Web applications exposed through a service mesh ingress gateway are vulnerable to common web attacks such as SQL injection and cross-site scripting. By connecting a Service Mesh (ASM) ingress gateway to a Web Application Firewall (WAF) instance, all inbound traffic is inspected before it reaches your backend services. WAF filters out malicious requests and forwards only legitimate traffic to the ingress gateway.
After you complete the steps in this guide, your ingress gateway routes traffic through a WAF 3.0 instance, and your access logs include WAF-added headers for debugging.
How it works
With this integration, traffic flows through the following path:
Client --> WAF instance (inspects traffic) --> Ingress gateway --> Backend servicesWAF inspects each incoming request against its rule sets. Legitimate requests are forwarded to the ingress gateway with additional headers, such as the client IP address and a custom tag. Malicious requests are blocked before they reach the gateway.
Two connection methods are available:
| Criteria | Layer 4 CLB | CNAME |
|---|---|---|
| Scope | All traffic on the ingress gateway | Specific domain names only |
| DNS changes | Not required | Required |
| Best for | Full gateway protection | Multi-domain gateways where only some domains need WAF |
Layer 4 CLB (recommended): Associates the Classic Load Balancer (CLB) instance of the ingress gateway with WAF. All traffic that reaches the CLB is routed through WAF for inspection. A CLB instance was formerly known as a Server Load Balancer (SLB) instance.
CNAME: Routes only requests for specified domain names through WAF. Use this method when the ingress gateway serves multiple domains and only some require WAF protection.
To use the CNAME method, point the DNS record of your domain name to the CNAME provided by WAF. WAF then forwards inspected traffic to the ingress gateway.
Prerequisites
Before you begin, make sure that you have:
An ingress gateway deployed in your ASM instance. See Create an ingress gateway
A cluster added to the ASM instance. See Add a cluster to an ASM instance
The HTTPBin application deployed and exposed on port 80 of the ingress gateway. See Deploy the httpbin application
Step 1: Connect the ingress gateway to WAF
Method 1: Use a Layer 4 CLB instance
Log on to the Web Application Firewall console.
Purchase a WAF 3.0 instance. Click Subscription or Pay-As-You-Go, confirm the region and other settings, and then click Buy Now.
Skip this step if you already have a WAF instance.
In the left-side navigation pane, click Website Configuration. On the Website Configuration page, click the Cloud Native tab, click CLB(TCP), and then click Add.
In the Configure Instance- Layer 4 CLB Instance panel, find the CLB instance associated with your ingress gateway and click Add Port in the Actions column. Select the port used by the ingress gateway, and then click OK.
This example uses HTTP port 80. To use HTTPS, configure an HTTPS certificate first.
NoteTo find the CLB instance associated with your ingress gateway, log on to the ASM console and open the gateway details page.
Select Enable Traffic Mark, add the following three headers, and then click OK:
Header type Header name Value Custom Header customwaftagcustomwaftagvalueOriginating IP Address clientrealip-- Source Port clientrealport-- These headers are appended to requests that pass through WAF, which allows you to confirm that a request was inspected by WAF and to retrieve the original client IP address.
Method 2: Use a CNAME
Log on to the Web Application Firewall console.
Purchase a WAF 3.0 instance. Click Subscription or Pay-As-You-Go, confirm the region and other settings, and then click Buy Now.
Skip this step if you already have a WAF instance.
In the left-side navigation pane, click Website Configuration. On the Website Configuration page, click the CNAME Record tab, and then click Add.
In the Configure Listener step, configure the listener parameters and click Next.
