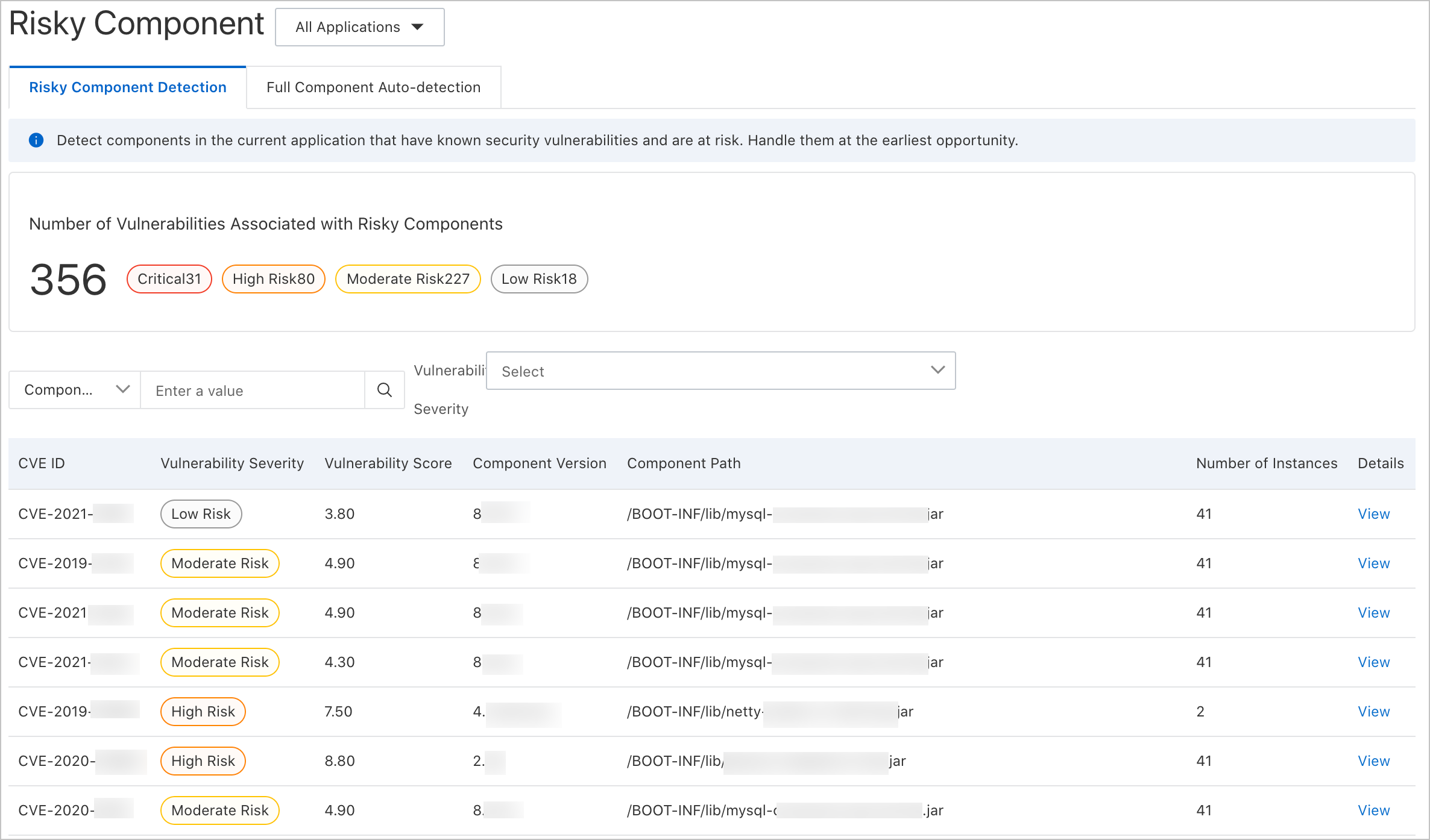
Third-party dependencies from public repositories such as Maven can introduce vulnerabilities with known Common Vulnerabilities and Exposures (CVE) entries. Application Real-Time Monitoring Service (ARMS) Application Security scans your applications to detect these risky components, giving you visibility into CVE severity, affected versions, and dependency paths so you can prioritize remediation.
From the Risky Components page, you can:
Identify third-party dependencies with known CVEs across all monitored applications
Assess vulnerability severity, scores, and affected component versions
Trace component paths to locate vulnerable dependencies in your dependency tree
Review a full inventory of all third-party components, including those without known vulnerabilities
Risky components expose your application to potential attacks. Upgrade affected components as soon as possible. If an immediate upgrade is not feasible, set the prevention mode to Monitor and Block so that ARMS intercepts exploit attempts at runtime.
Prerequisites
Before you begin, make sure you have:
An application monitored by ARMS with Application Security enabled
Access to the ARMS console
Open the Risky Components page
Log on to the ARMS console.
In the left-side navigation pane, choose Application Security > Risky Component Detection.
