vsftpd (Very Secure FTP Daemon) is an open source FTP server for UNIX and Linux systems. It supports FTP, SFTP over SSH, and FTP with SSL (Secure Sockets Layer)/TLS (Transport Layer Security) encryption, and is widely used for its stability and configurability.
This topic describes how to install and configure vsftpd on an Alibaba Cloud Elastic Compute Service (ECS) Linux instance.
Quick deployment
Click Run now to open Terraform Explorer, where you can view and run Terraform code to automatically build an FTP site on an ECS instance.
Prerequisites
Before you begin, ensure that you have:
A Linux ECS instance running Alibaba Cloud Linux 3 or 2, CentOS 7.x 64-bit, Ubuntu, or Debian
A static public IP address or an Elastic IP Address (EIP) associated with the instance. For details, see Elastic IP Address
Alibaba Cloud Linux 3 and 2/CentOS 7.x
Step 1: Install vsftpd
Update system packages and install vsftpd.
sudo yum update -y sudo yum install vsftpd -yStart vsftpd and enable it to start on boot.
sudo systemctl start vsftpd sudo systemctl enable vsftpdVerify the service is running.
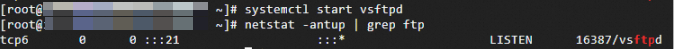
netstat -antup | grep ftpIf the output is similar to the following, vsftpd has started successfully. At this point, vsftpd runs in anonymous mode by default. Anonymous users can connect without a password but cannot upload or modify files.
Step 2: Configure vsftpd
Create a dedicated FTP user and set a password. This topic uses
ftpuseras an example.sudo useradd -d /data/ftp -s /sbin/nologin ftpuser # Set home directory; disable shell access sudo passwd ftpuserCreate the FTP directory and set ownership and permissions.
vsftpd requires that the chroot root directory is not writable by the FTP user. Setting permissions to
750(owner has write access; FTP user does not) satisfies this requirement. If you need the directory to be writable, addallow_writeable_chroot=YESto the configuration file in the next step. This resolves the500 OOPS: vsftpd: refusing to run with writable rooterror.sudo mkdir -p /data/ftp sudo chown ftpuser:ftpuser /data/ftp sudo chmod 750 /data/ftp # Must be 755 or 750; see note belowBack up the configuration file.
sudo cp /etc/vsftpd/vsftpd.conf /etc/vsftpd/vsftpd.conf.bakOpen the configuration file for editing.
sudo vim /etc/vsftpd/vsftpd.confSet the basic security parameters.
listen=YES # Enable IPv4 listener anonymous_enable=NO # Disable anonymous access local_enable=YES # Enable local user logon write_enable=YES # Allow file uploads chroot_local_user=YES # Lock users to their home directory allow_writeable_chroot=YES # Resolve chroot write errorsAdd passive mode settings at the end of the file.
Passive mode is recommended because most client machines are behind firewalls or network address translation (NAT) and cannot receive inbound connections required by active mode.
pasv_enable=YES # Enable passive mode pasv_min_port=40000 # Lower bound of the passive port range pasv_max_port=40100 # Upper bound of the passive port range pasv_address=<public_ip_address> # Replace with your instance's public IP addressRestart vsftpd to apply the configuration.
sudo systemctl restart vsftpd
Step 3: Open security group ports
Add inbound rules to the security group of your ECS instance. For instructions, see Add a security group rule.
Passive mode (recommended): Allow TCP traffic on port 21 and ports 40000–40100. For information about why a port range is required for FTP passive mode and configuration recommendations, see Recommendations for FTP passive mode port configuration.
Active mode: Allow TCP traffic on port 21 only.
If you use active mode, clients in a local area network (LAN) must obtain their real public IP address before connecting, or the connection will fail.
Step 4: Verify the FTP service
Verify the service using an FTP client, a browser, or a file explorer.
