Web サイトが Object Storage Service (OSS) からリソースを読み込むと、ブラウザが「CORS ポリシーによってブロックされました」というエラーを報告することがあります。このエラーは、Web ページが同じプロトコル、ドメイン名、ポートからのみリソースにアクセスできるように制限する、ブラウザの同一オリジンポリシーが原因です。たとえば、https://www.example.com のページは、https://example-bucket.oss-cn-hangzhou.aliyuncs.com/test.jpg のような異なるドメインの OSS リソースに直接アクセスすることはできません。 OSS バケットにオリジン間リソース共有 (CORS) ルールを設定して、特定の Web サイトが OSS リソースにアクセスすることを安全に権限付与できます。これにより、Web ページはオブジェクトと直接やり取りできるようになります。
OSS バケットにオリジン間リソース共有 (CORS) ルールを設定して、特定の Web サイトが OSS リソースにアクセスすることを安全に権限付与できます。これにより、Web ページはオブジェクトと直接やり取りできるようになります。
仕組み
CORS リクエストは、単純リクエストとプリフライトリクエストに分類されます。単純リクエストは直接送信されます。プリフライトリクエストは、メインリクエストを送信する前に、まず許可を取得する必要があります。
次のいずれかの条件が満たされる場合、プリフライトリクエストが必要です。
リクエストが
GET、HEAD、またはPOST以外のメソッドを使用している。リクエストが
POSTメソッドを使用し、Content-Typeがtext/plain、application/x-www-form-urlencoded、またはmultipart/form-data以外である。リクエストに
x-oss-*などのカスタムヘッダーが含まれている。
ブラウザが OSS に単純リクエストを送信すると、次のプロセスが発生します。
ブラウザはリクエストに
Originヘッダーを追加します。Originヘッダーは、リクエストを開始したページのオリジンを指定します (例:Origin: https://www.example.com)。OSS は、リクエストの HTTP メソッドと
Originヘッダーの値を宛先バケットの CORS 設定と比較して、一致する項目を検索します。一致が見つかった場合、OSS は応答にAccess-Control-Allow-Originヘッダーを含めます。Access-Control-Allow-Originヘッダーには、最初のリクエストのOriginヘッダーの値が含まれます。ブラウザは応答を受信し、
Access-Control-Allow-Originヘッダーの値が元のリクエストのドメインと一致するかどうかを確認します。一致する場合、リクエストは成功します。一致しない場合、または応答にAccess-Control-Allow-Originヘッダーが含まれていない場合、リクエストは失敗します。
プリフライトリクエストは、まず次のステップを実行します。成功した場合、単純リクエストと同じプロセスに進みます。
ブラウザは、意図したメインリクエストのメソッド (
Access-Control-Request-Method) とヘッダー (Access-Control-Request-Headers) を含むOPTIONSリクエストを送信します。OSS は、CORS 設定に基づいて、リクエスト内のメソッドとヘッダーが許可されているかどうかを確認します。プリフライトリクエスト内のメソッドまたはヘッダーの値が、宛先リソースで許可されているメソッドとヘッダーのセットに含まれていない場合、リクエストは失敗し、メインリクエストは送信されません。
静的 Web サイトリソースの読み込み
https://www.example.com の Web サイトは、OSS バケットに保存されているイメージ、CSS、および JS ファイルを読み込む必要があります。
ステップ 1: CORS ルールを設定する
[OSS コンソール]にログインします。宛先バケットの [データセキュリティ] > [CORS 設定] ページに移動し、次のようにルールを作成します。
パラメーター | 値 | 説明 |
オリジン |
| リソースのセキュリティを確保するために、この特定の Web サイトへのリクエストを制限します。 |
許可されるメソッド |
| GET はリソースをダウンロードし、HEAD はキャッシュを検証します。 |
許可されるヘッダー | 空のままにする | このシナリオには、プリフライトリクエストをトリガーしない単純リクエストが含まれるため、このパラメーターは使用されません。空のままにしてください。 |
公開されるヘッダー |
|
|
キャッシュタイムアウト | 86400 | プリフライト応答を 24 時間キャッシュして、将来の潜在的なプリフライトリクエストを削減します。 |
Vary: Origin ヘッダーを返す。 | 未チェック | オリジンは単一で特定されているため、このオプションは複数ドメインのキャッシュ問題を処理する必要がありません。 |