In the top navigation bar, select a region.
By default, the page displays vulnerability counts across all applications.
Filter by application
To view risky components for a single application, use either method:
At the top of the Risky Components page, open the All Applications drop-down list and select an application.
In the left-side navigation pane, choose Application Security > Application List. Find the target application and click the number in the Risky Components column.
View vulnerability details
The Risky Component Detection tab lists all detected vulnerabilities. Each row contains the following fields:
| Column | Description |
|---|---|
| CVE ID | Identifier in the Common Vulnerabilities and Exposures database. Use this to look up the vulnerability in public CVE databases for additional context. |
| Vulnerability severity | Severity rating (for example, Critical, High, Medium, or Low) based on the nature of the vulnerability. |
| Vulnerability score | Numeric risk score that quantifies the severity. Higher scores indicate greater risk. |
| Component version | Version of the affected third-party component. |
| Component path | Full dependency path that includes the vulnerable component, showing how the dependency is introduced into your application. |
Filter vulnerabilities
Narrow down results by filtering on any combination of:
Component path -- Locate vulnerabilities in a specific dependency chain.
CVE ID -- Search for a specific vulnerability.
Vulnerability severity -- Focus on the most severe vulnerabilities first.
Inspect a specific vulnerability
Click View in the Details column to open a detail panel. The panel contains:
Full vulnerability details, including the CVE description
Affected components and their versions
Application instances running the vulnerable component
View all third-party components
The Risky Component Detection tab only lists components with known CVEs. To see every third-party component in your applications, switch to the Full Component Auto-detection tab.
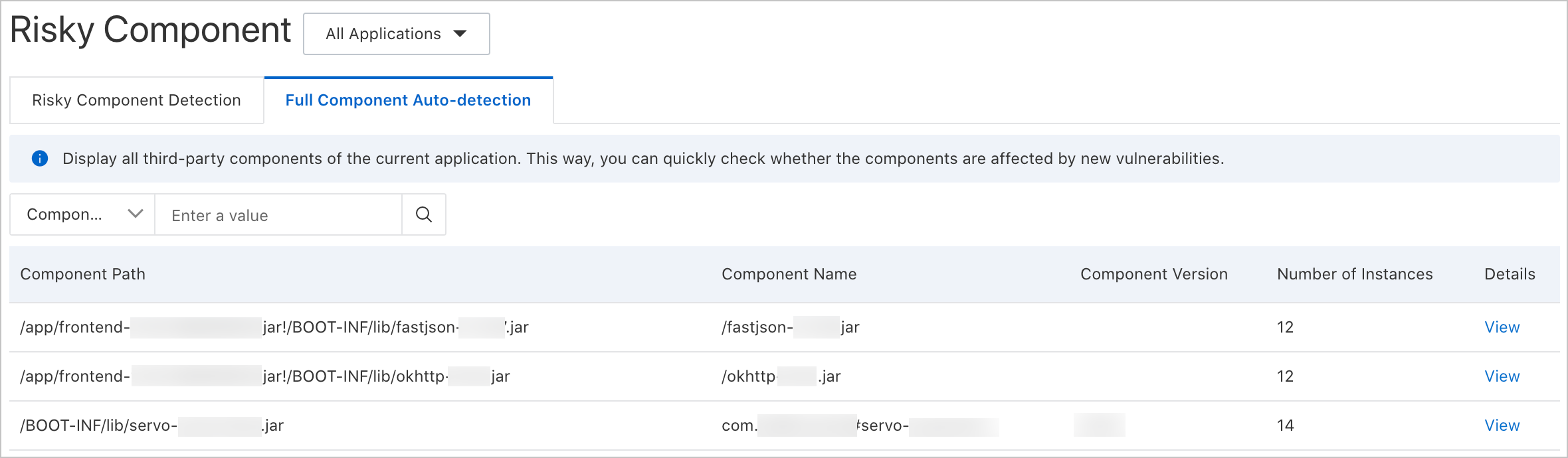
Use this tab for proactive security management. For example, when a new vulnerability is publicly disclosed, search the full component list to determine whether your applications include the affected component -- before it appears on the Risky Component Detection tab.
Remediation guidance
Address risky components in order of severity. The following table summarizes the recommended approach:
| Action | When to use | Details |
|---|---|---|
| Upgrade the component | A patched version is available (recommended) | Check the CVE entry for the fixed version. Update the dependency in your project configuration (for example, pom.xml for Maven) and redeploy. For transitive dependencies, upgrade the direct dependency that introduces the vulnerable component. |
| Enable runtime protection | An upgrade is not immediately feasible | Set the prevention mode to Monitor and Block in ARMS. This intercepts exploit attempts targeting the vulnerability at runtime, providing a temporary safeguard while you plan the upgrade. |
| Monitor the full component inventory | Ongoing practice | Regularly review the Full Component Auto-detection tab. When a new CVE is disclosed, search the inventory to determine exposure before the vulnerability appears on the Risky Component Detection tab. |