Test the local connection from the instance.
ftp ftpuser@localhostA
Login successfulmessage confirms the connection works.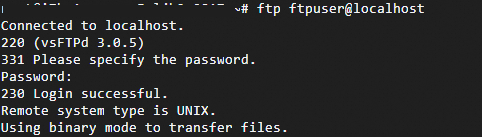
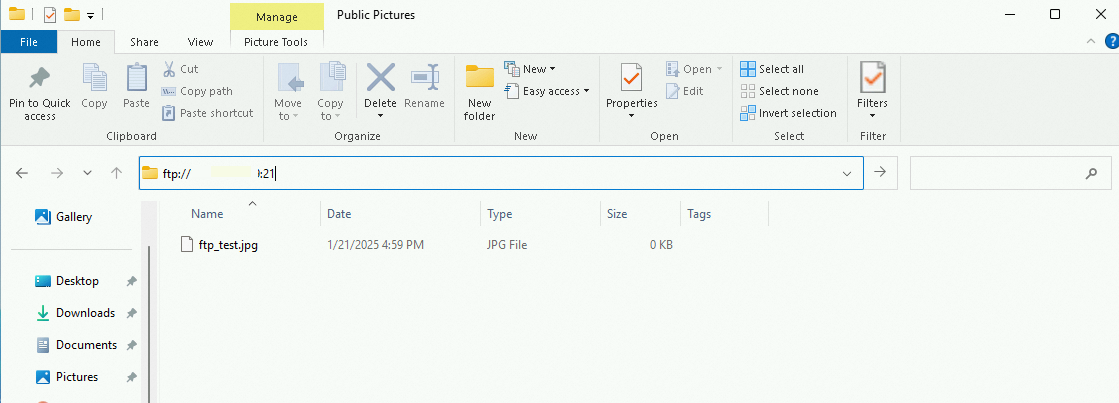
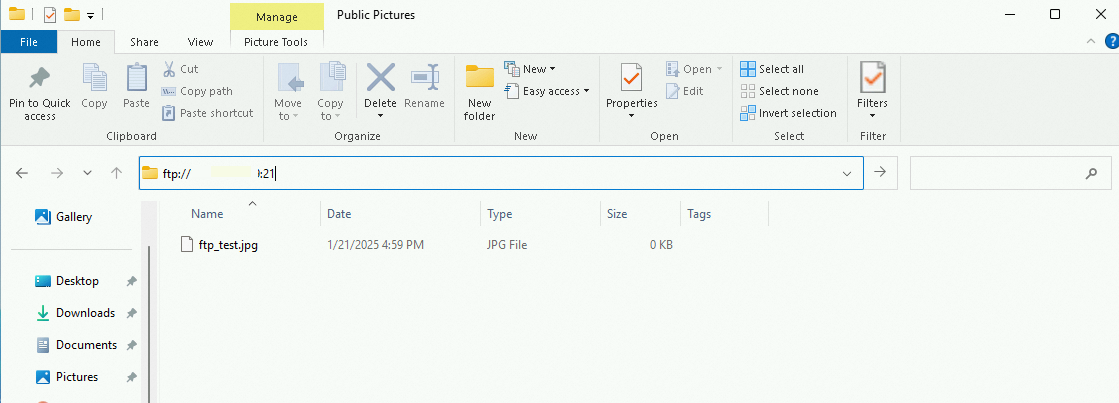
Test the client connection from a remote machine. On the client computer, open the file explorer and go to the FTP address shown in the figure. Enter the FTP username and password in the logon dialog box. After logging in, you can upload and download files.
Ubuntu and Debian
Step 1: Install vsftpd
Update system packages and install vsftpd.
sudo apt update && sudo apt upgrade -y sudo apt install vsftpd -yStart vsftpd and enable it to start on boot.
sudo systemctl start vsftpd sudo systemctl enable vsftpd
Step 2: Configure vsftpd
Create a dedicated FTP user.
sudo useradd -m -s /bin/bash ftpuser # Create the user and generate a home directory sudo passwd ftpuser # Set a strong passwordCreate a file storage directory inside the user's home directory and set permissions.
sudo mkdir /home/ftpuser/ftp-files sudo chown ftpuser:ftpuser /home/ftpuser/ftp-files sudo chmod 755 /home/ftpuser/ftp-filesBack up the configuration file.