ステップ 2: 設定を検証する
https://www.example.com にアクセスし、イメージなどの OSS リソースが正しく読み込まれ、ブラウザコンソールに CORS エラーがないことを確認します。
フロントエンドから直接ファイルをアップロードする
Web ページ https://app.example.com のユーザーは、プロフィール写真やドキュメントなどのファイルを OSS に直接アップロードします。
ステップ 1: CORS ルールを設定する
[OSS コンソール]にログインします。宛先バケットの [データセキュリティ] > [CORS 設定] ページに移動し、次のようにルールを作成します。
パラメーター | 値 | 説明 |
オリジン |
| この権限付与されたアプリケーションのみがアップロードを実行する権限を持つようにします。 |
許可されるメソッド |
| PUT または POST は、アップロード操作を実行するために必要な HTTP メソッドです。 |
許可されるヘッダー |
| フロントエンドからの直接アップロードのセキュリティは、固定の |
公開されるヘッダー |
|
|
キャッシュタイムアウト | 600 | アップロード操作は頻度が低いです。10 分のキャッシュは、プリフライトリクエストを削減しつつ、設定変更を迅速に反映させることができます。 |
Vary: Origin ヘッダーを返す | チェック済み | テスト環境など、将来の潜在的な複数ドメインのデプロイメントに備え、CDN のキャッシュ汚染を防ぎます。 |
ステップ 2: 設定を検証する
https://app.example.com ページでアップロード操作を実行します。ファイルが OSS に正常にアップロードされ、ブラウザコンソールに CORS エラーがないことを確認します。
複数の環境をサポートする
dev.example.com や app.example.com など、開発、テスト、本番用の複数のサブドメインが同じ OSS リソースにアクセスする必要があります。
ステップ 1: CORS ルールを設定する
[OSS コンソール]にログインします。宛先バケットの [データセキュリティ] > [CORS 設定] ページに移動し、次のようにルールを作成します。
パラメーター | 値 | 説明 |
オリジン |
|
|
許可されるメソッド |
| 複数の環境にまたがるテストニーズを満たすために、リソースの読み取りとアップロードの両方を許可します。 |
許可されるヘッダー |
| 開発中のさまざまな環境や機能では、異なるカスタムヘッダーが導入される可能性があります。 |
公開されるヘッダー |
| ダウンロードの検証とアップロード結果のフィードバックの両方をサポートします。 |
キャッシュタイムアウト | 3600 | 1 時間のキャッシュは、複数の環境間での切り替えとデバッグに柔軟性を提供します。 |
Vary: Origin ヘッダーを返す | チェック済み | 必須。これにより、CDN は |
ステップ 2: 設定を検証する
https://dev.example.com と https://app.example.com の両方でアクセスまたはアップロードテストを実行し、すべての操作が成功することを確認します。
認証付きで API スタイルの呼び出しを行う
https://api.example.com のフロントエンドアプリケーションは、Authorization などのカスタムヘッダーを含めることで、保護された OSS リソースにアクセスする必要があります。
ステップ 1: CORS ルールを設定する
[OSS コンソール]にログインします。宛先バケットの [データセキュリティ] > [CORS 設定] ページに移動し、次のようにルールを作成します。
パラメーター | 値 | 説明 |
オリジン |
| 認証情報を含むリクエストの場合、オリジンは正確で信頼できるドメイン名でなければなりません。 |
許可されるメソッド |
| 読み取り、更新、削除を含む、非公開リソースの完全なライフサイクル管理をサポートします。 |
許可されるヘッダー |
|
|
公開されるヘッダー |
| 成功した操作の検証識別子と、失敗した場合のトラブルシューティング ID を提供します。 |
キャッシュタイムアウト | 600 | 認証済みリクエストの場合、プリフライトキャッシュ時間を短くする (10 分) ことで、セキュリティポリシーの変更をより迅速に適用できます。 |
Vary: Origin ヘッダーを返す | チェック済み | CDN に、異なるオリジンに対して応答を個別にキャッシュするように指示し、混乱を避けます。 |
ステップ 2: 設定を検証する
https://api.example.com ページから Authorization ヘッダー付きのリクエストを開始し、保護された OSS リソースにアクセスできることを確認します。
本番環境での使用
セキュリティのベストプラクティス
最小権限の原則に従います。
