request without a JWT:
kubectl exec $(kubectl get pod -l app=sleep -o jsonpath={.items..metadata.name}) -c sleep \
-- curl http://details:9080/details/1 -o /dev/null -s -w '%{http_code}\n'Expected output: 403. The authorization policy blocks requests without a valid JWT from testing@secure.istio.io.
OPA policies
Open Policy Agent (OPA) is a general-purpose policy engine for fine-grained access control. OPA runs alongside your microservices and evaluates each request against your policies before the request is processed.
ASM integrates with OPA, so you can define and dynamically update fine-grained access control policies without redeploying services. For details, see Dynamically update OPA policies in ASM.
For more information about OPA, visit the Open Policy Agent website.
Architecture components
ASM's zero trust architecture consists of four components that work together:
| Component | Role |
|---|---|
| Certificate authority | Manages the full lifecycle of certificates, including issuing and rotating CA certificates. |
| Control plane APIs | Distributes authentication policies, authorization policies, and secure naming information to Envoy sidecar proxies. |
| Sidecar proxies | Act as policy enforcement points (PEPs) that secure all traffic entering and leaving each service. |
| Envoy extensions | Collect telemetry data for auditing and monitoring. |
Each workload receives a TLS X.509 certificate that encodes its identity. ASM automatically rotates these certificates and private keys on a regular schedule. If a private key is compromised, ASM replaces it immediately to minimize the attack surface.
Use case examples
IP-based access control at the ingress gateway. Add authorization policies to the ingress gateway to allow or deny traffic based on source IP address, or integrate a custom external authorization service.
Cross-region access control for financial applications. Use authorization policies to protect cross-region multi-language applications from external networks. Audit egress traffic through the egress gateway to control which third-party services your applications can reach.