sudo cp /etc/vsftpd.conf /etc/vsftpd.conf.bakOpen the configuration file for editing.
sudo nano /etc/vsftpd.confSet the basic security parameters.
listen=YES anonymous_enable=NO # Disable anonymous access local_enable=YES # Allow local user logon write_enable=YES # Enable write permissions chroot_local_user=YES # Lock users in their home directoryAdd the following settings at the end of the file.
allow_writeable_chroot=YES # Allow writing to the chroot directory local_root=/home/ftpuser/ftp-files # Set the FTP user's root directory # Passive mode configuration pasv_enable=YES pasv_address=<your_public_ip_address> # Replace with your instance's public IP address pasv_min_port=40000 pasv_max_port=40100Restart vsftpd to apply the configuration.
sudo systemctl restart vsftpdAfter installation, a default user named
ftpis created with no password. Set a password for this user.sudo passwd ftpAdd the
ftpuser to the allowed users list.echo "ftp" | sudo tee -a /etc/vsftpd.userlistCreate an FTP directory for the
ftpuser and grant permissions.sudo mkdir /home/ftp sudo chmod 777 /home/ftp
Step 3: Open security group ports
Add inbound rules to the security group of your ECS instance. For instructions, see Add a security group rule.
Passive mode (recommended): Allow TCP traffic on port 21 and ports 40000–40100.
Active mode: Allow TCP traffic on port 21 only.
If you use active mode, clients in a LAN must obtain their real public IP address before connecting, or the connection will fail.
Step 4: Verify the FTP service
Test the local connection from the instance.
ftp ftpuser@localhostA
Login successfulmessage confirms the connection works.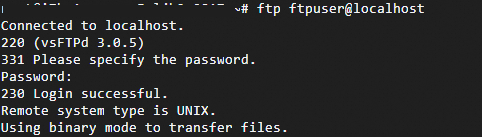
Test the client connection from a remote machine. On the client computer, open the file explorer and go to the FTP address shown in the figure. Enter the FTP username and password in the logon dialog box. After logging in, you can upload and download files.
Troubleshooting
| Issue | Solution |
|---|---|
Timeout after 227 Entering Passive Mode | Check that pasv_address matches your instance's public IP address, and that firewall rules on both client and server allow the passive port range. |
550 Permission denied | Set the directory permissions to 755. |
| Only empty directories are listed | Check the chroot_local_user configuration. |
500 OOPS: vsftpd: refusing to run with writable root | Run chmod a-w /data/ftp to remove write permission from the chroot root directory. |
| Passive mode connection timeout | Verify the firewall rules and the pasv_address setting. |
| Cannot upload files | Confirm that the directory permissions are 755 or 750. |
Appendix: vsftpd configuration reference
Configuration files (Alibaba Cloud Linux and CentOS)
| File | Description |
|---|---|
/etc/vsftpd/vsftpd.conf | Core vsftpd configuration file |
/etc/vsftpd/ftpusers | Blacklist file. Users listed here cannot access the FTP server. |
/etc/vsftpd/user_list | Whitelist file. Users listed here can access the FTP server. |
Logon control parameters
| Parameter | Description |
|---|---|
anonymous_enable=YES | Accepts anonymous users |
no_anon_password=YES | Anonymous users can log in without a password |
anon_root=(none) | Home directory for anonymous users |
local_enable=YES | Accepts local users |
local_root=(none) | Home directory for local users |
User permission parameters
| Parameter | Description |
|---|---|
write_enable=YES | Allows file uploads (global setting) |
local_umask=022 | File permissions for uploads by local users |
file_open_mode=0666 | Permissions for uploaded files; works with local_umask |
anon_upload_enable=NO | Allows anonymous users to upload files |
anon_mkdir_write_enable=NO | Allows anonymous users to create directories |
anon_other_write_enable=NO | Allows anonymous users to edit and delete files |
chown_username=lightwiter | Username assigned to files uploaded by anonymous users |