[オリジン (AllowedOrigin)]を正確に設定する: バケットが完全に公開されていない限り、AllowedOriginを*に設定しないでください。Web サイトのドメイン名を正確に指定します (例:https://www.example.com)。[許可されるメソッド (AllowedMethod)]を制限する: ビジネスに必要な HTTP メソッドのみを公開します。Web サイトがデータの読み取りのみを必要とする場合は、GETとHEADのみを設定します。[許可されるヘッダー (AllowedHeader)]を明示的に指定する:Authorizationヘッダーなどの認証情報を伴うリクエストの場合、*を使用しないでください。必要なすべてのリクエストヘッダーを明示的にリストする必要があります。
パフォーマンスのベストプラクティス
プリフライトキャッシュの最適化:
キャッシュタイムアウト (MaxAgeSeconds)に、86400秒 (24 時間) などの適切な値を設定します。これにより、プリフライトリクエストが大幅に削減され、レイテンシーとリクエストコストが削減されます。Vary: Originの影響を評価する:Vary: Originを有効にすると、キャッシュ汚染の問題が解決されますが、CDN キャッシュの複雑さが増します。これにより、キャッシュヒット率が低下し、CDN back-to-origin トラフィックが増加し、追加のコストとレイテンシーが発生する可能性があります。このオプションは、十分な評価を行った後にのみ使用してください。
CDN アクセラレーションシナリオ
バケットが CDN によって高速化され、CDN ドメイン名を使用してアクセスされる場合、クロスオリジンリクエストは最初に CDN の POP (Point of Presence) に到達します。この場合、OSS コンソールではなく、CDN コンソールで CORS ルールを設定する必要があります。OSS の CORS 設定は、OSS オリジンドメイン名に直接行われたリクエストにのみ適用されます。詳細については、「オリジン間リソース共有を設定する」をご参照ください。
CORS ルールのパラメーター
各バケットに最大 20 個の CORS ルールを設定できます。OSS はルールを上から下に順に評価し、リクエストに一致する最初のルールを適用します。一致が見つかると、OSS は後続のルールをチェックしません。
パラメーター | 必須 | 説明 |
オリジン (AllowedOrigin) | はい | OSS リソースへのクロスオリジンリクエストを行うことが許可されている Web サイト (オリジンドメイン) を指定します。
|
許可されるメソッド (AllowedMethod) | はい | 許可される HTTP メソッドを指定します。
|
許可されるヘッダー (AllowedHeader) | いいえ | プリフライトリクエストに適用され、実際のリクエストに含めることができる HTTP ヘッダーを決定します。
|
公開されるヘッダー (ExposeHeader) | いいえ | クライアント側の JavaScript コードからアクセスできる OSS 応答ヘッダーを指定します。
|
キャッシュタイムアウト (MaxAgeSeconds) | いいえ | ブラウザがプリフライト
|
Vary: Origin | いいえ | 応答に
重要 このオプションを有効にすると、CDN のキャッシュヒット率が低下する可能性があります。 |
よくある質問
エラー: リクエストされたリソースに 'Access-Control-Allow-Origin' ヘッダーが存在しません。
このエラーは通常、ブラウザが CORS ヘッダーのない古い応答をキャッシュしたか、受信リクエストに一致する CORS ルールがないために発生します。
ブラウザのキャッシュをクリアして、もう一度テストしてください。エラーが解決しない場合は、次の手順に従って CORS ルールが正しく設定されているか確認してください。
左側のナビゲーションウィンドウで、[データセキュリティ] > [CORS 設定] を選択します。
[CORS 設定] ページで、[ルールの作成] をクリックします。
[CORS ルールの作成] パネルで、[オリジン] を
*に設定し、すべての [許可されるメソッド] を選択し、[許可されるヘッダー] を*に設定し、[公開されるヘッダー] をETagとx-oss-request-idに設定し、[キャッシュタイムアウト (秒)] を 0 に設定し、[Vary: Origin] を選択して、[OK] をクリックします。問題が解決しない場合は、任意のサーバーにログインし、次のコマンドを実行してクロスオリジンリクエストヘッダーを表示します。
curl -v -o output_file.txt -H 'Origin:[$URL2]' '[$URL1]'説明[$URL1] は、リクエストされた OSS リソースの URL です。
[$URL2] は、CORS ルールで設定したオリジンアドレスです。
コマンドは同様の出力を返します。
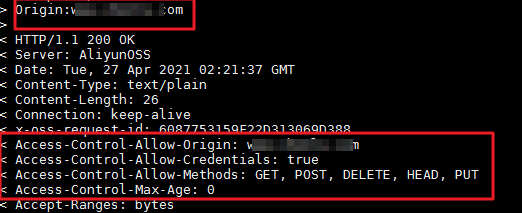