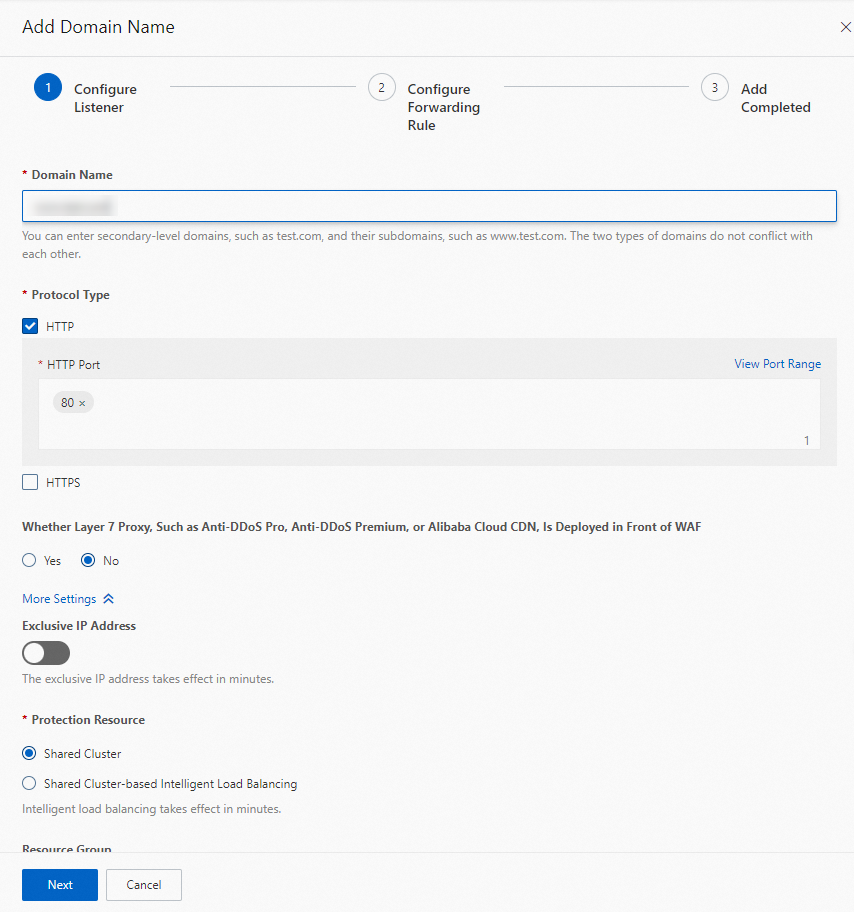
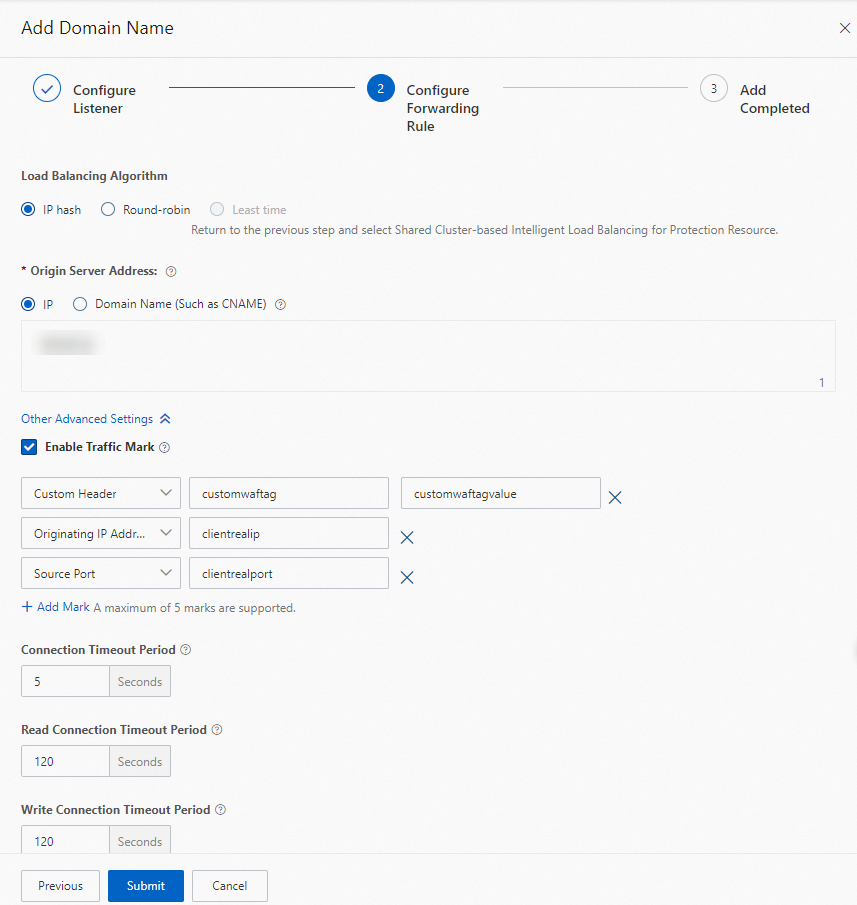
In the Configure Forwarding Rule step, configure the following settings and click Submit:
Set Load Balancing Algorithm to IP hash.
