ApsaraVideo VOD enables you to configure access control policies in the cloud by setting Referer blacklists and whitelists, User-Agent blacklists and whitelists, and IP address blacklists and whitelists. This provides basic protection for your video resources. The access control feature is easy to use and settings take effect quickly. No additional development is required.
Referer blacklist and whitelist
Overview
Referer is used to track and identify the source of requests based on the HTTP Referer mechanism. You can configure a Referer blacklist or whitelist to identify and filter users. This allows you to control access to ApsaraVideo VOD resources.
After you configure a Referer whitelist or a Referer blacklist, user requests are sent to a point of presence (POP). The POP then authenticates the user identity based on the preset Referer whitelist or blacklist. If a request meets the rules, video data is returned. If a request does not meet the rules, the request is denied and HTTP status code 403 is returned.
After you configure a Referer blacklist or whitelist, wildcard domain names are automatically supported. For example, if you specify example.com as the domain name, the wildcard domain *.example.com takes effect. This means that the Referer blacklist or whitelist settings take effect on all domain names that match *.example.com.
In most cases, mobile devices do not provide the Referer header. By default, access requests that have an empty Referer header are allowed. You can disable access from requests that have an empty Referer header.
Referer is based on HTTP headers, which are prone to forgery and have low security.
For more information, see Configure a Referer whitelist or blacklist to enable hotlink protection.
Example
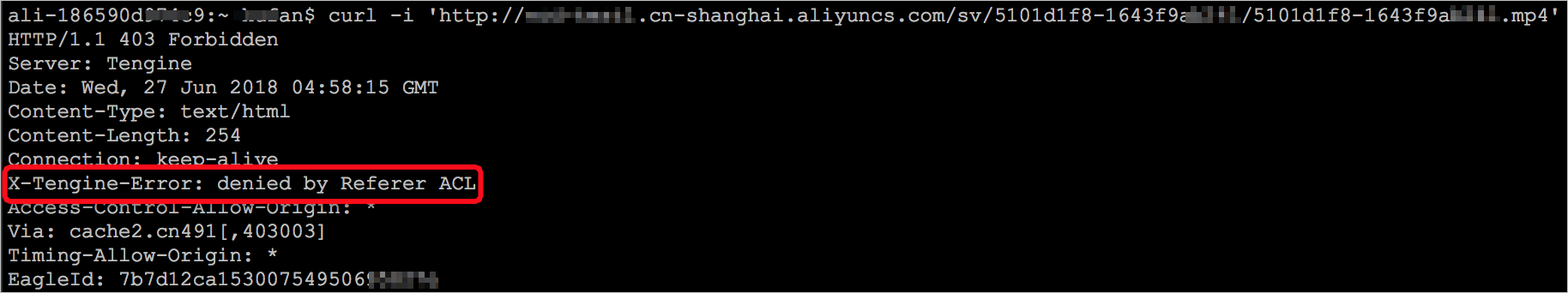
Set the Referer whitelist of the example.cn-shanghai.aliyuncs.com domain name in ApsaraVideo VOD to aliyundoc.com and disable access from requests that have an empty Referer header. Sample code:
curl -i 'http://example.cn-shanghai.aliyuncs.com/sv/5101d1f8-1643f9a****/5101d1f8-1643f9a****.mp4'Return results
A success response is returned for the following request that contains an allowed Referer:
curl -i 'http://example.cn-shanghai.aliyuncs.com/sv/5101d1f8-1643f9a****/5101d1f8-1643f9a****.mp4' \ -H 'Referer: http://www.aliyundoc.com'
User-Agent blacklist and whitelist
Overview
User-Agent is a special string header. It helps the server identify the operating system type and version, CPU type, browser type and version, browser rendering engine, language, and plug-in that are used by users. You can configure a User-Agent blacklist or whitelist to control access from specific browsers or devices.
User-Agent is based on HTTP headers, which are prone to forgery and have low security.
For more information, see Configure a User-Agent blacklist or whitelist.
Example
User-Agent header for Internet Explorer 9.0 on a PC:
User-Agent:Mozilla/5.0(compatible;MSIE9.0;WindowsNT6.1;Trident/5.0;Simulate the following HTTP request for verification:
curl -i 'http://example.cn-shanghai.aliyuncs.com/sv/5101d1f8-1643f9a****.mp4' \ -H 'User-Agent: iPhone OS;MI 5'
IP address blacklist and whitelist
Overview
You can add a list of IP addresses or CIDR blocks.
For example, you can add the
172.16.0.1/24CIDR block to the IP address blacklist or whitelist. The first 24 bits are network bits. The remaining 8 bits are host bits. The subnet can accommodate 254 hosts. Therefore, the CIDR block specifies IP addresses from 172.16.0.1 to 172.16.0.255.You can choose whether to preferentially use remote_addr or X-Forwarded-For (XFF) to determine the IP address of the request source. You can also use both remote_addr and X-Forwarded-For (XFF).
If you configure an IP address blacklist or whitelist, you cannot distribute content to many consumers. Therefore, IP-based access control is not suitable for widespread content distribution. Additionally, illegal access may occur even when the access limit is not exceeded in a whitelist mechanism.
For more information, see Configure an IP address blacklist or whitelist.