応答に設定と一致する CORS ヘッダーが含まれている場合、問題はローカルキャッシュが原因である可能性があります。ブラウザは、正しい CORS ヘッダーを含まない以前のリクエストからの応答をキャッシュしている可能性があります。新しいクロスオリジンリクエストが行われると、ブラウザはキャッシュされた応答を使用するため、チェックが失敗します。次の解決策を試してください。
ブラウザで Ctrl+F5 を押してキャッシュをクリアし、問題が解決するかどうかをテストします。
CORS ルールの [キャッシュタイムアウト] を 0 に設定します。これにより、リソースがクライアントにキャッシュされるのを防ぎ、すべてのリクエストがサーバーから権限付与情報を取得するようになります。
説明オブジェクトをアップロードするときに、オブジェクトの cache-control を no-cache に設定できます。すでにアップロードされているオブジェクトについては、ossutil を使用してこの設定を変更できます。詳細については、 set-meta (オブジェクトのメタデータを管理する) をご参照ください。
CDN を使用して OSS を高速化します。これにより、CDN によって提供されるすべてのリクエストが CORS ヘッダーを返すようになります。
応答に 2 つの CORS ヘッダーが含まれているか、OSS 設定と一致しないヘッダーが含まれている場合、問題は OSS を高速化するために CDN を使用していることが原因である可能性があります。
[CDN コンソール]にログインし、OSS の CDN アクセラレーションを一時的に無効にして、クロスオリジンの問題が解決したことを確認します。
確認後、特定のドメイン名をクリックし、[キャッシュ設定] > [HTTP レスポンスヘッダー] をクリックします。
必要に応じてカスタム HTTP 応答ヘッダーを設定します。
CORS の問題がまだ解決しない場合は、さらなるトラブルシューティングについて「OSS のオリジン間リソース共有 (CORS) の一般的なエラーと解決策」をご参照ください。
エラー: 「Access-Control-Allow-Origin」ヘッダーの値「...」が、指定されたオリジンと一致しません。
サーバーは Access-Control-Allow-Origin ヘッダーを返しましたが、その値が現在のリクエストの Origin と一致しません。これは多くの場合、キャッシュの問題です。複数の Web サイトドメイン名が OSS にアクセスするように設定した場合、ブラウザまたは CDN が 1 つの Web サイトのアクセス権限をキャッシュし、それを誤って別の Web サイトに提供することがあります。
CORS ルールの [Vary: Origin] オプションを有効にして、異なる Web サイト間のキャッシュの競合を防ぎます。または、ブラウザのキャッシュをクリアして再試行してください。
エラー: プリフライトリクエストへの応答がアクセス制御チェックをパスしません: リクエストの credentials モードが「include」の場合、応答の「Access-Control-Allow-Origin」ヘッダーの値はワイルドカード「*」であってはなりません。
このエラーは、フロントエンドコードが認証情報付きのリクエストを送信し、Access-Control-Allow-Credentials が True であるにもかかわらず、Access-Control-Allow-Origin がワイルドカード * として設定されているために発生します。セキュリティ上の理由から、ブラウザはこの場合にワイルドカードオリジンの使用を禁止し、任意のドメインがリソースにアクセスして認証情報を取得するのを防ぎます。この情報には、Cookie や Authorization ヘッダーなどの機密データが含まれます。
リクエストヘッダーに
Credentials情報を含めるには、Access-Control-Allow-Originの値をワイルドカード*から特定のドメイン名 (例:https://example.com) に変更します。リクエストヘッダーに
Credentials情報を含める必要がない場合は、フロントエンドコードでxhr.withCredentialsをfalseに設定し、サーバー側でAccess-Control-Allow-Credentialsがfalseに設定されていることを確認します。
OSS からのクロスオリジン読み込みが遅い場合、どうすれば改善できますか?
クロスオリジンリクエストは、Origin ヘッダーを含む標準の HTTP リクエストです。読み込み速度は、リクエストがクロスオリジンであるかどうかではなく、クライアントと OSS バケット間の物理的なネットワークパスに依存します。たとえば、クライアントが中国 (香港) にあり、バケットが中国本土にある場合、これは長距離アクセスと見なされます。この場合、OSS 転送アクセラレーションエンドポイントを使用してネットワークパスを最適化できます。詳細については、「転送アクセラレーション」をご参照ください。
転送アクセラレーションにより、世界中のお客様が最適化されたネットワークを使用してデータを転送できます。これにより、アップロードとダウンロードの速度が大幅に向上し、さまざまなリージョンのユーザーに良好なアクセス体験が保証されます。