Set Origin Server Address to IP and enter the public IP address of the ingress gateway.
Select Enable Traffic Mark and add the following three headers:
Header type Header name Value Custom Header customwaftagcustomwaftagvalueOriginating IP Address clientrealip-- Source Port clientrealport-- Keep the default values for other parameters.
In the Add Completed step, click Copy CNAME to save the CNAME provided by WAF, and then click Complete.
NoteAfter this step, update the DNS record of your domain name to point to the CNAME provided by WAF. Until you do this, traffic does not flow through the WAF instance.
Step 2: (Optional) Customize access log fields
WAF appends headers to back-to-origin requests, such as the custom tag, client IP address, and client port configured in Step 1. By default, these headers do not appear in ASM access logs.
To include WAF-added headers in your access logs for easier debugging, customize the access log fields in the ASM console. For detailed instructions, see Customize access logs on the data plane.
Step 3: Verify the WAF connection
If you used a Layer 4 CLB instance
Open a browser and go to:
http://<ingress-gateway-IP>:80/status/418Replace <ingress-gateway-IP> with the IP address of your ingress gateway.
Expected output:
-=[ teapot ]=-
_...._
.' _ _ `.
| ."` ^ `". _,
\_;`"---"`|//
| ;/
\_ _/
`"""`If you used a CNAME
Run the following command:
curl -H "Host:<your-domain>" "http://<waf-cname>/status/418" -vReplace the following placeholders:
| Placeholder | Description | Example |
|---|---|---|
<your-domain> | The domain name configured in WAF | example.com |
<waf-cname> | The CNAME provided by WAF | geszcfxxxx.aliyunwaf1.com |
Expected output:
* Trying x.x.x.x:80...
* Connected to geszcfxxxxxxxxxxxxxxxxxxxxppbeiz.aliyunwaf1.com (x.x.x.x) port 80 (#0)
> GET /status/418 HTTP/1.1
> Host:xxxx
> User-Agent: curl/7.84.0
> Accept: */*
>
* Mark bundle as not supporting multiuse
< HTTP/1.1 418 Unknown
< Date: Wed, 22 Feb 2023 05:07:23 GMT
< Content-Length: 135
< Connection: keep-alive
< Set-Cookie: acw_tc=0bc1599a16770424432844282e82xxxxxxxxxxxxxxxxxxx1ad989e7e5245f;path=/;HttpOnly;Max-Age=1800
< server: istio-envoy
< x-more-info: http://tools.ietf.org/html/rfc2324
< access-control-allow-origin: *
< access-control-allow-credentials: true
< x-envoy-upstream-service-time: 1
<
-=[ teapot ]=-
_...._
.' _ _ `.
| ."` ^ `". _,
\_;`"---"`|//
| ;/
\_ _/
`"""`This example uses the CNAME directly instead of a real domain name. To access the application through your actual domain name, update the DNS resolution to point your domain to the CNAME provided by WAF.
Step 4: View WAF-added headers in gateway logs
Confirm that WAF is active on the traffic path by checking the traffic mark headers in the ASM Log Center.
Log on to the ASM console. In the left-side navigation pane, choose Service Mesh > Mesh Management.
On the Mesh Management page, click the name of the target ASM instance.
On the ASM Gateway Logs tab, enter
418in the search box and click Search & Analyze.The log entries display the values of the WAF-added headers (
customwaftag,clientrealip,clientrealport), confirming that requests are flowing through the WAF instance.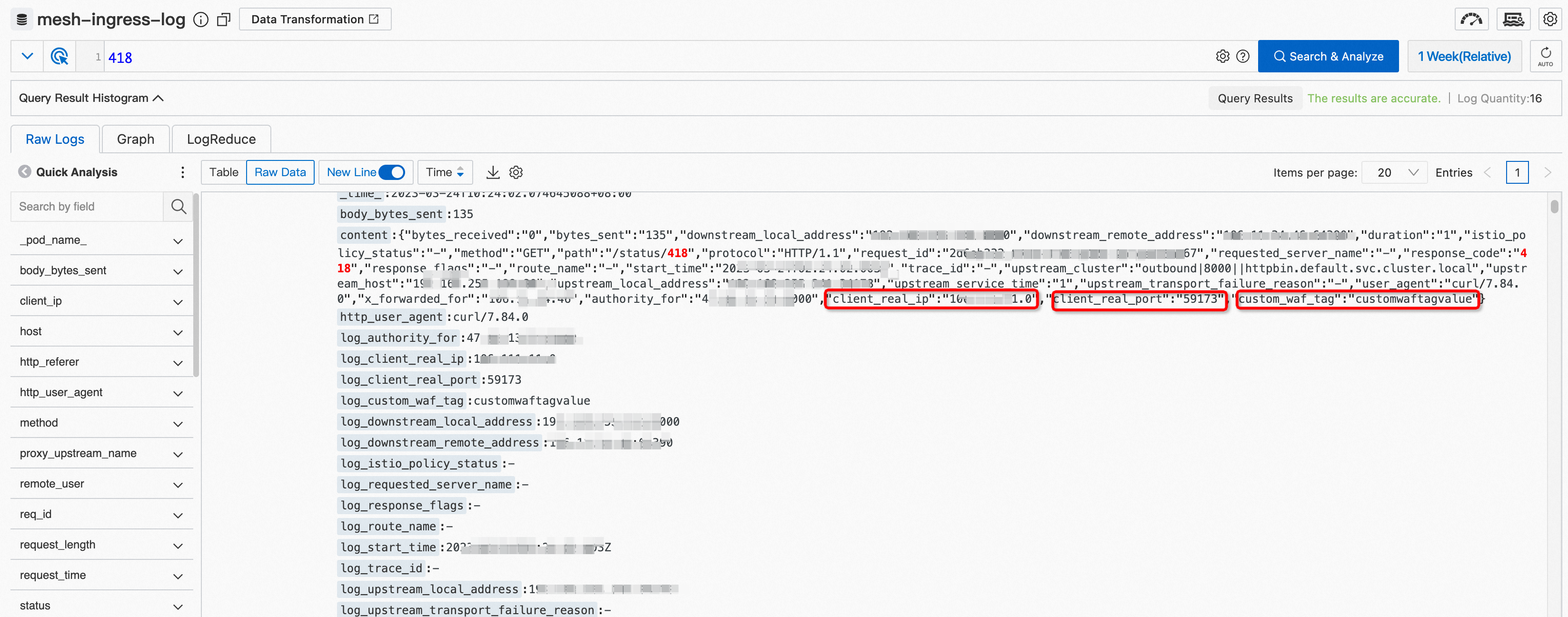
What to do next
Configure WAF protection rules: Log on to the WAF console to configure advanced protection capabilities to protect your website from attacks.
Add more traffic mark headers: To track additional custom headers, repeat Step 2 to include them in the access log configuration.